Mining China’s ‘Little Red Book’ for Open Source Gold
The challenges of conducting open-source research in China are well-documented. Consistently named one of the most digitally oppressive countries in the world, China blocks some of the world’s largest social media platforms, such as Facebook, Google, and YouTube. Those that are still accessible are mostly Chinese-owned, strictly regulated and monitored in real time by AI systems as well as tens of thousands of “internet police”.
But despite these strict controls, Chinese apps – which boast more than a billion estimated users – remain an information goldmine for investigative journalists covering stories both within and outside China.

Support Bellingcat
Your donations directly contribute to our ability to publish groundbreaking investigations and uncover wrongdoing around the world.
Since most foreign sites are banned, Chinese platforms are the largest resource available to journalists and researchers interested in what’s going on in the world’s second-most populous country. Even when a topic is being censored, patterns in the censorship can themselves serve as investigative leads: a 2020 BuzzFeed News investigation, for example, mapped out detention camps in Xinjiang by examining areas that had been blanked out on China’s Baidu Maps.
With millions of Chinese people living overseas, social media activity by members of the diaspora can also turn into global stories.
Serial rapist Zou Zhenhao, a Chinese PhD student, was jailed in London last year after one of his victims posted a warning on Xiaohongshu, also known as Little Red Book or Rednote, an app popular with young Chinese women living abroad. Another woman Zou had raped reached out to the original poster, who put her in touch with the police – leading to the conviction of a man described by police as possibly one of the worst sexual predators in British history.
Founded in 2013 as a Hong Kong shopping guide, Xiaohongshu has evolved into a lifestyle and e-commerce platform that has been compared with Instagram, Pinterest and Amazon. Last year, it reported about 300 million monthly active users, rivalling some of China’s largest social media platforms.

