Visualização de leitura
Hackers Use Jenkins Access to Deploy DDoS Botnet Against Gaming Servers
Anti-DDoS Firm Heaped Attacks on Brazilian ISPs
A Brazilian tech firm that specializes in protecting networks from distributed denial-of-service (DDoS) attacks has been enabling a botnet responsible for an extended campaign of massive DDoS attacks against other network operators in Brazil, KrebsOnSecurity has learned. The firm’s chief executive says the malicious activity resulted from a security breach and was likely the work of a competitor trying to tarnish his company’s public image.

An Archer AX21 router from TP-Link. Image: tp-link.com.
For the past several years, security experts have tracked a series of massive DDoS attacks originating from Brazil and solely targeting Brazilian ISPs. Until recently, it was less than clear who or what was behind these digital sieges. That changed earlier this month when a trusted source who asked to remain anonymous shared a curious file archive that was exposed in an open directory online.
The exposed archive contained several Portuguese-language malicious programs written in Python. It also included the private SSH authentication keys belonging to the CEO of Huge Networks, a Brazilian ISP that primarily offers DDoS protection to other Brazilian network operators.
Founded in Miami, Fla. in 2014, Huge Networks’s operations are centered in Brazil. The company originated from protecting game servers against DDoS attacks and evolved into an ISP-focused DDoS mitigation provider. It does not appear in any public abuse complaints and is not associated with any known DDoS-for-hire services.
Nevertheless, the exposed archive shows that a Brazil-based threat actor maintained root access to Huge Networks infrastructure and built a powerful DDoS botnet by routinely mass-scanning the Internet for insecure Internet routers and unmanaged domain name system (DNS) servers on the Web that could be enlisted in attacks.
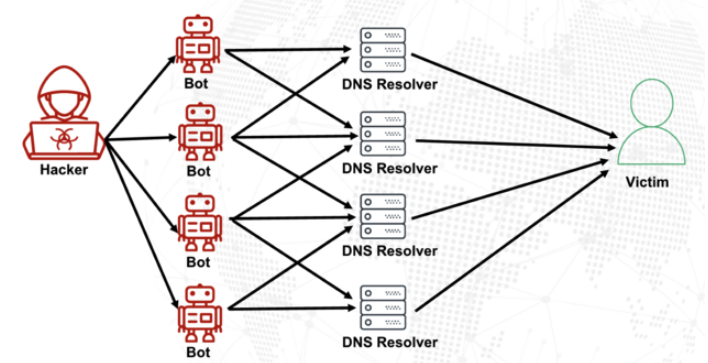
DNS is what allows Internet users to reach websites by typing familiar domain names instead of the associated IP addresses. Ideally, DNS servers only provide answers to machines within a trusted domain. But so-called “DNS reflection” attacks rely on DNS servers that are (mis)configured to accept queries from anywhere on the Web. Attackers can send spoofed DNS queries to these servers so that the request appears to come from the target’s network. That way, when the DNS servers respond, they reply to the spoofed (targeted) address.
By taking advantage of an extension to the DNS protocol that enables large DNS messages, botmasters can dramatically boost the size and impact of a reflection attack — crafting DNS queries so that the responses are much bigger than the requests. For example, an attacker could compose a DNS request of less than 100 bytes, prompting a response that is 60-70 times as large. This amplification effect is especially pronounced when the perpetrators can query many DNS servers with these spoofed requests from tens of thousands of compromised devices simultaneously.
A DNS amplification and reflection attack, illustrated. Image: veracara.digicert.com.
The exposed file archive includes a command-line history showing exactly how this attacker built and maintained a powerful botnet by scouring the Internet for TP-Link Archer AX21 routers. Specifically, the botnet seeks out TP-Link devices that remain vulnerable to CVE-2023-1389, an unauthenticated command injection vulnerability that was patched back in April 2023.
Malicious domains in the exposed Python attack scripts included DNS lookups for hikylover[.]st, and c.loyaltyservices[.]lol, both domains that have been flagged in the past year as control servers for an Internet of Things (IoT) botnet powered by a Mirai malware variant.
The leaked archive shows the botmaster coordinated their scanning from a Digital Ocean server that has been flagged for abusive activity hundreds of times in the past year. The Python scripts invoke multiple Internet addresses assigned to Huge Networks that were used to identify targets and execute DDoS campaigns. The attacks were strictly limited to Brazilian IP address ranges, and the scripts show that each selected IP address prefix was attacked for 10-60 seconds with four parallel processes per host before the botnet moved on to the next target.
The archive also shows these malicious Python scripts relied on private SSH keys belonging to Huge Networks’s CEO, Erick Nascimento. Reached for comment about the files, Mr. Nascimento said he did not write the attack programs and that he didn’t realize the extent of the DDoS campaigns until contacted by KrebsOnSecurity.
“We received and notified many Tier 1 upstreams regarding very very large DDoS attacks against small ISPs,” Nascimento said. “We didn’t dig deep enough at the time, and what you sent makes that clear.”
Nascimento said the unauthorized activity is likely related to a digital intrusion first detected in January 2026 that compromised two of the company’s development servers, as well as his personal SSH keys. But he said there’s no evidence those keys were used after January.
“We notified the team in writing the same day, wiped the boxes, and rotated keys,” Nascimento said, sharing a screenshot of a January 11 notification from Digital Ocean. “All documented internally.”
Mr. Nascimento said Huge Networks has since engaged a third-party network forensics firm to investigate further.
“Our working assessment so far is that this all started with a single internal compromise — one pivot point that gave the attacker downstream access to some resources, including a legacy personal droplet of mine,” he wrote.
“The compromise happened through a bastion/jump server that several people had access to,” Nascimento continued. “Digital Ocean flagged the droplet on January 11 — compromised due to a leaked SSH key, in their wording — I was traveling at the time and addressed it on return. That droplet was deprecated and destroyed, and it was never part of Huge Networks infrastructure.”
The malicious software that powers the botnet of TP-Link devices used in the DDoS attacks on Brazilian ISPs is based on Mirai, a malware strain that made its public debut in September 2016 by launching a then record-smashing DDoS attack that kept this website offline for four days. In January 2017, KrebsOnSecurity identified the Mirai authors as the co-owners of a DDoS mitigation firm that was using the botnet to attack gaming servers and scare up new clients.
In May 2025, KrebsOnSecurity was hit by another Mirai-based DDoS that Google called the largest attack it had ever mitigated. That report implicated a 20-something Brazilian man who was running a DDoS mitigation company as well as several DDoS-for-hire services that have since been seized by the FBI.
Nascimento flatly denied being involved in DDoS attacks against Brazilian operators to generate business for his company’s services.
“We don’t run DDoS attacks against Brazilian operators to sell protection,” Nascimento wrote in response to questions. “Our sales model is mostly inbound and through channel integrator, distributors, partners — not active prospecting based on market incidents. The targets in the scripts you received are small regional providers, the vast majority of which are neither in our customer base nor in our commercial pipeline — a fact verifiable through public sources like QRator.”
Nascimento maintains he has “strong evidence stored on the blockchain” that this was all done by a competitor. As for who that competitor might be, the CEO wouldn’t say.
“I would love to share this with you, but it could not be published as it would lose the surprise factor against my dishonest competitor,” he explained. “Coincidentally or not, your contact happened a week before an important event – one that this competitor has NEVER participated in (and it’s a traditional event in the sector). And this year, they will be participating. Strange, isn’t it?”
Strange indeed.
eBay Struggles with Widespread Outage, Disrupting Transactions and API Access

