Visualização de leitura
The Cyber Express Weekly Roundup: EU AI Act Updates, Malware Expansion, Critical Vulnerabilities, and Rising Cybercrime Trends

The Cyber Express Weekly Roundup
EU Updates AI Act with Simpler Rules and New AI Content Bans
In a significant regulatory update, the European Union has agreed to revise parts of the EU AI Act. The updated framework aims to simplify compliance requirements for businesses while simultaneously introducing stricter restrictions on harmful AI-generated content. Read more..ClickFix Malware Campaign Expands to macOS
Another key development is the expansion of the ClickFix malware campaign beyond Windows systems. Security researchers at Microsoft have confirmed that the operation is now targeting macOS users using deceptive troubleshooting content. Read more...Critical PAN-OS Vulnerability Enables Remote Code Execution
A critical security flaw has been identified in Palo Alto Networks’ PAN-OS firewall software. Tracked as CVE-2026-0300, the vulnerability carries a CVSS score of 9.3, indicating severe risk. The issue originates from a buffer overflow vulnerability in the User-ID Authentication Portal. Read more...Latvian Cybercriminal Sentenced in Global Ransomware Case
Latvian national Deniss Zolotarjovs has been sentenced to 102 months in prison for his role in a large-scale ransomware operation. According to the U.S. Department of Justice, the group operated under multiple ransomware brands, including Conti, Royal, Akira, and Karakurt. Between 2021 and 2023, the organization carried out attacks against more than 54 companies worldwide, using data theft and encryption-based extortion tactics to pressure victims into paying ransom demands. Read more...FBI Warns of Rising Cyber-Enabled Cargo Theft
The FBI has issued an alert regarding a sharp rise in cyber-enabled cargo theft. Criminal actors are using impersonation techniques to pose as legitimate logistics providers, allowing them to intercept and redirect freight shipments. The agency noted that logistics, shipping, and insurance companies have been targeted since at least 2024. Read more...Weekly Takeaway
This week’s The Cyber Express weekly roundup highlights the growing convergence of regulatory change, advanced malware threats, critical infrastructure vulnerabilities, ransomware enforcement actions, and supply chain fraud. As the global cybersecurity landscape continues to evolve, organizations across all sectors remain under increasing pressure to strengthen defenses and adapt to emerging risks.Dirty Frag Linux Vulnerability Exposes Major Distributions to Root Access Attacks
Dirty Frag Targets Multiple Linux Distributions
The new LPE vulnerability affects a broad range of Linux distributions, including Ubuntu 24.04.4, RHEL 10.1, openSUSE Tumbleweed, CentOS Stream 10, AlmaLinux 10, and Fedora 44. Researchers warned that successful exploitation allows an unprivileged local user to escalate privileges and gain full root access. In a public disclosure sent to the oss-security mailing list on May 8, 2026, Kim described Dirty Frag as a “universal Linux LPE” capable of compromising all major Linux distributions. The disclosure stated: “This is a report on ‘Dirty Frag’, a universal LPE that allows obtaining root privileges on all major distributions.” Kim also emphasized that the impact closely resembles Copy Fail, or CVE-2026-31431, which has already been observed under active exploitation in the wild.How Dirty Frag Works
The first component of Dirty Frag, the xfrm-ESP Page-Cache Write vulnerability, originates from the IPSec (xfrm) subsystem. Researchers said it provides attackers with a four-byte store primitive similar to CVE-2026-31431 and allows overwriting small portions of the kernel page cache. However, exploitation through the xfrm-ESP path requires an unprivileged user to create a namespace. Ubuntu blocks this behavior through AppArmor restrictions, limiting the effectiveness of that exploit path on Ubuntu-based Linux distributions. To bypass that limitation, Dirty Frag chains a second flaw: the RxRPC Page-Cache Write vulnerability. Kim explained: “RxRPC Page-Cache Write does not require the privilege to create a namespace, but the rxrpc.ko module itself is not included in most distributions.” He added that while RHEL 10.1 does not ship the rxrpc.ko module by default, Ubuntu systems load it automatically. By combining both vulnerabilities, attackers can adapt exploitation techniques depending on the target environment. “Chaining the two variants makes the blind spots cover each other. In an environment where user namespace creation is allowed, the ESP exploit runs first. Conversely, on Ubuntu, where user namespace creation is blocked but rxrpc.ko is built, the RxRPC exploit works.”Links to Older Linux Kernel Vulnerabilities
Researchers traced the xfrm-ESP vulnerability back to a Linux kernel source code commit made in January 2017. Interestingly, the same commit was also identified as the root cause of another serious Linux kernel issue, CVE-2022-27666, a buffer overflow vulnerability with a CVSS score of 7.8 that affected multiple Linux distributions. The RxRPC Page-Cache Write vulnerability, meanwhile, was reportedly introduced in June 2023. Security firm CloudLinx stated in an advisory that the flaw exists in the “ESP-in-UDP MSG_SPLICE_PAGES no-COW fast path” and is reachable through the XFRM user netlink interface. AlmaLinux also released a technical analysis explaining how the issue impacts kernel memory handling: “The bug lives in the in-place decryption fast paths of esp4, esp6, and rxrpc: when a socket buffer carries paged fragments that are not privately owned by the kernel, the receive path decrypts directly over those externally-backed pages.” According to the advisory, this behavior can expose or corrupt plaintext data while an unprivileged process still maintains a reference to the affected pages.Public PoC Increases Risk for Linux Distributions
The threat level surrounding Dirty Frag has intensified due to the public release of a fully working proof-of-concept exploit. Researchers warned that the exploit can grant root access using a single command, significantly lowering the barrier for attackers. Until official patches become available, administrators are urged to disable the affected modules manually. The recommended mitigation command is:sudo sh -c "printf 'install esp4 /bin/false\ninstall esp6 /bin/false\ninstall rxrpc /bin/false\n' > /etc/modprobe.d/dirtyfrag.conf; rmmod esp4 esp6 rxrpc 2>/dev/null; true"Security experts also warned that Dirty Frag importantly differs from CVE-2026-31431. Unlike Copy Fail, Dirty Frag can still be exploited even if the Linux kernel’s algif_aead module has been disabled. Kim stated: “Note that Dirty Frag can be triggered regardless of whether the algif_aead module is available.” He further cautioned: “In other words, even on systems where the publicly known Copy Fail mitigation (algif_aead blacklist) is applied, your Linux is still vulnerable to Dirty Frag.” With no patches currently available and exploit code already circulating publicly, the newly disclosed Dirty Frag LPE vulnerability presents a significant risk to Linux distributions worldwide.