The app’s 600 million daily searches by the end of 2024 also accounted for half of market leader Baidu’s search volume, demonstrating that it is emerging as a critical search and discovery engine, not just a social platform.
Although primarily a Chinese-language app, Xiaohongshu gained attention in the English-speaking world last year, when millions of American TikTok users flocked to the platform in anticipation of a TikTok ban under US President Donald Trump.
Responding to the surge of international users – sparked by the #TikTokRefugees trend – Xiaohongshu rolled out an AI-powered translation feature, making the app more accessible to non-Chinese audiences. This also meant that journalists without Chinese language skills can more easily communicate on and navigate the platform.
Despite its growing popularity both within and outside China, the app is relatively new and underexplored compared to more well-established platforms such as Weibo.
This guide aims to provide a starting point for those looking to explore Xiaohongshu for open-source investigations, including an overview of its main user demographics, potential topics to explore and strategic search methods specific to the app.
User Demographics and Topics
According to Xiaohongshu’s official data, the platform’s demographic profile is mainly young, female and urban. As of 2024, 70 percent of its users were women, with half of all users belonging to Gen Z and living in China’s largest cities.
As previously mentioned, the app has also gained popularity with the Chinese diaspora. Many Chinese nationals living abroad use it as a search engine for local information, posting and searching for content related to their daily lives, from restaurant recommendations and apartment hunting to navigating foreign bureaucracies and finding community resources.
This demographic profile makes Xiaohongshu particularly well-suited for investigating stories about consumer fraud and urban livability issues. For example, Chinese outlets like Jiemian have used Xiaohongshu posts to expose the grey-market ecosystem of paid reviews and fake endorsements tied to the platform’s e-commerce model, while in 2022, International Financial News traced a mother-and-baby store scam that defrauded over 400 parents back to product recommendation posts on the platform.
Given its predominantly female user base, Xiaohongshu has also evolved into one of China’s most important spaces for feminist discourse and women’s issues. Academic researchers have used content on the platform to analyse local discussions on menstrual shaming, sexual harassment, and the controversial “divorce cooling-off period” introduced in 2021. As Rest of World reported, women have increasingly congregated on Xiaohongshu, where they outnumber male users and have found ways to trick the app’s recommendation algorithm so their posts are shown mostly to other women.
The Relevance of Censorship
Political content and current affairs about China are largely absent from the app – a result of both active censorship and platform design.
All Chinese social media platforms, including Xiaohongshu, operate under strict content moderation requirements from the Cyberspace Administration of China. A leaked 143-page internal document published by China Digital Times in 2022 revealed how Xiaohongshu censors respond to government directives in “real-time”, blocking content related to politically sensitive topics such as criticism of the Chinese Communist Party, labour strikes and student suicides. Xiaohongshu’s commercial focus also makes it less likely that these topics would be discussed on the platform: as Rest of World reported, the platform functions less like Weibo – a public square for current events – and more like “a giant mall, where shoppers tell each other what to buy”.
Coverage of international affairs is also tightly controlled: only state-owned or state-controlled news organisations can obtain licences to publish original news content. However, content about life abroad, particularly stories about the cost of living, healthcare, or social problems in Western countries, circulates more freely on platforms including Xiaohongshu, and provide journalists with insight into how Chinese diaspora communities engage with local political systems.
For example, when the 2025 Miss Finland was accused of making anti-Asian gestures, searching for “芬兰小姐” (Miss Finland) and “投诉” (complaint) on Xiaohongshu revealed a trove of collective action: users shared different complaint pathways, posted templates for filing reports, and documented various outcomes from their complaints.
For such large-scale public events, Xiaohongshu can be both an organising platform and a rich source for tracking how diaspora communities coordinate responses to discrimination, providing journalists with insight into grassroots activism and transnational advocacy networks.
Getting Started
Xiaohongshu is available for download on both Apple’s App Store and Google Play worldwide, or can be accessed via a web browser. In international app stores, the app appears under the name “RedNote,” but this is the same application as Xiaohongshu – content and accounts are shared across both. The key difference is that RedNote users who register with overseas phone numbers are automatically tagged as international users, which affects the content the algorithm surfaces to them.
For users who download the app outside mainland China, Xiaohongshu automatically detects the device language and location. Upon first login, international users are prompted with an option to automatically translate all content into English (or their device language). If enabled, posts and comments will display with translations by default, and the algorithm will prioritise English-language content and posts created by or for international users, such as expat influencers.
For researchers and journalists seeking to observe the platform as Chinese users experience it, consider disabling automatic translation. This allows you to see content as it natively appears and helps you distinguish between posts created for international audiences versus those created for domestic users – a distinction that matters when assessing how representative your sample is for the relevant topic.
The default home feed, or the “Explore” tab, is where the algorithm surfaces content based on your engagement history, location and user profile. The feed uses a grid layout displaying post thumbnails with titles and like counts.
On the top right corner of the screen, the search bar also allows keyword searches across posts, users and topics. Results can be filtered by content type (e.g. notes, videos, users or products) and sorted by relevance or recency.

Using the Search Bar
Xiaohongshu’s search function is relatively basic. You can search by keywords and filter by time and location, but the options are general: time filters include “past day,” “past week,” or “past six months,” while location filters offer “same city” or “nearby”.
For example, searching “Canada” returns posts tagged with that keyword, which you can then sort by recency or proximity.

For breaking news events, try searching location names or names of individuals involved in the incident, filtering for the most recent posts to capture real-time reactions and on-the-ground accounts before they’re censored or deleted.
Xiaohongshu primarily uses algorithms to curate and push content through personalised feeds. For journalists using Xiaohongshu for investigative purposes, it can be useful to actively search for topics of interest to train your algorithm – the more you search and engage with specific content, the more relevant posts the algorithm will surface to you.
However, if you are researching the platform itself – studying what content Xiaohongshu promotes, how censorship operates, or what narratives dominate – you may want to start from a clean slate. In that case, consider periodically turning off personalised recommendations (Settings → Privacy Settings → Personalisation Options), clearing your browsing history, clearing cached data, or using a fresh account to observe what the platform shows to a “neutral” user.
Language and Lingo
During the influx of “TikTok refugees” in January 2025, Xiaohongshu launched a translation feature for users outside mainland China, enabling the automatic translation of comments and posts.
However, this does not translate search queries. The platform’s search engine is still optimised for Chinese, though there is a “prioritise English” filter for overseas users, and searching in English will return some results.

