CISA Launches CI Fortify to Defend Critical Infrastructure From Nation-State Cyber Threats





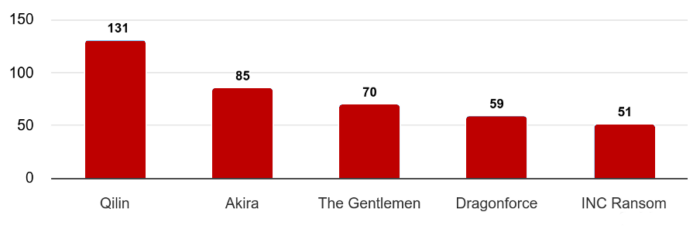 One of the most defining aspects of the March 2026 threat landscape was the scale of ransomware attacks. CRIL recorded 702 ransomware incidents globally, underscoring the continued dominance of ransomware as a primary attack vector.
Among the most active threat groups were Qilin, Akira, The Gentlemen, Dragonforce, and INC Ransom. Collectively, these actors were responsible for over 56% of all observed ransomware activity, reflecting their operational maturity and extensive affiliate networks.
Industries most affected by ransomware attacks included:
One of the most defining aspects of the March 2026 threat landscape was the scale of ransomware attacks. CRIL recorded 702 ransomware incidents globally, underscoring the continued dominance of ransomware as a primary attack vector.
Among the most active threat groups were Qilin, Akira, The Gentlemen, Dragonforce, and INC Ransom. Collectively, these actors were responsible for over 56% of all observed ransomware activity, reflecting their operational maturity and extensive affiliate networks.
Industries most affected by ransomware attacks included:


