White House Considers Mandatory Federal Vetting for All New AI Models
The post White House Considers Mandatory Federal Vetting for All New AI Models appeared first on Daily CyberSecurity.
Google expands its “Results about you” tool to remove sensitive IDs and explicit images from Search, strengthening privacy protections amid rising identity theft.
The post Google Expands ‘Results About You’ to Shield IDs, Fight Deepfake Abuse appeared first on TechRepublic.
Em 2025, pesquisadores de segurança cibernética descobriram vários bancos de dados abertos pertencentes a diversas ferramentas de geração de imagens de IA. Esse fato por si só faz você se perguntar o quanto as startups de IA se preocupam com a privacidade e a segurança dos dados de seus usuários. Mas a natureza do conteúdo nesses bancos de dados é muito mais alarmante.
Um grande número de imagens geradas nesses bancos de dados eram imagens de mulheres em lingerie ou totalmente nuas. Algumas foram claramente criadas a partir de fotos de crianças ou destinadas a fazer mulheres adultas parecerem mais jovens (e despidas). Por fim, a parte mais perturbadora: algumas imagens pornográficas foram geradas a partir de fotos completamente inocentes de pessoas reais, provavelmente tiradas de mídias sociais.
Neste post, vamos explicar o que é sextorsão e por que, graças às ferramentas de IA, qualquer pessoa pode se tornar uma vítima. Detalhamos o conteúdo desses bancos de dados abertos e fornecemos conselhos sobre como evitar ser vítima de sextorsão na era da IA.
A extorsão sexual on-line se tornou tão comum que ganhou seu próprio nome global: sextorsão (uma junção de sexo e extorsão). Já detalhamos seus vários tipos em nosso post, Cinquenta tons de sextorsão. Para recapitular, essa forma de chantagem envolve a ameaça de publicar imagens ou vídeos íntimos para coagir a vítima a realizar determinadas ações ou extorquir dinheiro dela.
Antes, as vítimas de sextorsão eram tipicamente trabalhadores da indústria adulta ou indivíduos que compartilhavam conteúdo íntimo com pessoas não confiáveis.
No entanto, o rápido avanço da inteligência artificial, em especial da tecnologia de conversão de texto em imagem, revolucionou essa prática. Agora, literalmente, qualquer pessoa que publicou suas fotos mais inocentes pode se tornar vítima de sextorsão. Isso ocorre porque a IA generativa torna possível despir pessoas de forma rápida, fácil e convincente em qualquer imagem digital ou adicionar um corpo nu gerado à cabeça de alguém em questão de segundos.
É claro que esse tipo de falsificação era possível antes da IA, mas exigia longas horas de trabalho meticuloso no Photoshop. Agora, basta descrever o resultado desejado em palavras.
Para piorar a situação, muitos serviços generativos de IA não se preocupam muito em proteger o conteúdo criado por intermédio deles. Como mencionado, no ano passado os pesquisadores descobriram pelo menos três bancos de dados acessíveis ao público pertencentes a esses serviços. Isso significa que os nudes gerados dentro deles estavam disponíveis não apenas para o usuário que os criou, mas para qualquer pessoa na Internet.
Em outubro de 2025, o pesquisador de segurança cibernética Jeremiah Fowler descobriu um banco de dados aberto contendo mais de um milhão de imagens e vídeos gerados por IA. Segundo o pesquisador, a esmagadora maioria desse conteúdo era de natureza pornográfica. O banco de dados não estava criptografado nem protegido por senha, o que significa que qualquer usuário da Internet poderia acessá-lo.
O nome do banco de dados e as marcas d’água em algumas imagens levaram Fowler a acreditar que sua fonte era a empresa americana SocialBook, que oferece serviços para influenciadores e de marketing digital. O site da empresa também fornece acesso a ferramentas para gerar imagens e conteúdo usando IA.
No entanto, uma análise mais aprofundada revelou que o próprio SocialBook não estava gerando diretamente esse conteúdo. Os links dentro da interface do serviço levavam a produtos de terceiros: os serviços de IA MagicEdit e DreamPal, que eram as ferramentas usadas para criar as imagens. Essas ferramentas permitiam que os usuários gerassem imagens a partir de descrições de texto, editassem fotos carregadas e executassem várias manipulações visuais, incluindo criação de conteúdo explícito e troca de rosto.
O vazamento estava vinculado a essas ferramentas específicas, e o banco de dados continha o produto de seu trabalho, incluindo imagens geradas e editadas por IA. Uma parte das imagens levou o pesquisador a suspeitar que elas foram enviadas para a IA como referências para a criação de imagens provocativas.
Fowler afirma que cerca de 10 mil fotos eram adicionadas ao banco de dados todos os dias. O SocialBook nega qualquer conexão com o banco de dados. Depois que o pesquisador informou a empresa sobre o vazamento, várias páginas no site do SocialBook que antes mencionavam MagicEdit e DreamPal ficaram inacessíveis e começaram a retornar erros.
Ambos os serviços, MagicEdit e DreamPal, foram inicialmente comercializados como ferramentas para experimentação visual interativa e orientada pelo usuário com imagens e personagens de arte. Infelizmente, uma parte significativa desses recursos estava diretamente ligada à criação de conteúdo sexualizado.
Por exemplo, o MagicEdit oferecia uma ferramenta para trocas de roupas virtuais com tecnologia de IA, bem como um conjunto de estilos que tornavam as imagens de mulheres mais reveladoras após o processamento, como substituir roupas cotidianas por roupas de banho ou lingerie. Seus materiais promocionais prometiam transformar um visual comum em sexy em segundos.
O DreamPal, por sua vez, foi inicialmente posicionado como um bate-papo de role-playing baseado em IA e foi ainda mais explícito sobre seu posicionamento orientado para adultos. O site se oferecia para criar uma namorada de IA ideal, com determinadas páginas mencionando diretamente o conteúdo erótico. As FAQ também mencionavam que os filtros para conteúdo explícito em bate-papos haviam sido desativados para não limitar as fantasias mais íntimas dos usuários.
Ambos os serviços suspenderam as operações. No momento da redação deste artigo, o site DreamPal retornou um erro, enquanto o MagicEdit parecia disponível novamente. Seus aplicativos foram removidos da App Store e do Google Play.
Jeremiah Fowler diz que, no início de 2025, ele descobriu mais dois bancos de dados abertos contendo imagens geradas por IA. Um deles pertencia ao site sul-coreano GenNomis e continha 95 mil entradas, uma parte substancial das quais eram imagens de pessoas “despidas”. Entre outras coisas, o banco de dados incluía imagens com versões infantis de celebridades: as cantoras americanas Ariana Grande e Beyoncé, bem como a estrela de reality shows Kim Kardashian.
À luz de incidentes como esses, fica claro que os riscos associados à sextorsão não se limitam mais a mensagens privadas ou à troca de conteúdo íntimo. Na era da IA generativa, até mesmo fotos comuns, quando postadas publicamente, podem ser usadas na criação de conteúdo comprometedor.
Esse problema é especialmente relevante para as mulheres, mas os homens também não devem ficar muito à vontade: o famoso esquema de chantagem de “invadi seu computador e usei a webcam para fazer vídeos de você navegando em sites adultos” pode atingir um nível totalmente novo de persuasão, graças à geração de fotos e vídeos pelas ferramentas de IA.
Portanto, proteger sua privacidade nas mídias sociais e controlar quais dados sobre você estão disponíveis publicamente tornam-se medidas essenciais para proteger sua reputação e tranquilidade. Para evitar que suas fotos sejam usadas para criar conteúdo questionável gerado por IA, recomendamos tornar todos os seus perfis de mídia social o mais privados possível, afinal, eles podem ser a fonte de imagens dos nudes gerados por IA.
Já publicamos vários guias detalhados sobre como reduzir sua pegada digital on-line ou até mesmo remover seus dados da Internet; como impedir que data brokers compilem dossiês sobre você e proteger-se de abusos envolvendo imagens íntimas.
Além disso, temos um serviço dedicado, Privacy Checker: perfeito para quem deseja uma abordagem rápida, mas sistemática, das configurações de privacidade em todos os lugares possíveis. Ele compila guias passo a passo para proteger contas em mídias sociais e serviços on-line em todas as principais plataformas.
E para garantir a segurança e a privacidade dos dados da sua criança, o Safe Kids pode ajudar: ele permite que os pais monitorem em quais mídias sociais as crianças passam o tempo. A partir daí, você pode ajudá-las a ajustar as configurações de privacidade das contas para que as fotos postadas não sejam usadas para criar conteúdo impróprio. Explorem juntos nosso guia para a segurança on-line de crianças e, se sua criança sonha em se tornar um blogueiro popular, Explorem juntos nosso guia para a segurança on-line de crianças e, se sua criança sonha em se tornar um blogueiro popular, converse com ela sobre o nosso guia passo a passo de segurança cibernética para aspirantes a blogueiros.





