The post Omani Government Targeted in Blatant Iranian-Nexus Cyberespionage appeared first on Daily CyberSecurity.
Visualização de leitura
Carding service Jerry’s Store leak exposes 345,000 stolen payment cards
Jerry’s Store, a card-checking service used by cybercriminals, exposed 345,000 stolen payment cards after leaving its server open, revealing sensitive data.
A cybercriminal operation known as Jerry’s Store has reportedly exposed a large cache of stolen payment card data after leaving its own infrastructure accessible online. The service appears to have been used to test whether stolen credit and debit card details were still valid, effectively acting as a verification tool for fraudsters before the data was resold or abused.
“Jerry’s Store marketplace leaked 345,000 stolen credit card details through an exposed, insecurely configured server created using AI assistance.” reads the report published by CyberNews.
“The leak occurred after Cursor AI generated flawed code without authentication, exposing credit card numbers, names, addresses, and security codes.”
Researchers found that the exposed server contained information linked to roughly 345,000 payment cards. Of those, nearly 200,000 cards had been marked as invalid by the service, while more than 145,000 records were identified as valid. The leaked records reportedly included highly sensitive cardholder data such as card numbers, expiration dates, security codes, names, and billing addresses. Cybernews
The incident is notable not only because of the volume of exposed data, but also because it shows how organized and automated parts of the carding economy have become. Instead of manually checking stolen cards one by one, criminal marketplaces and fraud services increasingly rely on infrastructure that can validate payment data at scale. Once a card is confirmed as active, it becomes more valuable for resale, fraud attempts, or account takeover activity.
Cybernews estimated that valid stolen card records typically sell for around $7 to $18 on dark web markets. Using that range, the valid card data exposed through Jerry’s Store could be worth between $1 million and $2.6 million. The true value of the broader operation may be higher, since the platform reportedly handled more than just the leaked payment-card records.
CyberNews researchers found that Jerry’s Store operators used Cursor, an AI coding tool by Anysphere, to build their server and admin dashboards. However, flawed guidance from the AI likely led to misconfigurations, leaving the system exposed and causing the data leak.
“We were able to confirm that the leak originated from the user asking to create a statistics dashboard, and Cursor created an unauthenticated open web directory to serve the webpage, ignoring the need to set up authentication or ensure that only the intended dashboard would be accessible,” CyberNews team explained.


The case is ironic: a cybercriminal service built to profit from stolen card data exposed itself due to poor security. This failure creates added risk for victims, as data already circulating in underground markets can spread further, reaching new attackers who did not originally steal it.
The story also highlights a wider trend in cybercrime: illicit services are becoming more productized. Carding shops, validation tools, automated fraud services, and dark web marketplaces increasingly resemble commercial platforms, with pricing models, customer interfaces, and backend infrastructure. Rapid7 has described this broader ecosystem as “carding-as-a-service,” where stolen cards and fraud tooling are packaged for easier use by criminals with varying levels of technical skill.
A similar pattern has been seen in other carding-related incidents. BidenCash, a carding-focused marketplace, became known for releasing large batches of stolen payment-card data as a promotional tactic to attract users and vendors.
Law enforcement has also targeted related ecosystems. In a case involving B1ack’s Stash, authorities seized domains tied to underground vendors trafficking stolen financial data, including payment-card records. That case underlines how carding markets remain a priority for investigators because they support a chain of downstream crimes, from unauthorized purchases to identity theft and money laundering.
Consumers should closely monitor accounts, enable alerts, use virtual cards, and replace compromised ones. Banks must strengthen fraud detection, quickly block stolen cards, and monitor underground markets.
The Jerry’s Store leak shows that even cybercriminal platforms can have weak security. When they fail, the impact still hits ordinary users, whose stolen card data may spread further and be reused, traded, and exploited across the fraud ecosystem.
Follow me on Twitter: @securityaffairs and Facebook and Mastodon
(SecurityAffairs – hacking, Jerry’s Store)
Vimeo Data Exposed in Anodot Supply Chain Attack
The post Vimeo Data Exposed in Anodot Supply Chain Attack appeared first on Daily CyberSecurity.
French Police Arrest HexDex Hacker Over Mass Data Theft and Leaks
RAMP Uncovered: Anatomy of Russia’s Ransomware Marketplace
Leaked data from RAMP reveals Russia’s ransomware ecosystem, analyzing 1,732 threads, 7,707 users, and 340,000 IP records from the forum.
RAMP was not just another dark web forum. It was one of the clearest examples of how ransomware has become an organized marketplace, with sellers, buyers, brokers, and recruiters all playing different roles in the same criminal ecosystem.
A leaked database from RAMP gives us a rare look behind the curtain. It shows how cybercrime works when it becomes structured, commercial, and repeatable. Instead of random hackers acting alone, RAMP functioned like a business platform where criminals could sell access, recruit affiliates, advertise ransomware, and negotiate deals in private.
