Dangerous New Linux Exploit Gives Attackers Root Access to Countless Computers


Researchers are warning about the risks posed by a low-cost device that can give insiders and hackers unusually broad powers in compromising networks.
The devices, which typically sell for $30 to $100, are known as IP KVMs. Administrators often use them to remotely access machines on networks. The devices, not much bigger than a deck of cards, allow the machines to be accessed at the BIOS/UEFI level, the firmware that runs before the loading of the operating system.
This provides power and convenience to admins, but in the wrong hands, the capabilities can often torpedo what might otherwise be a secure network. Risks are posed when the devices—which are exposed to the Internet—are deployed with weak security configurations or surreptitiously connected to by insiders. Firmware vulnerabilities also leave them open to remote takeover.


© Getty Images
It’s hard to overstate the role that Wi-Fi plays in virtually every facet of life. The organization that shepherds the wireless protocol says that more than 48 billion Wi-Fi-enabled devices have shipped since it debuted in the late 1990s. One estimate pegs the number of individual users at 6 billion, roughly 70 percent of the world’s population.
Despite the dependence and the immeasurable amount of sensitive data flowing through Wi-Fi transmissions, the history of the protocol has been littered with security landmines stemming both from the inherited confidentiality weaknesses of its networking predecessor, Ethernet (it was once possible for anyone on a network to read and modify the traffic sent to anyone else), and the ability for anyone nearby to receive the radio signals Wi-Fi relies on.
In the early days, public Wi-Fi networks often resembled the Wild West, where ARP spoofing attacks that allowed renegade users to read other users' traffic were common. The solution was to build cryptographic protections that prevented nearby parties—whether an authorized user on the network or someone near the AP (access point)—from reading or tampering with the traffic of any other user.


© Getty Image | BlackJack3D

Websites that authenticate users through links and codes sent in text messages are imperiling the privacy of millions of people, leaving them vulnerable to scams, identity theft, and other crimes, recently published research has found.
The links are sent to people seeking a range of services, including those offering insurance quotes, job listings, and referrals for pet sitters and tutors. To eliminate the hassle of collecting usernames and passwords—and for users to create and enter them—many such services instead require users to provide a cell phone number when signing up for an account. The services then send authentication links or passcodes by SMS when the users want to log in.
A paper published last week has found more than 700 endpoints delivering such texts on behalf of more than 175 services that put user security and privacy at risk. One practice that jeopardizes users is the use of links that are easily enumerated, meaning scammers can guess them by simply modifying the security token, which usually appears at the right of a URL. By incrementing or randomly guessing the token—for instance, by first changing 123 to 124 or ABC to ABD and so on—the researchers were able to access accounts belonging to other users. From there, the researchers could view personal details, such as partially completed insurance applications.

Over the past year, Meta has blanketed TV screens around the world with commercials touting the privacy of Whatsapp, its encrypted messenger with a monthly user base of 3 billion people.
“It’s private,” one ad campaign featuring the former cast of the Modern Family TV show says. “On Whatsapp, no one can see or hear your personal messages … not even us,” a different series of ads declares.
On Monday, the former head of security for the Meta-owed messaging app filed a federal whistleblower lawsuit that tells a far different narrative. The suit, filed in US District Court for the District of Northern California, recites a litany of purported security and privacy flaws that Meta not only didn’t fix after becoming aware of them, but also kept secret, allegedly in violation of a $5 billion settlement then-Whatsapp parent company Facebook reached with the Federal Trade Commission. The complaint was filed by Attaullah Baig, who became head of WhatsApp security in 2021.


