Visualização de leitura
ZDI-26-316: Siemens Simcenter Femap IPT File Parsing Memory Corruption Remote Code Execution Vulnerability
ZDI-26-315: Apple macOS USD Out-Of-Bounds Read Information Disclosure Vulnerability
ZDI-26-314: Apple macOS USD File Parsing Out-Of-Bounds Write Remote Code Execution Vulnerability
ZDI-26-313: Apple Safari Regular Expression Duplicate Named Groups Heap-based Buffer Overflow Remote Code Execution Vulnerability
ZDI-26-312: Apple Safari Web Inspector WebCore Style Resolver Use-After-Free Remote Code Execution Vulnerability
ZDI-26-311: Apple macOS CoreSymbolication Out-Of-Bounds Read Information Disclosure Vulnerability
ZDI-26-310: Microsoft Windows splwow64 Race Condition Local Privilege Escalation Vulnerability
ZDI-26-309: Microsoft Windows Message Queueing Double Free Local Privilege Escalation Vulnerability
ZDI-26-308: Ivanti Endpoint Manager RemoteControlAuth Exposed Dangerous Method Information Disclosure Vulnerability
A year of Apple Security Bounty research — 16 closed findings, full disclosure
Spent 2024–2025 filing Apple Security Bounty reports. All 16 are now closed. I've written up every one — including the ones Apple were right to reject, the ones where my own PoC was lying to me, and the few where I couldn't bridge the gap between binary evidence and a working exploit. No hype, no CVE-farming. [link] [comments]
AI-Coded App Vulnerability Checklist - 33 LLM-specific items with detection methods
Recently saw a post '20 common AI-coded app vulnerabilities', and thought to myself that 20 is nice but very optimistic, as an avid AI user for years now I personally saw more than 20 on every project that was not ai-written in a targeted manner, but as huge chunks. So, I got my good friends Claude, ChatGPT, Gemini and Grok to help me throw few more into it. Initial thought was to package as a vulnerability scanner, but... would rather not even attempt to earn on vulnerabilities and instead encourage users to run audits for keeping all free, open source and with an ability to contribute. And here it is:
Open source checklist of 258 vulnerabilities common in applications built with AI coding assistants. 17 categories. Detection method ([S] static, [R] runtime, [C] config) and severity rating on every item.
The part that isn't in existing references - Category 6, 33 items specific to LLM integration. Some of the less-obvious ones:
6.26 - MCP tool poisoning: attacker-controlled MCP server injects instructions into tool results the agent reads as trusted input. Detection: static analysis of MCP server config plus runtime inspection of tool result handling before prompt injection.
6.27 - Agent memory poisoning: malicious content written to long-term memory (vector DB, key-value store, file) is retrieved in a future session and executed in context. Detection: audit memory write paths for content validation before storage.
6.30 - Cross-agent prompt injection: orchestrator passes Agent A's output as Agent B's input without sanitization or trust boundary. Detection: static analysis of multi-agent orchestration code.
6.31 - Insecure agent handoff: parent agent passes full API keys/session tokens to sub-agents rather than scoped credentials with minimum required permissions.
Companion prompt.md runs all 258 checks against a codebase using Claude Code or any capable LLM CLI. Returns file paths, line numbers, code snippets, specific remediations.
Apache 2.0. license - so anyone willing to do anything around this are open to do so.
[link] [comments]
[GUEST DIARY] Tearing apart website fraud to see how it works., (Wed, May 13th)
[This is a Guest Diary by Joshua Nikolson, an ISC Intern and part of the SANS.edu Bachelor's degree in Applied Cybersecurity (BACS) program.]
Introduction
One day at work, a friend messaged me, “How do you check a website to see if it’s legit?” This friend recently received a phishing text message from a “bank”, and I figured he wanted to be careful and double-check. I told him to put the URL into VirusTotal but said that just because it may say it’s clean, that doesn’t mean it’s not malicious.
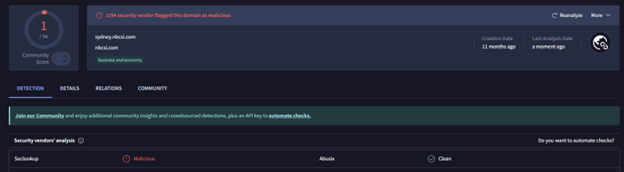
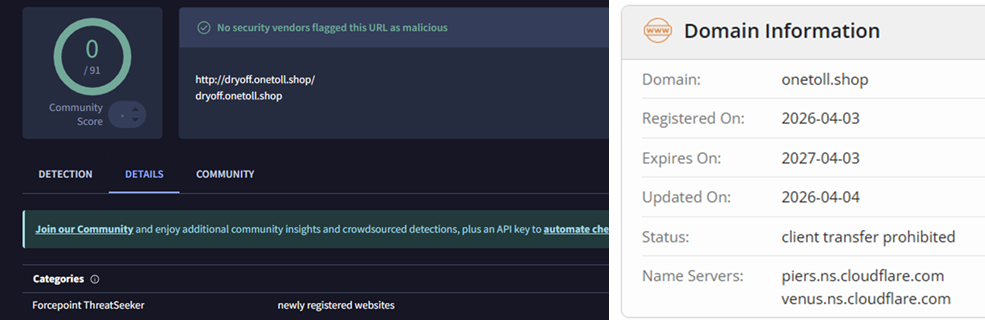
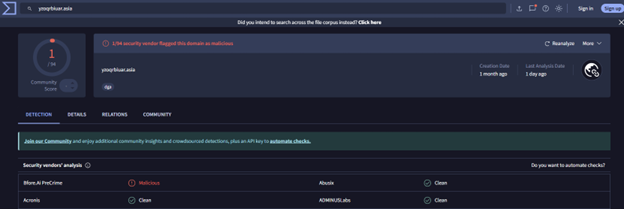
He sent me a screenshot of the VirusTotal page for the URL, with no detections and everything showing green. I took a moment to look at it a little more closely. The domain name was unusual, and right off the bat I could see it had been created in the last few months. As of now, it has one detection from a vendor. All domains mentioned in this blogpost will be listed in the Indicators of Compromise section at the end.
Going to the site, I could immediately tell that something was off about it. It was a secondhand marketplace that seemed to sell just about everything under the sun, with tons of listings in each category and items priced too good to be true. While the site had that “AI vibecoded feeling”, I wanted to give my friend something more concrete other than “don’t trust this site”.
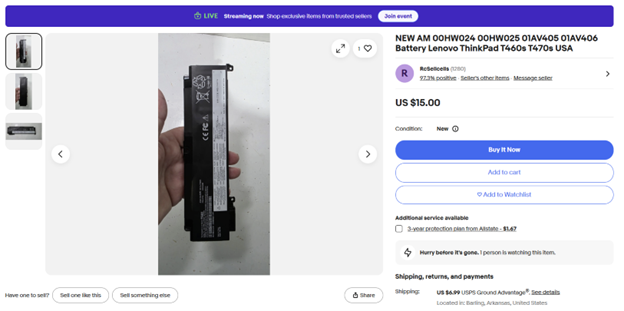
I decided to reverse image search one of the product images, a Lenovo ThinkPad battery replacement, and after some digging, I found an eBay listing with all the same product images and item descriptions. I did this for a few more of the site’s listings and came to the same result. I let my friend know, and he said, “Yeah, it looked too good to be true”.
Finding a Marketplace
I found this interesting and wanted to see if I could find something similar again. Today, it is trivial to use AI to mass-deploy these scams, and I wanted to see what would happen if I tried to buy something.
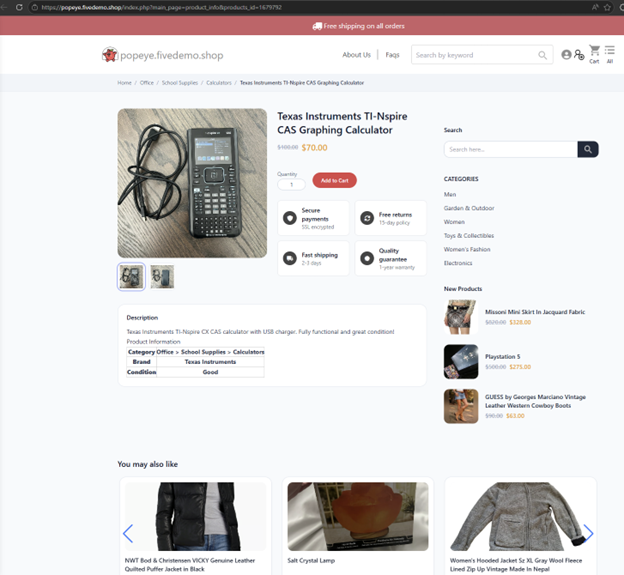
Let’s look up what my friend was originally looking for: a Texas Instruments TI-nSpire CAS calculator. Simply searching on Google and going to the second page, something pops out to me. Why is a driving school selling a calculator?