The Scope of the eBay Outage
The eBay outage first began to affect eBay users on the afternoon of April 26, when they began reporting issues with the platform’s functionality. According to Downdetector, a popular service that tracks online outages, the spike in complaints reached around 3:30 PM ET, with the situation worsening the evening. As of 10:30 PM ET, more than 1,300 outage reports were logged, although the number eventually decreased to about 600 by 11:50 PM ET. Users complained that essential functions like search were malfunctioning, and pages were loading extremely slowly. "I can't even search for anything or complete a purchase," one frustrated user posted on social media. Others echoed similar concerns, noting that critical transactions were unable to be completed, with error messages preventing them from checking out. Sellers also voiced their frustrations, noting that they could not access the API, which is crucial for the functioning of third-party tools used to manage listings, inventory, and sales. "It’s been nearly 6 hours since the API went down, and we have no word from support," one seller wrote, emphasizing the financial impact of the outage.Social Media Users Complain About the Outage
While eBay has not officially confirmed the cause of the outage, rumors quickly began circulating on social media that the hacktivist group 313 Team was responsible for a DDoS attack targeting the platform. DDoS attacks, which flood a website with traffic to overwhelm its servers and take it offline, have become a frequent tactic for hacktivist groups in recent years. The group, which has previously targeted high-profile organizations, allegedly posted a claim on various forums, taking credit for the disruption. However, this attribution has not been independently verified, and eBay has not provided details about the nature of the attack. The company’s official status page displayed no alerts of a cyberattack, showing only minor updates on the system’s functionality. Despite these official updates, the community’s response has been vocal, with many users continuing to report issues well into the night. One individual posted, "It’s not just down for me, it’s down for everyone. Is this part of a bigger attack targeting e-commerce sites?" With eBay’s customer support channels largely silent or offering only generic responses, users took to social media to express their frustration. The company’s Instagram account, where many users had previously reached out for help, quickly became a forum for complaints. One commenter wrote, “Brooo you’re down—come on, get up! I need to pay for an auction.” Others left similar messages, questioning the reliability of the platform and demanding answers.DDoS wave continues as Mastodon hit after Bluesky incident
Mastodon suffered a major DDoS attack shortly after a similar incident hit Bluesky. The outage was significant but resolved within a few hours.
Mastodon was hit by a major DDoS attack just days after a similar disruption affected Bluesky. Mastodon is a free and open-source software platform for decentralized social networking with microblogging features similar to X.
The attack caused a major outage, impacting users across the decentralized platform. However, Mastodon’s team responded quickly and mitigated the issue within a few hours, restoring normal service.
Below is the timeline of the attack:
- April 20, 2026 at 12:58 PM – We are currently experiencing a DDoS attack. We are actively investigating the issue.
- April 20, 2026 at 3:05 PM – We have implemented countermeasure against the DDoS attack, and the site is accessible. We are continuing to monitor the situation.
- April 20, 2026 at 12:58 PM – We are currently experiencing a DDoS attack. We are actively investigating the issue.
A group called 313 Team claimed responsibility for the attack on Bluesky, but no threat actor has publicly taken credit for the Mastodon attack.
Follow me on Twitter: @securityaffairs and Facebook and Mastodon
(SecurityAffairs – hacking, DDOS)
Bluesky Back Online After DDoS Attack, as Iran-Linked 313 Team Takes Credit
Bluesky hit by 24-hour DDoS attack as pro-Iran group claims responsibility
Bluesky suffered a 24-hour DDoS attack that caused outages. A pro-Iran hacker group claimed responsibility for the disruption.
Bluesky experienced a sophisticated DDoS attack that disrupted its services for about 24 hours, starting on April 15.
Bluesky is a decentralized, open-source microblogging social media platform similar to X (formerly Twitter). It allows users to post short messages, images, and videos (up to 300 characters) while providing more control over algorithms, data, and moderation.
The attack disrupted feeds, notifications, threads, and search, causing intermittent outages. A pro-Iran hacker group, called 313 Team (aka “Islamic Cyber Resistance in Iraq”), claimed responsibility, highlighting growing threats against social media platforms and the impact of coordinated disruption campaigns.
“Our team received a report of intermittent app outages at about 11:40pm PDT on April 15, 2026. They worked through the night to mitigate a sophisticated Distributed Denial-of-Service (DDoS) attack, which intensified throughout the day.” Bluesky announced. “We have not seen any evidence of unauthorized access to private user data.”
The company found no signs of data breaches and confirmed it limited the impact of the attack and avoided prolonged outages.
313 Team is a pro-Iran hacktivist group tied to politically driven cyber activity like DDoS attacks, defacements, phishing, and data-leak claims. It targets public services, government and symbolic platforms to create disruption and amplify geopolitical tensions. Analysts link it to the broader Iran-aligned ecosystem, sometimes close to state interests. However, the group often exaggerates its impact, so claims should be treated with caution.
Follow me on Twitter: @securityaffairs and Facebook and Mastodon
(SecurityAffairs – hacking, Islamic Cyber Resistance in Iraq)
Bluesky, Fast-Growing X Alternative, Hit by Sophisticated DDoS Attack