CVE-2025-68670: discovering an RCE vulnerability in xrdp

In addition to KasperskyOS-powered solutions, Kaspersky offers various utility software to streamline business operations. For instance, users of Kaspersky Thin Client, an operating system for thin clients, can also purchase Kaspersky USB Redirector, a module that expands the capabilities of the xrdp remote desktop server for Linux. This module enables access to local USB devices, such as flash drives, tokens, smart cards, and printers, within a remote desktop session – all while maintaining connection security.
We take the security of our products seriously and regularly conduct security assessments. Kaspersky USB Redirector is no exception. Last year, during a security audit of this tool, we discovered a remote code execution vulnerability in the xrdp server, which was assigned the identifier CVE-2025-68670. We reported our findings to the project maintainers, who responded quickly: they fixed the vulnerability in version 0.10.5, backported the patch to versions 0.9.27 and 0.10.4.1, and issued a security bulletin. This post breaks down the details of CVE-2025-68670 and provides recommendations for staying protected.
Client data transmission via RDP
Establishing an RDP connection is a complex, multi-stage process where the client and server exchange various settings. In the context of the vulnerability we discovered, we are specifically interested in the Secure Settings Exchange, which occurs immediately before client authentication. At this stage, the client sends protected credentials to the server within a Client Info PDU (protocol data unit with client info): username, password, auto-reconnect cookies, and so on. These data points are bundled into a TS_INFO_PACKET structure and can be represented as Unicode strings up to 512 bytes long, the last of which must be a null terminator. In the xrdp code, this corresponds to the xrdp_client_info structure, which looks as follows:
{
[..SNIP..]
char username[INFO_CLIENT_MAX_CB_LEN];
char password[INFO_CLIENT_MAX_CB_LEN];
char domain[INFO_CLIENT_MAX_CB_LEN];
char program[INFO_CLIENT_MAX_CB_LEN];
char directory[INFO_CLIENT_MAX_CB_LEN];
[..SNIP..]
}The value of the INFO_CLIENT_MAX_CB_LEN constant corresponds to the maximum string length and is defined as follows:
#define INFO_CLIENT_MAX_CB_LEN 512
When transmitting Unicode data, the client uses the UTF-16 encoding. However, the server converts the data to UTF-8 before saving it.
if (ts_info_utf16_in( // [1]
s, len_domain, self->rdp_layer->client_info.domain, sizeof(self->rdp_layer->client_info.domain)) != 0) // [2]
{
[..SNIP..]
}The size of the buffer for unpacking the domain name in UTF-8 [2] is passed to the ts_info_utf16_in function [1], which implements buffer overflow protection [3].
static int ts_info_utf16_in(struct stream *s, int src_bytes, char *dst, int dst_len)
{
int rv = 0;
LOG_DEVEL(LOG_LEVEL_TRACE, "ts_info_utf16_in: uni_len %d, dst_len %d", src_bytes, dst_len);
if (!s_check_rem_and_log(s, src_bytes + 2, "ts_info_utf16_in"))
{
rv = 1;
}
else
{
int term;
int num_chars = in_utf16_le_fixed_as_utf8(s, src_bytes / 2,
dst, dst_len);
if (num_chars > dst_len) // [3]
{
LOG(LOG_LEVEL_ERROR, "ts_info_utf16_in: output buffer overflow"); rv = 1;
}
/ / String should be null-terminated. We haven't read the terminator yet
in_uint16_le(s, term);
if (term != 0)
{
LOG(LOG_LEVEL_ERROR, "ts_info_utf16_in: bad terminator. Expected 0, got %d", term);
rv = 1;
}
}
return rv;
}Next, the in_utf16_le_fixed_as_utf8_proc function, where the actual data conversion from UTF-16 to UTF-8 takes place, checks the number of bytes written [4] as well as whether the string is null-terminated [5].