Content warning: This article contains descriptions of non-consensual sexual imagery.
Depending on which of his social media profiles you were looking at, Mark Resan was either a marketing lead at Google or working for a dental implant company, a human resources company and a business software firm – all at the same time.

But a Bellingcat investigation has found that the Hungarian national is the key figure behind, and the likely owner of, at least two deepfake porn websites – RefacePorn and DeepfakePorn – that until recently were selling paid subscriptions.
There is no question about the nature of these websites. RefacePorn’s landing page shows an explicit video of a woman performing a sexual act. As the video plays, her face is replaced with a variety of other women’s faces. The text above declares: “Face swap deepfake porn. Upload your face!”
Deepfake porn sites such as these, which use artificial intelligence to create sexually explicit images and videos – usually without the consent of those whose faces or bodies are featured – have proliferated at an alarming rate in recent years. The impact on victims has been described as “life-shattering”, with the mental health effects similar to those reported by victims of sexual assault.
While the technology to make these synthetic images is not new, the rise of mainstream AI image generator tools and “Nudify” apps has made it more widely available to people without deep technical expertise. Earlier this year, New Zealand MP Laura McClure held up an AI-generated nude of herself in parliament, describing how it took her less than five minutes to create after a quick Google search.
A 2024 study by the My Image My Choice campaign found that there was a 1,780 percent increase in sexually explicit deepfakes last year compared to 2019. Almost all (99 percent) of victims were women, according to a 2023 study by Security Hero.

The creation of such images and videos is now illegal in a few countries, including the US and the UK, but legislation has not caught up in many others, and the owners of platforms that enable this content often face no repercussions. In May 2024, the EU passed a directive which mandates that member states – including Hungary, where Resan resides – criminalise the creation and distribution of non-consensual sexual deepfakes by June 2027.
Alexios Mantzarlis, co-founder of Indicator, a news site that focuses on digital deception, said his publication estimates that deepfake porn sites likely make millions of dollars a year.
“The incentive system will continue to exist until the tools become too toxic to handle for domain hosts and content delivery networks,” added Mantzarlis, who is also the director of the Security, Trust and Safety Initiative at Cornell Tech.
Bellingcat’s investigation into RefacePorn and DeepfakePorn – which spanned corporate registries, domain name registrations, payment redirect sites, website code and leaked data – led us back to Resan.
By simulating the purchase of subscriptions on these websites, Bellingcat was led through a series of redirects to a payments dashboard by Peerwallet, a payment processor that recorded more than US$331,000 in sales from July 2024 to August 2025 by Dorocron LLP. Dorocron is a Canadian-registered company whose main – if not sole – source of income appeared to be from paid subscriptions to these sites. The real amount is likely higher, as this was just one of several payment processors the websites have used.
Subscribe to our newsletter for first access to our published content and events that our staff and contributors are involved with, including interviews and training workshops.
Dorocron LLP did not respond to multiple requests for comment via email, and calls to the number listed on sites that had the company’s details in their legal information sections went unanswered.
Resan is the only person who appears to have been publicly associated with Dorocron LLP, and he is also the sole director of a UK-registered company, Facitic Ltd, that registered the domain of RefacePorn. Resan did not respond to multiple requests for comment sent via email over the past two weeks. Multiple emails and phone calls to Facitic Ltd also went unanswered.
However, days after we first reached out to Resan, his LinkedIn and X profiles were deleted, and his previously public Facebook profile was either deleted or made private. Both RefacePorn and DeepfakePorn also became inaccessible, displaying an error message that said “this site can’t be reached”.
Archives of RefacePorn and DeepfakePorn, which were previously available on the Internet Archive’s Wayback Machine, have also now been excluded from the archive. The Internet Archive told Bellingcat it processed exclusion requests submitted by someone with rights to both sites on Dec. 5.
Like other websites Bellingcat has investigated, RefacePorn’s ownership was hidden behind a network of website domains, fake websites used to redirect payments, and international business registries.
Using the tool DNSlytics, we examined the Google tag history on RefacePorn and found a tag that was also used on DeepfakePorn, as well as a website called facitic.com.
Google Analytics tags are small pieces of unique code that developers can place in the backend of a website to track its analytics. Each code is unique to a specific user, who can use the same tag across multiple websites.
Both RefacePorn and DeepfakePorn offer tiered subscription packages with similar names and prices based on the number of deepfakes that could be generated and the level of support.
When simulating a purchase of one of these packages – without actually completing payment – on DeepfakePorn, we received a link to make a payment hosted through the domain “remakerai.me”. Similarly, a mock purchase on RefacePorn pointed us to a payment link on “airemaker.me”. Bellingcat has observed the use of redirects, which can be used to obscure payments, by other deepfake porn sites. Many payment processors, including Paypal and Stripe, have restrictions on buying or selling sexually oriented online content.
Payment processors often block payments that come from websites making deepfake pornography.
Using a redirect site hides the original site from the payment processor, making it harder to block.
Despite this, payment processors sometimes manage to block the redirect site.
But If one redirect site is blocked, the site owner can quickly switch to another redirect site that isn’t blocked.
Graphic: Galen Reich
The redirected payment links hosted on airemaker.me and remakerai.me offered several payment options including Paypal, credit cards and cryptocurrencies. Bellingcat selected the credit card option, and in both cases was emailed a link to complete the purchase on a payment platform called Peerwallet. This email included a link to the seller’s profile, Dorocron LLP.
This profile showed the funds received by the seller, which totalled more than $331,000 as of August 2025. This income was related to 16,264 sales. According to this dashboard, Dorocron LLP had been a member of Peerwallet since July 22, 2024, meaning these sales all occurred over the past year.

RefacePorn has been active since at least May 2022, according to promotional posts by an Instagram account with the username “Dorocron2323” and the account name “Hassler Mark”. Social media accounts for RefacePorn were also created on X and Facebook in May 2022.

While the transactions on Peerwallet were not broken down by domain, two were the payment redirect sites for the deepfake porn sites we investigated. Bellingcat’s review of the 21 “approved domains” listed on this profile found no evidence that payments were ever accepted through the other sites.
Short-lived, “disposable” domains are known to be used by bad actors to evade detection, presenting a moving target for payment processors and authorities. As of publication, both airemaker.me and remakerai.me are no longer accessible. But in the course of the investigation, we observed RefacePorn and DeepfakePorn’s payment links redirecting to other third-party sites, before the sites went offline.