Bluesky Cyberattack Disrupts Core Platform Functions
The disruption began at approximately 11:40 PM PDT on April 15, when Bluesky received initial reports of intermittent outages. Engineers responded immediately, working overnight to contain what was later described as a “sophisticated” DDoS attack. As the attack intensified over the next several hours, it began to impact the platform’s functionality. In an early update, Bluesky stated: “We are experiencing some service interruptions, and our team is working on the issue. You can find the latest updates at status.bsky.app or follow @status.bsky.app.” As more users reported issues, the company clarified the extent of the disruption: “The attack is impacting our application, with users experiencing intermittent interruptions in service for their feeds, notifications, threads and search.” DDoS attacks function by overwhelming servers with massive volumes of traffic, effectively preventing legitimate users from accessing services. In this case, the cyberattack on Bluesky followed that pattern, focusing on disrupting availability rather than infiltrating systems or extracting sensitive data.Platform Stabilizes While Attack Continues
By around 9 PM PDT on April 16, Bluesky reported that the platform had stabilized despite the continued presence of DDoS traffic. The company noted: “The application has remained stable since approximately 9 PM PDT, April 16 despite ongoing Distributed Denial-of-Service (DDoS) attacks. We have not seen any evidence of unauthorized access to private user data.” This message was reiterated in subsequent updates, reinforcing the company’s position that user data remained secure. In its final communication on the incident, Bluesky stated: “The application has remained stable since the evening of April 16 and we have seen no evidence of unauthorized access to private user data. Given the ongoing stability, this will be our final update.”Attribution Remains Unclear as Platform Continues to Grow
The company has not officially attributed the attack to any specific group or actor. However, a group identifying itself as “313 Team,” reportedly claimed responsibility through a Telegram message, stating that it had carried out a “massive cyberattack” targeting Bluesky’s application programming interface (API). The incident comes amid a period of significant growth for the platform. Since its inception, Bluesky has expanded to approximately 43.7 million users, driven in part by users migrating from X following political developments in the United States.Operation PowerOFF: 53 DDoS domains seized and 3 Million criminal accounts uncovered
Operation PowerOFF shut down 53 DDoS-for-hire domains, arrested four suspects, and exposed data on over 3 million criminal user accounts.
Operation PowerOFF is an international law enforcement action that dismantled 53 domains linked to DDoS-for-hire services used by over 75,000 cybercriminals. Authorities arrested four suspects, seized infrastructure, and gained access to databases containing more than 3 million user accounts. They are now warning identified users, while continuing investigations with multiple search warrants.
DDoS-for-hire services, or “booters,” are illegal platforms that let users pay to launch DDoS attacks that flood websites or servers with traffic, causing outages. They are used for harassment, extortion, or disruption and can lead to serious legal consequences for users.
“On 13 April 2026, 21 countries joined forces in a coordinated action week that focused on enforcement and prevention measures against over 75 000 criminal users engaging in distributed denial-of-service (DDoS)-for-hire services.” reads the press release published by EUROPOL. “With over 75 000 warning emails and letters being sent to identified criminal users and 4 arrests, the action week also led to the takedown of 53 domains and the issuing of 25 search warrants.”