{
unsigned int rv = 0;
char32_t c32;
char u8str[MAXLEN_UTF8_CHAR];
unsigned int u8len;
char *saved_s_end = s->end;
// Expansion of S_CHECK_REM(s, n*2) using passed-in file and line #ifdef USE_DEVEL_STREAMCHECK
parser_stream_overflow_check(s, n * 2, 0, file, line); #endif
// Temporarily set the stream end pointer to allow us to use
// s_check_rem() when reading in UTF-16 words
if (s->end - s->p > (int)(n * 2))
{
s->end = s->p + (int)(n * 2);
}
while (s_check_rem(s, 2))
{
c32 = get_c32_from_stream(s);
u8len = utf_char32_to_utf8(c32, u8str);
if (u8len + 1 <= vn) // [4]
{
/* Room for this character and a terminator. Add the character */
unsigned int i;
for (i = 0 ; i < u8len ; ++i)
{
v[i] = u8str[i];
}
v n -= u8len;
v += u8len;
}
else if (vn > 1)
{
/* We've skipped a character, but there's more than one byte
* remaining in the output buffer. Mark the output buffer as
* full so we don't get a smaller character being squeezed into
* the remaining space */
vn = 1;
}
r v += u8len;
}
// Restore stream to full length s->end = saved_s_end;
if (vn > 0)
{
*v = '\0'; // [5]
}
+ +rv;
return rv;
}Consequently, up to 512 bytes of input data in UTF-16 are converted into UTF-8 data, which can also reach a size of up to 512 bytes.
CVE-2025-68670: an RCE vulnerability in xrdp
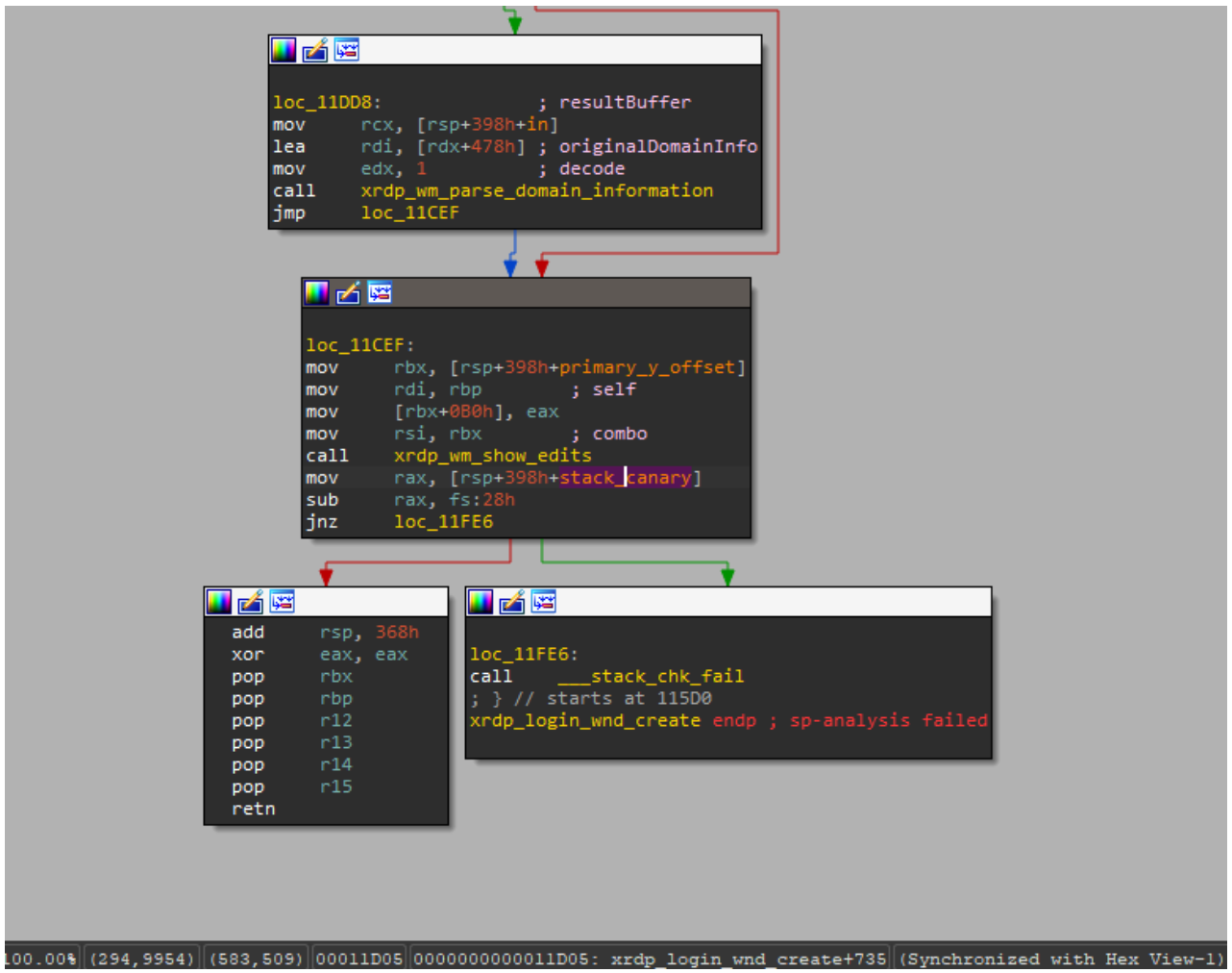
The vulnerability exists within the xrdp_wm_parse_domain_information function, which processes the domain name saved on the server in UTF-8. Like the functions described above, this one is called before client authentication, meaning exploitation does not require valid credentials. The call stack below illustrates this.