Of the 21 domains on Dorocron LLP’s Peerwallet profile, only two were still accessible as of the end of November, with the rest either down due to expired domains or server issues, displaying generic domain parking pages, or requiring a login to view. Though almost all of the sites had their registration information redacted, Resan was listed as the most recent registrant for one of the expired domains.
The two sites still accessible listed a variety of products, including eBooks and digital products. Both had almost identical products and templates, and listed Dorocron LLP under their company information in their footers.
Bellingcat tried to check out items on each of the sites, and in both cases was prompted to log in. It was, however, impossible to register an account, and when we tried with an active email address we were redirected to a login page saying that the email address was “unknown”.
Archived screengrabs of some of the sites that now have expired domains or require a login to view showed that many of them followed the same format, selling eBooks and video courses with “resell rights”.
Peerwallet told Bellingcat in September that Dorocron LLP was “not approved” to sell deepfake porn, and that it was looking into the issue. However, when Bellingcat asked for an update in November, Peerwallet appeared to have closed down. Emails to the payment processor’s founder have also gone unanswered.
Dorocron LLP was registered in British Columbia, Canada in March 2022. We were unable to verify if Resan’s name was on the corporate records as information on company owners or directors in British Columbia is restricted to law enforcement and other officials.
However, Resan’s name has been used to register at least 13 sites alongside an email bearing Dorocron’s name from as far back as 2013, nine years before Dorocron was registered in Canada. The earliest domain registration, from 2013, included the name of a now-dissolved UK-registered company called “Webnaser LTD”, whose registration documents also cite Resan as the sole director.

A leak found on data breach site Intelx.io shows that an almost identical password (with different capitalisation of some letters) was used to log into this “dorocron” Gmail account and a Netflix account associated with Resan’s personal email address. This password was also used to log into web domain registry GoDaddy using RefacePorn’s support email address.
Leaked passwords on Intelx.io revealed another link between Resan and DeepfakePorn: an email with the username “resanmark” was used to log into DeepfakePorn’s website, with a password containing his birth year. In all, we found four unique passwords that were reused between Resan’s personal emails, the Dorocron emails, and a support email for RefacePorn. These four passwords include either Resan’s name or the date or year of his birth.
Resan also posted two job listings from his now-deleted LinkedIn account about a year ago, for a full-stack web developer and a WordPress developer at Dorocron LLP. In the web developer listing, he described the company as “developing and applying revolutionary AI technologies” and said the job would have “high wages”. We could not find any other individual with a public association to Dorocron LLP on LinkedIn or elsewhere.

Your donations directly contribute to our ability to publish groundbreaking investigations and uncover wrongdoing around the world.
Aside from his links to Dorocron LLP, Resan is also the sole director and person with significant control of Facitic Ltd, a UK-registered company which was listed as the registrant for RefacePorn.
Using DomainTools, we were able to see the historical registrant information in a WHOIS lookup of the site’s domain registration. When we checked this in August 2025, we were able to see that, as of June 2025, Facitic Ltd was the registered owner of RefacePorn. This information was later redacted – as it is for other sites linked to Resan such as DeepfakePorn.
ICANN, which regulates websites, requires domain name providers to verify the accuracy of their customers’ details, including the registrant's name and contact details. Such details are publicly visible by default, but can be anonymised using paid privacy services.
The UK registration for Facitic Ltd lists Resan’s country of residence as Dubai, while the registration for another UK company he registered – which was also listed as the owner of some of the now-expired approved domains on Dorocron LLP’s Peerwallet profile – states that he resides in Cyprus. Meanwhile, Resan’s social media accounts stated that he lives in Hungary. On Peerwallet’s dashboard, the primary user of Dorocron is listed as being based in Hungary.
It is unclear if Resan actually holds positions in any of the six companies he listed himself as working at on his Facebook and LinkedIn profiles. Bellingcat has reached out to these companies to check, but has not received any replies as of publication.
Some of the connections Bellingcat found between RefacePorn and Mark Resan:

