LABScon25 Replay | Please Connect to the Foreign Entity to Enhance Your User Experience
In this LABScon 25 presentation, Joe FitzPatrick explores how networked devices manufactured overseas have quietly become indispensable to everything from small-business prototyping labs to roadside infrastructure. He argues that the safeguards meant to manage the risks these devices introduce are, in practice, largely ineffective.
Starting with recent reports of undocumented cellular radios found in solar inverters used in U.S. highway infrastructure, Joe notes that adding that kind of connectivity to a device with an exposed serial port takes minutes and can be done by anyone: the manufacturer, the installer, or someone who came along later.
From there he covers the familiar mechanisms by which banned hardware finds its way into supply chains anyway, through relabeling and FCC-certified modular components, before turning to mandatory product activation in consumer devices like drones and 3D printers, and what it actually takes to use them without phoning home.
The deeper problem is that small businesses and infrastructure operators are genuinely dependent on imported hardware because it works and it’s affordable. A significant amount of it runs on devices that connect to foreign entities by default, and there’s no clean domestic alternative.
Joe concludes that import bans don’t fix problems that exist equally in domestic products, and that trade policy is the wrong tool for what is fundamentally a consumer safety problem. His preferred alternatives are right to repair with offline use guarantees, hardware and firmware bills of materials, and comprehensive privacy legislation.
This talk is essential viewing for security practitioners concerned about hardware supply chain risks, the unexpected connectivity of critical infrastructure, or the US’s deep dependence on foreign-manufactured consumer electronics.
About the Author
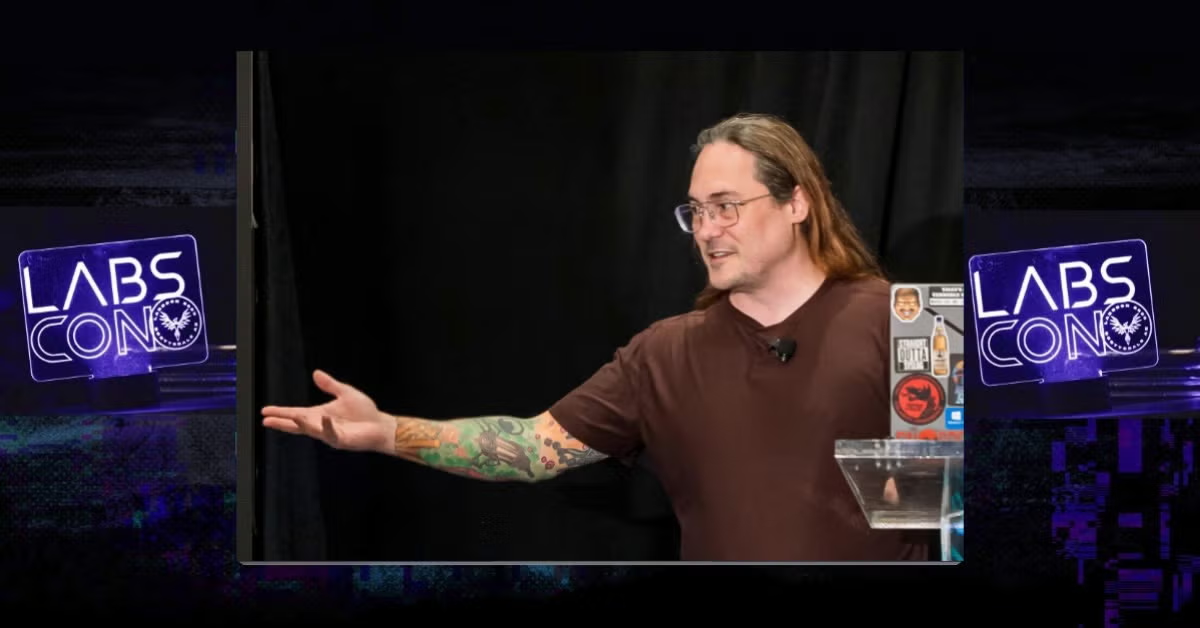
Joe FitzPatrick (@securelyfitz) is an Instructor and Researcher at SecuringHardware.com. Joe has spent most of his career working on low-level silicon debug, security validation, and penetration testing of CPUs, SoCs, and microcontrollers. He has spent the past decade developing and delivering hardware security related tools and training, instructing hundreds of security researchers, pen testers, and hardware validators worldwide. When not teaching Applied Physical Attacks training, Joe is busy developing new course content or working on contributions to the NSA Playset and other misdirected hardware projects, which he regularly presents at all sorts of fun conferences.
LABScon 2026 | Call For Papers
Submission Deadline: June 19, 2026
LABScon is a unique venue for original research to be shared among peers. The benefit of an invite-only audience of researchers is that there’s no need for long preambles or introductions – speakers are encouraged to dive right into their technical findings.
- Original content only.
- Talks are 20 minutes long + 5 minutes for Q&A.
- Workshops are 90 minutes long.
- LABScon is primarily a threat intelligence and vulnerability research conference but we keep an open-mind.
About LABScon
This presentation was featured live at LABScon 2025, an immersive 3-day conference bringing together the world’s top cybersecurity minds, hosted by SentinelOne’s research arm, SentinelLABS.
Keep up with all the latest on LABScon here.