Tropic Trooper Weaponizes GitHub and VS Code for East Asian Espionage
The post Tropic Trooper Weaponizes GitHub and VS Code for East Asian Espionage appeared first on Daily CyberSecurity.
A fake purchase order attachment turned out to be a phishing page designed to harvest your login details.
The post Purchase order attachment isn’t a PDF. It’s phishing for your password appeared first on Security Boulevard.
An attachment named New PO 500PCS.pdf.hTM, posing as a purchase order in PDF form, turned out to be something entirely different: a credential-harvesting web page that quietly sent passwords and IP/location data straight to a Telegram bot controlled by an attacker.
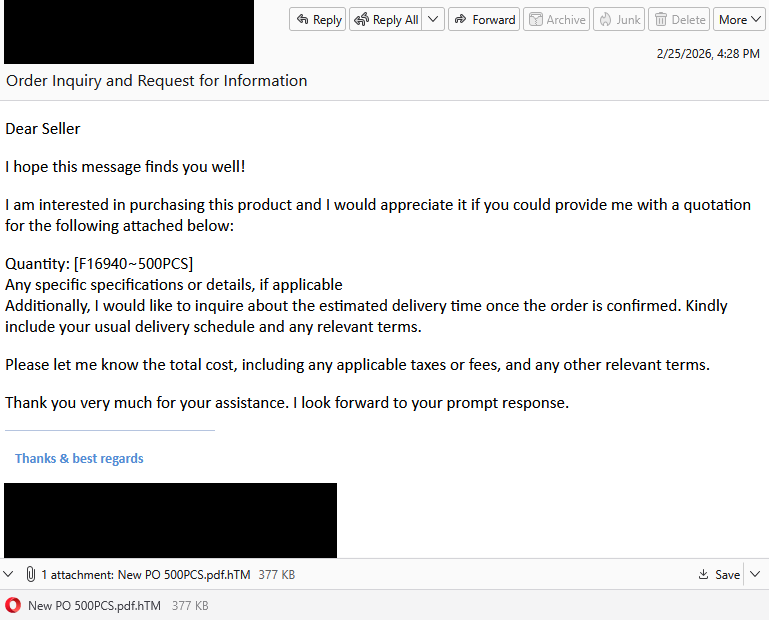
Imagine you’re in accounts payable, sales, or operations. Your day is a steady flow of invoices, purchase orders, and approvals. An email like this may look like just another item in your daily queue.

“Dear Seller
I hope this message finds you well!
I am interested in purchasing this product and I would appreciate it if you could provide me with a quotation for the following attached below:
Quantity: [f16940-500PCS]
Any specific specifications or details, if applicable
Additionally, I would like to inquire about the estimated delivery time once the order is confirmed. Kindly include your usual delivery schedule and any relevant terms.
Please let me know the total cost, including any applicable taxes or fees, and any other relevant terms.
Thank you very much for your assistance. I look forward to your prompt response.”
What immediately jumps out is the double file extension. Attachments with extensions like .pdf.htm are classic phishing tactics. These files are usually disguised as documents (PDF), but they’re actually HTML files that open in a browser and can contain malicious scripts or phishing forms.
But let’s suppose you didn’t notice that. What happens when you open the attachment?

You’re shown a password prompt in front of a blurred background. The recipient’s email address is already filled in. In the background, the phishing script grabs some environment details—IP, geolocation, and user agent—and sends them to the attacker along with any details you filled out.
After a short “Verifying…” message, you get a familiar-looking error:

This is a psychological trick:
You type your password again and click Next and this one appears to be accepted.
Instead of opening a real document, you’re redirected to a blurry image that looks like an invoice hosted on ibb[.]co. That’s a shortened domain for ImgBB, a legitimate image-hosting and sharing service. That unexpected image may confuse you just enough to stop you from immediately changing your credentials or immediately alerting your IT department.

Rather than emailing stolen credentials or logging them on a server that might be blocked by security software, the page sends them using a Telegram bot. The attacker receives:
Telegram is encrypted, widely used, and often not blocked by organizations, which makes it a popular command and control (C2) channel for phishers.