But the language you search in shapes far more than just your results – it determines which version of the platform you see. When you search in English or use an international account, the algorithm treats you as a foreign user and surfaces content accordingly: influencers explaining why they love living in China, comparisons showing Chinese life favourably against the West.
This isn’t a neutral cross-section of the platform – it is a curated bubble. To access what Chinese users actually discuss among themselves, it would be more effective to search in simplified Chinese and, ideally, use a China-registered account if you have access to one. If you don’t read Chinese, you can also consider using a translation tool (Google Translate, DeepL, or an AI assistant) to convert your search terms into simplified Chinese before entering them.
Despite such tools and the in-app translation feature, it is always useful when researching using Chinese platforms to work with a native speaker familiar with the local context. They can flag when an innocuous-seeming term actually carries hidden meaning, and help identify coded conversations about a censored topic.
On Xiaohongshu specifically, this coded language extends beyond political topics to include anything the platform’s algorithm might flag as “vulgar” or promotional. For example, users substitute fruits and neutral terms for body parts or sexual content to avoid being flagged as inappropriate – the peach emoji for buttocks, or 炒菜 (“cooking”) for explicit material. They may also use abbreviations and emojis for commercial terms to evade anti-marketing filters, such as “vx” (the abbreviation of how WeChat is pronounced in Chinese) or “![]() 绿” (“plus green”, apparently referring to WeChat’s green logo) for WeChat, or “米” (rice) or the moneybag emoji for money.
绿” (“plus green”, apparently referring to WeChat’s green logo) for WeChat, or “米” (rice) or the moneybag emoji for money.
Advanced Search Strategies
For more sophisticated searching, consider using third-party marketing analytics tools like Xinhong and Qiangu, which can show trending topics, popular posts and engagement metrics, as well as identify key content creators posting about specific subjects.
For example, on Xinhong, when you search for “Canada” in Chinese, it also shows show trending related searches such as “加拿大总理” (Canadian Prime Minister). Clicking through these suggestions leads to recent posts—for example, posts about Mark Carney’s latest statements at Davos, along with user comments and reactions.