What the leak exposed
The leaked data covers activity from November 2021 to January 2024 and includes user records, forum threads, private messages, IP logs, and admin activity. That matters because it shows both the public side of the forum and the hidden conversations that helped turn forum posts into real attacks.
“Comparitech gained exclusive access to a leaked database from RAMP. The full MySQL dump contains user records, forum threads, private messages, IP logs, and admin activity spanning November 2021 through January 2024.” reads the analysis published by Comparitech.
The scale is significant. Comparitech’s analysis found 7,707 registered users, 1,732 forum threads, 340,333 IP log records, 1,899 private conversations, and 3,875 private messages. In other words, this was not a small corner of the internet. It was a large criminal marketplace with a lot of movement and a lot of participants.
RAMP in numbers
| Metric | Figure |
|---|---|
| Registered users | 7,707 |
| Forum threads | 1,732 |
| IP log records | 340,333 |
| Private conversations | 1,899 |
| Private messages | 3,875 |
| RaaS programs advertised | 14 |
| Leak sites referenced | 250+ |
These numbers show a mature underground community, not a loose collection of opportunists.
Why RAMP mattered
RAMP became popular because it supported the full ransomware chain. That means it was not only a place to talk about attacks. It was a place to buy access, find partners, exchange tools, and recruit affiliates.
The forum’s access market was especially important. The database shows 333 threads offering access to compromised corporate networks. That is a big deal, because initial access is often the hardest part of a ransomware operation. Once criminals get inside a network, the rest of the attack becomes much easier.
The forum also hosted 60 threads in its ransomware-as-a-service section. That section revealed a growing trend toward generous profit splits, with affiliates getting up to 90% of ransom payments in some cases. That kind of arrangement helps explain why ransomware keeps attracting new actors. It is a criminal business model designed to scale.
What was being sold
| Category | What it tells us |
|---|---|
| Access listings | Criminals were selling entry into real corporate networks |
| RaaS recruitment | Operators were hiring affiliates to spread attacks |
| Private messages | Deals were negotiated behind the scenes |
| IP logs | Activity was tracked and monitored at scale |
This mix of public listings and private negotiations shows how ransomware markets move from advertisement to execution.
Targets and sectors
The leak also shows what kinds of organizations were being targeted. RAMP listings included defense contractors, banks, hospitals, energy companies, technology firms, and government agencies across more than 20 countries.
The United States was the top target. It appeared in 40% of listings where a country could be identified. Government agencies were the most targeted sector, with 21 listings, followed by finance and banking, and technology and telecom, each with 11 listings.
That pattern is important. It shows that ransomware actors are not just chasing easy victims. They are targeting organizations that are likely to be pressured into paying because they cannot afford downtime, data loss, or public exposure.
The hidden layer
The most revealing part of the leak may be the private conversations. The database included 1,899 conversations and 3,875 messages. These messages covered topics like VPN access, stealer logs, and private RaaS partnership requests.
That hidden layer matters because public forum posts do not tell the whole story. A public listing can advertise access, but a private conversation is where the real business happens. This is where criminals confirm details, negotiate price, and decide whether a listing is worth moving forward.
The leaked data also suggests that a single access broker posted 41 separate listings. That suggests some actors were operating like wholesalers, moving multiple entry points into corporate networks rather than focusing on just one victim.
Why this matters today
RAMP helps explain why ransomware remains such a serious threat. The forum made it easier for criminals to specialize. One person could steal access, another could sell malware, and another could launch the final attack. That division of labor makes ransomware faster, cheaper, and harder to stop.
It also shows why law enforcement pressure does not automatically end the problem. Even when a major forum is disrupted, the ecosystem can fragment and move elsewhere. Criminal markets often adapt rather than disappear.
In practice, this means defenders need to think beyond malware alone. They need to monitor stolen credentials, exposed remote access, suspicious logins, and signs of initial access being sold or traded. The earliest stage of the attack chain is often the most important one to catch.
What organizations should learn
The RAMP leak reinforces a simple lesson: ransomware is an ecosystem, not just a piece of malware. If attackers can buy access, recruit help, and sell stolen access in one place, then defenders need to protect every stage of the environment, from identity to endpoint to remote access.
Organizations should focus on a few practical controls:
- reduce exposed services and external access paths,
- enforce MFA everywhere possible,
- detect unusual login behavior,
- monitor dark web exposure for corporate credentials,
- and improve incident response before an attack happens.
The leaked database is valuable because it shows the real machinery behind ransomware. It is not just about encryption at the end of an attack. It is about the marketplace that makes the attack possible in the first place.
“This analysis is based on a MySQL database dump of the RAMP forum’s XenForo installation. We parsed raw SQL to extract structured data from the xf_user (7,707 records), xf_thread (1,732 records), xf_post, xf_ip (340,333 records), xf_admin_log, xf_conversation_master (1,899 records), and xf_conversation_message (3,875 records) tables.” concludes the analysis. “IP addresses were decoded from binary format and geolocated against known ISP allocations. All findings are based on data as it existed in the database dump and have not been independently verified against live sources.”