x rdp_wm_parse_domain_information(char *originalDomainInfo, int comboMax,
int decode, char *resultBuffer)
xrdp_login_wnd_create(struct xrdp_wm *self)
xrdp_wm_init(struct xrdp_wm *self)
xrdp_wm_login_state_changed(struct xrdp_wm *self)
xrdp_wm_check_wait_objs(struct xrdp_wm *self)
xrdp_process_main_loop(struct xrdp_process *self)The code snippet where the vulnerable function is called looks like this:
char resultIP[256]; // [7]
[..SNIP..]
combo->item_index = xrdp_wm_parse_domain_information(
self->session->client_info->domain, // [6]
combo->data_list->count, 1,
resultIP /* just a dummy place holder, we ignore
*/ );As you can see, the first argument of the function in line [6] is the domain name up to 512 bytes long. The final argument is the resultIP buffer of 256 bytes (as seen in line [7]). Now, let’s look at exactly what the vulnerable function does with these arguments.
static int
xrdp_wm_parse_domain_information(char *originalDomainInfo, int comboMax,
int decode, char *resultBuffer)
{
int ret;
int pos;
int comboxindex;
char index[2];
/* If the first char in the domain name is '_' we use the domain name as IP*/
ret = 0; /* default return value */
/* resultBuffer assumed to be 256 chars */
g_memset(resultBuffer, 0, 256);
if (originalDomainInfo[0] == '_') // [8]
{
/* we try to locate a number indicating what combobox index the user
* prefer the information is loaded from domain field, from the client
* We must use valid chars in the domain name.
* Underscore is a valid name in the domain.
* Invalid chars are ignored in microsoft client therefore we use '_'
* again. this sec '__' contains the split for index.*/
pos = g_pos(&originalDomainInfo[1], "__"); // [9]
if (pos > 0)
{
/* an index is found we try to use it */
LOG(LOG_LEVEL_DEBUG, "domain contains index char __");
if (decode)
{
[..SNIP..]
}
/ * pos limit the String to only contain the IP */
g_strncpy(resultBuffer, &originalDomainInfo[1], pos); // [10]
}
else
{
LOG(LOG_LEVEL_DEBUG, "domain does not contain _");
g_strncpy(resultBuffer, &originalDomainInfo[1], 255);
}
}
return ret;
}As seen in the code, if the first character of the domain name is an underscore (line [8]), a portion of the domain name – starting from the second character and ending with the double underscore (“__”) – is written into the resultIP buffer (line [9]). Since the domain name can be up to 512 bytes long, it may not fit into the buffer even if it’s technically well-formed (line [10]). Consequently, the overflow data will be written to the thread stack, potentially modifying the return address. If an attacker crafts a domain name that overflows the stack buffer and replaces the return address with a value they control, execution flow will shift according to the attacker’s intent upon returning from the vulnerable function, allowing for arbitrary code execution within the context of the compromised process (in this case, the xrdp server).
To exploit this vulnerability, the attacker simply needs to specify a domain name that, after being converted to UTF-8, contains more than 256 bytes between the initial “_” and the subsequent “__”. Given that the conversion follows specific rules easily found online, this is a straightforward task: one can simply take advantage of the fact that the length of the same string can vary between UTF-16 and UTF-8. In short, this involves avoiding ASCII and certain other characters that may take up more space in UTF-16 than in UTF-8, while also being careful not to abuse characters that expand significantly after conversion. If the resulting UTF-8 domain name exceeds the 512-byte limit, a conversion error will occur.
PoC
As a PoC for the discovered vulnerability, we created the following RDP file containing the RDP server’s IP address and a long domain name designed to trigger a buffer overflow. In the domain name, we used a specific number of K (U+041A) characters to overwrite the return address with the string “AAAAAAAA”. The contents of the RDP file are shown below:
alternate full address:s:172.22.118.7 full address:s:172.22.118.7 domain:s:_veryveryveryverKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKeryveryveryveryveryveryveryveryveryveryveryveryveryveryveryveryveryveryveryveaaaaaaaaryveryveryveryveryveryveryveryveryveryveryveryverylongdoAAAAAAAA__0 username:s:testuser
When you open this file, the mstsc.exe process connects to the specified server. The server processes the data in the file and attempts to write the domain name into the buffer, which results in a buffer overflow and the overwriting of the return address. If you look at the xrdp memory dump at the time of the crash, you can see that both the buffer and the return address have been overwritten. The application terminates during the stack canary check. The example below was captured using the gdb debugger.
