Steganography & Sabotage: Inside Pawn Storm’s PRISMEX Offensive Against NATO Logistics
The post Steganography & Sabotage: Inside Pawn Storm’s PRISMEX Offensive Against NATO Logistics appeared first on Daily CyberSecurity.

Microsoft today released updates to fix more than 50 security holes in its Windows operating systems and other software, including patches for a whopping six “zero-day” vulnerabilities that attackers are already exploiting in the wild.
![]()
Zero-day #1 this month is CVE-2026-21510, a security feature bypass vulnerability in Windows Shell wherein a single click on a malicious link can quietly bypass Windows protections and run attacker-controlled content without warning or consent dialogs. CVE-2026-21510 affects all currently supported versions of Windows.
The zero-day flaw CVE-2026-21513 is a security bypass bug targeting MSHTML, the proprietary engine of the default Web browser in Windows. CVE-2026-21514 is a related security feature bypass in Microsoft Word.
The zero-day CVE-2026-21533 allows local attackers to elevate their user privileges to “SYSTEM” level access in Windows Remote Desktop Services. CVE-2026-21519 is a zero-day elevation of privilege flaw in the Desktop Window Manager (DWM), a key component of Windows that organizes windows on a user’s screen. Microsoft fixed a different zero-day in DWM just last month.
The sixth zero-day is CVE-2026-21525, a potentially disruptive denial-of-service vulnerability in the Windows Remote Access Connection Manager, the service responsible for maintaining VPN connections to corporate networks.
Chris Goettl at Ivanti reminds us Microsoft has issued several out-of-band security updates since January’s Patch Tuesday. On January 17, Microsoft pushed a fix that resolved a credential prompt failure when attempting remote desktop or remote application connections. On January 26, Microsoft patched a zero-day security feature bypass vulnerability (CVE-2026-21509) in Microsoft Office.
Kev Breen at Immersive notes that this month’s Patch Tuesday includes several fixes for remote code execution vulnerabilities affecting GitHub Copilot and multiple integrated development environments (IDEs), including VS Code, Visual Studio, and JetBrains products. The relevant CVEs are CVE-2026-21516, CVE-2026-21523, and CVE-2026-21256.
Breen said the AI vulnerabilities Microsoft patched this month stem from a command injection flaw that can be triggered through prompt injection, or tricking the AI agent into doing something it shouldn’t — like executing malicious code or commands.
“Developers are high-value targets for threat actors, as they often have access to sensitive data such as API keys and secrets that function as keys to critical infrastructure, including privileged AWS or Azure API keys,” Breen said. “When organizations enable developers and automation pipelines to use LLMs and agentic AI, a malicious prompt can have significant impact. This does not mean organizations should stop using AI. It does mean developers should understand the risks, teams should clearly identify which systems and workflows have access to AI agents, and least-privilege principles should be applied to limit the blast radius if developer secrets are compromised.”
The SANS Internet Storm Center has a clickable breakdown of each individual fix this month from Microsoft, indexed by severity and CVSS score. Enterprise Windows admins involved in testing patches before rolling them out should keep an eye on askwoody.com, which often has the skinny on wonky updates. Please don’t neglect to back up your data if it has been a while since you’ve done that, and feel free to sound off in the comments if you experience problems installing any of these fixes.
Russia-linked group APT28 (aka UAC-0001, aka Fancy Bear, Pawn Storm, Sofacy Group, Sednit, BlueDelta, and STRONTIUM) is behind Operation Neusploit, a campaign that exploits a newly disclosed Microsoft Office vulnerability.
The APT28 group has been active since at least 2007 and it has targeted governments, militaries, and security organizations worldwide. The group was involved also in the string of attacks that targeted 2016 Presidential election.
The group operates out of military unity 26165 of the Russian General Staff Main Intelligence Directorate (GRU) 85th Main Special Service Center (GTsSS).
In January 2026, Zscaler ThreatLabz uncovered the campaign Operation Neusploit targeting Central and Eastern Europe. Threat actors targeted the vulnerability CVE-2026-21509, they used weaponized RTF files and localized lures to deploy MiniDoor, PixyNetLoader, and Covenant Grunt implants.