Authorities disrupted booter services by seizing servers and infrastructure used to launch attacks, limiting further harm. Access to seized databases with over 3 million user accounts enabled coordinated global actions against cybercriminals and raised awareness about the illegality of these services.
Operation PowerOFF continues with a strong prevention phase to stop future DDoS attacks. Authorities launched campaigns targeting users, including ads warning young people searching for attack tools, removal of over 100 malicious URLs, and warning messages sent via blockchains used for payments. They also updated the official website to highlight ongoing actions and raise awareness about the risks and illegality of DDoS-for-hire services.

Authorities continue dismantling global DDoS-for-hire networks under Operation PowerOFF. In August 2025, the U.S. also took down the RapperBot botnet, used for large-scale attacks across more than 80 countries since 2021.
In December 2024, law enforcement agencies operating under Operation PowerOFF disrupted 27 of the most popular platforms (including zdstresser.net, orbitalstress.net, and starkstresser.net) to launch Distributed Denial-of-Service (DDoS) attacks. The authorities also arrested three administrators of these platforms in France and Germany, and identified over 300 users.
Follow me on Twitter: @securityaffairs and Facebook and Mastodon
(SecurityAffairs – hacking, Operation PowerOFF)
Operation PowerOFF: 75K Users of DDoS-for-Hire Services Identified and Warned
New Mirai Variant Nexcorium Hijacks DVR Devices for DDoS Attacks
Operation PowerOFF Knocks Out 75,000 DDoS Attackers and Over 50 Service Domains
A major international law enforcement campaign has hit the DDoS-for-hire ecosystem, warning more than 75,000 suspected users and disrupting the infrastructure that helped power online attacks around the world. Backed by Europol, Operation PowerOFF brought together authorities from 21 countries in a coordinated action week on 13 April 2026. The operation resulted in four arrests, […]
The post Operation PowerOFF Knocks Out 75,000 DDoS Attackers and Over 50 Service Domains appeared first on GBHackers Security | #1 Globally Trusted Cyber Security News Platform.

