CVE-2026-20700: Apple Patches Zero-Day Exploited in Sophisticated Cyber Attacks
SOC Prime previously highlighted Apple’s actively exploited WebKit zero-day CVE-2025-14174, a case that showed how quickly weaponized iOS flaws can move from targeted activity to real operational risk for organizations and high-value users. That same case later led to additional fixes, with CVE-2025-14174 and CVE-2025-43529 both issued in response to it, reinforcing a familiar pattern in which separate bugs are addressed as part of a broader security incident rather than in isolation.
In February 2026, that story continued with CVE-2026-20700, an exploited memory corruption vulnerability in dyld, Apple’s Dynamic Link Editor. Apple states that an attacker with memory write capability may be able to achieve arbitrary code execution, and notes the issue may have been used in an “extremely sophisticated attack” against specific targeted individuals.
Notably, with the latest update, Apple has addressed its first actively exploited zero-day in 2026. Public reporting also notes that the company patched nine zero-day vulnerabilities exploited in the wild in 2025.
Register for SOC Prime’s AI-Native Detection Intelligence Platform, backed by cutting-edge technologies and top cybersecurity expertise to outscale cyber threats and build a resilient cybersecurity posture. Click Explore Detections to access the comprehensive collection of SOC content for vulnerability exploit detection, filtered by the custom “CVE” tag.
Detections from the dedicated rule set can be applied across 40+ SIEM, EDR, and Data Lake platforms and are mapped to the latest MITRE ATT&CK® framework v18.1. Security teams can also leverage Uncoder AI to accelerate detection engineering end-to-end by generating rules directly from live threat reports, refining and validating detection logic, auto-visualizing Attack Flows, converting IOCs into custom hunting queries, and instantly translating detection code across diverse language formats.
CVE-2026-20700 Analysis
Apple clarifies that CVE-2026-20700 resides in dyld, the system component responsible for loading dynamic libraries into memory and bridging application code with system frameworks. That placement matters because vulnerabilities in foundational loader components can be valuable in real-world exploit chains that depend on how code is mapped and executed at runtime.
Apple keeps technical details limited, but it confirms two points defenders should prioritize. Apple is aware of exploitation tied to highly targeted activity, which suggests mature tradecraft rather than opportunistic attacks. Apple also confirms the impact is arbitrary code execution, which means the outcome is not only stability issues, but attacker-controlled instruction execution on the device under the right conditions.
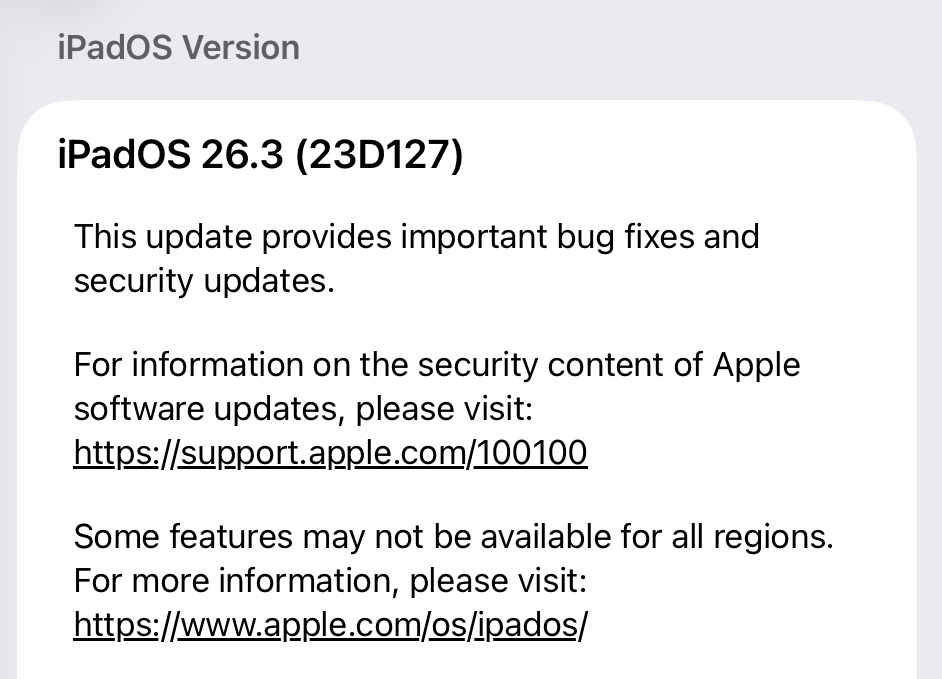
Patches for CVE-2026-20700 are available in iOS 26.3 and iPadOS 26.3, macOS Tahoe 26.3, watchOS 26.3, tvOS 26.3, and visionOS 26.3. Apply the latest Apple security updates across all supported devices, confirm that systems are running the remediated versions, and enforce and validate compliance. Users are also prompted to enable automatic updates on personal devices.
To strengthen coverage beyond patching, rely on the SOC Prime Platform to reach the world’s largest detection intelligence dataset, adopt an end-to-end pipeline that spans detection through simulation while streamlining security operations and speeding up response workflows, reduce engineering overhead, and stay ahead of emerging threats.
FAQ
What is CVE-2026-20700 and how does it work?
CVE-2026-20700 is a memory corruption vulnerability in Apple’s dyld component. Apple states that an attacker with memory write capability may be able to exploit the flaw to execute arbitrary code.
When was CVE-2026-20700 first discovered?
Apple publicly disclosed and patched CVE-2026-20700 in its February 11, 2026 security release.
What is the impact of CVE-2026-20700 on organizations and users?
Successful exploitation can result in arbitrary code execution, which is dangerous because it can enable deeper compromise depending on the attacker’s access and the device’s role in the environment.
Can CVE-2026-20700 still affect me in 2026?
Yes. Devices running vulnerable versions, especially those not updated to the patched OS releases, can remain exposed.
How can you protect from CVE-2026-20700?
Update Apple devices to the latest available security release for your OS line, including iOS 26.3,iPadOS 26.3, and macOS Tahoe 26.3, where applicable. Enable automatic updates where possible and verify patch coverage, particularly if you maintain older OS branches that may require separate backported fixes.
The post CVE-2026-20700: Apple Patches Zero-Day Exploited in Sophisticated Cyber Attacks appeared first on SOC Prime.