On January 26, Microsoft released out-of-band security updates to address an actively exploited Office zero-day vulnerability tracked as CVE-2026-21509. Zscaler reported in-the-wild exploitation on January 29, 2026.
The issue is a security feature bypass vulnerability that affects multiple Office versions, including Microsoft Office 2016, Microsoft Office 2019, Microsoft Office LTSC 2021, Microsoft Office LTSC 2024, and Microsoft 365 Apps for Enterprise.
“Reliance on untrusted inputs in a security decision in Microsoft Office allows an unauthorized attacker to bypass a security feature locally.” reads the advisory that confirms that the issue is actively exploited in the wild. “An attacker must send a user a malicious Office file and convince them to open it.”
The update addresses a flaw that bypasses OLE security protections in Microsoft 365 and Office, exposing users to vulnerable COM/OLE controls.
Microsoft confirmed that the Office Preview Pane is not affected and cannot be used as an attack vector. However, the tech giant did not disclose technical details about the attacks exploiting this vulnerability.
“In January 2026, ThreatLabz identified APT28 weaponizing CVE-2026-21509 to target users in Central and Eastern Europe, including Ukraine, Slovakia, and Romania.” reads the report published by Zscaler. “Social engineering lures were crafted in both English and localized languages, (Romanian, Slovak and Ukrainian) to target the users in the respective countries.”
The researchers detailed two attack chains in Operation Neusploit, both starting with a weaponized RTF exploiting CVE‑2026‑21509. One path drops MiniDoor, a malicious Outlook VBA project that lowers macro security and quietly forwards victims’ emails to attacker-controlled addresses.
“MiniDoor’s primary goal is to steal the user’s emails and forward them to the threat actor.” reads the report.
The second, more complex chain deploys PixyNetLoader, which sets persistence via COM hijacking and scheduled tasks, then loads a fake EhStorShell.dll.
“Similar to the first dropper variant, after successful exploitation of CVE-2026-21509, the attack chain downloads a tool that ThreatLabz named PixyNetLoader, which drops malicious components on the endpoint and sets up the Windows environment to start the infection chain.” states the report.
This DLL extracts hidden shellcode from a PNG using steganography, evades sandboxes, and runs a .NET Covenant Grunt implant in memory, abusing legitimate APIs for command-and-control.
ThreatLabz links the campaign to Russia‑aligned APT28 with high confidence. The targets match APT28’s past focus on Central and Eastern Europe, using Romanian, Ukrainian, and English lures. The tools include MiniDoor, a simplified NotDoor variant tied to APT28, while the infrastructure reuses Filen API C2 seen in earlier APT28 operations. The PixyNetLoader chain also mirrors prior campaigns, combining COM hijacking, DLL proxying, XOR‑encrypted strings, and PNG‑embedded Covenant Grunt shellcode.
“This campaign by the Russia-linked group APT28 targeted countries in Central Europe and Eastern Europe with specially crafted RTF files that exploit CVE-2026-21509, resulting in the deployment of MiniDoor and PixyNetLoader.” concludes the report. “ThreatLabz research highlights that APT28 continues to evolve its TTPs by weaponizing the latest vulnerabilities in popular and widely used applications such as Microsoft Office.”
Follow me on Twitter: @securityaffairs and Facebook and Mastodon
(SecurityAffairs – hacking, APT28)

Right after Microsoft disclosed an actively exploited Office zero-day (CVE-2026-21509) on January 26, 2026, CERT-UA reported UAC-0001 (APT28) leveraging the vulnerability in the wild. The russia-backed threat actor targeted organizations in Ukraine and the EU with malicious Office documents, and metadata shows one sample was created on January 27 at 07:43 UTC, illustrating the rapid weaponization of CVE-2026-21509.
APT28 (UAC-0001) has a long record of conducting cyber operations aligned with russian state interests, with a persistent focus on Ukraine and its allied partners. Ukraine frequently serves as an initial testing environment for newly developed tactics, techniques, and procedures that are later scaled to broader international targets.