Follow me on Twitter: @securityaffairs and Facebook and Mastodon
(SecurityAffairs – hacking, data leak)
Threat Landscape March 2026: Ransomware Dominance, Access Brokers, Data Leaks, and Critical Exploitation Trends

Cyble Research & Intelligence Labs (CRIL) in its monthly threat landscape analysis observed a highly active threat environment throughout March 2026, shaped by large-scale ransomware campaigns, persistent data breach activity, growing initial access brokerage markets, and exploitation of critical vulnerabilities affecting widely deployed enterprise systems.
Threat actors continued to prioritize financial extortion, credential access, and operational disruption, while increasingly targeting sectors rich in sensitive data or dependent on business continuity.
Quick Summary
Key threat trends identified during March 2026 include:
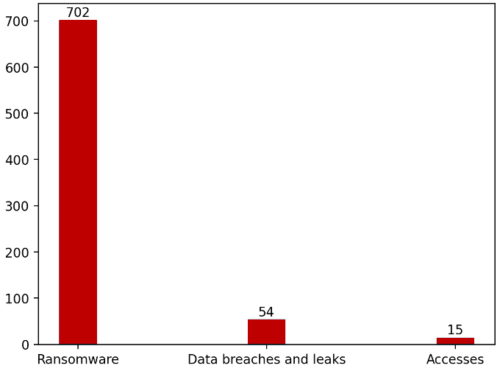
- 702 ransomware attacks recorded globally.
- 54 major data breach and leak incidents observed.
- 20 compromised access sale listings tracked across cybercrime forums.
- High concentration of attacks against Professional Services, Manufacturing, Retail, and Government sectors.
- Continued exploitation of vulnerabilities listed in CISA’s Known Exploited Vulnerabilities (KEV) catalog.
These trends indicate a mature cybercriminal ecosystem where access brokers, ransomware operators, and data leak actors increasingly operate in parallel.
Ransomware Activity Remained the Dominant Threat
CRIL recorded 702 ransomware attacks worldwide in March 2026, reflecting sustained aggression from both established groups and emerging operators.
Top Ransomware Groups
Qilin, Akira, The Gentlemen, Dragonforce, and INC Ransom were the top five most active ransomware actors in March 2026.
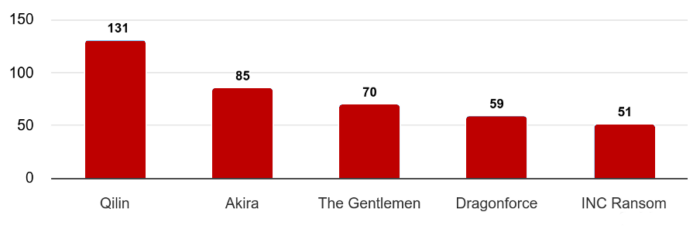
Together, the top five groups accounted for more than 56% of observed ransomware activity, highlighting strong operational scale and affiliate ecosystems.
Most Targeted Industries
Construction, Professional Services, Manufacturing, Healthcare, and Energy & Utilities were the most targeted sectors by ransomware actors in March 2026.
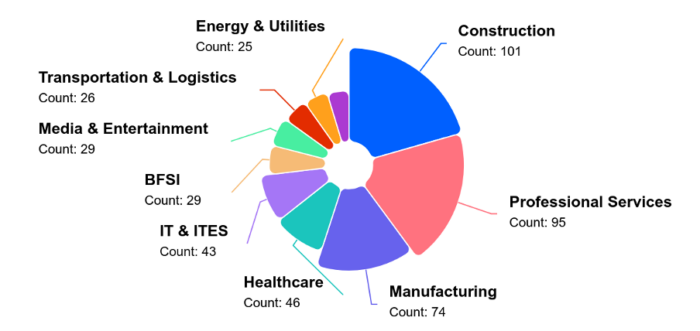
Threat actors continued using data theft + operational disruption as dual-extortion pressure tactics.
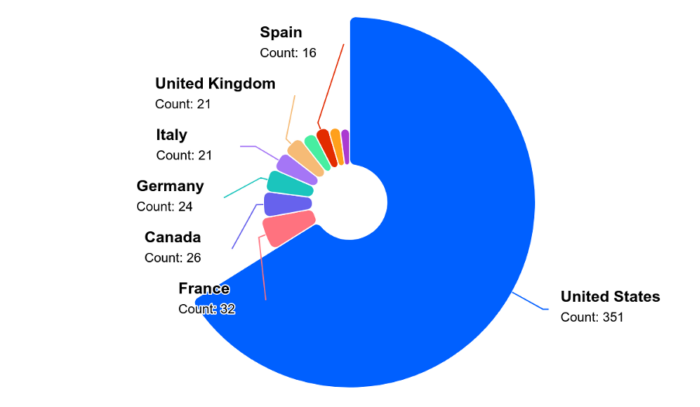
And when it came to country-wise split-up, the United States remained the focal point amid the ongoing geopolitical issues with Iran.