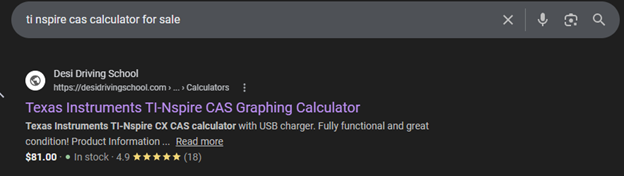
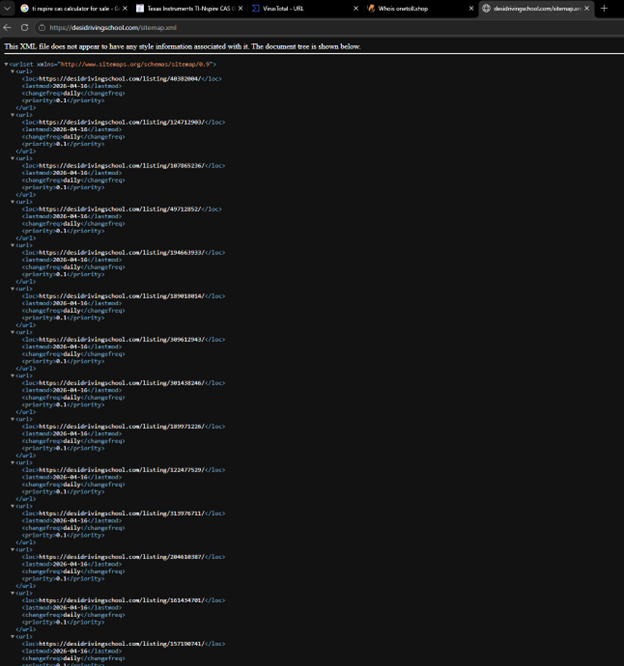
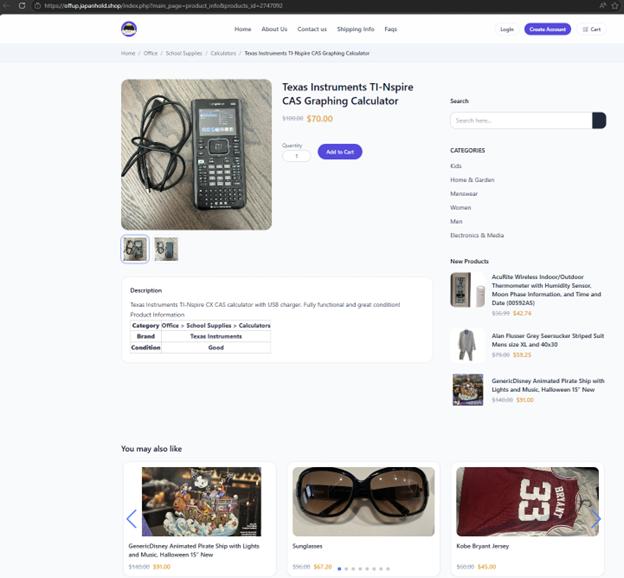
The search result link, hxxps://desidrivingschool[.]com/listing/164903741/ redirects to a marketplace where it is for sale:
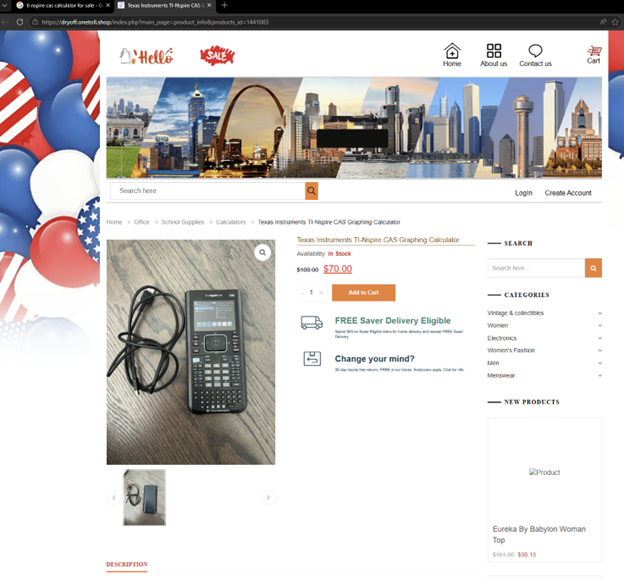
This domain looks suspicious on its own, and to add insult to injury, it was registered ~12 days ago on April 3rd, 2026:
What's happening here?
You may be asking why this Desi Driving School is showing up in the search results for this calculator? Good question. If you append “/sitemap.xml” to the URL, you can see tons of these listings that are meant to infiltrate the search results. This is a prime example of SEO poisoning, in which potential victims are lured through their shopping searches to these fake marketplaces.
Threat actors have previously used compromised WordPress sites as command-and-control infrastructure or to stage payloads, but this is being used as a distinct attack vector. Unfortunately, this website was likely compromised, whether through something like a malicious WordPress plugin or stolen credentials, and is now being used to drive traffic to this malicious marketplace:
You can see the range of products that this site offers. They must have a good distribution network.
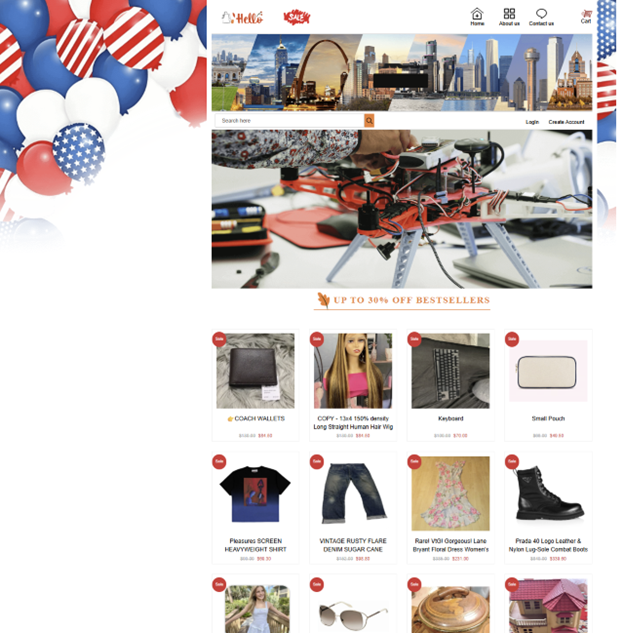
While reverse-image searching for images of the calculator, I found another similar posting on a different fake marketplace. Same images, same description and title, same exact setup with a redirect…

And another… with what looks like loads of other compromised sites being used.
You can endlessly find these sites by searching any description of a product listed with quotes in Google to find the real item that is being sold and copied from, such as this blazer:
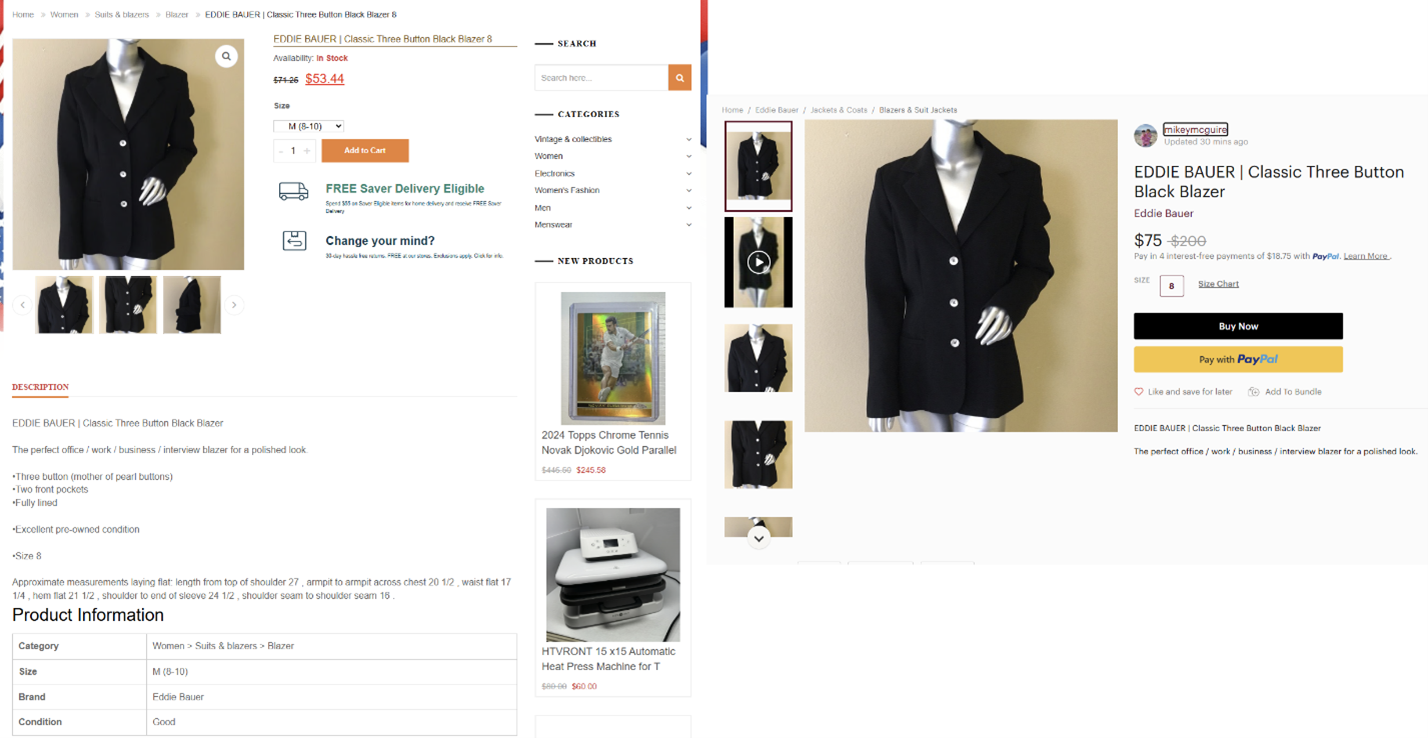
If the price was higher than the actual listing, you might think the scheme is just scraping listings, posting them at a higher price, then purchasing the cheaper item and shipping it. However, I do not think that is the case. Let’s try to buy this Eddie Bauer blazer with a fake identity and a fake debit card from Privacy.com and see what happens.