On Nov. 10, 2025, a few weeks before we contacted him, Resan applied for Facitic Ltd to be struck off the UK companies register. Based on Resan’s filings, Facitic Ltd was incorporated with an initial capital of £100 in January 2024, and there has been no recorded change in its accounts since.
This comes as UK regulator Ofcom cracks down on websites associated with UK businesses offering AI-powered nudify services. On Oct. 23, Ofcom imposed a £50,000 fine on UK-registered company Itai Tech Ltd, which has been linked to some of the biggest deepfake pornography sites in the world, for failing to prevent children from accessing pornographic content.
It is unclear what triggered Resan to file to dissolve the company, and he did not respond to Bellingcat’s query about this.
The websites linked to Resan are not among the largest in the deepfake porn industry. A similar but much larger site that Bellingcat has investigated, MrDeepFakes, received millions of visits each month. Bellingcat and its partners Tjekdet, Politiken and CBC exposed the site’s key administrator David Do in May, with MrDeepFakes going offline after we reached out to Do for comment.
In comparison, RefacePorn and DeepfakePorn received about 91,000 and 154,000 visits in October, according to digital marketing platform SemRush. But their smaller size does not mean they can’t cause significant harm.
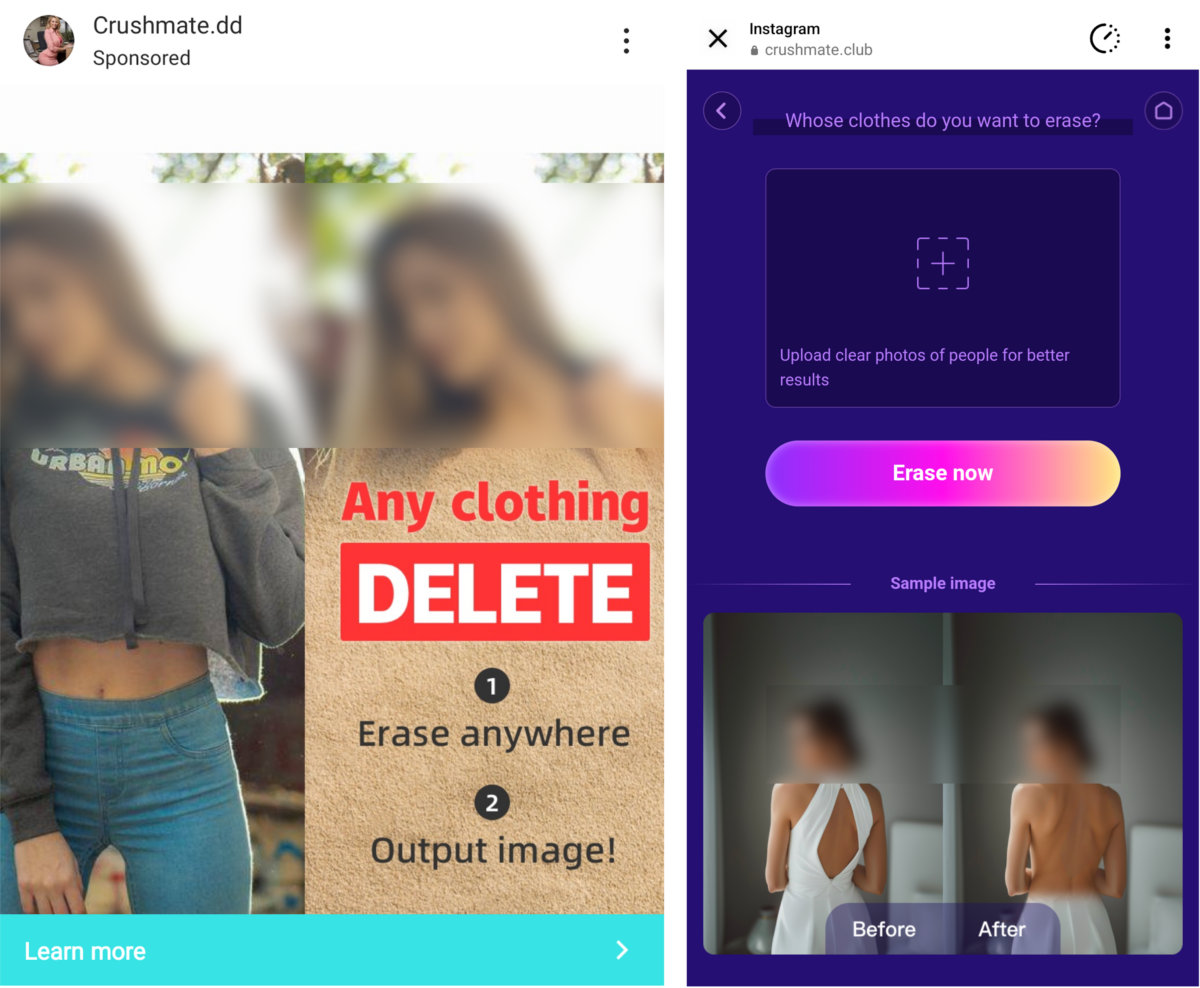
Mantzarlis, of the news site Indicator, said there were “smaller players” taking bigger risks around regulation, such as “Crush AI”, a group of Chinese-owned apps that bypassed Meta’s moderation rules to run 25,000 ads on Facebook and Instagram before the social media giant sued them.
“These smaller players are often the ones that are more actively trying to stand out on social media to catch up with the bigger ones,” Mantzarlis said.
In the course of our investigation, we ran tests using the free features on RefacePorn to determine if there were any restrictions on images that could be uploaded on the website.
Without actually generating the content, we uploaded AI-generated images of adult women and underage girls. Unlike on other websites we have tested, which have added the bare minimum of checks to prevent uploading images depicting children, there was no restriction or evidence of age-related safeguards on RefacePorn.
While there aren’t laws in Hungary explicitly prohibiting deepfake porn, the possession, creation and distribution of sexually explicit images of minors is illegal.
“As the more established websites come under sustained regulatory pressure and others get litigated into oblivion, the minnows are ready to try and capture market share,” Mantzarlis said.
And while some sites such as RefacePorn and DeepfakePorn may fold in the face of public scrutiny, others continue to operate, unchecked and easily accessible, online.
“These websites are eminently replaceable and there's no reason to believe that there is any form of ‘brand loyalty’,” Mantzarlis said. “Perpetrators are going to search for ‘nudify’ or click on an ad and go to whatever tool does the job.”
Melissa Zhu contributed to this report.
Bellingcat is a non-profit and the ability to carry out our work is dependent on the kind support of individual donors. If you would like to support our work, you can do so here. You can also subscribe to our Patreon channel here. Subscribe to our Newsletter and follow us on Bluesky here and Mastodon here.
The post Profiting From Exploitation: How We Found the Man Behind Two Deepfake Porn Sites appeared first on bellingcat.
Neste ano, o Brasil sofreu mais de 315 bilhões de tentativas de ataque cibernético apenas no primeiro semestre — número que representa cerca de 84% de todo o tráfego malicioso registrado na América Latina no período, de acordo com um levantamento da Fortinet divulgado em agosto passado. Com adversários fazendo uso crescente de IA para conduzir campanhas de phishing, ataques DDoS e exploração de vulnerabilidades em ambientes híbridos e multicloud, líderes de segurança corporativa se veem diante de uma encruzilhada: manter o SOC (Security Operations Center) da forma como está ou apostar em novas tecnologias e formas de trabalho que respondam à nova realidade.
Grupos criminosos adotam táticas avançadas e combinam técnicas de Advanced Persistent Threat (APT) com ferramentas de IA para driblar as defesas tradicionais. Golpes que envolvem deepfakes ou phishing automatizado por IA tornam cada vez mais difícil distinguir o legítimo do malicioso. Ao mesmo tempo, a superfície de ataque das organizações se expandiu dramaticamente. Com ambientes de TI híbridos e multicloud, centenas de novos serviços e integrações são adicionados constantemente aos ecossistemas corporativos, abrindo brechas que muitas vezes são difíceis de monitorar.
O problema é que grande parte dos SOCs atuais foi concebida para um contexto em que as ameaças eram baseadas em assinatura e o volume de eventos era controlável. Hoje, porém, a multiplicação de fontes de telemetria, tais como endpoints, nuvens, APIs, identidades, dispositivos IoT e aplicações SaaS, faz com que o volume de logs cresça de forma exponencial.
Não se trata apenas de mais dados, mas de dados de naturezas distintas, com diferentes formatos, níveis de granularidade e relevância operacional. Ferramentas modernas de detecção e monitoramento, como EDRs, XDRs e soluções de observabilidade, coletam informações em tempo real e geram fluxos contínuos de telemetria que precisam ser correlacionados com ameaças conhecidas e comportamentos anômalos. Sem uma arquitetura de dados e automação adequadas, esse ecossistema torna-se difícil de orquestrar – e o SOC passa a lidar menos com ruído e mais com complexidade analítica. O desafio, portanto, deixou de ser filtrar falsos positivos e passou a ser transformar grandes volumes de logs em inteligência acionável com velocidade e contexto.
E, quando os adversários passam a empregar IA para criar malwares praticamente indetectáveis, um SOC calcado apenas em esforço humano não consegue escalar na mesma proporção do risco. O resultado é um descompasso perigoso entre a capacidade defensiva e a velocidade com que as ameaças modernas atuam, evidenciando que manter o status quo não é mais sustentável.
Uma das principais transformações em curso é a adoção do modelo de SOC as a Service, que redefine a forma como as empresas estruturam sua defesa cibernética. Diferente do modelo híbrido ou totalmente interno, o SOCaaS oferece monitoramento, detecção e resposta a incidentes 24×7 por meio de uma plataforma escalável e baseada em nuvem, administrada por especialistas em cibersegurança.
Esse formato elimina a necessidade de manter infraestrutura local pesada e reduz o tempo de implantação, ao mesmo tempo em que garante acesso contínuo a tecnologias e analistas altamente especializados.
Ao integrar telemetria proveniente de múltiplas camadas, o SOC as a Service consolida os eventos em um único datalake de análise, aplicando correlação e contextualização automatizadas com apoio de SOAR e machine learning. Assim, os alertas deixam de ser tratados de forma isolada e passam a compor narrativas completas de ataque, permitindo uma visão tática e antecipada das ameaças.
Essa automação nativa reduz drasticamente o tempo médio de detecção (MTTD) e o tempo médio de resposta (MTTR), pontos críticos para conter ataques modernos que podem se propagar em minutos.
Outro benefício do modelo é a atualização contínua da inteligência de ameaças. Fornecedores de SOCaaS normalmente operam com bases globais de threat intelligence, alimentadas por fontes de ciberinteligência regionais e internacionais.
Essa atualização constante amplia a visibilidade sobre novas campanhas maliciosas, técnicas de exploração e indicadores de comprometimento (IoCs), garantindo que o ambiente corporativo permaneça protegido mesmo diante de vetores inéditos. Ao mesmo tempo, as plataformas de SOCaaS modernas integram recursos de análise comportamental (UEBA) e aprendizado contínuo, permitindo identificar padrões anômalos e prevenir movimentos laterais antes que evoluam para incidentes graves.
Mais do que uma modernização tecnológica, a adoção de modelos de SOC as a Service representa um novo paradigma de defesa cibernética. O CISO que ainda vê o SOC apenas como um centro de monitoramento precisa agora encará-lo como um núcleo de inteligência e antecipação, sustentado por automação, correlação de dados e aprendizado de máquina.
Content warning: This story discusses non-consensual deepfake nude imagery.
On the surface, Crushmate appeared to be one of many artificial intelligence “girlfriend” or “companion” apps. Its multiple websites said it specialised in “crafting the AI girl of your dreams”, and on Google and Apple’s app stores, it was described as an “AI chat product designed to provide users with a comprehensive emotional support and communication experience”.
But ads linked to the app on popular social media platforms showed it was offering an entirely different service – making nonconsensual nude images of real women.
Meta announced last week that it was suing Joy Timeline HK Limited (“Joy Timeline”), the Hong Kong-based company it said was behind a group of deepfake “nudifying” apps under “CrushAI”, which include Crushmate. This was following a 404 Media report in January that CrushAI had bought thousands of ads on Instagram and Facebook, using multiple fake Facebook profiles to evade Meta’s moderators.
However, a Bellingcat investigation has uncovered two additional companies in Hong Kong and mainland China – Soul friendship HK Limited (“Soul friendship”) and Wuhan Ruisen Zhuoxin Network Technology Co., Ltd (“Wuhan Ruisen”) – that appear to have links to these apps.
The CrushAI ads showed women, including celebrities and influencers, having their clothes artificially removed using deepfake technology. They led to pages prompting users to upload photos of people and “erase clothes” off them.