gef➤ bt #0 __pthread_kill_implementation (no_tid=0x0, signo=0x6, threadid=0x7adb2dc71740) at ./nptl/pthread_kill.c:44 #1 __pthread_kill_internal (signo=0x6, threadid=0x7adb2dc71740) at ./nptl/pthread_kill.c:78 #2 __GI___pthread_kill (threadid=0x7adb2dc71740, signo=signo@entry=0x6) at./nptl/pthread_kill.c:89 #3 0x00007adb2da42476 in __GI_raise (sig=sig@entry=0x6) at ../sysdeps/posix/raise.c:26 #4 0x00007adb2da287f3 in __GI_abort () at ./stdlib/abort.c:79 #5 0x00007adb2da89677 in __libc_message (action=action@entry=do_abort, fmt=fmt@entry=0x7adb2dbdb92e "*** %s ***: terminated\n") at ../sysdeps/posix/libc_fatal.c:156 #6 0x00007adb2db3660a in __GI___fortify_fail (msg=msg@entry=0x7adb2dbdb916 "stack smashing detected") at ./debug/fortify_fail.c:26 #7 0x00007adb2db365d6 in __stack_chk_fail () at ./debug/stack_chk_fail.c:24 #8 0x000063654a2e5ad5 in ?? () #9 0x4141414141414141 in ?? () #10 0x00007adb00000a00 in ?? () #11 0x0000000000050004 in ?? () #12 0x00007fff91732220 in ?? () #13 0x000000000000030a in ?? () #14 0xfffffffffffffff8 in ?? () #15 0x000000052dc71740 in ?? () #16 0x3030305f70647278 in ?? () #17 0x616d5f6130333030 in ?? () #18 0x00636e79735f6e69 in ?? () #19 0x0000000000000000 in ?? ()
Protection against vulnerability exploitation
It is worth noting that the vulnerable function can be protected by a stack canary via compiler settings. In most compilers, this option is enabled by default, which prevents an attacker from simply overwriting the return address and executing a ROP chain. To successfully exploit the vulnerability, the attacker would first need to obtain the canary value.
The vulnerable function is also referenced by the xrdp_wm_show_edits function; however, even in that case, if the code is compiled with secure settings (using stack canaries), the most trivial exploitation scenario remains unfeasible.
Nevertheless, a stack canary is not a panacea. An attacker could potentially leak or guess its value, allowing them to overwrite the buffer and the return address while leaving the canary itself unchanged. In the security bulletin dedicated to CVE-2025-68670, the xrdp maintainers advise against relying solely on stack canaries when using the project.
Vulnerability remediation timeline
- 12/05/2025: we submitted the vulnerability report via https://github.com/neutrinolabs/xrdp/security.
- 12/05/2025: the project maintainers immediately confirmed receipt of the report and stated they would review it shortly.
- 12/15/2025: investigation and prioritization of the vulnerability began.
- 12/18/2025: the maintainers confirmed the vulnerability and began developing a patch.
- 12/24/2025: the vulnerability was assigned the identifier CVE-2025-68670.
- 01/27/2026: the patch was merged into the project’s main branch.
Conclusion
Taking a responsible approach to code makes not only our own products more solid but also enhances popular open-source projects. We have previously shared how security assessments of KasperskyOS-based solutions – such as Kaspersky Thin Client and Kaspersky IoT Secure Gateway – led to the discovery of several vulnerabilities in Suricata and FreeRDP, which project maintainers quickly patched. CVE-2025-68670 is yet another one of those stories.
However, discovering a vulnerability is only half the battle. We would like to thank the xrdp maintainers for their rapid response to our report, for fixing the vulnerability, and for issuing a security bulletin detailing the issue and risk mitigation options.




423 Firefox Flaws Fixed as Browser Gains Support for Claude, Mythos, and More
Mozilla has successfully identified and patched 423 latent security vulnerabilities in Firefox using advanced artificial intelligence models, notably Claude Mythos Preview. Two weeks after initially announcing their AI-assisted security initiative, Firefox developers have shared a behind-the-scenes look at how they engineered a highly effective threat-hunting pipeline. This milestone marks a significant shift in open-source security, […]
The post 423 Firefox Flaws Fixed as Browser Gains Support for Claude, Mythos, and More appeared first on GBHackers Security | #1 Globally Trusted Cyber Security News Platform.

Threat Brief: Exploitation of PAN-OS Captive Portal Zero-Day for Unauthenticated Remote Code Execution
Unit 42 details CVE-2026-0300, a buffer overflow vulnerability in the PAN-OS User-ID Authentication Portal. Read now for details.
The post Threat Brief: Exploitation of PAN-OS Captive Portal Zero-Day for Unauthenticated Remote Code Execution appeared first on Unit 42.