The latest UAC-0001 campaign in the limelight follows the same pattern. According to CERT-UA#19542, UAC-0001 targeted Ukrainian state bodies with malicious Office documents exploiting CVE-2026-21509 to deploy the COVENANT framework. The same attack pattern was later observed against EU organizations, demonstrating rapid operational expansion beyond Ukraine.
Sign up for the SOC Prime Platform to proactively defend your organization against UAC-0001 (APT28) attacks exploiting CVE-2026-21509. Just press Explore Detections below and access a relevant detection rule stack, enriched with AI-native CTI, mapped to the MITRE ATT&CK® framework, and compatible with a wide range of SIEM, EDR, and Data Lake technologies.
Security experts can also use the “CERT-UA#19542” tag based on the relevant CERT-UA alert identifier to search for the detection stack directly and track any content changes. For more rules to detect attacks related to the UAC-0001 adversary activity, security teams can search the Threat Detection Marketplace library leveraging the “UAC-0001” or “APT28” tags based on the group identifier, as well as the relevant “CVE-2026-21509” tag addressing the Microsoft Office zero-day exploitation.
Additionally, users can refer to a dedicated Active Threats item on the UAC-0001 (APT28) latest attacks to access the AI summary, related detection rules, simulations, and the attack flow in one place.
Security teams can also rely on Uncoder AI to create detections from raw threat reports, document and optimize code, and generate Attack Flows. Additionally, cyber defenders can easily convert IOCs from the latest CERT-UA#19542 alert into performance-optimized queries compatible with your security stack.
![]()
In late January 2026, CERT-UA observed a series of targeted cyber attacks attributed to UAC-0001 (APT28) that leveraged an actively exploited Microsoft Office vulnerability tracked as CVE-2026-21509. The malicious activity emerged shortly after Microsoft publicly disclosed the flaw and was initially directed at Ukrainian government entities before expanding to organizations across the European Union.
To establish initial access, attackers distributed specially crafted Microsoft Word documents exploiting CVE-2026-21509. One document, titled “Consultation_Topics_Ukraine(Final).doc,” referenced COREPER, the Committee of Permanent Representatives of the EU, which prepares decisions and coordinates policy among EU member states. Although the file became publicly accessible on January 29, metadata analysis showed it had been created on January 27 (one day after Microsoft’s advisory), indicating rapid weaponization of the vulnerability.
In parallel, CERT-UA received reports of phishing emails impersonating official correspondence from the Ukrainian Hydrometeorological Center. These messages, sent to more than 60 recipients primarily within central executive authorities of Ukraine, contained malicious DOC attachments. When opened in Microsoft Office, the documents established a network connection to an external resource over WebDAV and downloaded a shortcut file containing code designed to retrieve and launch an executable file.
Successful execution of the downloaded payload results in the creation of a malicious DLL file, EhStoreShell.dll, masquerading as the legitimate Enhanced Storage Shell Extension library, and an image file (SplashScreen.png) containing shellcode. The attack also modifies the Windows registry path for CLSID {D9144DCD-E998-4ECA-AB6A-DCD83CCBA16D}, implementing COM hijacking, and creates a scheduled task named OneDriveHealth.
Scheduled execution of the task causes the explorer.exe process to terminate and restart, which (due to the COM hijacking) ensures the loading of EhStoreShell.dll. The DLL executes shellcode from the image file, ultimately resulting in the launch of the COVENANT framework. Command-and-control communications for COVENANT relied on legitimate cloud storage infrastructure provided by Filen (filen.io).
Toward the end of January 2026, CERT-UA identified additional documents using the same exploit chain and delivery mechanisms in attacks against EU-based organizations. Technical overlaps in document structure, embedded URLs, and supporting infrastructure suggest these incidents were part of a coordinated UAC-0001 (APT28) campaign, demonstrating the rapid scaling of the operation beyond its initial Ukrainian targets.
Given the active exploitation of a Microsoft Office zero-day and the challenges many organizations face in promptly applying patches or mitigations, further abuse of CVE-2026-21509 is expected in the near term.