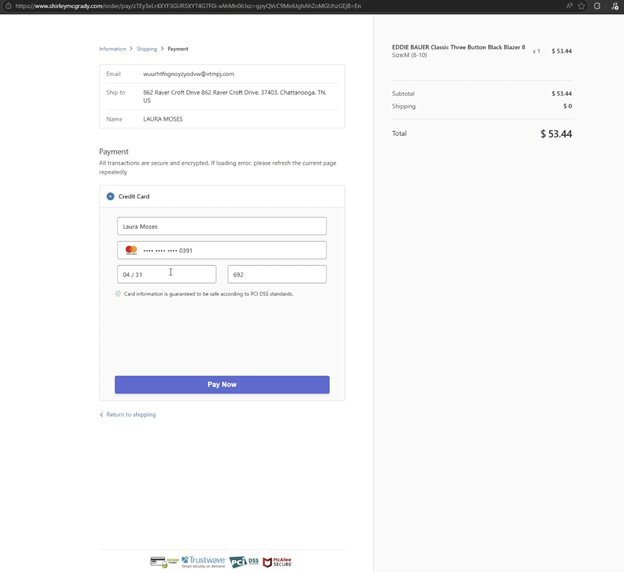
Right away, I can tell this checkout page is a replica of the Shopify checkout page and looks almost identical.
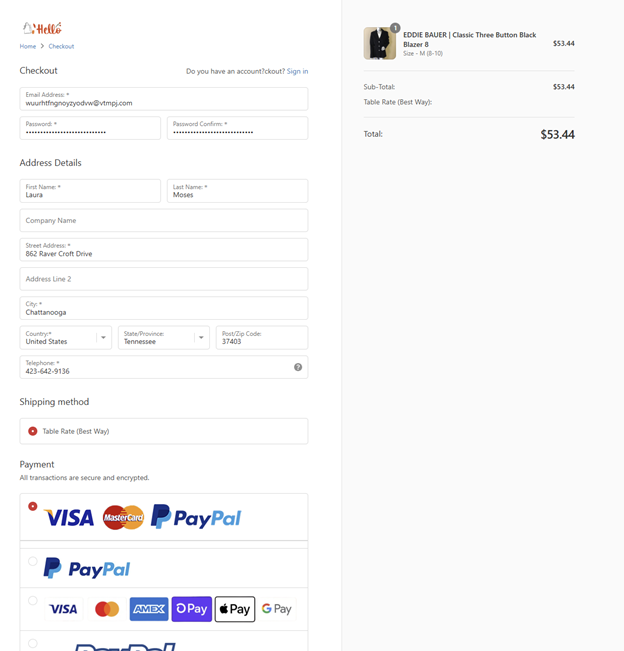
Choosing Mastercard, we’ll check out and pay now. Let’s prepare my fake card. Creating a temporary debit card with a $5 spending limit is extremely easy with Privacy.com, and I have my Mastercard ready.
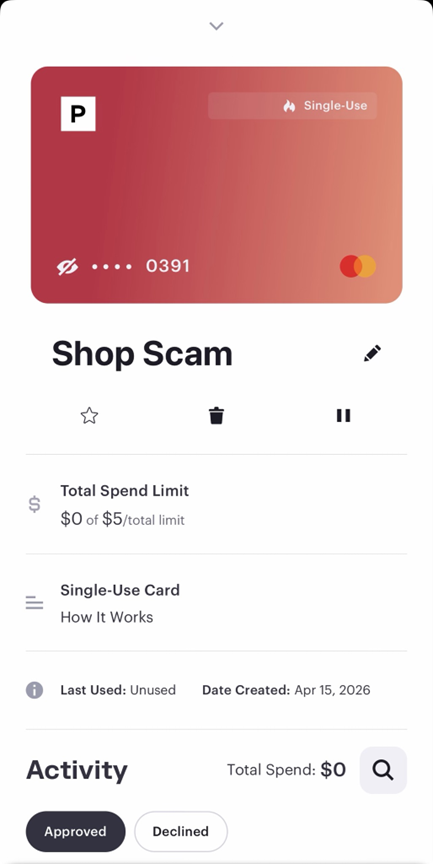
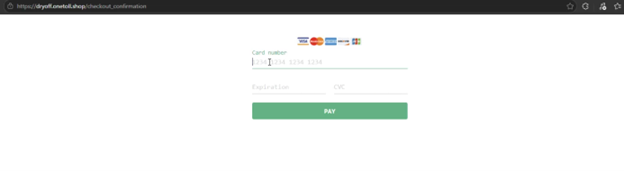
First, I am instructed to enter my card here:
Then I get redirected to this page and must enter my information again:
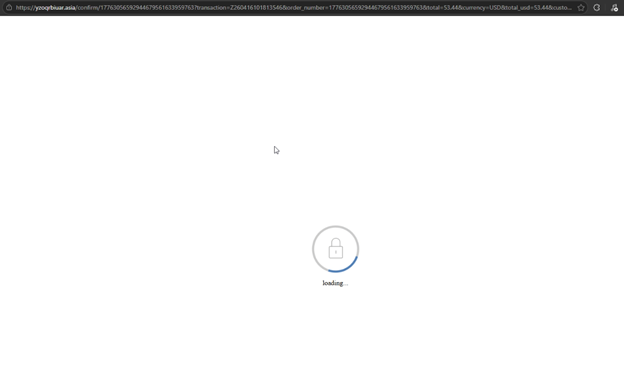
After hitting pay now, a loading screen with a different URL is shown that reminds me of the PayPal loading screen:
And then I am redirected to a thank-you page for my order, despite the card being declined, which they know because it shows failure_code=failed in the URL.
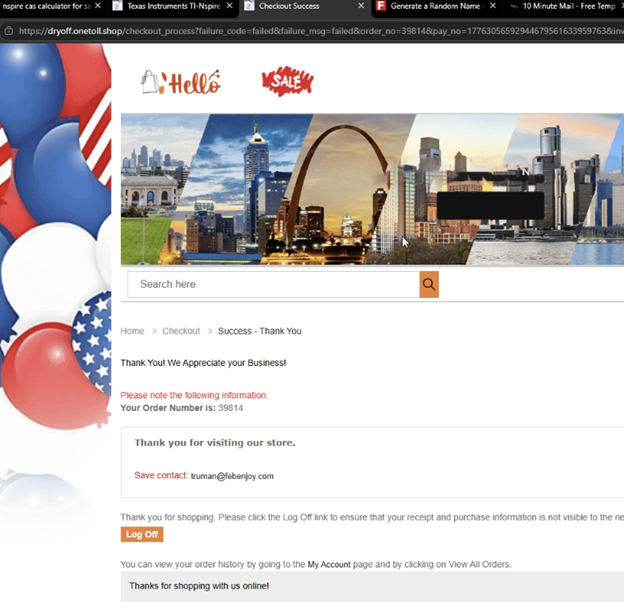
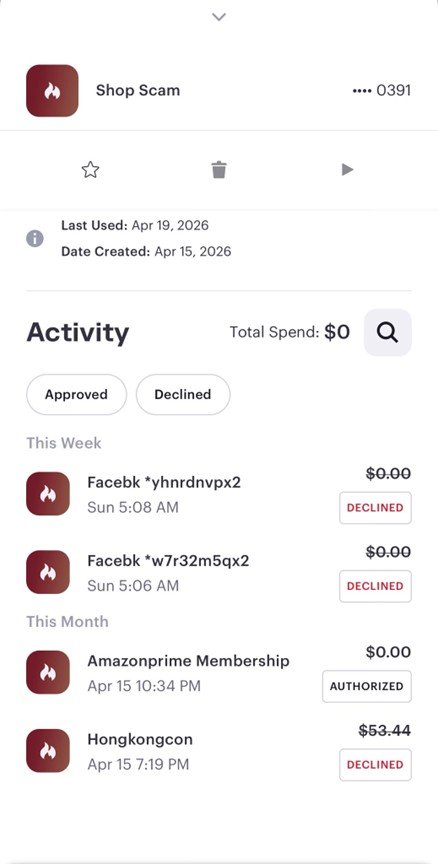
Only one declined charge was seen on my card. However, in other testing instances, I have seen an additional charge at a different price than the “advertised product”.