Salesforce Marketing Cloud Vulnerabilities Expose Cross-Tenant Subscriber Data Risks

AMPScript and SFMC Template Injection Risks
Modern enterprises rely heavily on Salesforce Marketing Cloud to manage large-scale marketing campaigns, personalized customer journeys, and trackable email communications. The platform, formerly known as ExactTarget, supports dynamic content generation through technologies such as AMPScript, Server-Side JavaScript (SSJS), and internal data views connected to large subscriber databases. While these features provide flexibility for marketers, researchers noted that they also increase the impact of any underlying vulnerability. One of the major concerns centered on SFMC’s server-side templating framework. AMPScript and SSJS allow organizations to dynamically insert subscriber attributes such as names, email addresses, and engagement metrics directly into marketing content. However, functions like TreatAsContent introduced a dangerous behavior because they effectively evaluate user-controlled input as executable template code. Researchers explained that if attacker-controlled data was passed into these functions, it could trigger template injection inside Salesforce Marketing Cloud environments. The issue became more severe because SFMC historically supported AMPScript execution within email subject lines. According to the findings, legacy behavior caused subject templates to be evaluated twice by default. That design opened the door for payload execution during the second rendering stage. Researchers demonstrated the risk using the following payload inside a name field: %%=RowCount(LookupRows("_Subscribers","SubscriberKey",_subscriberkey))=%% If processed during the second evaluation phase, the payload could execute successfully and create a reliable injection point inside the marketing workflow. Once template execution was achieved, attackers could potentially use built-in SFMC functions such as LookupRows to query internal Data Views, including:- _Subscribers
- _Sent
- _Job
- _SMSMessageTracking
- _Click
CloudPages and “View Email in Browser” Vulnerability
Researchers identified an even more serious vulnerability tied to SFMC’s “view email in browser” functionality and CloudPages infrastructure. Many Salesforce customers configure branded domains such as view.example.com or pages.example.com that route back to shared SFMC infrastructure. These links typically rely on an encrypted qs parameter containing tenant and message-specific information. According to researchers from Searchlight Cyber, the older “classic” qs implementation used unauthenticated CBC encryption. The researchers found that the implementation behaved as a padding oracle, which made it possible to decrypt and re-encrypt query string parameters under certain conditions. Initially, the researchers abused the weakness using the Padre tool before later improving the process through the AMPScript MicrositeURL function. This allowed them to forge valid QS values and access workflows such as “Forward to a Friend,” which could resolve subscriber identifiers into actual email addresses. One of the most concerning aspects of the vulnerability was SFMC’s use of a single static encryption key shared across tenants. Researchers stated that once the cryptographic structure became understood, attackers could theoretically enumerate subscribers and access email content across multiple organizations using the same mechanism.Legacy Encryption Weaknesses Expanded the Attack Surface
The researchers also uncovered an older URL format that relied on per-parameter “encryption.” However, the mechanism reportedly consisted of a repeating static XOR key combined with a checksum. Although the scheme was considered legacy functionality, researchers found that it still worked on modern SFMC tenants. Because the implementation lacked strong cryptographic protections, attackers could decrypt and enumerate parameters such as JobID and ListSubscriber at high speed without relying on the slower padding-oracle technique. The findings highlighted how legacy systems inside large cloud platforms can continue to create security exposure long after newer protections are introduced.Impact of the Salesforce Marketing Cloud Vulnerability
Researchers concluded that the combined vulnerabilities could have enabled attackers to:- Enumerate and exfiltrate subscriber records
- Access sent marketing emails and engagement data
- Forge cross-tenant QS tokens
- Access emails belonging to other organizations
- Exploit hard-coded cryptographic material
- Abuse argument-injection flaws tied to the MicrositeURL function
- Manipulate CloudPages and other SFMC web workflows
CISA Launches CI Fortify to Defend Critical Infrastructure From Nation-State Cyber Threats

CI Fortify Initiative Focuses on Isolation and Recovery
Under the CI Fortify initiative, CISA is urging critical infrastructure organizations to assume that third-party communications and service providers may become unreliable during a crisis. Operators are also being asked to plan under the assumption that threat actors may already have some level of access to OT networks. Nick Andersen, Acting Director at CISA, emphasized the need for organizations to prepare for worst-case operational scenarios. “In a geopolitical crisis, the critical infrastructure organizations Americans rely on must be able to continue delivering, at a minimum, crucial services,” Andersen said. “They must be able to isolate vital systems from harm, continue operating in that isolated state, and quickly recover any systems that an adversary may successfully compromise.” The isolation strategy outlined under CI Fortify involves proactively disconnecting operational technology systems from external business networks and third-party connections. CISA said this approach is intended to prevent cyber impacts from spreading into OT environments while allowing organizations to continue delivering essential services in a degraded communications environment. The agency advised operators to identify critical customers, including military infrastructure and other lifeline services, and determine the minimum operational capabilities needed to support them during emergencies. CISA also recommended updating engineering processes and business continuity plans to support safe operations for extended periods while systems remain isolated.Recovery Planning Central to Critical Infrastructure Resilience