13.5M Device Botnet Drives 2 Tbps DDoS Attacks on FinTech, Qrator Finds
Q1 2026 Malware Statistics Report for Linux SSH Servers
Alleged German DDoS-for-Hire Kingpin Behind Fluxstress Caught in Thailand
How AI Is Reshaping Wholesale Network Defense

AI is reshaping network defense, enabling real-time DDoS detection and automated mitigation across global wholesale networks.
The post How AI Is Reshaping Wholesale Network Defense appeared first on Security Boulevard.
Masjesu botnet targets IoT devices while evading high-profile networks
Masjesu is a stealthy DDoS-for-hire botnet targeting IoT devices, active since 2023 and designed to stay hidden by avoiding high-profile networks.
Masjesu is a stealthy botnet active since 2023, advertised as a DDoS-for-hire service. It targets IoT devices like routers and gateways, spanning multiple architectures. Designed for persistence, it executes carefully, avoiding high-profile IP ranges such as the U.S. Department of Defense to remain undetected and survive long-term, favoring low-key attacks over mass infection.
“The Masjesu botnet, a sophisticated, commercially-run Internet of Things (IoT) threat, has been operational and evolving since early 2023, continuing into 2026. Its primary focus is stealth, and it is offered as a “Distributed Denial of Service (DDoS)-for-hire service,” typically marketed via Telegram. It targets a wide array of IoT devices, such as routers and gateways, across multiple architectures (including i386, MIPS, ARM, and AMD64).” reads the report published by Trellix. “Built for persistence and low visibility, Masjesu favors careful, low-key execution over widespread infection, deliberately avoiding blocklisted IP ranges such as those belonging to the Department of Defense (DoD) to ensure long-term survival.”
Masjesu hides its strings, configs, and payloads with XOR encryption to bypass static detection. It scans random IPs and exploits vulnerabilities in devices from D-Link, GPON, and Netgear to spread. Its C2 setup uses multiple domains and fallback IPs and runs TCP, UDP, and HTTP flood attacks.

Masjesu launched DDoS floods up to approximately 290 Gbps, drawing traffic from countries like Vietnam, Ukraine, Iran, Brazil, Kenya, and India, with Vietnam providing nearly half. Operators market its large, stable, and geographically diverse botnet to target CDNs, game servers, and enterprises.

To achieve persistence, the malware renames itself as a legitimate system file (e.g., /usr/lib/ld-unix.so.2), installs a cron job to run every 15 minutes, and daemonizes to operate silently. It also spoofs process names like systemd-journald to avoid detection.
Masjesu kills competing processes (wget, curl, sshd) and locks down /tmp to maintain exclusive control. Its C2 uses multiple domains with a fallback IP, retrieving commands and payloads via HTTP.
For propagation, the bot scans random IPs, avoids sensitive ranges (e.g., DoD), and exploits known flaws in routers and IoT devices (D-Link, GPON, Netgear, etc.).
“Masjesu utilizes the Createchildrenreplic() function for further propagation. This function scans random IP addresses,excluding a catalog of blocklisted IP address ranges (Table 2), for specific hardcoded open ports.” continues the report. “Based on the port identified, a corresponding vulnerability exploit is executed on the target device. Upon successful exploitation, the malicious payload is downloaded onto the compromised device.”
Once infected, bots execute DDoS attacks (TCP, UDP, HTTP floods) based on C2 instructions.
Overall, Masjesu combines obfuscation, resilience, and wide exploitation to sustain a distributed, hard-to-detect attack infrastructure.
“Masjesu (XorBot) is a rapidly maturing IoT botnet focused on DDoS-for-hire, primarily marketed via Telegram and resistant to takedowns. Technically, it minimizes detectability and maximizes attack effectiveness by randomizing packet headers and payloads to better mimic legitimate traffic.” concludes the report. “The botnet continues to expand by infecting a broad range of IoT devices across multiple architectures and manufacturers. “
Follow me on Twitter: @securityaffairs and Facebook and Mastodon
(SecurityAffairs – hacking, Masjesu botnet)