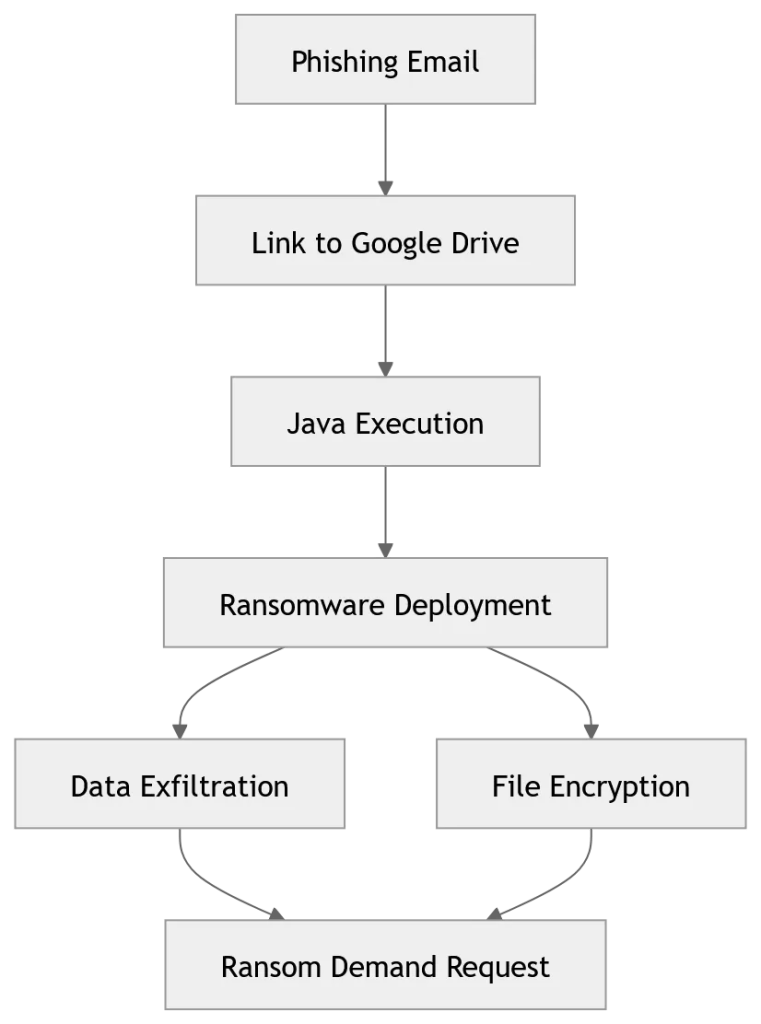 Image Source: Acronis’ Threat Research Unit (TRU)[/caption]
User reports on public cybersecurity forums also describe similar incidents, supporting the assessment that phishing is the main entry point.
Image Source: Acronis’ Threat Research Unit (TRU)[/caption]
User reports on public cybersecurity forums also describe similar incidents, supporting the assessment that phishing is the main entry point.
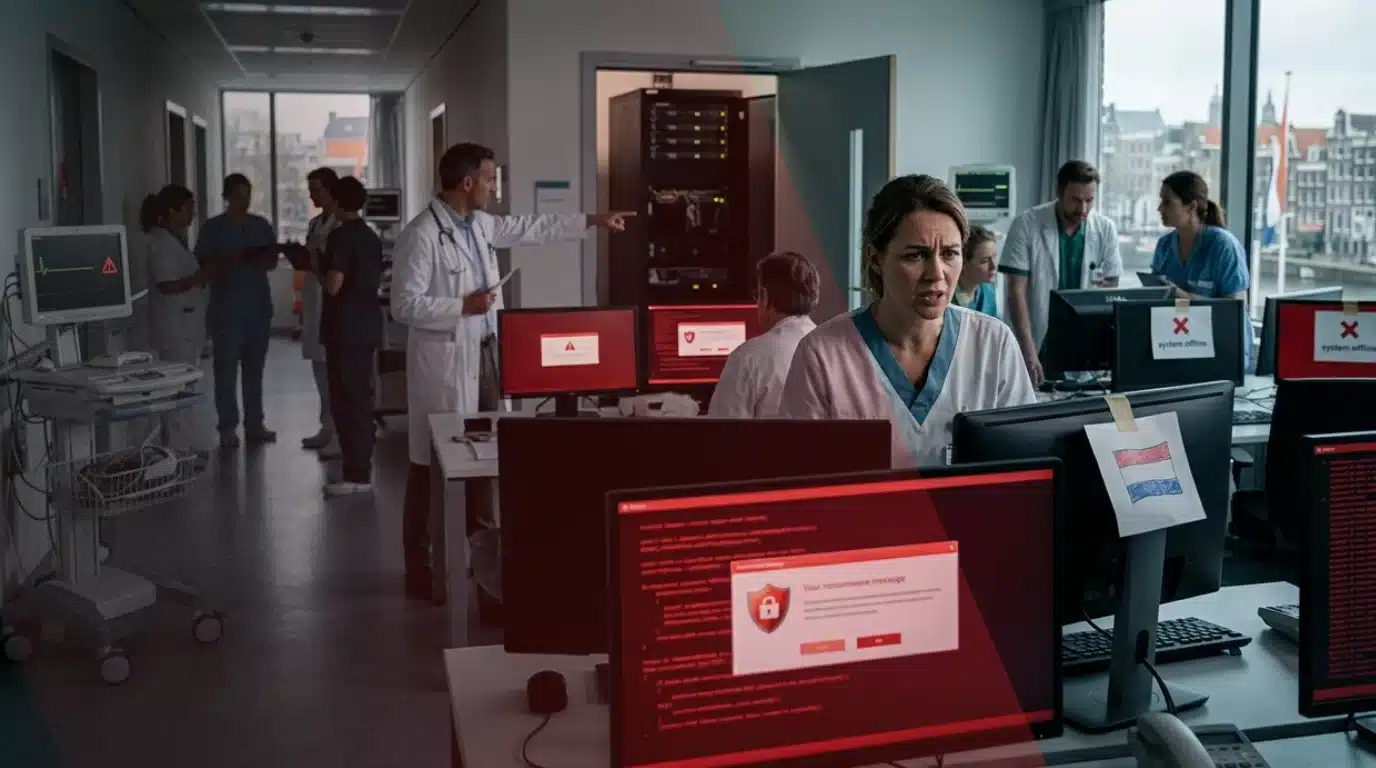


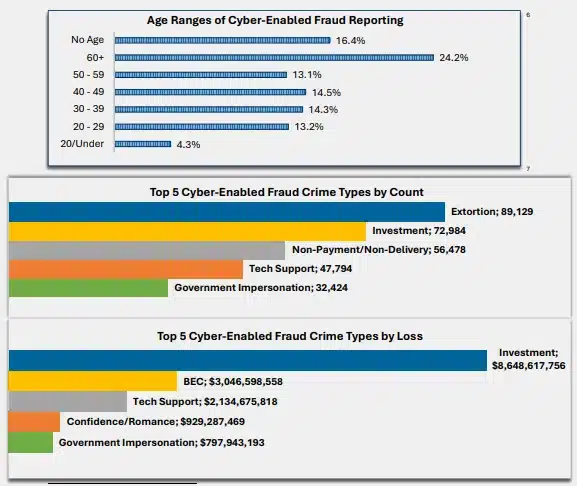 Image Source: FBI Report[/caption]
These scams are no longer basic phishing attempts. Attackers spend time building trust, approaching victims through social media, messaging apps, or even dating platforms. Once trust is established, victims are guided toward fake investment platforms that show fabricated profits. By the time withdrawals are attempted, the money is gone.
Image Source: FBI Report[/caption]
These scams are no longer basic phishing attempts. Attackers spend time building trust, approaching victims through social media, messaging apps, or even dating platforms. Once trust is established, victims are guided toward fake investment platforms that show fabricated profits. By the time withdrawals are attempted, the money is gone.