404 Media’s report prompted Illinois Senator Dick Durbin to write to Meta CEO Mark Zuckerberg about CrushAI’s advertising on Meta’s platforms, in a letter pointing out that “the generation and dissemination of nonconsensual, deepfake intimate imagery are acts of abuse and violations of privacy that inflict lasting harm on victims”.
Asked about the two other companies Bellingcat has linked to CrushAI, Meta said it was looking into them and would take action, including legal action, as necessary if it found violations of its policies. The company also said they will continue to take the necessary steps against other advertisers who abuse their platform.
Soul friendship was the listed developer of Crushmate on the Apple App Store, while Wuhan Ruisen filed an application for a US federal trademark related to the Crushmate brand last year. Documents supporting Wuhan Ruisen’s trademark application suggest that the app earned more than US$45,000 in subscriptions between December 2023 and July last year.

Your donations directly contribute to our ability to publish groundbreaking investigations and uncover wrongdoing around the world.
The legal filing, which Meta provided to Bellingcat, shows that the social media giant is seeking an injunction to prevent Joy Timeline from placing ads related to nudify apps on its platforms. It is also claiming US$289,200 in damages, including costs it said it incurred for investigating and removing ads for the CrushAI apps, to respond to public and regulators’ queries in relation to the ads and to take enforcement action against Joy Timeline.
The complaint stated that Joy Timeline placed over 87,000 violating ads on Facebook and Instagram as of February this year, mainly targeting users in the US, Canada, Australia, Germany and the UK.
In response to Bellingcat’s queries, a Crushmate representative said that the app had permanently shut down but had “very briefly relied on the support of many third-party partners” in the early stages of its business.
On the relationship between CrushAI and Joy Timeline as well as the two other companies the representative said that “since the project has now ended and the team no longer exists, I’m unfortunately unable to verify whether the company you mentioned in your email was one of our former partners”.
Soul friendship, Joy Timeline and Wuhan Ruisen did not respond to multiple requests for comment on their relationships with each other or with CrushAI.
Like other notorious AI nudify apps, CrushAI appears to own multiple websites with the same domain name (“crushmate”) but different extensions such as .site .net .vip and .us. Bellingcat found at least 23 domains that used the Crushmate name, all of which are no longer accessible. These were mostly registered on two days in April and July 2024. We also found other sites with identical homepage layouts and content to Crushmate, with similar domains like “Crushai”, “crushh”, “crrru”, “crushx” and “crush1”.
Using Domain Tools, we were able to link these sites – and more – through an identical Google Analytics Tag, which is used to track website traffic.
While nearly every one of these websites had their WHOIS registration info redacted for privacy, one was not, and it was registered to Joy Timeline.
Our search on Whoxy, a reverse WHOIS search tool, found 158 domains registered publicly to Joy Timeline at the time of publication. Only one carried the Crushmate name, but 28 more had almost identical layouts and also appeared to be deepfake “nudify” apps.
For example, archived versions of the main pages of two of these domains, “sparkaifun [dot] online” and “chatnplay [dot] online”, were identical to the home page and “clothing eraser” pages on CrushAI’s sites.

It is possible that there are more similar web domains that did not show up in our searches, as domain registrants can also choose to redact their information. Other active domains owned by Joy Timeline, according to publicly accessible domain information, include homepages for other “AI chat” apps, photo editing apps and mobile games, among others.
On Hong Kong’s Companies Registry, Joy Timeline’s director was listed as a person called Zhang Xiao, who holds a Chinese passport.

The company was registered with 100 shares issued at a total value of HK$100 (US$12.80). Zhang Xiao was listed in the company documents as owning 90 of these shares, while another Chinese national, Zhang Shiwei, owns 10.
Zhang Shiwei is the director of Soul friendship, which Bellingcat’s investigation has also linked to the CrushAI apps.
Although Crushmate is no longer available on Google’s Play Store and Apple’s App Store, archived versions of its app listings on both of these stores led us to Soul friendship, another Hong Kong-based company.
Crushmate’s developer on Google’s Play Store from September 2024, based on a cached version of the page, was listed as “LipLip Team”. Our online searches of LipLip Team showed that it had another app listed on the Play Store called “LipLip – Live Video Chat&Meet”, which appeared to be a chatting app.


Bellingcat could not find any company called “LipLip Team” registered in Hong Kong, where LipLip-Chat’s archived X bio stated that the app is based.
But the URL of LipLip’s page from the developer’s archived Google Play Store profile, based on both indexed copies of the Google Play Store listing and LipLip’s X bio, included the ID “hk.soulfriendship.chat” – our first clue that another company was involved.

On the Google Play Store, the app ID which makes up part of the URL is based on the package name of an app, which uniquely identifies the app across the Play Store. The package name could be set to anything, as long as it is not used by any other app on the Play Store.
However, in this case, it happens to closely match the name of Soul friendship, the Hong Kong-based developer that published both Crushmate and LipLip-Chat on the Apple App Store.

We were able to find more information on Soul friendship by viewing LipLip-Chat’s Apple App Store listing as it would appear from a country within the European Union.
Due to the EU’s Digital Services Act, Apple is legally required to verify and display more detailed information for traders distributing apps in the EU than in other jurisdictions.
This includes developers’ Data Universal Numbering System (DUNS) number – a nine-digit number key for uniquely identifying companies worldwide – as well as contact information such as their address, phone number and email address.
Even from outside of the EU, it is easy to view this information by tweaking the country code in the URL of the web-based App Store listing.
For example, the developer information visible on the US app store listing for LipLip-Chat only shows Soul friendship’s name. But simply changing the country code from “us” to “nl” (the Netherlands’ country code) reveals the company’s DUNS Number, address, phone number and email address:

The address listed for Soul friendship, in the commercial district of Wan Chai, Hong Kong, is the same one on Joy Timeline’s domain name registration records. This address is also listed as belonging to one of the 6,900 or so Trust or Company Service Providers (TCSPs) in Hong Kong which are authorised to provide, among other corporate services, a registered business or office address.
Documents from the Companies Registry in Hong Kong show that Zhang Shiwei is Soul friendship’s listed director.

Although they have different names and directors, Soul friendship’s and Joy Timeline’s shareholders are the same and there are multiple overlaps in how the two companies operate.
Like Joy Timeline, Soul friendship was registered with 100 shares issued at a total value of HK$100. In a mirror of the arrangement for Joy Timeline, Zhang Shiwei, the director of Soul friendship, owns 90 of Soul friendship’s shares while Zhang Xiao, the director of Joy Timeline, owns 10 shares.
In addition to their common TCSP-linked address in Wan Chai, both companies used the same registered office address in Kwun Tong, an industrial and business area in Hong Kong, on their business filings. This is the address of another TCSP, which serves as the company secretary for both of these businesses.
Searches for Soul friendship and Joy Timeline online did not turn up much, except websites under their names that used identical templates. Neither website mentioned Crushmate or CrushAI, and both said on their “About Us” page that they were founded in 2022 and provided “IT consulting and software development services”.

To complicate things even further, Bellingcat found two US federal trademark applications filed for Crushmate by a mainland Chinese company, Wuhan Ruisen, in August 2024. The first application, in the category of “Advertising, Business, and Retail Services”, was rejected on the grounds that the company did not provide sufficient evidence of using the Crushmate mark in commerce.
The second one, in “Computer and Software Products and Electrical and Scientific Products”, was officially registered with the trademark office on April 29, 2025. The documents filed for federal trademark applications are publicly accessible through the United States Patent and Trademark Office (USPTO)’s website.
Subscribe to our newsletter for first access to our published content and events that our staff and contributors are involved with, including interviews and training workshops.
In their trademark applications, Wuhan Ruisen provided “specimens”, which are samples of how their trademark is used in commerce. These included screenshots of both Crushmate’s Google Play Store and Apple App Store listings – showing LipLip team and Soul friendship HK as the app developers – as well as screenshots of their website.
John Halski, a US-based lawyer whose practice focuses on trademark and copyright, told Bellingcat that it is possible for a company to include samples or specimens in their trademark application from a different company through a third party licence.
However, Halski said that whether multiple company names in an application would be questioned depended on the examiner.
“The [trademark] examiner has the discretion to ask: ‘You sent me this specimen showing that party XYZ is using it and you claim that your name is ABC’. Then they may ask, ‘is this under a licence arrangement?’”
Anyone may file an application for a trademark, whether or not they own it, but other parties may oppose the application – such as if they are claiming to be the original owners of the trademark – within 30 days after it is published. Wuhan Ruisen’s application for the Crushmate trademark was published on March 11 this year, and successfully registered without opposition on April 29.
The application documents included a screenshot that appeared to show a Stripe payment dashboard, with 4,563 successful payments. All of the visible payments were for US$9.99, which was the weekly cost of a VIP subscription to Crushmate on the US site at the time the application was submitted.

