
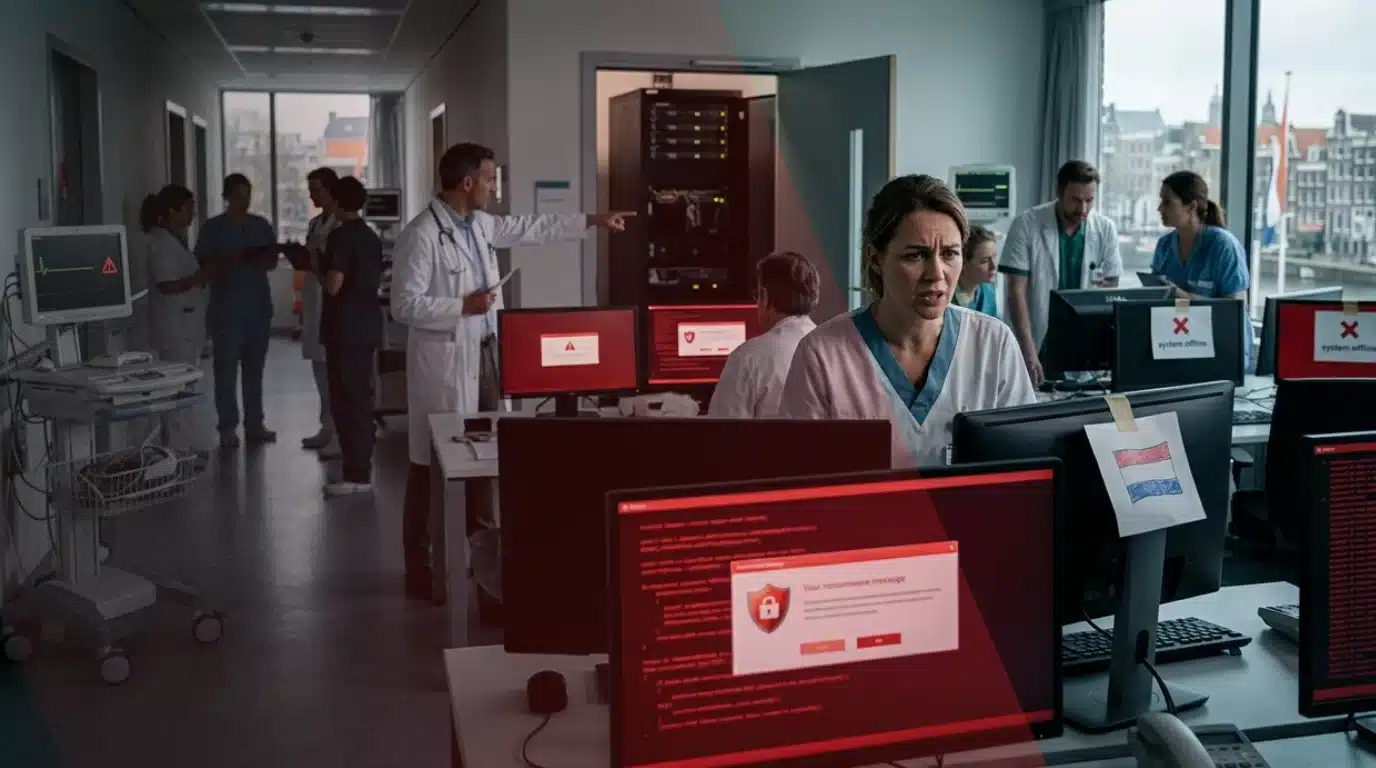
The ChipSoft ransomware incident has disrupted healthcare operations across multiple institutions after the Dutch software vendor was hit by a cyberattack on April 7. The attack forced hospitals to disconnect critical systems and triggered widespread precautionary actions, highlighting the ongoing risks
ransomware poses to the healthcare sector.
Z-CERT
confirmed it has been working closely with ChipSoft, healthcare institutions, and other stakeholders since the incident was first detected. The organization is actively monitoring the situation while providing support and
threat intelligence to affected entities.
ChipSoft Ransomware Incident Forces System Shutdowns
In response to the
ransomware incident, the company disabled connections to key platforms, including Zorgportaal, HiX Mobile, and the Zorgplatform, as a precaution. These systems remain temporarily unavailable as ChipSoft works to restore services in phases.
Users are being issued new login credentials as part of the recovery process. ChipSoft has maintained direct communication with its customers, outlining steps to manage disruptions while systems are gradually brought back online.
According to
reports, 11 hospitals disconnected ChipSoft software from their networks following the attack. A confidential advisory also urged customers to cut secure
VPN connections after the compromise was identified.
Hospitals Face Operational Challenges, Not Critical Disruptions
The ChipSoft
ransomware incident has led to logistical challenges across healthcare institutions rather than critical failures in patient care. Hospitals have increased staffing at service desks, expanded telephony support, and relied more heavily on direct communication channels.
Systems were
reported unavailable at several hospitals, including Sint Jans Gasthuis, Laurentius Hospital, VieCuri Medical Center, and Flevo Hospital.
Despite these disruptions, Z-CERT noted that no critical care processes have come to a standstill so far, suggesting that contingency plans and manual workflows are helping maintain essential medical services.
Investigation Ongoing, Attackers Yet to Be Identified
At this stage, the source of the ChipSoft ransomware incident remains unknown, and no
ransomware group has claimed responsibility. ChipSoft’s website was also reported unreachable at the time of writing, indicating ongoing technical or
security challenges.
The attack appears to have originated from a compromise within ChipSoft’s environment, prompting widespread defensive actions by its customers to limit further
risk.
Ripple Effects Extend Beyond Immediate Disruptions
The impact of the ransomware incident has extended beyond system outages. Leiden University Medical Center (LUMC)
announced it has postponed the rollout of a new electronic patient record system supplied by ChipSoft following the breach.
The hospital clarified that there are no indications that patient
data has been leaked, reinforcing the current assessment that the incident has not resulted in data exposure.
Healthcare Sector Remains a Prime Target
The ChipSoft ransomware incident highlights the persistent threat facing healthcare organizations. Cybercriminals frequently target hospitals and medical software providers due to the critical nature of their services, where downtime can create pressure to restore systems quickly.
A recent example includes the
cyberattack on University of Hawaiʻi Cancer Center, where a ransomware incident impacted research systems and exposed sensitive personal data collected over decades. While clinical operations were not affected, the breach highlighted the long-term risks associated with storing large volumes of historical data.
Z-CERT Continues Support and Monitoring
Z-CERT continues to play a central role in managing the fallout from the ransomware incident. The organization is assisting healthcare institutions with prevention, detection, response, and recovery efforts, while also sharing updated threat intelligence.
As restoration efforts progress, authorities and healthcare providers remain focused on minimizing disruption and ensuring patient care remains uninterrupted.
The ransomware incident serves as another reminder of how cyberattacks on third-party vendors can cascade across critical sectors, reinforcing the need for stronger resilience in
healthcare cybersecurity systems.
![]()

![]()
![]()

![]()