To reduce the attack surface, organizations should implement the mitigation measures outlined in Microsoft’s advisory, including recommended Windows registry configurations. In addition, as UAC-0001 (APT28) leverages legitimate Filen cloud infrastructure for COVENANT command-and-control operations, network interactions with Filen-related domains and IP addresses should be restricted or placed under enhanced monitoring.
Additionally, security experts can rely on SOC Prime’s AI-Native Detection Intelligence Platform, which equips SOC teams with cutting-edge technologies and top cybersecurity expertise to stay ahead of APT28 attacks while maintaining operational effectiveness.
Leveraging MITRE ATT&CK offers in-depth insight into the latest UAC-0001 (APT28) attacks leveraging CVE-2026-21509 exploit to target Ukrainian and EU entities. The table below displays all relevant Sigma rules mapped to the associated ATT&CK tactics, techniques, and sub-techniques. Tactics Techniques Sigma Rule Persistence Scheduled Task/Job: Scheduled Task (T1053.005) Event Triggered Execution: Component Object Model Hijacking (T1546.015) Defense Evasion Masquerading: Match Legitimate Resource Name or Location (T1036.005) Command and Control Application Layer Protocol: Web Protocols (T1071.001) Ingress Tool Transfer (T1105) Impact Service Stop (T1489)
The post UAC-0001 (APT28) Attack Detection: russia-Backed Actor Actively Exploits CVE-2026-21509 Targeting Ukraine and the EU appeared first on SOC Prime.
Microsoft issued an emergency patch for a high-severity zero-day vulnerability in Office that allows attackers to bypass document security checks and is being exploited in the wild via malicious files.
Microsoft pushed the emergency patch for the zero‑day, tracked as CVE-2026-21509, and classified it as a “Microsoft Office Security Feature Bypass Vulnerability” with a CVSS score of 7.8 out of 10.
The flaw allows attackers to bypass Object Linking and Embedding (OLE) mitigations that are designed to block unsafe COM/OLE controls inside Office documents. This means a malicious attachment could infect a PC despite built-in protections.
In a real-life scenario, an attacker creates a fake Word, Excel, or PowerPoint file containing hidden “mini‑programs” or special objects. They can run code and do other things on the affected computer. Normally, Office has safety checks that would block those mini-programs because they’re risky.
However, the vulnerability allows the attacker to tweak the file’s structure and hidden information in a way that tricks Office into thinking the dangerous mini‑program inside the document is harmless. As a result, Office skips the usual security checks and allows the hidden code to run.
As code to test the bypass is publicly available, increasing the risk of exploitation, users are under urgent advice to apply the patch.

What you need to do depends on which version of Office you’re using.
The affected products include Microsoft Office 2016, 2019, LTSC 2021, LTSC 2024, and Microsoft 365 Apps (both 32‑bit and 64‑bit).
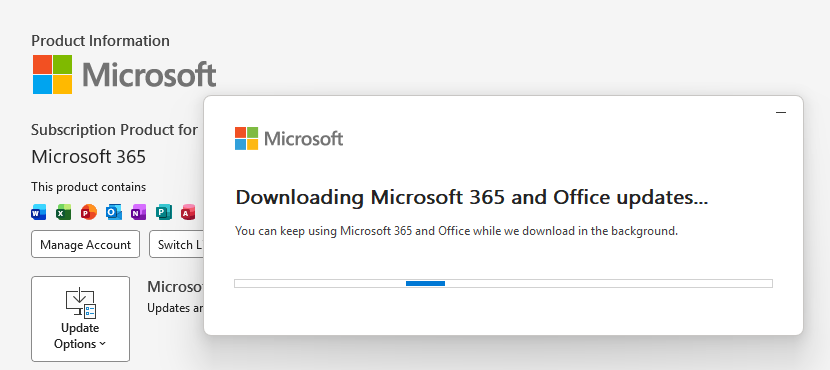
Office 2021 and later are protected via a server‑side change once Office is restarted. To apply it, close all Office apps and restart them.
Office 2016 and 2019 require a manual update. Run Windows Update with the option to update other Microsoft products turned on.