While these tools are designed for marketers, they provide journalists with valuable capabilities: tracking how topics evolve, identifying influential voices in specific communities, and discovering related hashtags or discussions that might not surface through basic platform search. These tools often require paid subscriptions but can significantly enhance research efficiency for long-term investigations.
Another valuable feature is Xiaohongshu’s group chat function, where users gather around shared keywords and topics—from city-specific communities to niche interests. These groups are often highly active and provide access to candid community discussions that don’t appear in public posts. To find relevant groups, go to Messages → Group Square, where you can browse categories or search by keyword and request to join.
Monitoring active group chats related to relevant topics, whether that’s a specific city, industry, or issue, can help journalists and researchers stay updated on emerging issues and detect potential story leads before they become widely visible on public feeds.
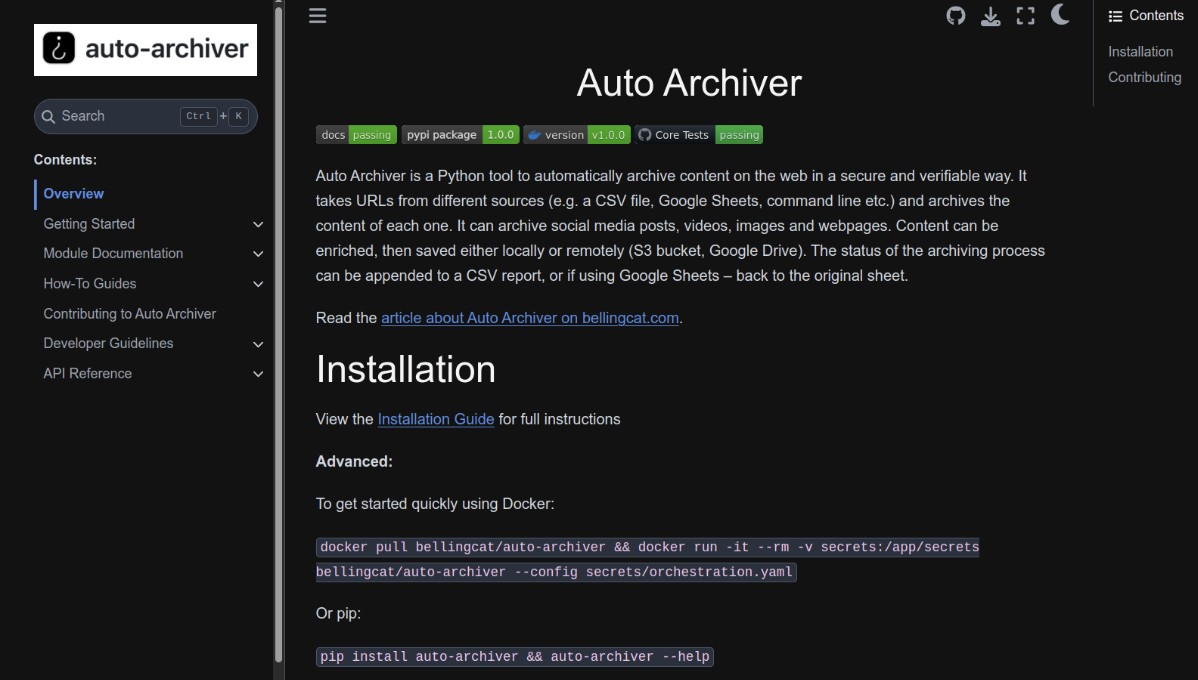
Preserving the Evidence
Chinese social media content can disappear quickly and without warning due to censorship, making immediate preservation critical.
Always take two preservation steps immediately upon discovering relevant content:
First, screenshot the entire post, including the URL, timestamp, username, like/comment counts, and location tags. These metrics establish context and authenticity. Use tools that capture full-page screenshots rather than just visible portions, as posts can be long and comments extensive. Second, archive the web page using services like archive.today or Wayback Machine. Note that these services capture only static content – comments and engagement metrics may not be fully preserved and should be screenshotted separately.
For Xiaohongshu specifically, always preserve the user’s unique ID found in their profile URL when viewed on a browser, which follows the format “user/profile/[unique ID]”. Users can change their display names, but this unique identifier remains constant, allowing you to track accounts over time even after name changes. This is critical for long-term investigations or when monitoring specific sources.

Xiaohongshu operates under the same legal and censorship constraints as all Chinese social media platforms, and researchers should approach it with appropriate caution. Content moderation is extensive: users who post about sensitive subjects risk having their content removed or their accounts suspended, and the platform is required to comply with government data requests. For researchers, this means the information you find represents only what has survived the censorship process.
That said, Xiaohongshu remains a remarkably rich resource for open-source research. Its strength lies precisely in its apolitical, lifestyle-oriented identity: while political discussion is suppressed, candid conversations about everyday life flourish. For journalists willing to invest in learning the platform’s rhythms, building Chinese-language search skills, and understanding its coded vocabularies, Xiaohongshu offers a window into how ordinary Chinese people talk among themselves – an area that remains largely untapped by international media.
Bellingcat is a non-profit and the ability to carry out our work is dependent on the kind support of individual donors. If you would like to support our work, you can do so here. You can also subscribe to our Patreon channel here. Subscribe to our Newsletter and follow us on Bluesky here, Instagram here, Reddit here and YouTube here.
The post Mining China’s ‘Little Red Book’ for Open Source Gold appeared first on bellingcat.