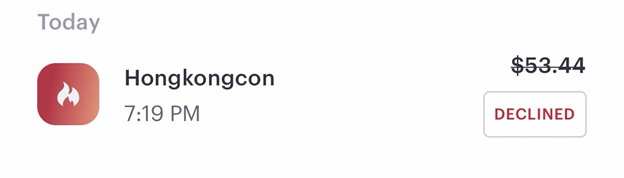
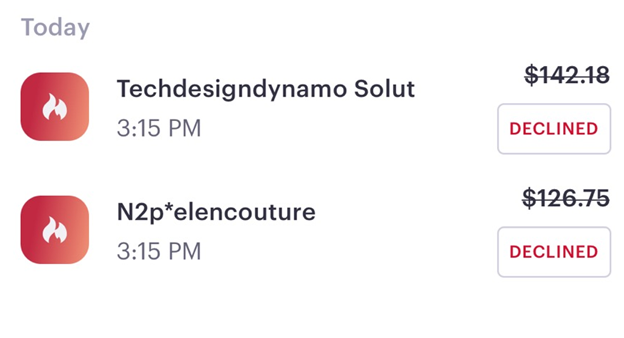
The above screenshot is from the order we just made, and this next screenshot is from a different test where two charges were attempted right away on order:
It seems that shirleymcgrady is another similar site, but probably used as the main checkout for the other smaller sites.
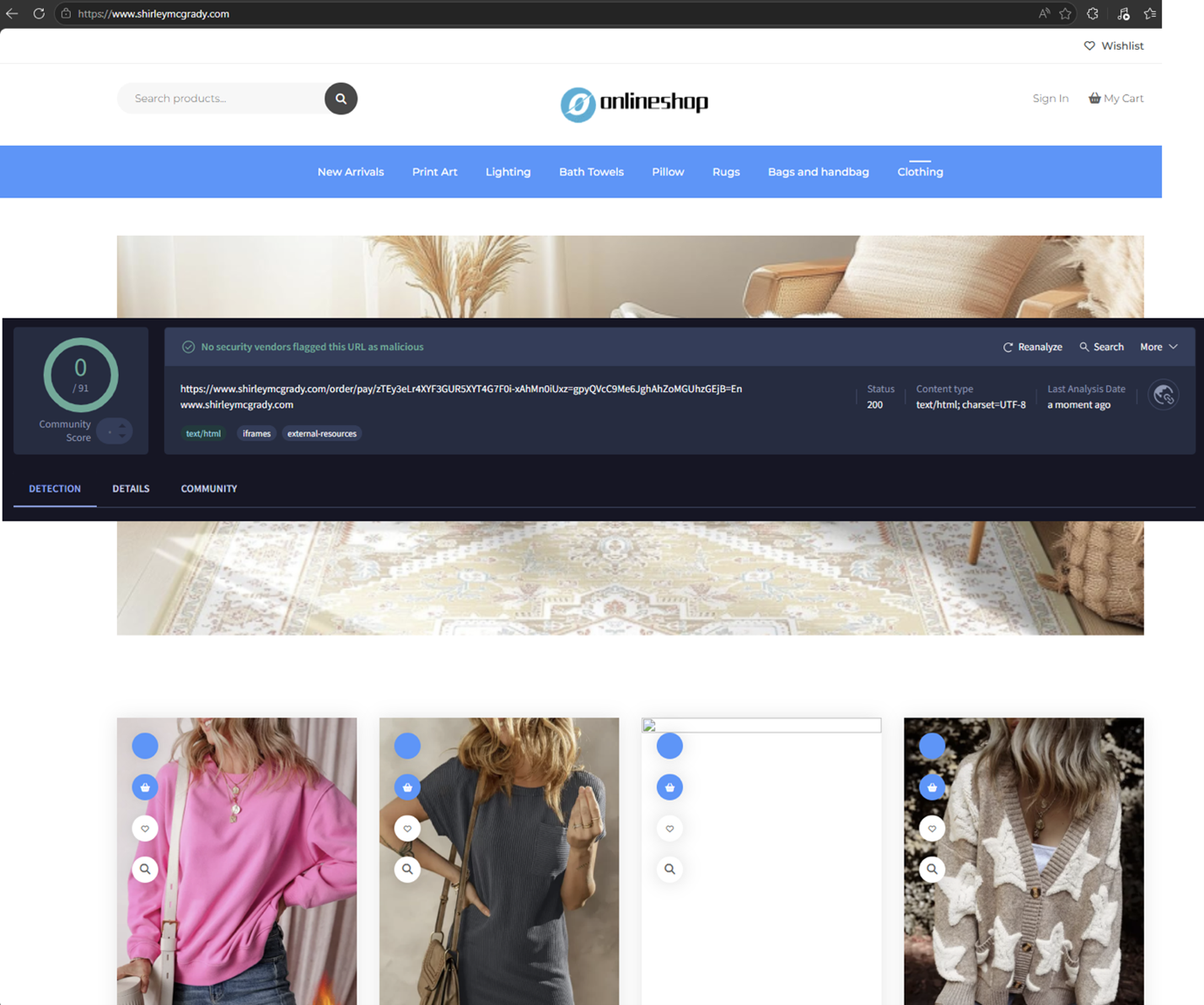
The loading page domain from the payment was also created recently, 1 month ago, with one detection on VirusTotal.
Aftermath
A few days after I tried to check out, multiple other charges were attempted on the card:
The clear objective of the scam here is to have the victim make a payment for an item that will never be shipped, resulting in their personal and payment information being stolen. I can only imagine how many people were duped by these marketplaces, considering their popularity, and it must be paying off for the attackers.
With the evolving expertise of AI tools and technology in general, attackers can create these campaigns in a matter of seconds. This takes advantage of the average person’s trust by having a high-ranking site in the search results, images that look real (because they are real, and stolen), and a site that seems trustworthy enough for someone to enter their card details.
I would love to take this a step further and use a card with more funds to purchase a lower-cost item to see how different, if at all, the result would be. It is also fun to hunt down these different marketplaces and see how many you can find. Annoyingly, some of them use registrars that make it harder, not easier, to report abuse, but if anyone reading this would like to investigate this further, I would love to offer my help and see what we can do about it.
Indicators of Compromise
Marketplace Domains:
sydney.nbcsi[.]com
dryoff.onetoll[.]shop
popeye.fivedemo[.]shop
offup.japanhold[.]shop
Redirector Domains:
desidrivingschool[.]com
curencares[.]in
abralipedema.com[.]br
Payment Page Domains:
shirleymcgrady[.]com
yzoqrbiuar[.]asia
ISC Stormcast For Wednesday, May 13th, 2026 https://isc.sans.edu/podcastdetail/9930, (Wed, May 13th)
Proxying the Unproxyable? Sending EXE traffic to a Proxy, (Wed, May 13th)
.. if “unproxyable” is a word that is ..
I had a recent engagement where I had to look at the network traffic generated by a Windows executable. Unfortunately, it was all TLS, and all TLS1.3 to boot. So from a PCAP all I got was a whole lot of “yup, that’s encrypted”, and since it was TLSv1.3 all I really had to work with was the IP addresses, not even server names in the server hello packets to help out. And the IP addresses involved were those “500 DNS names AWS” shotgun addresses, so no help there.
What I really needed was something to take specific traffic, say traffic from an executable, and redirect that to a proxy. If that proxy is then burp suite, then Bob’s yer Uncle, now I can look at the traffic!! If you’d rather use fiddler or some other proxy, go for it, anything will work.