© Getty Images | NurPhoto
Extensions installed on almost 1 million devices have been overriding key security protections to turn browsers into engines that scrape websites on behalf of a paid service, a researcher said.
The 245 extensions, available for Chrome, Firefox, and Edge, have racked up nearly 909,000 downloads, John Tuckner of SecurityAnnex reported. The extensions serve a wide range of purposes, including managing bookmarks and clipboards, boosting speaker volumes, and generating random numbers. The common thread among all of them: They incorporate MellowTel-js, an open source JavaScript library that allows developers to monetize their extensions.
Tuckner and critics say the monetization works by using the browser extensions to scrape websites on behalf of paying customers, which include AI startups, according to MellowTel founder Arsian Ali. Tuckner reached this conclusion after uncovering close ties between MellowTel and Olostep, a company that bills itself as "the world's most reliable and cost-effective Web scraping API." Olostep says its service “avoids all bot detection and can parallelize up to 100K requests in minutes.” Paying customers submit the locations of browsers they want to access specific webpages. Olostep then uses its installed base of extension users to fulfill the request.
Starting today, Google is implementing a change that will enable its Gemini AI engine to interact with third-party apps, such as WhatsApp, even when users previously configured their devices to block such interactions. Users who don't want their previous settings to be overridden may have to take action.
An email Google sent recently informing users of the change linked to a notification page that said that “human reviewers (including service providers) read, annotate, and process” the data Gemini accesses. The email provides no useful guidance for preventing the changes from taking effect. The email said users can block the apps that Gemini interacts with, but even in those cases, data is stored for 72 hours.
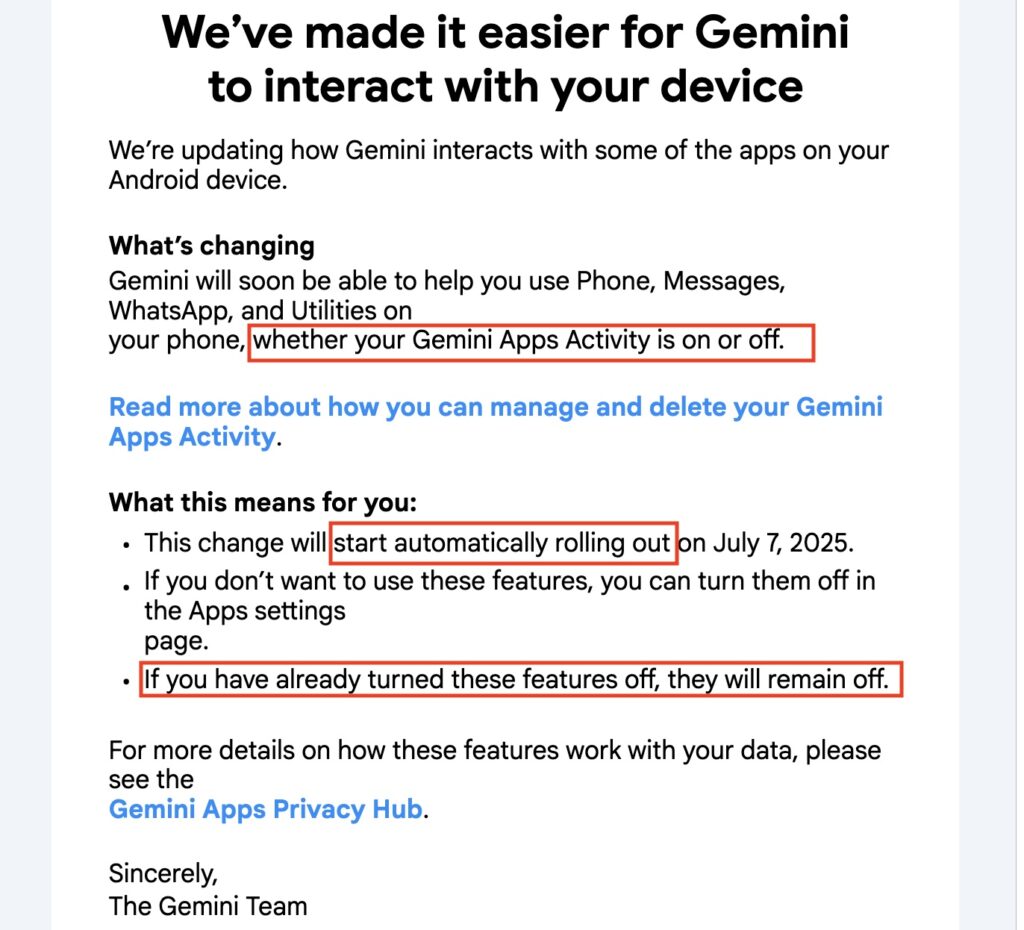 An email Google recently sent to Android users.
An email Google recently sent to Android users.
The email never explains how users can fully extricate Gemini from their Android devices and seems to contradict itself on how or whether this is even possible. At one point, it says the changes “will automatically start rolling out” today and will give Gemini access to apps such as WhatsApp, Messages, and Phone “whether your Gemini apps activity is on or off.” A few sentences later, the email says, “If you have already turned these features off, they will remain off.” Nowhere in the email or the support pages it links to are Android users informed how to remove Gemini integrations completely.


Signal Messenger is warning the users of its Windows Desktop version that the privacy of their messages is under threat by Recall, the AI tool rolling out in Windows 11 that will screenshot, index, and store almost everything a user does every three seconds.
Effective immediately, Signal for Windows will by default block the ability of Windows to screenshot the app. Signal users who want to disable the block—for instance to preserve a conversation for their records or make use of accessibility features for sight-impaired users—will have to change settings inside their desktop version to enable screenshots.
“Although Microsoft made several adjustments over the past twelve months in response to critical feedback, the revamped version of Recall still places any content that’s displayed within privacy-preserving apps like Signal at risk,” Signal officials wrote Wednesday. “As a result, we are enabling an extra layer of protection by default on Windows 11 in order to help maintain the security of Signal Desktop on that platform even though it introduces some usability trade-offs. Microsoft has simply given us no other option.”