Assuming the only payments recorded by the dashboard were for these subscriptions, this would imply that by the time of the application being submitted in August last year, Crushmate had earned at least US$45,584.37 in subscriptions. It is unclear what the exact timeframe captured by the screenshot of this dashboard was, although the application states that the first use of the trademark was Dec. 25, 2023.
Another screengrab included in the application, also apparently from Crushmate’s Stripe dashboard, showed a breakdown of the locations of Crushmate’s paying customers. This view on Stripe’s dashboard displays the “tax thresholds” for each state in the US and shows whether the income generated has reached taxable status. The screengrab indicated that Crushmate had paying customers across the US, with the most transactions from Kentucky and Utah.

Based on documents from China’s official business registry which match the company’s name in Chinese and address, Wuhan Ruisen was established in March 2021 with a registered capital of 10 million Chinese yuan (US$1.38 million).

We are not naming the legal representative of Wuhan Ruisen, listed in these documents, as the exact relationship between this company and CrushAI is still unclear. The legal representative’s name does not appear on Soul friendship or Joy Timeline’s business registration records in Hong Kong.
A search for the company’s name on China’s Internet Content Provider licence database shows that it registered for five different domain names. Only one was accessible as of June. This site, which describes the Wuhan company as a “professional software development company” focusing on the development of desktop and mobile software, lists a number of apps supposedly developed by the company. None of the CrushAI apps were among them.

Some of the apps on this page have a close resemblance to software by foreign developers. For example, the first app on the page is an AI translator called “DeepL”, which is also the name of an AI translation app by a German startup that does not currently offer paid plans in mainland China.
On third-party consumer service platform Heimao Tousu, there were more than 40 complaints between October 2023 and March 2025 about the company. Most said they paid between 29 and 69 yuan (US$4 to US$9.50) to download software they believed to be genuine, only to discover the products were fake or did not work. When they asked for refunds, they were ignored.

Wuhan Ruisen did not respond to multiple emails requesting for comment, and when we called the phone number listed on its website, we got an automated message stating that the number dialled was invalid.
Crushmate’s X profile and a US domain site carrying its name was accessible until April. That same month, the US Take It Down Act, which criminalises the distribution of non-consensual deepfake pornography at the federal level, passed. It was signed into law in May, and Crushmate’s X profile was deleted sometime that month.
At time of publication, all 23 of the Crushmate domains, the additional nudify-related domains owned by Joy Timeline, and the other CrushAI domains appear to be either offline or display an “under maintenance” notice after users register and log in.

When Bellingcat reached out to a support email listed on several Crushmate websites, an unnamed individual responded.
This person said the decision to shut down operations and disband the team actually took place “several months” before the introduction of the Take It Down Act.
“Since then, this inbox has remained inactive,” they said.
The person emailing us did not explain why they were replying from an inactive account, or respond to subsequent questions about who they were or what their role in Crushmate or CrushAI was.
Joy Timeline has purchased domains as recently as May 14, but none of these appear to be nudify sites or currently hosting content.
Featured image credit: Reihaneh Golpayegani / Telling Tales / Licensed by CC-BY 4.0
Bellingcat is a non-profit and the ability to carry out our work is dependent on the kind support of individual donors. If you would like to support our work, you can do so here. You can also subscribe to our Patreon channel here. Subscribe to our Newsletter and follow us on Bluesky here and Mastodon here.
The post Meta’s Suit Against Hong Kong Firm Was Just the Beginning – More Companies Linked to CrushAI ‘Nudify’ Apps appeared first on bellingcat.
This article is the result of a collaboration with TjekDet, Denmark’s fact-checking media outlet, Danish newspaper Politiken, and the Canadian Broadcasting Corporation (CBC). Watch CBC’s documentary here.
Warning: This article discusses non-consensual sexually explicit content from the start.

MrDeepFakes billed itself as the “largest and most user-friendly” platform for celebrity deepfake pornography. The website, which was visited millions of times every month, hosted almost 70,000 explicit and sometimes violent videos, which had collectively been viewed more than 2.2 billion times.
They show mostly famous women whose faces have been inserted into hardcore porn with artificial intelligence – and without their consent.
In the background, an active community of more than 650,000 members shared tips on how to generate this content, commissioned custom deepfakes, and posted misogynistic and derogatory comments about their victims.

For years, the website has been shrouded in secrecy, existing in a legal grey area and concealing the identity of those who control it. Until now.
Bellingcat, in collaboration with Danish outlets Tjekdet, Politiken and the Canadian Broadcasting Corporation (CBC), has conducted an investigation to reveal the identity of a key administrator behind MrDeepFakes.

David Do is a 36-year-old Canadian pharmacist who, based on open source information, lives an unassuming and respectable life in the suburbs outside of Toronto. Photos and videos posted online show him with family, friends and colleagues. The university graduate has a well-paying job in a public hospital and drives a new Tesla.
But Do has been living a double life: in secret, he is the most prominent figure identified to have had control over the administration of MrDeepFakes. He was also an influential member of its growing online community, producing his own deepfake porn and assisting users who want to make their own.
Online posts show Do is a technically minded individual with a long-standing interest in creating and distributing adult content, and provide an insight into efforts to obfuscate his identity.

We identified Do by cross-referencing data from massive credential leaks, which are publicly available via breach databases. A series of burner emails, IP addresses, repeated usernames, and a unique password reveal a more than decade-long digital trail that allowed researchers to link him to MrDeepFakes.
Bellingcat, Tjekdet, Politiken and CBC have sent Do multiple requests for comment since late March but did not receive a response as of publication. Last month, the CBC hand-delivered correspondence to Do setting out the findings of this investigation, but he declined to comment.
Shortly after, Do’s Facebook page and the social media accounts of some family members were deleted. Do then travelled to Portugal with his family, according to reviews posted on Airbnb, only returning to Canada this week.