Alongside isolation, the CI Fortify initiative places strong emphasis on recovery planning. CISA urged operators to maintain updated system documentation, create secure backups of critical files, and regularly practice system replacement or manual operational transitions. The agency noted that organizations should also identify communications dependencies that could complicate recovery efforts, such as licensing servers, remote vendor access, or upstream network connections. CISA encouraged operators to work closely with managed service providers, system integrators, and vendors to understand potential failure points and establish alternative recovery pathways. The initiative also highlights broader benefits of emergency planning beyond cybersecurity incidents. According to CISA, the same planning processes can help organizations maintain operations during weather-related disruptions, equipment failures, and safety emergencies. The agency said isolation planning can help cut off command-and-control access to compromised systems, while strong recovery preparation can reduce incident response costs and shorten recovery timelines.Security Vendors and Service Providers Asked to Support CI Fortify
The CI Fortify initiative extends beyond infrastructure operators and calls on cybersecurity vendors, industrial automation suppliers, and managed service providers to support resilience planning efforts. Industrial control system vendors are being encouraged to identify barriers that could interfere with isolation and recovery procedures, including licensing restrictions and server dependency issues. Managed service providers and integrators are expected to assist organizations in engineering updates, local backup collection, and recovery documentation planning. Meanwhile, security vendors are being asked to support threat monitoring and provide intelligence if nation-state actors shift from espionage-focused activity to destructive cyber operations. CISA also requested vendors share information related to tactics that could undermine recovery or bypass isolation protections, including malicious firmware updates and vulnerabilities affecting software-based data diodes.Volt Typhoon Cyberattacks Continue to Shape U.S. Cybersecurity Strategy
The launch of CI Fortify is closely tied to ongoing concerns surrounding the Volt Typhoon cyberattacks, which U.S. officials have linked to Chinese state-sponsored threat actors. CISA’s initiative specifically references the Volt Typhoon campaign as an example of how adversaries have attempted to establish long-term access inside U.S. critical infrastructure systems to potentially support disruptive actions during military conflicts. The Volt Typhoon operation first became public in 2023, when U.S. authorities revealed that Chinese hackers had infiltrated multiple sectors of American critical infrastructure. Former CISA Director Jen Easterly stated in 2024 that the agency had identified and removed Volt Typhoon intrusions across several sectors. She later reiterated in 2025 that efforts continued to focus on identifying and evicting Chinese cyber actors from critical infrastructure environments. Despite these operations, cybersecurity researchers and some government officials have warned that Chinese threat actors may still retain access to portions of critical infrastructure networks. Several experts have argued that nation-state groups remain deeply embedded in certain environments despite years of remediation efforts. With the CI Fortify initiative, CISA appears to be shifting focus toward operational resilience, recognizing that prevention alone may not be sufficient against sophisticated nation-state cyber threats targeting U.S. critical infrastructure.Spring Vulnerabilities Open Door to Arbitrary File Access and GCP Secret Leaks
Security researchers have identified four new vulnerabilities in the Spring Cloud Config Server, ranging from medium to critical severity. These newly disclosed flaws could allow attackers to access arbitrary files, leak Google Cloud Platform (GCP) secrets, and manipulate system directories. Administrators, please patch your systems immediately to prevent active exploitation. Spring Vulnerabilities Critical Directory Traversal […]
The post Spring Vulnerabilities Open Door to Arbitrary File Access and GCP Secret Leaks appeared first on GBHackers Security | #1 Globally Trusted Cyber Security News Platform.

Copy Fail: What You Need to Know About the Most Severe Linux Threat in Years
Copy Fail (CVE-2026-31431) is a critical Linux kernel LPE that allows stealthy root access. This flaw impacts millions of systems. Read our analysis.
The post Copy Fail: What You Need to Know About the Most Severe Linux Threat in Years appeared first on Unit 42.

PAN-OS Flaw CVE-2026-0300 Exposes Firewalls to Remote Code Execution

Technical Details of the Buffer Overflow Vulnerability in PAN-OS
The root cause of CVE-2026-0300 PAN-OS is classified under CWE-787: Out-of-bounds Write, a common but dangerous type of buffer overflow vulnerability. Attackers can exploit this flaw to overwrite memory and potentially take full control of affected systems. The vulnerability impacts PA-Series and VM-Series firewalls when the User-ID™ Authentication Portal is enabled. Importantly, Prisma Access, Cloud NGFW, and Panorama appliances are not affected. Security data associated with the vulnerability highlights the following:- Attack Vector: Network
- Attack Complexity: Low
- Privileges Required: None
- User Interaction: None
- Confidentiality, Integrity, Availability Impact: High
Active Exploitation and Risk Factors
Evidence shows limited exploitation of CVE-2026-0300 PAN-OS, particularly targeting systems where the User-ID Authentication Portal is exposed to untrusted networks or the public internet. Environments that allow external access to this portal face the highest level of risk. The severity is further highlighted by the CVSS vector: CVSS:4.0/AV:N/AC:L/AT:N/PR:N/UI:N/VC:H/VI:H/VA:H This translates to a scenario where attackers can remotely compromise systems without needing credentials or user involvement, leveraging the buffer overflow vulnerability to gain root-level access.Affected and Unaffected Versions
Multiple versions of PAN-OS are impacted by CVE-2026-0300, including:- PAN-OS 12.1 versions prior to 12.1.4-h5 and 12.1.7
- PAN-OS 11.2 versions prior to 11.2.4-h17, 11.2.7-h13, 11.2.10-h6, and 11.2.12
- PAN-OS 11.1 versions prior to 11.1.4-h33, 11.1.6-h32, 11.1.7-h6, 11.1.10-h25, 11.1.13-h5, and 11.1.15
- PAN-OS 10.2 versions prior to 10.2.7-h34, 10.2.10-h36, 10.2.13-h21, 10.2.16-h7, and 10.2.18-h6
Mitigation and Workarounds
While patches are being rolled out, organizations are advised to take immediate steps to reduce exposure to the buffer overflow vulnerability in PAN-OS. Recommended mitigations include:- Restricting access to the User-ID Authentication Portal to trusted internal IP addresses only
- Preventing any exposure of the portal to the public internet
- Disabling the User-ID Authentication Portal entirely if it is not required
New WhatsApp Flaws Could Affect Billions of Users After Meta Security Patch
Meta patched two WhatsApp flaws affecting iOS, Android, and Windows users, including bugs tied to risky files, links, and Reels previews.