Compromised Access Market Expanded
CRIL tracked 20 distinct incidents involving the sale of unauthorized network access on underground forums.
Most Targeted Sectors
- Professional Services – 25%
- Retail – 20%
- IT & ITES
- Manufacturing
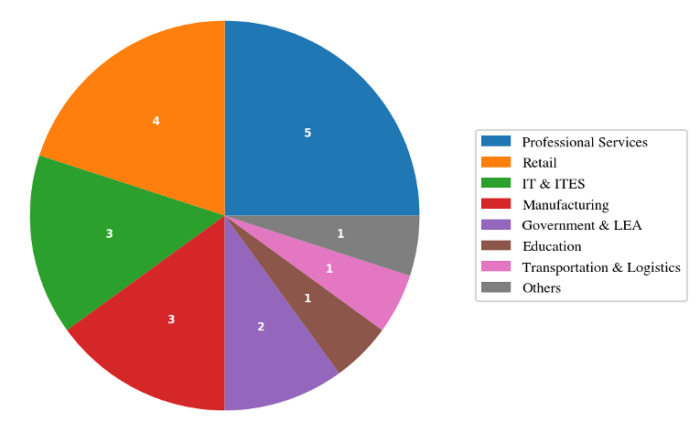
Leading Access Sellers
A small group of actors dominated this market:
- vexin
- holyduxy
- algoyim
These three actors were responsible for over 55% of observed access listings.
This reinforces the role of access brokers as upstream enablers for ransomware, espionage, and fraud operations.
Data Breaches and Leak Markets Remained Active
CRIL observed 54 significant breach and leak incidents during the month.
Most Targeted Sectors
- Government & Law Enforcement
- Retail
- Technology
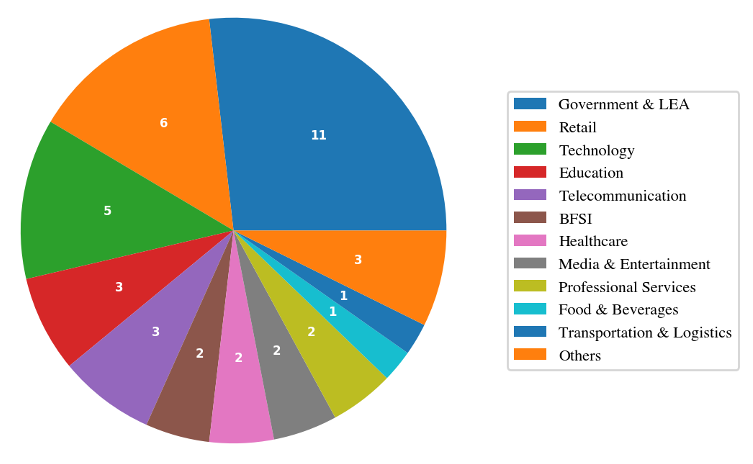
Notable Incidents
Hospitality Holdings – TA Claimed 5TB Leak
Threat actor “nightly” claimed theft of over 5TB of data, including biometric records, CCTV footage, and financial documents.
South African Government Dataset for Sale
Threat actor XP95 advertised 3.8TB of allegedly stolen provincial government data.
Travel Data Leak
Over 95,000 travel-related records were reportedly exposed, including passports and payment data.
Exploited Vulnerabilities Accelerated Risk
March also saw active exploitation of critical vulnerabilities affecting enterprise technologies.
Notable KEV-listed vulnerabilities included:
- CVE-2026-20131 – Cisco Secure Firewall Management Center
- CVE-2025-53521 – F5 BIG-IP APM
- CVE-2026-20963 – Microsoft SharePoint Server
- CVE-2026-33017 – Langflow AI
- CVE-2021-22681 – Rockwell Automation ICS
Key Trend
Attackers exploited both:
- Newly disclosed zero-days
- Legacy vulnerabilities from prior years
This showcases widespread failures in patch management and exposure reduction.
Emerging Strategic Threat Developments
AI-Augmented Offensive Operations
Threat actors reportedly used CyberStrikeAI, an open-source AI-native security testing framework, in attacks against Fortinet FortiGate devices across 55 countries, compromising more than 600 appliances.
Supply Chain Malware via npm
North Korean actors were linked to 26 malicious npm packages distributing RAT malware through Pastebin/Vercel-based infrastructure.
Geopolitical Cyber Risk
Iran-linked cyber operations were assessed as likely to increase following regional tensions, with potential ransomware and hacktivist targeting across the Middle East.