On Sunday, the MrDeepFakes site was shut down. “A critical service provider has terminated service permanently,” a notice on the platform says. “We will not be relaunching. Any website claiming this is fake.”
CBC approached David Do again on Monday but he refused to answer questions about his involvement with MrDeepFakes. “I don’t want to be recorded please,” he said. “I have to go. I’m busy right now.”
Update: David Do is on leave from his position as a hospital pharmacist, his employer confirmed on May 13, while an internal investigation is underway. Separately, the Ontario College of Pharmacists has said it is “taking immediate steps to look into this matter further and determine the necessary actions we need to take to protect the public”.
Deepfake pornography is the use of artificial intelligence to create non-consensual, sexually explicit images and videos. Research shows that 99 per cent of victims are women.
Actress Jenna Ortega, singer Taylor Swift and politician Alexandria Ocasio-Cortez are among some of the high-profile victims whose faces have been superimposed into hardcore pornographic content.
But the technology is also being used on people who are not in the public eye.
A 2024 survey found that at least one in nine high school students knew of someone who had used AI technology to make deepfake pornography of a classmate and The New York Times has reported that schools across the US were dealing with incidents of teenagers making deepfakes of their female classmates.
Adam Dodge, from EndTAB (End Technology-Enabled Abuse), said it was becoming easier to weaponise technology against victims. “In the early days, even though AI created this opportunity for people with little-to-no technical skill to create these videos, you still needed computing power, time, source material and some expertise. And now you need very little of those things,” he said.
“It is literally point-and-click violence against women. Some of these apps only require one photo of the target, and you, on the app, literally use your finger to drag the woman’s face into a video and then just release it and AI does the rest, editing that victim into the photo. And then you press play and it now appears that the victim from the photo is engaging in sex acts.”
Dodge said the MrDeepFakes site had grown since 2008 and added features that were typically used by regular businesses to promote an air of legitimacy. “ It’s incredible and I’m incredulous that the site has been allowed to survive this long,” he told Bellingcat.
“This is sexual violence, and it’s as harmful as any other form of sexual violence in our opinion. I’ve talked to mental health professionals who work with rape and trauma survivors, and they analogise it to a woman who is sexually assaulted while unconscious or drugged, and it’s filmed, and then they have to watch it later.
“They have no memory of this happening to them. But the simple act of watching it is deeply traumatic and that’s what this technology manufactures. And the permanency and the public nature of it are the two, I would argue, most powerfully traumatic things that victims often experience.”
Governments around the world are scrambling to tackle the scourge of deepfake pornography, which continues to flood the internet as technology advances. In Canada, the distribution of non-consensual intimate images is illegal, but this is not widely applied to deepfakes. Canadian. Prime Minister Mark Carney pledged to pass a law criminalising the production and distribution of non-consensual deepfakes during his federal election campaign.
In the US, legislation varies by state, with about half having laws against deepfake pornography. The US Congress last month passed the Take it Down Act, which criminalises the distribution of non-consensual deepfake pornography at the federal level. President Donald Trump is expected to sign the bill into law.
The EU does not have specific laws prohibiting deepfakes but has announced plans to call on member states to criminalise the “non-consensual sharing of intimate images”, including deepfakes. Member states will not enact these laws until 2027. In the UK, it is already an offence to share non-consensual sexually explicit deepfakes, and the government has announced its intention to criminalise the creation of these images. Australia passed new laws to combat sexually explicit deepfakes last year.
The identity of the person or people in control of MrDeepFakes has been the subject of media interest since the website emerged in the wake of a ban on the “deepfakes” Reddit community in early 2018.
But the porn site’s hosting providers have bounced around the globe and premium memberships can be bought with cryptocurrency, which have made it virtually impossible to trace ownership.

Your donations directly contribute to our ability to publish groundbreaking investigations and uncover wrongdoing around the world.
Adam Dodge, the founder of EndTAB (End Technology-Enabled Abuse), said MrDeepFakes was an “early adopter” of deepfake technology that targets women. He said it had evolved from a video sharing platform to a training ground and marketplace for creating and trading in AI-powered sexual abuse material of both celebrities and private individuals.
“Our digital world is really good at empowering people who want to do harm by allowing them to remain anonymous while simultaneously making it almost impossible for victims to unmask them,” he said.
In January, Bellingcat, in collaboration with the German YouTube channel STRG_F, examined the companies behind two apps used for creating deepfakes that it advertised prominently on its homepage.

For this investigation, researchers conducted a forensic analysis of the forums on MrDeepFakes’ website. The forums are a virtual marketplace where members commission deepfakes and trade tips on making videos with the same technology that is used for creating revenge porn.
Videos posted to the tube site are described strictly as “celebrity content”, but forum posts included “nudified” images of private individuals. Forum members referred to victims as “bitches”and “sluts”, and some argued that the womens’ behaviour invited the distribution of sexual content featuring them. Users who requested deepfakes of their “wife” or “partner” were directed to message creators privately and communicate on other platforms, such as Telegram.
A search of the forums returned two accounts for MrDeepFakes “staff members”. One joined in March 2019 and is also listed as a “moderator”. The other joined in February 2018 and is also listed as an “administrator” (two additional administrator accounts, created in 2018 and 2021, were not listed as staff members, and one now-defunct account previously tagged as staff and moderator was created in the year after the site was set up).

Therefore, the focus of this investigation was the oldest account in the forums, with a user ID of “1” in the source code, which was also the only profile found to hold the joint titles of staff member and administrator. The long-time handle used by this account was “dpfks”.
Researchers began by analysing the profile. The dpfks bio contained little identifying information, but an archive from 2021 shows the account had posted 161 videos which had amassed more than five million views. It earned the badge of “Verified Video Creator”.
Forum posts document dpfks’ involvement as a creator and leader in the community. Archives show dpfks posted an in-depth guide to using software that creates deepfake porn, published website rules and content guidelines, advertised for volunteers to work as moderators, and gave technical advice to users.
Dpfks’ posts carried the tagline: “Fake it till you make it.”

In a 2019 archive, in replies to users on the site’s chatbox, dpfks said they were “dedicated” to improving the platform. “There is a reason why we are the biggest deepfake site. I care about the community and teaching others.
“I don’t think other site owners care enough to make their own deepfakes, and keep uptodate [sic] with it. My first few deepfakes were s**t too, the more you make, the better you get.”
Legitimate online platforms take measures to protect users’ personal information but data breaches are common and can affect anyone, from the average user to senior US government officials. In this case, data breaches allowed researchers to link email accounts that had been reused across porn sites, warez (pirated content) forums and server admin platforms to a key operator of MrDeepFakes.
Central to the findings was one email account – dpfkscom@gmail.com – that was used in the “Contact Us” link on the footer of MrDeepFakes’ official forums in archives from 2019 and 2020.
Using breached data, researchers linked this Gmail address to the alias “AznRico”. This alias appears to consist of a known abbreviation for “Asian” and the Spanish word for “rich” (or sometimes “sexy”). The inclusion of “Azn” suggested the user was of Asian descent, which was confirmed through further research. On one site, a forum post shows that AznRico posted about their “adult tube site”, which is a shorthand for a porn video website.
The AznRico alias was frequently associated with a personal Hotmail address in David Do’s full name, which appeared in leaks alongside this username 22 times. Researchers also uncovered a cryptocurrency trading account for AznRico that later changed its username to “duydaviddo”.
The analysis showed that the MrDeepFakes Gmail address was used to register a profile on a separate porn website. This profile used a unique 11-character password which was also used across other accounts, including a profile on the Ashley Madison dating website that was registered with Do’s personal Hotmail address. A search of the unique password in breach databases returned 17 results linked to other email addresses that included Do’s full name.
Further searches of Do’s Hotmail account led to more leaks that displayed his date of birth. The Hotmail account was also linked to a residential address in Ontario, which public records show is the location of a house owned by Do’s parents. This email was also used to register a Yelp account for a user named “David D” who lives in the Greater Toronto Area.
Do has never publicly acknowledged operating MrDeepFakes, but a single email address published by the porn site formed the basis of a digital trail that led to usernames, passwords and other email accounts which overlap with his personal and professional data since 2008.

David Do keeps a low profile under his own name, but photos of him have been published on the social media accounts of his family and employer. He also appears in photos and on the guest list for a wedding in Ontario, and in a graduation video from university.
Do’s Airbnb profile displayed glowing reviews for trips in Canada, the US and Europe (Do and his partner’s Airbnb accounts were deleted after CBC approached him on Monday). His home address, as well as the address of his parents’ house, have both been blurred on Google Street View, a privacy feature that is available on request.

In the late 2000s, while studying at university, Do was involved in the creation of Xinoa (xinoa.net), a warez forum. Do’s personal Hotmail address, which includes his full name, is visible in source code as an admin contact for the site, archives from 2008 show.
The profile page “ddo” is tagged as the “Root Admin” and “Xinoa Owner”, and lists a date of birth matching that of Do. The profile includes download links to television shows, one of which was accompanied by a comment about “exam week” in 2009, when Do was studying at university. This username is also similar to Do’s Instagram profile (“ddo.jpg”), a link to which was included in the bio section of his Facebook account under the name “Doh Dave”. Both social media accounts have been deleted.
An account on an internet marketing forum was registered using a Xinoa administrator email address, breach data shows. That account was linked to an IP address owned by the University of Waterloo, where Do earned degrees in biomedical science in 2010 and pharmacy in 2014, according to Rocketreach.
The 2015 Ashley Madison data breach shows user “ddo88” registered on the dating site with Do’s Hotmail address and was listed as an “attached male seeking females” in Toronto. They described themselves as being of Asian ethnicity, 173 cm tall and weighing 66 kg. The breached profile was linked to a Toronto-based address and also contained a date of birth, which matches Do’s birth date in public records.
Xinoa would become the springboard for a more sophisticated operation.