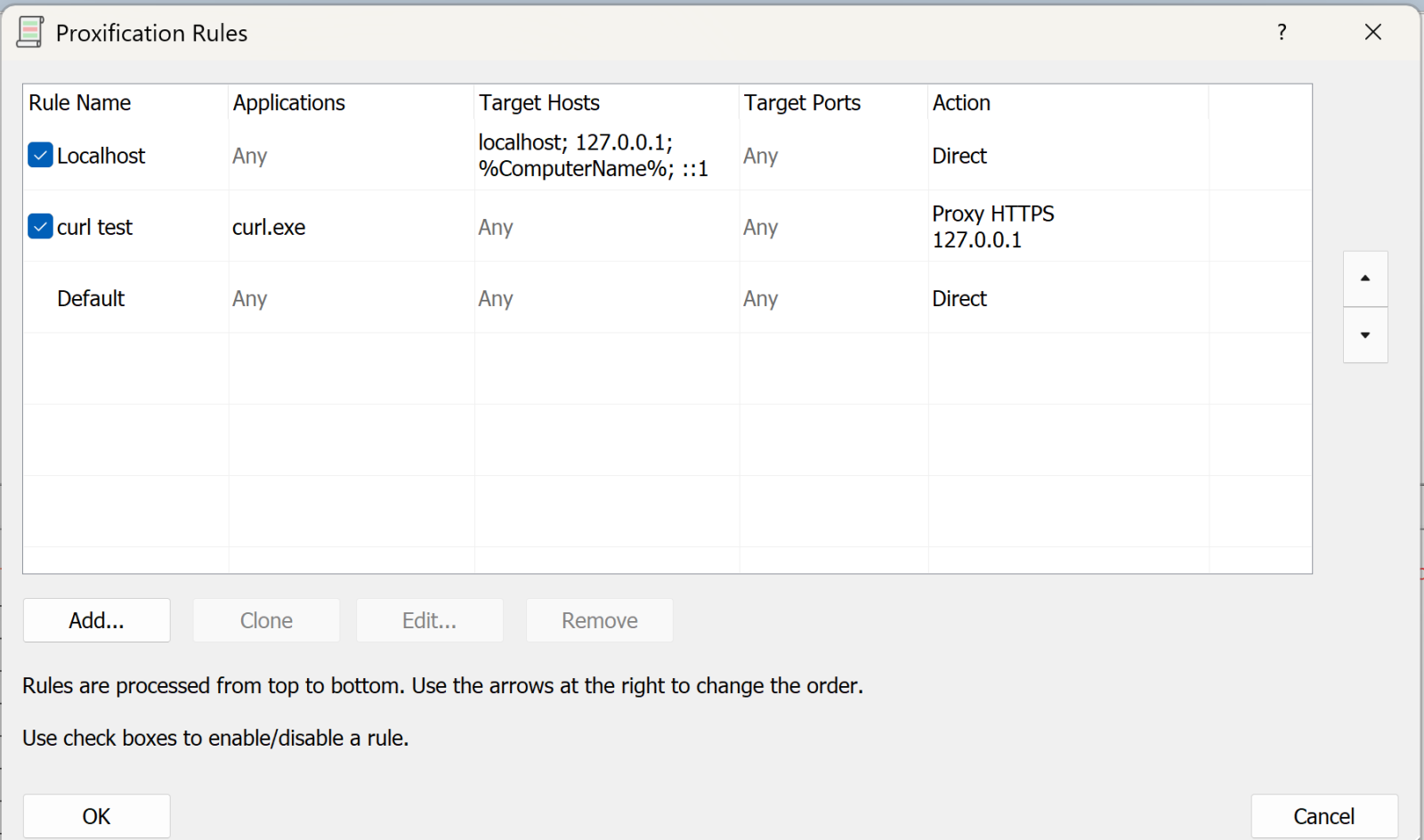
A few minutes of Googling, and I found Proxifier (https://www.proxifier.com/)
Proxifier allows you set up rules, for instance “send traffic from abc.exe to proxy A”, “send traffic from def.exe to proxy B”, or “send everything else direct”, or any combination. Proxies can be direct or Socks5.
In my case, I was looking at a client executable, and was able to follow all the API calls and data transferred, it was EXACTLY what I needed that day.
I can’t show you the client output - watching the API’s roll by was as cool as it gets though, and the proxy intercept in burp lets you “play” with individual calls if that’s what you need. But I can certainly show you how this works, let’s use curl as our example exe.
Let's start in proxifier. First you need to set up your proxy(s). In this case I'm using Burp Suite Pro running locally, so the proxy is:
.png)
Next, we’ll set up the rules:
The first rule says “anything to my own machine, send direct”. Given how much loopback cruft happens on a typical Windows box, this rule is gold (unless that’s what you are looking for that is).
The second rule is “anything from curl.exe, send to the proxy we just defined” (or whatever your executable is).
You can have multiple of these rules doing different things.
The final rule is “everything else, send direct”
Now, let’s run a test with curl:
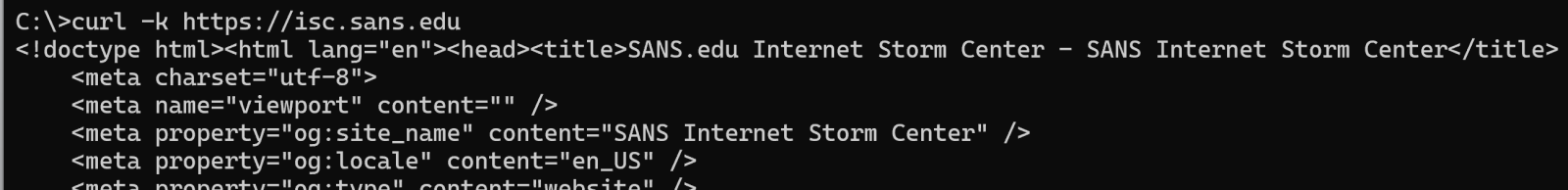
(and so on)
On proxifier, you see the transaction happen in real time:
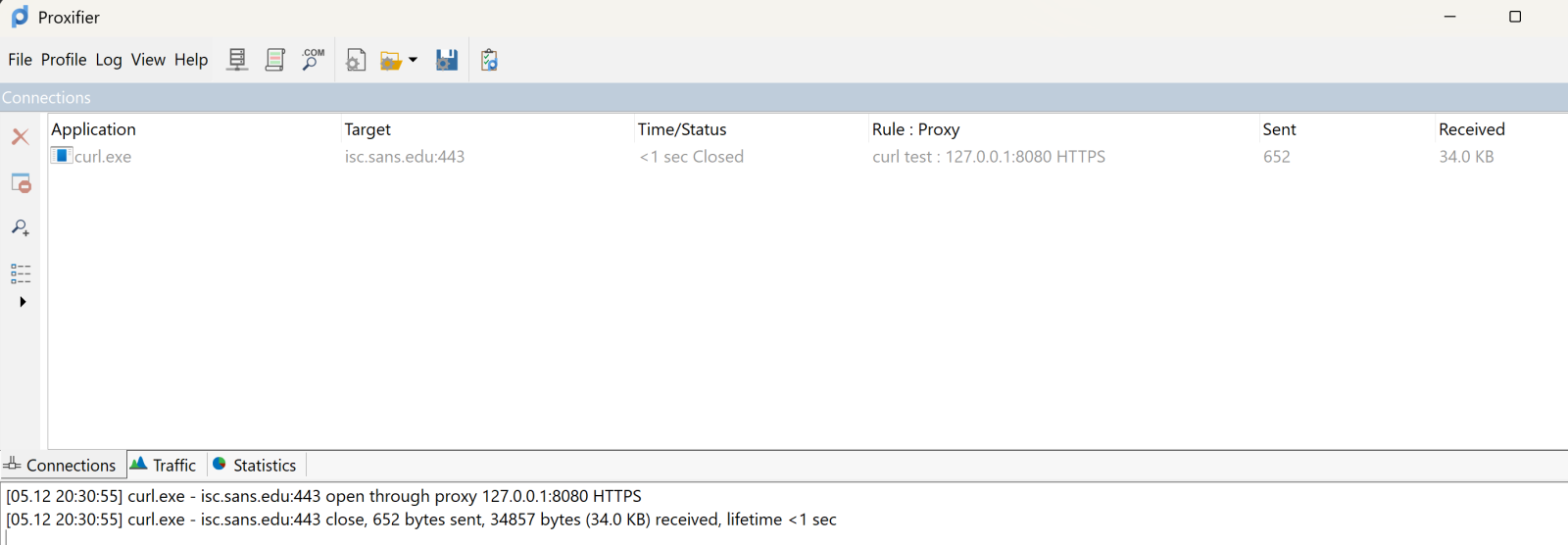
The top pane shows the executable, target and so on. It’s somewhat ephemeral, it’ll show the live view, then will go grey after the transaction complets, then after a few second disappears. The bottom pane scrolls in a more “log like” manner.