Industries Facing Highest Risk
Based on March activity, organizations in the following sectors faced elevated risk:
- Professional Services
- Government
- Manufacturing
- Retail
- Healthcare
- Critical Infrastructure
- Transportation & Logistics
These sectors combine valuable data, high uptime requirements, or complex supply chains.
Conclusion
The March 2026 threat landscape was defined by scale, specialization, and speed.
Threat actors increasingly leveraged:
- Access brokerage markets
- High-volume ransomware operations
- Large-scale data theft
- Rapid weaponization of critical vulnerabilities
- AI-enhanced offensive tooling
The combination of concentrated criminal ecosystems and widespread enterprise exposure creates a sustained high-risk environment for organizations globally.
Key Recommendations
- Prioritize remediation of KEV-listed vulnerabilities
- Strengthen identity security and MFA across remote access platforms
- Monitor for exposed credentials and access sale activity
- Segment critical networks to reduce lateral movement
- Conduct tabletop exercises for ransomware response
- Improve backup resilience and recovery testing
- Monitor software supply chain ecosystems
- Expand threat intelligence coverage across dark web and leak forums
Cyble’s threat intelligence, ransomware monitoring, vulnerability intelligence, and attack surface management solutions help organizations proactively identify risks, prioritize remediation, and defend against evolving global threats.
Book your demo now to see it in action!!!
The post Threat Landscape March 2026: Ransomware Dominance, Access Brokers, Data Leaks, and Critical Exploitation Trends appeared first on Cyble.
Public Notion Pages Leaks Profile Photos and Email address of Editors
Notion, a popular productivity and collaboration platform, is under significant scrutiny from the cybersecurity community.
Security researchers have revealed that public Notion pages silently expose the personally identifiable information (PII) of anyone who has ever edited them.
This data leak includes full names, email addresses, and profile photos, raising significant privacy concerns for organizations that rely on the platform for public documentation.
Notion Pages Exposes User Data
The underlying vulnerability stems from how Notion processes user data within public workspaces.
When a document is published to the web, the platform embeds editor UUIDs (Universally Unique Identifiers) directly into the page’s block permissions.
Threat actors and open-source intelligence (OSINT) researchers discovered that these internal identifiers are readily accessible in the page data without requiring any authentication, active session cookies, or security tokens.
Once these UUIDs are harvested, an attacker can feed them into a single unauthenticated POST request to Notion’s internal API endpoint: /api/v3/syncRecordValuesMain.
Because this endpoint does not enforce access controls for public page data, it returns the complete user profiles associated with those UUIDs.
every public Notion page is leaking the email addresses of everyone who edited it.
— impulsive (@weezerOSINT) April 19, 2026
zero authentication. no cookies. no tokens. one POST request returns full names, emails, and profile photos for every editor on the page.
your company wiki is public? every employee's email is… pic.twitter.com/jqWSCVBoyH
Consequently, a public company wiki or open-source project board can inadvertently expose the exact contact details of every employee or contributor who interacts with the document.
The most controversial aspect of this exposure is its long, unresolved timeline. According to security researchers, this exact API behavior was responsibly disclosed to Notion through the HackerOne bug bounty program in July 2022.
At the time, Notion’s security team triaged the submission as merely “informative”. It closed the report as out of scope without implementing a structural patch.
The issue recently resurfaced on X, sparking outrage among developers and cybersecurity professionals. Many paying subscribers expressed extreme frustration with the platform’s perceived negligence, noting that an issue ignored for nearly 4 years leaves thousands of indexable pages vulnerable to scraping.
Security experts emphasized that this exposed data creates a massive attack surface for targeted phishing campaigns and social engineering attacks against corporate targets.
Official Response and Proposed Mitigations
Following the intense public backlash, Notion has formally acknowledged the problem. Notion representative Max Schoening addressed the community’s concerns, noting that the platform provides user warnings about data visibility when a page is published to the web.
However, recognizing that this design choice poses unacceptable security risks, Notion is now working on a permanent architectural fix.
The engineering team plans to either strip PII completely from public-facing endpoints or implement an email proxy system to mask user addresses.
In the meantime, organizations using Notion for public-facing resources should remain vigilant, as their employee contact information may already be indexed and accessible to automated scraping tools.
Follow us on Google News, LinkedIn, and X for daily cybersecurity updates. Contact us to feature your stories.
The post Public Notion Pages Leaks Profile Photos and Email address of Editors appeared first on Cyber Security News.

Smashing Security podcast #463: This AI company leaked its own code. It’s also built something terrifying
Massive Data Breach Exposes 337K LAPD-Linked Records
A massive breach exposed 337K LAPD-linked files, raising concerns over third-party risk, sensitive data exposure, and law enforcement cybersecurity gaps.
The post Massive Data Breach Exposes 337K LAPD-Linked Records appeared first on TechRepublic.
Anthropic accidentally leaks Claude Code
Anthropic accidentally exposed Claude Code source via npm, causing the code to quickly spread online after discovery.