As unprofessional as this phishing attempt may look, each victim sending actual login details to the phisher is a win on a near-to-zero investment. For the target, it can turn into a nightmare ranging from having to change passwords to a compromised Acrobat or other account, which can then be used and sold for more serious attacks.
The good news: once you know what to look for, these attacks are much easier to spot and block. The bad news: they’re cheap, scalable, and will continue to circulate.
So, the next time a “PDF” asks for your password in a browser, pause to think about what might be hiding under the hood.
Beyond avoiding unsolicited attachments, here are a few ways to stay safe:
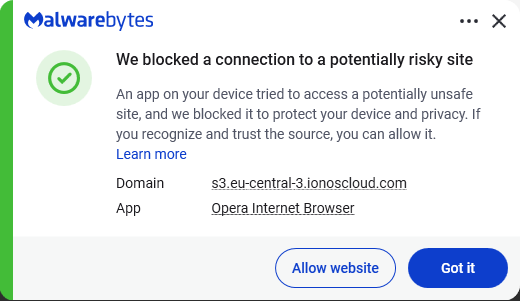
Pro tip: Malwarebytes Scam Guard recognized this email as a scam.
We don’t just report on scams—we help detect them
Cybersecurity risks should never spread beyond a headline. If something looks dodgy to you, check if it’s a scam using Malwarebytes Scam Guard. Submit a screenshot, paste suspicious content, or share a link, text or phone number, and we’ll tell you if it’s a scam or legit. Available with Malwarebytes Premium Security for all your devices, and in the Malwarebytes app for iOS and Android.
A PDF named “NEW Purchase Order # 52177236.pdf” turned out to be a phishing lure. So we analyzed the phishing script behind it.
A customer contacted me when Malwarebytes blocked the link inside a “purchase order” email they had received.

When I examined the attachment, it soon became clear why we blocked it.
The visible content of the PDF showed a button prompting the recipient to view the purchase order. Hovering over the button revealed a long URL that included a reference to a PDF viewer. While this might fool some people at first glance, a closer look raised red flags:

Since I’m rarely able to control my curiosity, I temporarily added an exclusion to Malwarebytes’ web protection so I could see where the link would take me. The destination was a website displaying a login form with the target’s email address already filled in (the address shown here was fabricated by me):

The objective was clear: phishing. But the site’s source code didn’t reveal much.
The most likely objective was to harvest business email addresses and their passwords. Attackers commonly test these credentials against enterprise services such as Microsoft Outlook, Google Workspace, VPNs, file-sharing platforms, and payroll systems. The deliberately vague prompt for a “business email” increases the likelihood that users will provide corporate credentials rather than personal ones.
There was also a small personalization touch. The “Estimado” greeting sets a professional tone and is common in business correspondence across Spanish-speaking regions.
For a full analysis read on, but the real clue is that the harvested credentials accompanied additional information about the victim’s browser, operating system, language, cookies, screen size, and location. This data was sent directly to the scammer’s account on Telegram, where it’s likely to be used to compromise the business network or sold on to other cybercriminals.
A quick search on VirusTotal showed that there were several PDF files linking to the exact same ionoscloud.com subdomain.
As I pointed out earlier, the source code of the initial phishing page did not reveal a lot. These are probably auto-generated templates that can be planted on any website, allowing attackers a fast rotation.

ionoscloud.com belongs to IONOS Cloud, the cloud infrastructure division of IONOS, a major European hosting company. It offers services similar to Amazon AWS or Microsoft Azure, including hosting for websites and files. Scammers specifically choose reputable cloud platforms like IONOS Cloud because of the “halo effect” of being hosted at a well-known domain, which means security companies can’t just block the whole domain.
The criminals also get the flexibility to quickly spin up, modify, or tear down phishing sites and continue to evade detection by moving to new URLs or storage buckets.
So, we followed the trail to a JavaScript file, which turned out to be obfuscated script—and a long one at that. But the end of it looked promising.

Since it was still unclear at this point what it was up to, I made a change to the script to avoid infection and which allowed me to get the source code without executing the script. To achieve this, I replaced the last line of the original script with code that exports the next layer to an HTML file.

The next obfuscation layer turned out to be easy. All it contained was a long string that needed to be unescaped. Because of the length, I used an online decoder to do that for me.

This showed me the code for the actual form that the target would see—and the goal of the whole phishing expedition.
The part that did the actual harvesting was hidden in another script.

This was still pretty long and obfuscated but by analyzing the code and giving the functions readable names I managed to find out which information the script gathered. For example, the script uses the ipapi location service:

And I found out where it sent the details.

Any credentials entered on the phishing page are POSTed directly to the attacker’s Telegram bot and immediately forwarded to their chosen Telegram chat for collection. The Telegram chat ID hardcoded in the script was 5485275217.
The advice here is pretty standard. (Do as our customer did, not as I did.)
Pro tip: Malwarebytes Scam Guard recognized the screenshot of the PDF as a phishing attempt and provided advice on how to deal with it.
We don’t just report on threats—we remove them
Cybersecurity risks should never spread beyond a headline. Keep threats off your devices by downloading Malwarebytes today.