In February 2018, when Do was working as a pharmacist, Reddit banned its almost 90,000-strong deepfakes community after introducing new rules prohibiting “involuntary pornography”. In the same week, MrDeepFakes’ predecessor site dpfks.com was launched, according to an archived changelog.
An analysis of the now-defunct domain shows the two sites share Google analytics tags and back-end software – as well as a forum admin who used the handle “dpfks”. Archives from 2018 and 2019 show the two sites redirecting or linking to each other. In a since-deleted MrDeepFakes’ forum post, dpfks confirms the link between the two sites and promises the new platform is “here to stay”.
“MrDeepFakes.com was formerly dpfks.com and we opened our doors shortly after the Reddit ban,” the 2018 post said. “I know joining a new forum or community feels like starting fresh, and starting over, but the community is small, and all the important players will stick together. I promise to keep this community running as long as I can, so that the deepfake community does not have to scramble and relocate again.”
Later in 2018, in a post on Voat, a defunct online message board similar to Reddit, dpfks said they “own and run” MrDeepFakes. In response to another user, dpfks refers to their life outside of operating a porn website. “I just got home from my day job,” the post said, “now back to this!” Some of dpfks’ earliest posts on Voat were deepfake videos of internet personalities and actresses. One of dpfks’ first posts on the MrDeepFakes’ forums was a link to a deepfake video of video game streamer Pokimane.

Other targets included the American politician Alexandria Ocasio-Cortez, for whom dpfks shared a folder containing more than 6,000 images that could be used to create deepfake pornography. Before it shut down this week, MrDeepFakes hosted 125 graphic videos tagged with Ocasio-Cortez that had collectively received more than 5.3 million views. After discovering she had been transposed into a deepfake porn video last year, Ocasio-Cortez told Rolling Stone that “digitizing violent humiliation” was akin to physical rape and sexual assault.
Another target of dpfks was American YouTube personality Gibi_ASMR, who gained popularity online with her ASMR (Autonomous Sensory Meridian Response) videos. Dpfks created and shared pornographic deepfakes of the YouTuber on the MrDeepFakes forums. In a statement published by EqualityNow in 2021, she said: “They’re running this business, profiting off my face doing something that I didn’t consent to, like my suffering is your livelihood. It made me really mad, but again, there was nothing I could do so I just had to leave it.”
In 2018, dpfks posted a two minute deepfake video of an Academy Award-winning American actress with the description: “[Name omitted] doesn’t do porn, but in this fake video she is completely naked with her legs spread in the air. Watch her face … while she struggles to take it.”

Forum posts under various aliases match those found in breaches linked to Do or the MrDeepFakes Gmail address. They show this user was troubleshooting platform issues, recruiting designers, writers, developers and search engine optimisation specialists, and soliciting offshore services.
The username “AznRico” was commonly associated with Do’s email account and could be found across several postings online. In 2009, years before MrDeepFakes was launched, this now-banned user posted to an internet marketing forum discussing online money-making techniques, including the monetisation of video traffic.
AznRico also posted on an auto lighting forum in 2009 to ask for advice about fixing headlights for a car in Canada – a 2006 Mitsubishi Lancer Ralliart. In another thread on the same forum, AznRico uploaded several images of the car, one of which was archived and contained metadata indicating that it was captured on a Sony Ericsson K850i.
In 2008, on a separate forum, AznRico said he had this model phone and posted about troubleshooting the device (that forum was subject to a data breach exposing David Do’s personal Hotmail address and unique password).

Public records obtained by CBC confirm that Do’s father is the registered owner of a red 2006 Mitsubishi Lancer Ralliart. While Do’s parents’ house is now blurred on Google Maps, the car is visible in the driveway in two images from 2009, and in Apple Maps imagery from 2019. CBC confirmed the car was still at the house last week.
In 2011, on a freelance job board, AznRico asked for help building a video streaming plugin. This profile also listed that the user was based in the same Ontario city where Do’s parents’ home is located. In 2018 – the same year MrDeepFakes was launched – AznRico asked for advice to fix slow load times on their porn site, which they said received about 15,000 to 20,000 visitors a day. Breach data shows this account was linked to Do’s personal Hotmail address.

In one forum post from January 2020, user “dj01039” complains that PayPal had limited their “stealth account”, which was used to “sell virtual goods” (PayPal was intermittently available as a payment option on MrDeepFakes). The username dj01039 matches the abbreviation of an email address (davidjames01039@gmail.com) that was linked to a PayPal donation button on MrDeepFakes in December 2019.
In June 2020, on another forum, a user with the same alias (who later changed it to “ac2124”) said their stealth account had been permanently closed and wanted to know about front companies that could accept payments on their behalf. The user described themself as the “webmaster of an adult tube site” who takes a cut from creators who post original porn videos, and also earns revenue from running ads. By December 2020, ac2124 said their website was earning between $4,000 and $7,000 a month.
Breach data also links the MrDeepFakes Gmail to an account on support forums for Kernel Video Sharing (KVS), a commercial content management system, where user “mongoose657” (formerly dj01039) sought help managing a video tube site. The discussions, from 2021 to 2024, were consistent with backend issues encountered when running a large website: storage solutions, ticket system failures, and outsourcing development work.
On the adult webmaster forum GoFuckYourself.com in 2020, dpfks (subsequently changed to “mjmango”) enquired about anonymous debit cards, which were advertised as allowing users to withdraw cash or pay for purchases anonymously. In 2021, mjmango responded to another user’s enquiry about how to monetise tube sites.
In another forum, ac2124 enquired about countries to form an offshore company and expressed concern about “know your customer” checks, which are used by the banking sector to confirm the identity of their customers. In a 2020 post, ac2124 said they had decided to make a “dummy site/front” for their adult site and enquired about online payment processing and “safe funds storage”.

In 2022, ac2124 sought advice for a Canadian citizen who operates an “adult niche website” and asked about “a company setup that focuses on privacy”. The post said: “At a bare minimum, this person shouldn’t be listed on any public registrar (as director, shareholder, UBO, etc). Open to using nominees, opening trusts, etc. What are some setups, or jurisdictions that should be looked into?” This user also asked specifically about setting up a company in the British Virgin Islands or Cayman Islands, both secrecy jurisdictions.
In late 2023, mjmango left positive feedback for an adult graphic designer below a post from the designer containing a MrDeepFakes logo. “Purchased another logo recently. As always great communication and allowed multiple re-edits,” the comment said. In March 2024, ac2124 posted about delays accessing a service that creates a “proxy” for a “high-risk website” so it can process transactions from the online payment processor, Stripe.
In April 2024, Dutch outlet Algemeen Dagblad (AD) reportedly made contact with the owner of MrDeepFakes, who was anonymised in their subsequent reporting. AD reported that this person claimed to have sold the website, but did not provide any evidence to support this claim. Our investigation could not confirm whether the site was ever sold, and if so when.
David Do did not respond to multiple requests for comment about his involvement with MrDeepFakes.
Correction: This story initially said the AznRico post about the K850i phone was from 2009, when it was 2008. The article was updated on May 8 to reflect this.
Ross Higgins, Connor Plunkett, Beau Donelly, George Katz, Kolina Koltai and Galen Reich contributed to this article.
Bellingcat is a non-profit and the ability to carry out our work is dependent on the kind support of individual donors. If you would like to support our work, you can do so here. You can also subscribe to our Patreon channel here. Subscribe to our Newsletter and follow us on Bluesky here and Mastodon here.
The post Unmasking MrDeepFakes: Canadian Pharmacist Linked to World’s Most Notorious Deepfake Porn Site appeared first on bellingcat.