Anthropic accidentally leaked the source code of its Claude Code tool after a large debug file was included in a public npm release. The file exposed over 500,000 lines of code, which were quickly discovered, shared, and analyzed by developers after being flagged online.
— Chaofan Shou (@Fried_rice) March 31, 2026
“Earlier today, a Claude Code release included some internal source code. No sensitive customer data or credentials were involved or exposed. This was a release packaging issue caused by human error, not a security breach. We’re rolling out measures to prevent this from happening again.” an Anthropic spokesperson’s told VentureBeat.
Claude Code’s memory system is carefully engineered for reliability and efficiency. Instead of storing everything, it uses a structured, self-correcting approach: a small index tracks pointers, while actual knowledge is fetched only when needed. Memory updates follow strict rules to avoid polluting context, and a background process continuously merges, deduplicates, and prunes data. Memory is treated as a guide, not absolute truth, and verification against real data is required. Irrelevant or derivable details are never stored, keeping the system lean and accurate.
Based on everything explored in the source code, here's the full technical recipe behind Claude Code's memory architecture:
— himanshu (@himanshustwts) March 31, 2026
[shared by claude code]
Claude Code’s memory system is actually insanely well-designed. It isn't like “store everything” but constrained, structured and… pic.twitter.com/PlGRvuvkts
The leaked Claude Code shows how Anthropic keeps its AI focused during long interactions, avoiding confusion or errors. It uses a layered memory system where a small index tracks locations instead of storing full data, and the actual information is retrieved only when needed. Failed updates don’t affect the AI’s memory, keeping it accurate. Essentially, the model treats its memory as a guide, checking details against the real data before taking action, offering a clear example for others to create more dependable AI agents.
“The leak also pulls back the curtain on “KAIROS,” the Ancient Greek concept of “at the right time,” a feature flag mentioned over 150 times in the source. KAIROS represents a fundamental shift in user experience: an autonomous daemon mode.” states VentureBeat. “While current AI tools are largely reactive, KAIROS allows Claude Code to operate as an always-on background agent. It handles background sessions and employs a process called autoDream. In this mode, the agent performs “memory consolidation” while the user is idle. The autoDream logic merges disparate observations, removes logical contradictions, and converts vague insights into absolute facts.”
The leak reveals Anthropic’s internal AI roadmap, including Capybara (Claude 4.6), Fennec (Opus 4.6), and the unreleased Numbat. Capybara v8 faces a 29–30% false claims rate versus 16.7% in v4. Features like “Undercover Mode” let Claude Code contribute to public repositories without revealing internal info.
The Claude Code leak not only compromises Anthropic’s IP but also exposes Anthropic’s internal architecture, giving attackers a roadmap to bypass security prompts.
Follow me on Twitter: @securityaffairs and Facebook and Mastodon
(SecurityAffairs – hacking, Claude Code)
Anthropic’s Claude Code Source Code Reportedly Leaked Via Their npm Registry
Anthropic’s proprietary Claude Code CLI tool has had its full TypeScript source code inadvertently exposed through a misconfigured npm package, after a security researcher discovered a leaked .map file referencing the unobfuscated codebase stored on Anthropic’s own cloud infrastructure.
On March 31, 2026, researcher Chaofan Shou made the disclosure public, posting: “Claude code source code has been leaked via a map file in their npm registry!”
Claude code source code has been leaked via a map file in their npm registry!
— Chaofan Shou (@Fried_rice) March 31, 2026
Code: https://t.co/jBiMoOzt8G pic.twitter.com/rYo5hbvEj8
The published @anthropic-ai/claude-code npm package reportedly contained a source map (.map) file that referenced the complete, unminified TypeScript source, which was directly downloadable as a ZIP archive from Anthropic’s own R2 cloud storage bucket.
The original unmodified source has since been preserved and mirrored in a public GitHub repository under the backup branch nirholas/claude-code.
What Was Exposed
The leaked codebase represents the entirety of Claude Code’s src/ directory, approximately 1,900 files and over 512,000 lines of code written in strict TypeScript, using the Bun runtime and a React + Ink terminal UI framework. The disclosure is substantial in scope, touching every critical subsystem of the CLI tool.
Key files confirmed in the leak include QueryEngine.ts (~46,000 lines), which drives the core LLM API engine, including streaming, tool loops, and token tracking; Tool.ts (~29,000 lines), defining all agent tool types and permission schemas; and commands.ts (~25,000 lines), which registers and executes the tool’s slash commands.
The exposed architecture details approximately 40 agent tools, including BashTool, FileReadTool, FileEditTool, and AgentTool for sub-agent spawning as well as roughly 85 slash commands spanning Git workflows, code review, memory management, and multi-agent orchestration.
The leak also reveals internal feature flags such as PROACTIVE, VOICE_MODE, BRIDGE_MODE, and KAIROS, indicating product features not yet publicly released.