The post New WhatsApp Flaws Could Affect Billions of Users After Meta Security Patch appeared first on TechRepublic.
WhatsApp Security Flaw Enables Malicious URL Execution Through Instagram Reels
WhatsApp has recently patched two notable security vulnerabilities that could have allowed attackers to execute malicious links and disguise dangerous files. The most alarming discovery involves a flaw in how WhatsApp processes Instagram Reels. This vulnerability allows remote threat actors to trigger arbitrary URLs on a victim’s device by exploiting unvalidated message elements. Meta’s latest […]
The post WhatsApp Security Flaw Enables Malicious URL Execution Through Instagram Reels appeared first on GBHackers Security | #1 Globally Trusted Cyber Security News Platform.

DarkSword Malware
DarkSword is a sophisticated piece of malware—probably government designed—that targets iOS.
Google Threat Intelligence Group (GTIG) has identified a new iOS full-chain exploit that leveraged multiple zero-day vulnerabilities to fully compromise devices. Based on toolmarks in recovered payloads, we believe the exploit chain to be called DarkSword. Since at least November 2025, GTIG has observed multiple commercial surveillance vendors and suspected state-sponsored actors utilizing DarkSword in distinct campaigns. These threat actors have deployed the exploit chain against targets in Saudi Arabia, Turkey, Malaysia, and Ukraine.
DarkSword supports iOS versions 18.4 through 18.7 and utilizes six different vulnerabilities to deploy final-stage payloads. GTIG has identified three distinct malware families deployed following a successful DarkSword compromise: GHOSTBLADE, GHOSTKNIFE, and GHOSTSABER. The proliferation of this single exploit chain across disparate threat actors mirrors the previously discovered Coruna iOS exploit kit. Notably, UNC6353, a suspected Russian espionage group previously observed using Coruna, has recently incorporated DarkSword into their watering hole campaigns.
A week after it was identified, a version of it leaked onto the internet, where it is being used more broadly.
This news is a month old. Your devices are safe, assuming you patch regularly.
Billions of Chrome Users Urged to Update After Google Patches 30 Security Flaws
Google patched 30 Chrome vulnerabilities, including four Critical flaws. Here’s what users should know and how to update Chrome and Firefox.
The post Billions of Chrome Users Urged to Update After Google Patches 30 Security Flaws appeared first on TechRepublic.
The Mythos AI Vulnerability Storm: What to Do Next
AI is transforming both software development and software risk.
The post The Mythos AI Vulnerability Storm: What to Do Next appeared first on Security Boulevard.
How AutoSecT Uses AI to Find Vulnerabilities That Actually Matter
We always think we are more vulnerable than our fellow contemporaries! In general sense, this shows lack of confidence, but when you are dealing with security, this is one of the best traits you can have! Sounds strange, right! Let’s be honest, most security teams aren’t short on vulnerability data. They’re drowning in it. Scan […]
The post How AutoSecT Uses AI to Find Vulnerabilities That Actually Matter appeared first on Kratikal Blogs.
The post How AutoSecT Uses AI to Find Vulnerabilities That Actually Matter appeared first on Security Boulevard.
Inside Vect Ransomware-as-a-Service
Vect ransomware, a new group that emerged in January 2026, has recently begun attracting attention in the cybersecurity space for its strategic partnerships, which are helping it expand. One notable collaboration is with TeamPCP, with evidence already surfacing as the latest victims on Vect's leak site appear to have been posted on behalf of TeamPCP.
Multiple Exim Mail Server Vulnerabilities Could Trigger Crashes via Malicious DNS Data
The developers of the Exim mail server have officially rolled out version 4.99.2 to address four newly discovered security vulnerabilities. This critical update patches multiple software flaws that could allow attackers to crash server connections, corrupt memory heaps, or potentially leak sensitive system data. Mail server administrators are strongly advised to apply these fixes immediately […]
The post Multiple Exim Mail Server Vulnerabilities Could Trigger Crashes via Malicious DNS Data appeared first on GBHackers Security | #1 Globally Trusted Cyber Security News Platform.

Multiple Wireshark Vulnerabilities Allow Arbitrary Code Execution via Malformed Packets
The Wireshark Foundation has released version 4.6.5 of its widely used network protocol analyzer, addressing a massive wave of security vulnerabilities. This urgent update patches over 40 distinct security flaws, driven by a recent surge in AI-assisted vulnerability reports. The most critical bugs in this release allow for possible arbitrary code execution, elevating the risk […]
The post Multiple Wireshark Vulnerabilities Allow Arbitrary Code Execution via Malformed Packets appeared first on GBHackers Security | #1 Globally Trusted Cyber Security News Platform.