Over in Burp, you see all the business that most sites have as their lead page:
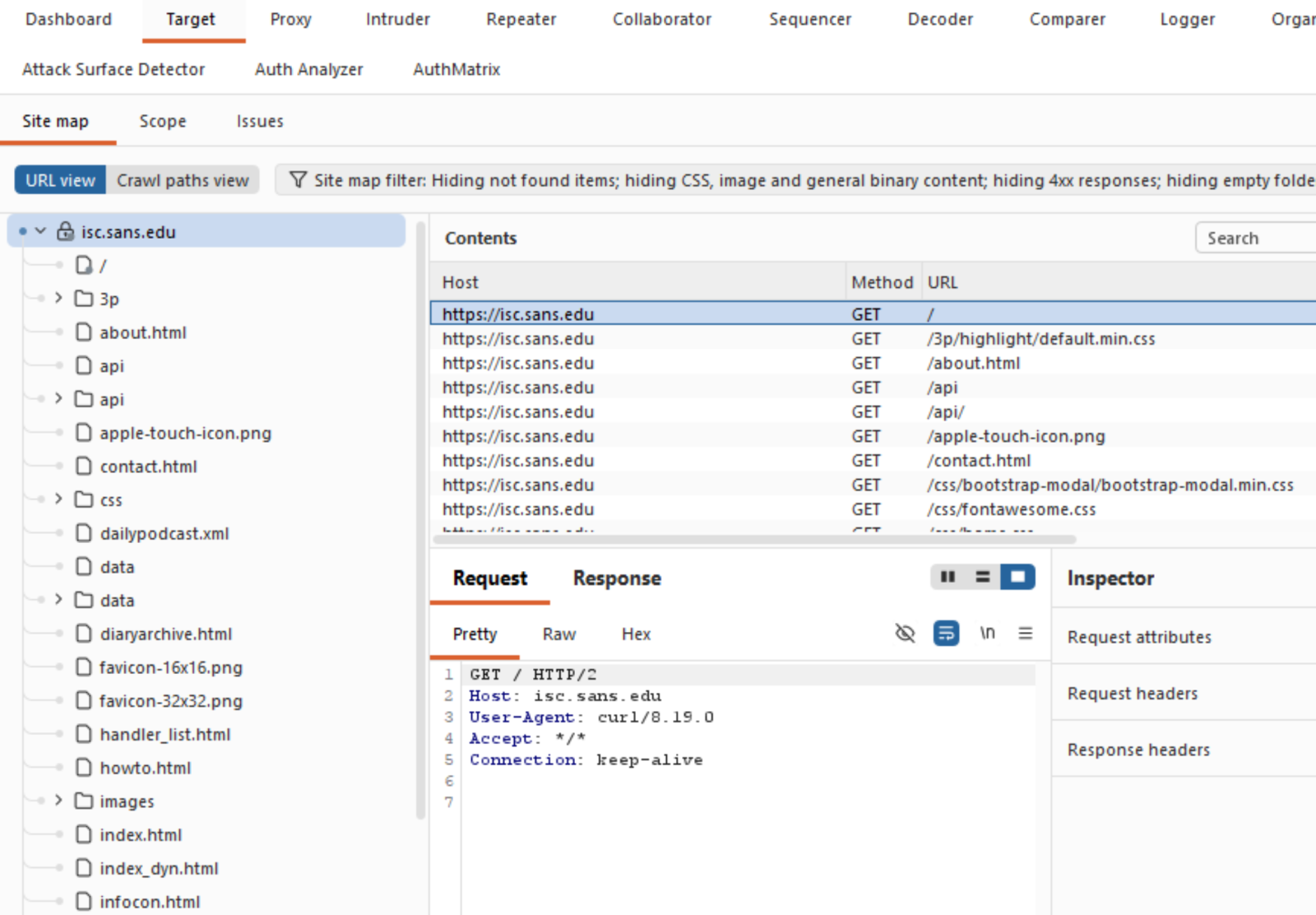
Which is exactly what you need, and can't get these days from a packet capture!
What else does Proxifier do? It also spits out a configurable log file, you can configure what’s in the logs and where to send it:
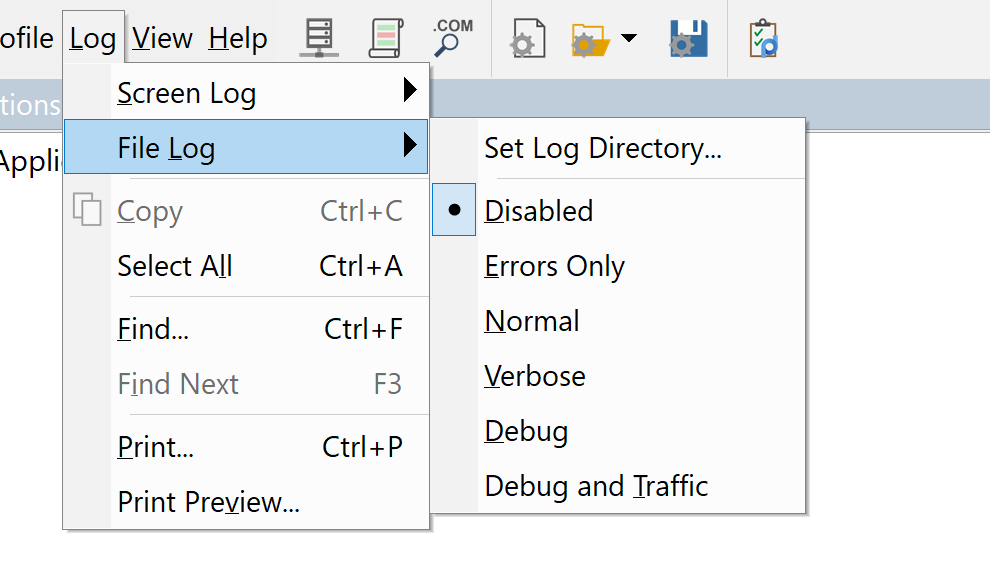
You can set similar sensitivity on the live on-screen log.
All in all, this tool was a life-saver for me, I’ve used it for a few years now and keep coming up with things that it can bail me out of!
Got a cool use for a tool like this? Give it a try and share your experiences in our comment form below (please keep any NDA’s in mind).
Do you have a similar or better tool for this, again, by all means share in our comment form!
===============
Rob VandenBrink
rob@coherentsecurity.com
Microsoft May 2026 Patch Tuesday, (Tue, May 12th)
Today's Microsoft patch Tuesday fixes 137 different vulnerabilities. In addition, the update addresses 137 Chromium-related issues affecting Microsoft Edge.
There are no already disclosed or already exploited vulnerabilities included in today's patches. I removed the Chromium issues from the table below and included only the 137 Microsoft issues to make it more readable.
Note that issues related to Microsoft Azure are labeled as "no customer action required.
Significant Vulnerabilities of interest:
CVE-2026-41103: This vulnerability affects the Microsoft SSO Plugin for Jira & Confluence. Exploitation could lead to an elevation of privileges. With ongoing supply chain attacks, development and CI/CD tools like Jira and Confluence are popular targets.
CVE-2026-41089: A preauthentication remote code execution vulnerability in the Netlogon service will always be a juicy target, worth some AI tokens to write an exploit for.
Other critical vulnerabilities include the usual Word and Microsoft Office issues.
| Description | |||||||
|---|---|---|---|---|---|---|---|
| CVE | Disclosed | Exploited | Exploitability (old versions) | current version | Severity | CVSS Base (AVG) | CVSS Temporal (AVG) |
| .NET Core Tampering Vulnerability | |||||||
| %%cve:2026-32175%% | No | No | - | - | Important | 4.3 | 3.8 |
| .NET Elevation of Privilege Vulnerability | |||||||
| %%cve:2026-32177%% | No | No | - | - | Important | 7.3 | 6.4 |
| %%cve:2026-35433%% | No | No | - | - | Important | 7.3 | 6.4 |
| ASP.NET Core Denial of Service Vulnerability | |||||||
| %%cve:2026-42899%% | No | No | - | - | Important | 7.5 | 6.5 |
| Azure AI Foundry Elevation of Privilege Vulnerability (no customer action required) |
|||||||
| %%cve:2026-35435%% | No | No | - | - | Critical | 8.6 | 7.5 |
| Azure Cloud Shell Spoofing Vulnerability (no customer action required) |
|||||||
| %%cve:2026-35428%% | No | No | - | - | Critical | 9.6 | 8.3 |
| Azure Connected Machine Agent Elevation of Privilege Vulnerability | |||||||
| %%cve:2026-40381%% | No | No | - | - | Important | 7.8 | 6.8 |
| Azure DevOps Information Disclosure Vulnerability (no customer action required) |
|||||||
| %%cve:2026-42826%% | No | No | - | - | Critical | 10.0 | 8.7 |
| Azure Logic Apps Elevation of Privilege Vulnerability | |||||||
| %%cve:2026-42823%% | No | No | - | - | Important | 9.9 | 8.6 |
| Azure Machine Learning Notebook Spoofing Vulnerability (no customer action required) |
|||||||
| %%cve:2026-32207%% | No | No | - | - | Critical | 8.8 | 7.7 |
| %%cve:2026-33833%% | No | No | - | - | Important | 8.2 | 7.1 |
| Azure Managed Instance for Apache Cassandra Remote Code Execution Vulnerability (no customer action required) |
|||||||
| %%cve:2026-33109%% | No | No | - | - | Critical | 9.9 | 8.6 |
| %%cve:2026-33844%% | No | No | - | - | Critical | 9.0 | 7.8 |
| Azure Monitor Action Group Notification System Elevation of Privilege Vulnerability (no customer action required) |
|||||||
| %%cve:2026-41105%% | No | No | - | - | Critical | 8.1 | 7.1 |
| Azure Monitor Agent Elevation of Privilege Vulnerability | |||||||
| %%cve:2026-32204%% | No | No | - | - | Important | 7.8 | 6.8 |
| Azure Monitor Agent Metrics Extension Elevation of Privilege Vulnerability | |||||||
| %%cve:2026-42830%% | No | No | - | - | Important | 6.5 | 5.7 |
| Azure SDK for Java Security Feature Bypass Vulnerability | |||||||
| %%cve:2026-33117%% | No | No | - | - | Important | 9.1 | 7.9 |
| Copilot Chat (Microsoft Edge) Information Disclosure Vulnerability (no customer action required) |
|||||||
| %%cve:2026-33111%% | No | No | - | - | Critical | 7.5 | 6.5 |
| Data Deduplication Elevation of Privilege Vulnerability | |||||||
| %%cve:2026-41095%% | No | No | - | - | Important | 7.8 | 6.8 |
| GitHub Copilot and Visual Studio Code Security Feature Bypass Vulnerability | |||||||
| %%cve:2026-41109%% | No | No | - | - | Important | 8.8 | 7.7 |
| Internet Key Exchange (IKE) Protocol Denial of Service Vulnerability | |||||||
| %%cve:2026-35424%% | No | No | - | - | Important | 7.5 | 6.5 |
| M365 Copilot Information Disclosure Vulnerability (no customer action required) |
|||||||
| %%cve:2026-26129%% | No | No | - | - | Critical | 7.5 | 6.5 |
| %%cve:2026-26164%% | No | No | - | - | Critical | 7.5 | 6.5 |
| M365 Copilot for Desktop Spoofing Vulnerability | |||||||
| %%cve:2026-41614%% | No | No | - | - | Important | 6.2 | 5.4 |
| Microsoft 365 Copilot for Android Spoofing Vulnerability | |||||||
| %%cve:2026-41100%% | No | No | - | - | Important | 4.4 | 3.9 |
| Microsoft Cryptographic Services Elevation of Privilege Vulnerability | |||||||
| %%cve:2026-40377%% | No | No | - | - | Important | 7.8 | 6.8 |
| Microsoft Data Formulator Remote Code Execution Vulnerability | |||||||
| %%cve:2026-41094%% | No | No | - | - | Important | 8.8 | 7.7 |
| Microsoft Dynamics 365 Business Central Elevation of Privilege Vulnerability | |||||||
| %%cve:2026-40417%% | No | No | - | - | Important | 7.8 | 6.8 |
| Microsoft Dynamics 365 Customer Insights Elevation of Privilege Vulnerability (no customer action required) |
|||||||
| %%cve:2026-33821%% | No | No | - | - | Critical | 7.7 | 6.7 |
| Microsoft Dynamics 365 On-Premises Remote Code Execution Vulnerability | |||||||
| %%cve:2026-42898%% | No | No | - | - | Critical | 9.9 | 8.6 |