How Source Maps Cause Leaks
Source map files (.map) are standard developer tools designed to map compiled or minified JavaScript back to its original source for debugging purposes.
When inadvertently bundled into production npm releases, however, they expose proprietary source code to anyone who knows where to look effectively bypassing obfuscation entirely. This is not the first time such an error has affected Anthropic; a similar source map exposure was reportedly patched in early 2025.
The breach raises serious intellectual property concerns for Anthropic, as the exposed code covers internal API client logic, OAuth 2.0 authentication flows, permission enforcement, multi-agent coordination, and even undisclosed feature pipelines. At the time of writing, Anthropic has not issued a public statement regarding the incident.
Organizations integrating Claude Code into their development workflows should monitor Anthropic’s official security advisories. Developers are urged to review the official npm registry for patched releases and avoid third-party mirrors of the leaked source.
Note: This article is based on publicly available disclosures. Cybersecurity News does not host or distribute the leaked source code.
Follow us on Google News, LinkedIn, and X for daily cybersecurity updates. Contact us to feature your stories.
The post Anthropic’s Claude Code Source Code Reportedly Leaked Via Their npm Registry appeared first on Cyber Security News.

Millions of Anonymous Student and Crime Tips Exposed in Major Data Breach
A reported breach of P3 Global Intel exposed millions of anonymous crime and school safety tips, raising new concerns about privacy and trust.
The post Millions of Anonymous Student and Crime Tips Exposed in Major Data Breach appeared first on TechRepublic.
French aircraft carrier Charles de Gaulle tracked via Strava activity in OPSEC failure
A French aircraft carrier was tracked in real time via a sailor’s Strava activity, exposing a persistent operational security flaw.
Le Monde revealed that France’s aircraft carrier Charles de Gaulle was tracked in real time through an officer’s activity on the Strava app. A sailor unknowingly shared running data from the ship, exposing its location in the Mediterranean. The French sailor’s public Strava profile, set as “public,” revealed the near real-time location of the aircraft carrier in the Mediterranean, near Cyprus and Turkey.
“On March 13, at 10:35 a.m., amidst the waves, Arthur (not his real name), a young officer in the French Navy, was out for a run, circling the deck of the ship where he worked. To record his performance—a little over 7 kilometers covered in thirty-five minutes—he used the smartwatch on his wrist. The data collected was then uploaded to the internet.” reported the French media outlet Le Monde. “Because Arthur has a profile on the sports app Strava, and it’s “public”: anyone can view it. “
The case highlights ongoing security risks from fitness apps, as sensitive military positions can still be revealed despite prior warnings.
President Emmanuel Macron announced the deployment of the French naval task force, including the aircraft carrier Charles de Gaulle, three frigates, and a supply ship, on March 3.
“On March 3, Emmanuel Macron himself announced that he had ordered its deployment, just days after the start of the war between Israel, the United States, and Iran.” concludes the report. “The sole French aircraft carrier was then in the Baltic Sea as part of NATO exercises and was scheduled to remain there until May. Its transit”
In the past, Strava fitness data has exposed sensitive military locations worldwide, as American and allied military personnel unknowingly shared exercise routes near bases in Afghanistan, Iraq, and Syria.
These maps clearly highlight otherwise hidden facilities and troop movements, creating serious security risks. Experts warn such data could help adversaries identify and target military sites, underscoring ongoing privacy issues with fitness trackers.
Follow me on Twitter: @securityaffairs and Facebook and Mastodon
(SecurityAffairs – hacking, aircraft carrier Charles de Gaulle)
Ariomex, Iran-based crypto exchange, suffers data leak
Resecurity says Iran’s Ariomex crypto exchange suffered a data leak exposing user and transaction data from 2022 to 2025.
Resecurity (USA) reports that Ariomex’s database, one of Iran’s cryptocurrency exchange platforms, suffered a data leak. The report published by the cybersecurity company presents the findings of a structured analysis of the leaked database, which contains information about end users, their transactions, and the context surrounding their operations, covering the period from 2022 to 2025.
For example, in one of the intercepted communications, Resecurity identified an individual named Seyyed Younes Shokori Bilankouhi requesting to deposit 3 million USD “with the help of the Iranian embassy.” In another case, an individual named Ramin Lak wanted to exchange 5 million USD. Notably, some users used Ariomex as a “bank”—purchasing crypto and storing it there for future use, similar to a traditional bank account. For example, user Eyraj Jaafari bought digital assets worth 100,000 USD multiple times but preferred to “cash out later.”
The experts highlighted that some of the observed records with substantial balances lacked KYC, or the provided information was modified. Resecurity identified multiple suspicious transactions involving large amounts exceeding millions of USD in value.