If you’re running build 16.0.10417.20095 or higher, no action is required. You can check your build number by opening any Office app, going to your account page, and selecting About for whichever application you have open. Make sure the build number at the top reads 16.0.10417.20095 or higher.
What always helps:
We don’t just report on threats—we remove them
Cybersecurity risks should never spread beyond a headline. Keep threats off your devices by downloading Malwarebytes today.

Shortly after its January Patch Tuesday release, addressing 114 vulnerabilities, including a zero-day in Windows Desktop Manager (CVE-2026-20805), Microsoft rushed out an emergency out-of-band update to fix another bug under active exploitation. This time, attackers are targeting CVE-2026-21509, a Microsoft Office zero-day that allows threat actors to bypass built-in security features.
In view of the exploitation cases confirmed by Microsoft, the flaw has been promptly added to the CISA’s Known Exploited Vulnerabilities (KEV) catalog, requiring US federal civilian agencies to patch it by February 16, 2026.
Microsoft products continue to be a juicy target for zero-day exploits, with 41 vulnerabilities identified as zero-days last year, 24 of which were leveraged for in-the-wild attacks, according to Tenable. The Windows operating system and Office components remain the primary attack vectors, with this trend persisting into 2026.
Sign up for SOC Prime Platform, aggregating the world’s largest detection intelligence dataset and offering a complete product suite that empowers SOC teams to seamlessly handle everything from detection to simulation. The Platform features a large collection of rules addressing critical exploits and cyber threats of any sophistication. Just press Explore Detections and immediately drill down to a relevant detection stack filtered by “CVE” tag.
All rules are mapped to the latest MITRE ATT&CK® framework v18.1 and are compatible with multiple SIEM, EDR, and Data Lake platforms. Additionally, each rule comes packed with broad metadata, including CTI references, attack flows, audit configurations, and more.
Cyber defenders can also use Uncoder AI to streamline their detection engineering routine. Turn raw threat reports into actionable behavior rules, test your detection logic, map out attack flows, turn IOCs into hunting queries, or instantly translate detection code across languages backed by the power of AI and deep cybersecurity expertise behind every step.
On January 26, 2026, Microsoft issued an advisory detailing a security feature bypass vulnerability affecting Microsoft Office 2016, Microsoft Office 2019, Microsoft Office LTSC 2021, Microsoft Office LTSC 2024, and Microsoft 365 Apps for Enterprise.
The security issue arises from Microsoft Office’s reliance on untrusted inputs in security decisions. This allows unauthenticated local hackers to bypass a security feature. Specifically, CVE-2026-21509 allows threat actors to bypass OLE mitigations in Microsoft 365 and Office, exposing users to vulnerable COM/OLE controls.
Exploitation typically involves convincing a user to open a malicious Office file sent by the attacker. While Microsoft notes that the Preview Pane is not directly an attack vector, the vulnerability can still be abused through low-complexity, user-interaction attacks.
Microsoft credits its internal cybersecurity research teams for vulnerability disclosure, sharing very little information on the exploitation cases. Security advisory only confirms exploitation attempts in the wild. Yet, a public PoC exploit is not available, suggesting that a limited number of threat actors might have leveraged the flaw in targeted campaigns.
Notably, Office 2021 and later users are automatically protected through a service-side fix after restarting the applications. Office 2016 and 2019 require either installing the upcoming security update or manually applying a registry change to block vulnerable COM/OLE controls. This involves adding a specific subkey under the COM Compatibility registry node and setting a Compatibility Flags DWORD value to 400. Users should back up the registry before making any changes and restart Office for the protections to take effect.
Organizations that rely on corresponding Microsoft Office products are urged to apply the patches immediately or follow the mitigation steps described in the advisory. Also, by enhancing the defenses with SOC Prime’s AI-Native Detection Intelligence Platform, SOC teams can source detection content from the largest and up-to-date repository, seamlessly adopt the full pipeline from detection to simulation into their security processes, orchestrate workflows in their natural language, and smoothly navigate the ever-changing threat landscape while strengthening defenses at scale.
The post CVE-2026-21509: Actively Exploited Microsoft Office Zero-Day Forces Emergency Patch appeared first on SOC Prime.