| %%cve:2026-42833%% | No | No | - | - | Important | 9.1 | 7.9 |
| Microsoft Edge (Chromium-based) Elevation of Privilege Vulnerability | |||||||
| %%cve:2026-42838%% | No | No | - | - | Important | 5.4 | 4.7 |
| Microsoft Edge (Chromium-based) Information Disclosure Vulnerability | |||||||
| %%cve:2026-41107%% | No | No | - | - | Moderate | 7.4 | 6.4 |
| Microsoft Edge (Chromium-based) for Android Spoofing Vulnerability | |||||||
| %%cve:2026-42891%% | No | No | - | - | Moderate | 6.5 | 5.7 |
| %%cve:2026-35429%% | No | No | - | - | Moderate | 4.3 | 3.9 |
| %%cve:2026-40416%% | No | No | - | - | Low | 4.3 | 3.8 |
| Microsoft Enterprise Security Token Service (ESTS) Spoofing Vulnerability (no customer action required) |
|||||||
| %%cve:2026-40379%% | No | No | - | - | Critical | 9.3 | 8.1 |
| Microsoft Excel Information Disclosure Vulnerability | |||||||
| %%cve:2026-40360%% | No | No | - | - | Important | 7.8 | 6.8 |
| Microsoft Excel Remote Code Execution Vulnerability | |||||||
| %%cve:2026-40359%% | No | No | - | - | Important | 7.8 | 6.8 |
| %%cve:2026-40362%% | No | No | - | - | Important | 7.8 | 6.8 |
| Microsoft Message Queuing (MSMQ) Remote Code Execution Vulnerability | |||||||
| %%cve:2026-34329%% | No | No | - | - | Important | 8.8 | 7.7 |
| Microsoft Office Click-To-Run Elevation of Privilege Vulnerability | |||||||
| %%cve:2026-40419%% | No | No | - | - | Important | 7.8 | 6.8 |
| %%cve:2026-40418%% | No | No | - | - | Important | 7.8 | 6.8 |
| %%cve:2026-35436%% | No | No | - | - | Important | 8.8 | 7.7 |
| %%cve:2026-40420%% | No | No | - | - | Important | 8.8 | 7.7 |
| Microsoft Office Remote Code Execution Vulnerability | |||||||
| %%cve:2026-40363%% | No | No | - | - | Critical | 8.4 | 7.3 |
| %%cve:2026-42831%% | No | No | - | - | Critical | 7.8 | 6.8 |
| %%cve:2026-40358%% | No | No | - | - | Critical | 8.4 | 7.3 |
| Microsoft Office Spoofing Vulnerability | |||||||
| %%cve:2026-42832%% | No | No | - | - | Important | 7.7 | 6.7 |
| Microsoft Outlook for iOS Tampering Vulnerability | |||||||
| %%cve:2026-42893%% | No | No | - | - | Important | 7.4 | 6.4 |
| Microsoft Partner Center Spoofing Vulnerability (no customer action required) |
|||||||
| %%cve:2026-34327%% | No | No | - | - | Critical | 8.2 | 7.1 |
| Microsoft Power Automate Desktop Information Disclosure Vulnerability | |||||||
| %%cve:2026-40374%% | No | No | - | - | Important | 6.5 | 5.7 |
| Microsoft PowerPoint for Android Spoofing Vulnerability | |||||||
| %%cve:2026-41102%% | No | No | - | - | Important | 7.1 | 6.2 |
| Microsoft SSO Plugin for Jira & Confluence Elevation of Privilege Vulnerability | |||||||
| %%cve:2026-41103%% | No | No | - | - | Critical | 9.1 | 7.9 |
| Microsoft SharePoint Server Remote Code Execution Vulnerability | |||||||
| %%cve:2026-35439%% | No | No | - | - | Important | 8.8 | 7.7 |
| %%cve:2026-40368%% | No | No | - | - | Important | 8.0 | 7.0 |
| %%cve:2026-33110%% | No | No | - | - | Important | 8.8 | 7.7 |
| %%cve:2026-33112%% | No | No | - | - | Important | 8.8 | 7.7 |
| %%cve:2026-40357%% | No | No | - | - | Important | 8.8 | 7.7 |
| %%cve:2026-40365%% | No | No | - | - | Critical | 8.8 | 7.7 |
| Microsoft Team Events Portal Information Disclosure Vulnerability (no customer action required) |
|||||||
| %%cve:2026-33823%% | No | No | - | - | Critical | 9.6 | 8.3 |
| Microsoft Teams Spoofing Vulnerability | |||||||
| %%cve:2026-32185%% | No | No | - | - | Important | 5.5 | 4.8 |
| Microsoft Word Information Disclosure Vulnerability | |||||||
| %%cve:2026-35440%% | No | No | - | - | Important | 5.5 | 4.8 |
| %%cve:2026-40421%% | No | No | - | - | Important | 4.3 | 3.8 |
| Microsoft Word Remote Code Execution Vulnerability | |||||||
| %%cve:2026-40364%% | No | No | - | - | Critical | 8.4 | 7.3 |
| %%cve:2026-40366%% | No | No | - | - | Critical | 8.4 | 7.3 |
| %%cve:2026-40361%% | No | No | - | - | Critical | 8.4 | 7.3 |
| %%cve:2026-40367%% | No | No | - | - | Critical | 8.4 | 7.3 |
| Microsoft Word for Android Spoofing Vulnerability | |||||||
| %%cve:2026-41101%% | No | No | - | - | Important | 7.1 | 6.2 |
| SQL Server Remote Code Execution Vulnerability | |||||||
| %%cve:2026-40370%% | No | No | - | - | Important | 8.8 | 7.7 |
| Secure Boot Security Feature Bypass Vulnerability | |||||||
| %%cve:2026-41097%% | No | No | - | - | Important | 6.7 | 5.8 |
| Visual Studio Code Elevation of Privilege Vulnerability | |||||||
| %%cve:2026-41613%% | No | No | - | - | Important | 8.8 | 7.7 |
| Visual Studio Code Information Disclosure Vulnerability | |||||||
| %%cve:2026-41612%% | No | No | - | - | Important | 5.5 | 4.8 |
| Visual Studio Code Remote Code Execution Vulnerability | |||||||
| %%cve:2026-41611%% | No | No | - | - | Important | 7.8 | 6.8 |
| Visual Studio Code Security Feature Bypass Vulnerability | |||||||
| %%cve:2026-41610%% | No | No | - | - | Important | 6.3 | 5.5 |
| Win32k Elevation of Privilege Vulnerability | |||||||
| %%cve:2026-33839%% | No | No | - | - | Important | 7.0 | 6.1 |
| %%cve:2026-33840%% | No | No | - | - | Important | 7.8 | 6.8 |
| %%cve:2026-34330%% | No | No | - | - | Important | 7.8 | 6.8 |
| %%cve:2026-34331%% | No | No | - | - | Important | 7.0 | 6.1 |
| Windows 11 Telnet Client Information Disclosure Vulnerability | |||||||
| %%cve:2026-35423%% | No | No | - | - | Important | 5.4 | 4.7 |
| Windows Admin Center Elevation of Privilege Vulnerability | |||||||
| %%cve:2026-35438%% | No | No | - | - | Important | 8.3 | 7.2 |
| Windows Admin Center in Azure Portal Elevation of Privilege Vulnerability | |||||||
| %%cve:2026-41086%% | No | No | - | - | Important | 8.8 | 7.7 |
| Windows Ancillary Function Driver for WinSock Elevation of Privilege Vulnerability | |||||||
| %%cve:2026-34344%% | No | No | - | - | Important | 7.8 | 6.8 |
| %%cve:2026-34345%% | No | No | - | - | Important | 7.0 | 6.1 |
| %%cve:2026-35416%% | No | No | - | - | Important | 7.0 | 6.1 |
| %%cve:2026-41088%% | No | No | - | - | Important | 7.8 | 6.8 |
| Windows Application Identity (AppID) Subsystem Elevation of Privilege Vulnerability | |||||||
| %%cve:2026-34343%% | No | No | - | - | Important | 7.8 | 6.8 |
| Windows Cloud Files Mini Filter Driver Elevation of Privilege Vulnerability | |||||||