Leaked customer records:
The data highlights the footprint of Iranian cryptocurrency holders in other geographies, including the US, the UK, Germany, France, the Netherlands, Romania, Russia, Sweden, Turkey, and many others. This intelligence could help block Iranian moneylenders and criminals from entering foreign markets.
A total of 11,826 records were identified, of which around 7,710 originate from Iran, based on IP address data and associated network intelligence. Ariomex data reveals substantial details about the user profiles, their identities, e-mails, IP addresses, and associated cryptocurrency operations.
Example:
- Asking to buy (exchange) $19 Million USD
- Email: khazayizahra75@gmail.com
- FirstName: Zahra
- Surname: Khazaei
- IP: 5.126.48.39
- OS: Android 8.0.0
- Browser: Chrome 106.0.0.0
- Country: Iran
Resecurity identified a stolen Ariomex database circulating on the Dark Web. The root cause of the breach was likely a compromised customer support (helpdesk), leading to the exposure of customer information. The company was able to reproduce missing fields, as well as to apply translation and AI to build profiles of each user with the associated information.
Notably, last year, another prominent cryptocurrency exchange platform in Iran, Nobitex, was hit by a major cyberattack that resulted in the destruction of approximately USD 90 million in digital assets.
Resecurity interprets Ariomex as a shadow financial institution aligned with the Iranian regime. The company emphasizes that disrupting the financial flows linked to the Iranian regime and taking control of crypto exchanges serving malign interests should be among the strategic priorities to identify threat actors and their activity.
Follow me on Twitter: @securityaffairs and Facebook and Mastodon
(SecurityAffairs – hacking, Ariomex)
12 Million exposed .env files reveal widespread security failures
Mysterium VPN found 12M IPs exposing .env files, leaking credentials and revealing widespread security misconfigurations worldwide.
Configuration mistakes rarely trigger alarms. A forgotten deny rule, an overlooked server setting, or a full project folder uploaded to production can quietly expose a company’s most sensitive secrets. In many cases, those secrets live inside simple environment files known as .env files.
Researchers at Mysterium VPN identified 12,088,677 IP addresses serving publicly accessible .env-style files.
“Researchers here at Mysterium VPN identified over 12 million IP addresses with publicly accessible .env-style files, revealing credentials and tokens, including JWT signing keys, API keys, database passwords, and service tokens.” reads the report published by Mysterium VPN. “The United States leads the count with nearly 2.8 million exposed IPs, accounting for around 23% of the total IP pool. The issue is global: Japan (1.1M), Germany (777K), India (652K), France (636K), and the UK (583K) also have substantial exposures, showing that this is a global security hygiene problem.”
These files exposed database credentials, API keys, JWT signing secrets, cloud tokens, and other sensitive values. The scale reveals a widespread operational hygiene problem affecting organizations across industries and regions.
A .env file stores key-value pairs that applications load at startup. Developers use them for database URLs, OAuth secrets, SMTP credentials, cloud access keys, and third-party tokens. The format stays simple and convenient. That same simplicity creates risk. If a server allows access to hidden files, anyone can request “/.env” and download live credentials without exploiting a vulnerability.
Attackers who retrieve these secrets skip the break-in phase entirely. They log in with valid credentials, query databases, forge authentication tokens, abuse APIs, or access cloud storage. OWASP guidance stresses strict secret control, rotation, auditing, and least-privilege scoping because exposed secrets often lead directly to compromise.
The exposure spans the globe. The United States accounts for nearly 2.8 million affected IPs, followed by Japan, Germany, India, France, the UK, Singapore, Ireland, Canada, and Australia. Large cloud and hosting footprints explain part of the distribution, but the pattern points to repeated deployment and configuration mistakes across ecosystems—not a single flawed platform.

These exposures usually stem from preventable errors: missing deny rules for hidden files, reverse proxies forwarding sensitive paths, static roots pointing to entire project directories, container images embedding secrets, or forgotten backup files such as .env.bak or .env.old. Attackers routinely scan for these predictable patterns.
When teams discover an exposed .env file, they must treat the event as a full security incident. Remove public access immediately, purge caches, and rotate every secret in the file. Invalidate tokens, review logs for suspicious access, and implement automated secret scanning in repositories and CI pipelines.
Long term, organizations need layered defenses. Block hidden and backup files at the server and CDN level. Move secrets out of web-accessible directories and into centralized secret management systems with audit logs and automated rotation. Scope keys to minimal permissions, enforce network restrictions, and adopt short-lived tokens. Deploy only approved artifacts and validate that no sensitive files remain publicly reachable.
The Mysterium VPN findings highlight a systemic issue: secret exposure continues at massive scale because teams treat configuration as an afterthought. Security teams must embed secret governance into development workflows, deployment pipelines, and infrastructure baselines. Without that shift, a single overlooked file will keep turning routine deployments into full-scale breaches.
Follow me on Twitter: @securityaffairs and Facebook and Mastodon
(SecurityAffairs – hacking, .env files)