© Getty Images
Google is adding a new security setting to Android to provide an extra layer of resistance against attacks that infect devices, tap calls traveling through insecure carrier networks, and deliver scams through messaging services.
On Tuesday, the company unveiled the Advanced Protection mode, most of which will be rolled out in the upcoming release of Android 16. The setting comes as mercenary malware sold by NSO Group and a cottage industry of other exploit sellers continues to thrive. These players provide attacks-as-a-service through end-to-end platforms that exploit zero-day vulnerabilities on targeted devices, infect them with advanced spyware, and then capture contacts, message histories, locations, and other sensitive information. Over the past decade, phones running fully updated versions of Android and iOS have routinely been hacked through these services.
Advanced Protection is Google’s latest answer to this type of attack. By flipping a single button in device settings, users can enable a host of protections that can thwart some of the most common techniques used in sophisticated hacks. In some cases, the protections hamper performance and capabilities of the device, so Google is recommending the new mode mainly for journalists, elected officials, and other groups who are most often targeted or have the most to lose when infected.


© Getty Images
About a decade ago, Apple and Google started updating iOS and Android, respectively, to make them less susceptible to “juice jacking,” a form of attack that could surreptitiously steal data or execute malicious code when users plug their phones into special-purpose charging hardware. Now, researchers are revealing that, for years, the mitigations have suffered from a fundamental defect that has made them trivial to bypass.
“Juice jacking” was coined in a 2011 article on KrebsOnSecurity detailing an attack demonstrated at a Defcon security conference at the time. Juice jacking works by equipping a charger with hidden hardware that can access files and other internal resources of phones, in much the same way that a computer can when a user connects it to the phone.
An attacker would then make the chargers available in airports, shopping malls, or other public venues for use by people looking to recharge depleted batteries. While the charger was ostensibly only providing electricity to the phone, it was also secretly downloading files or running malicious code on the device behind the scenes. Starting in 2012, both Apple and Google tried to mitigate the threat by requiring users to click a confirmation button on their phones before a computer—or a computer masquerading as a charger—could access files or execute code on the phone.


© Aurich Lawson | Getty Images
Spammers used OpenAI to generate messages that were unique to each recipient, allowing them to bypass spam-detection filters and blast unwanted messages to more than 80,000 websites in four months, researchers said Wednesday.
The finding, documented in a post published by security firm SentinelOne’s SentinelLabs, underscores the double-edged sword wielded by large language models. The same thing that makes them useful for benign tasks—the breadth of data available to them and their ability to use it to generate content at scale—can often be used in malicious activities just as easily. OpenAI revoked the spammers’ account in February.
The spam blast is the work of AkiraBot—a framework that automates the sending of messages in large quantities to promote shady search optimization services to small- and medium-size websites. AkiraBot used python-based scripts to rotate the domain names advertised in the messages. It also used OpenAI’s chat API tied to the model gpt-4o-mini to generate unique messages customized to each site it spammed, a technique that likely helped it bypass filters that look for and block identical content sent to large numbers of sites. The messages are delivered through contact forms and live chat widgets embedded into the targeted websites.

© Getty Images | Iurii Motov
A little over two weeks ago, a largely unknown China-based company named DeepSeek stunned the AI world with the release of an open source AI chatbot that had simulated reasoning capabilities that were largely on par with those from market leader OpenAI. Within days, the DeepSeek AI assistant app climbed to the top of the iPhone App Store's "Free Apps" category, overtaking ChatGPT.
On Thursday, mobile security company NowSecure reported that the app sends sensitive data over unencrypted channels, making the data readable to anyone who can monitor the traffic. More sophisticated attackers could also tamper with the data while it's in transit. Apple strongly encourages iPhone and iPad developers to enforce encryption of data sent over the wire using ATS (App Transport Security). For unknown reasons, that protection is globally disabled in the app, NowSecure said.
What’s more, the data is sent to servers that are controlled by ByteDance, the Chinese company that owns TikTok. While some of that data is properly encrypted using transport layer security, once it's decrypted on the ByteDance-controlled servers, it can be cross-referenced with user data collected elsewhere to identify specific users and potentially track queries and other usage.


© Getty Images
As many of us celebrated the year-end holidays, a small group of researchers worked overtime tracking a startling discovery: At least 33 browser extensions hosted in Google’s Chrome Web Store, some for as long as 18 months, were surreptitiously siphoning sensitive data from roughly 2.6 million devices.
The compromises came to light with the discovery by data loss prevention service Cyberhaven that a Chrome extension used by 400,000 of its customers had been updated with code that stole their sensitive data.
The malicious extension, available as version 24.10.4, was available for 31 hours, from December 25 at 1:32 AM UTC to Dec 26 at 2:50 AM UTC. Chrome browsers actively running Cyberhaven during that window would automatically download and install the malicious code. Cyberhaven responded by issuing version 24.10.5, and 24.10.6 a few days later.

© Getty Images