| %%cve:2026-35418%% | No | No | - | - | Important | 7.8 | 6.8 |
| %%cve:2026-33835%% | No | No | - | - | Important | 7.8 | 6.8 |
| %%cve:2026-34337%% | No | No | - | - | Important | 7.8 | 6.8 |
| Windows Common Log File System Driver Elevation of Privilege Vulnerability | |||||||
| %%cve:2026-40407%% | No | No | - | - | Important | 7.8 | 6.8 |
| %%cve:2026-40397%% | No | No | - | - | Important | 7.8 | 6.8 |
| Windows DNS Client Remote Code Execution Vulnerability | |||||||
| %%cve:2026-41096%% | No | No | - | - | Critical | 9.8 | 8.5 |
| Windows DWM Core Library Elevation of Privilege Vulnerability | |||||||
| %%cve:2026-42896%% | No | No | - | - | Important | 7.8 | 6.8 |
| Windows DWM Core Library Information Disclosure Vulnerability | |||||||
| %%cve:2026-35419%% | No | No | - | - | Important | 5.5 | 4.8 |
| %%cve:2026-34336%% | No | No | - | - | Important | 7.8 | 6.8 |
| Windows Event Logging Service Elevation of Privilege Vulnerability | |||||||
| %%cve:2026-33834%% | No | No | - | - | Important | 7.8 | 6.8 |
| Windows Filtering Platform (WFP) Security Feature Bypass Vulnerability | |||||||
| %%cve:2026-32209%% | No | No | - | - | Important | 4.4 | 3.9 |
| Windows GDI Remote Code Execution Vulnerability | |||||||
| %%cve:2026-35421%% | No | No | - | - | Critical | 7.8 | 6.8 |
| Windows Graphics Component Remote Code Execution Vulnerability | |||||||
| %%cve:2026-40403%% | No | No | - | - | Critical | 8.8 | 7.7 |
| Windows Hyper-V Elevation of Privilege Vulnerability | |||||||
| %%cve:2026-40402%% | No | No | - | - | Critical | 9.3 | 8.1 |
| Windows Kernel Elevation of Privilege Vulnerability | |||||||
| %%cve:2026-33841%% | No | No | - | - | Important | 7.8 | 6.8 |
| %%cve:2026-35420%% | No | No | - | - | Important | 7.8 | 6.8 |
| %%cve:2026-40369%% | No | No | - | - | Important | 7.8 | 6.8 |
| Windows Kernel-Mode Driver Remote Code Execution Vulnerability | |||||||
| %%cve:2026-34332%% | No | No | - | - | Important | 8.0 | 7.0 |
| Windows Lightweight Directory Access Protocol (LDAP) Denial of Service Vulnerability | |||||||
| %%cve:2026-34339%% | No | No | - | - | Important | 5.5 | 4.8 |
| Windows Link-Layer Discovery Protocol (LLDP) Elevation of Privilege Vulnerability | |||||||
| %%cve:2026-34341%% | No | No | - | - | Important | 7.0 | 6.1 |
| Windows Message Queuing (MSMQ) Elevation of Privilege Vulnerability | |||||||
| %%cve:2026-33838%% | No | No | - | - | Important | 7.8 | 6.8 |
| Windows Native WiFi Miniport Driver Remote Code Execution Vulnerability | |||||||
| %%cve:2026-32161%% | No | No | - | - | Critical | 7.5 | 6.5 |
| Windows Netlogon Remote Code Execution Vulnerability | |||||||
| %%cve:2026-41089%% | No | No | - | - | Critical | 9.8 | 8.5 |
| Windows Print Spooler Elevation of Privilege Vulnerability | |||||||
| %%cve:2026-34342%% | No | No | - | - | Important | 7.0 | 6.1 |
| Windows Projected File System Elevation of Privilege Vulnerability | |||||||
| %%cve:2026-34340%% | No | No | - | - | Important | 7.0 | 6.1 |
| Windows Remote Desktop Services Elevation of Privilege Vulnerability | |||||||
| %%cve:2026-40398%% | No | No | - | - | Important | 7.8 | 6.8 |
| Windows Rich Text Edit Elevation of Privilege Vulnerability | |||||||
| %%cve:2026-21530%% | No | No | - | - | Important | 6.7 | 5.8 |
| %%cve:2026-32170%% | No | No | - | - | Important | 6.7 | 5.8 |
| Windows SMB Client Elevation of Privilege Vulnerability | |||||||
| %%cve:2026-40410%% | No | No | - | - | Important | 7.0 | 6.1 |
| Windows Storage Spaces Controller Elevation of Privilege Vulnerability | |||||||
| %%cve:2026-35415%% | No | No | - | - | Important | 7.8 | 6.8 |
| Windows Storport Miniport Driver Denial of Service Vulnerability | |||||||
| %%cve:2026-34350%% | No | No | - | - | Important | 6.5 | 5.7 |
| Windows TCP/IP Denial of Service Vulnerability | |||||||
| %%cve:2026-40405%% | No | No | - | - | Important | 7.5 | 6.5 |
| %%cve:2026-40414%% | No | No | - | - | Important | 7.4 | 6.4 |
| %%cve:2026-40401%% | No | No | - | - | Important | 7.1 | 6.2 |
| %%cve:2026-40413%% | No | No | - | - | Important | 7.4 | 6.4 |
| Windows TCP/IP Driver Security Feature Bypass Vulnerability | |||||||
| %%cve:2026-35422%% | No | No | - | - | Important | 6.5 | 5.7 |
| Windows TCP/IP Elevation of Privilege Vulnerability | |||||||
| %%cve:2026-34351%% | No | No | - | - | Important | 7.8 | 6.8 |
| %%cve:2026-40399%% | No | No | - | - | Important | 7.8 | 6.8 |
| %%cve:2026-34334%% | No | No | - | - | Important | 7.8 | 6.8 |
| Windows TCP/IP Information Disclosure Vulnerability | |||||||
| %%cve:2026-40406%% | No | No | - | - | Important | 7.5 | 6.5 |
| Windows TCP/IP Local Elevation of Privilege Vulnerability | |||||||
| %%cve:2026-33837%% | No | No | - | - | Important | 7.8 | 6.8 |
| Windows TCP/IP Remote Code Execution Vulnerability | |||||||
| %%cve:2026-40415%% | No | No | - | - | Important | 8.1 | 7.1 |
| Windows Telephony Service Elevation of Privilege Vulnerability | |||||||
| %%cve:2026-42825%% | No | No | - | - | Important | 7.0 | 6.1 |
| %%cve:2026-34338%% | No | No | - | - | Important | 7.8 | 6.8 |
| %%cve:2026-40382%% | No | No | - | - | Important | 7.8 | 6.8 |
| Windows Volume Manager Extension Driver Remote Code Execution Vulnerability | |||||||
| %%cve:2026-40380%% | No | No | - | - | Important | 6.2 | 5.4 |
| Windows WAN ARP Driver Elevation of Privilege Vulnerability | |||||||
| %%cve:2026-40408%% | No | No | - | - | Important | 7.8 | 6.8 |
| Windows Win32k Elevation of Privilege Vulnerability | |||||||
| %%cve:2026-34333%% | No | No | - | - | Important | 7.8 | 6.8 |
| %%cve:2026-34347%% | No | No | - | - | Important | 7.0 | 6.1 |
| %%cve:2026-35417%% | No | No | - | - | Important | 7.8 | 6.8 |
--
Johannes B. Ullrich, Ph.D. , Dean of Research, SANS.edu
Twitter|
Disgruntled researcher who dropped BlueHammer and RedSun drops two new Windows 11 zero-days: A Bitlocker bypass, nicknamed YellowKey, and LPE, nicknamed GreenPlasma
Speaks for itself, take a look:
https://github.com/Nightmare-Eclipse/YellowKey
https://github.com/Nightmare-Eclipse/GreenPlasma
What other explanation is there for YellowKey other than a backdoor?
Oh also they say that next Tuesday there will be another big surprise. Keep your eyes peeled I guess.
[link] [comments]