A federal court in Detroit sentenced Russian national Illya Angelov, on Tuesday, for running a botnet operation that infected thousands of computers daily, sold backdoor access to ransomware groups and victimized 72 companies across 31 U.S. states.
The extortion scheme involving Angelov and his criminal organization, known by the FBI as "Mario Kart," ran from 2017 to 2021. Prosecutors said Angelov and co-conspirators built a network of compromised computers that distributed malware-infected files attached to spam emails.
Angelov and his co-manager then monetized this botnet by selling access to individual compromised computers to other criminal groups, who typically engaged in ransomware extortion schemes — locking victims out of their computer networks and demanding extortion payments to restore access.
A botnet is a network of devices secretly infected with malware and controlled remotely by an attacker without the device owners' knowledge. The court records describe a scheme that was lucrative and prolific, sending 700,000 emails a day to computers around the world and infecting approximately 3,000 computers daily.
The Mario Kart malware provided a backdoor through which software could be uploaded to victims' computers. Instead of directly exploiting this access, the Mario Kart group sold it to customers, that is, other cybercriminal groups. These customers typically used the backdoor access to distribute ransomware, encrypting victims' data and demanding extortion payments to decrypt it.
Angelov's group included software coders who developed programs to distribute spam emails and malware so advanced it could evade virus-detection software. The operation sold backdoor access at scale, functioning as a criminal wholesale supplier to ransomware operators who lacked the infrastructure to breach targets themselves.
Angelov pleaded guilty in secret in October to one count of conspiracy to commit wire fraud. Prosecutors requested he serve 61 months in prison — a significant break from advisory sentencing guidelines calling for more than 12 years — and he was ordered to pay a $100,000 fine and a $1.6 million money judgment. The reduction reflected both his voluntary cooperation and the circumstances of his surrender.
Angelov was sentenced four years after an associate, Vyacheslav Igorevich Penchukov, was arrested in Switzerland and later extradited to the U.S. Penchukov was a member of a group that negotiated a $1 million payment to Angelov and a second individual for access to Mario Kart. A few days after Penchukov's arrest, Angelov contacted U.S. authorities and eventually negotiated his surrender. At the time of his travel and surrender, he was living in the United Kingdom, a country from which the U.S. could have sought his extradition.
Vitlalii Alexandrovich Balint, who provided essential coding to Mario Kart, was sentenced five months earlier in federal court in Detroit to 20 months in prison. While Balint's role in Mario Kart was significant, he was Angelov's subordinate.
The Mario Kart case sits inside a broader DOJ enforcement pattern targeting the upstream criminal economy — the access brokers and botnet operators who supply the tools and entry points that ransomware groups deploy.
The day before Angelov's sentencing, a separate federal court sentenced Russian access broker Aleksei Volkov to 81 months for supplying network access to the Yanluowang ransomware group across dozens of U.S. organizations.
Two Russian cybercriminals sentenced in two consecutive days across two different federal districts signals a deliberate prosecutorial push against the ransomware supply chain's foundational layer, not just its most visible operators.
The scheme operated before the peak of ransomware extortion payments, which reached a high of $1.25 billion in 2023. That trajectory makes the infrastructure Angelov built — and the model it demonstrated — directly relevant to understanding how the ransomware economy scaled to where it stands today.

A single individual selling stolen network credentials to the right buyers can cause more damage than any ransomware group operating alone and a federal court in Indiana made that arithmetic concrete by sentencing a 26-year-old Russian citizen to 81 months in prison for precisely that role — of being an access broker.
Aleksei Volkov, of St. Petersburg, Russia, was sentenced in the Southern District of Indiana for assisting major cybercrime groups, including the Yanluowang ransomware group, in carrying out numerous attacks against U.S. companies and other organizations. Volkov facilitated dozens of ransomware attacks throughout the United States, causing over $9 million in actual losses and over $24 million in intended losses.
Volkov operated as what the cybersecurity industry calls an initial access broker, which is a specialized criminal role that sits upstream of ransomware deployment. Rather than executing attacks himself, Volkov found vulnerabilities in computer networks and systems, identified ways to access those networks and systems without authorization, and sold that illicit access to conspirators who were also cybercriminals.
Those co-conspirators then used the access Volkov provided to infect the affected computer networks and systems with malware, encrypting victims' data and preventing them from accessing it, damaging their business operations.
The conspirators then demanded that the victims pay ransom in cryptocurrency — sometimes in the tens of millions of dollars — in exchange for restoring access to the data and promising not to publicly disclose the hack or release victims' stolen data on a leak website.
The access broker model is a critical enabler of the modern ransomware economy. By separating the intrusion skill from the extortion operation, it allows ransomware groups to scale attacks without needing every member to possess deep technical exploitation expertise. Volkov effectively ran a supply chain for cybercrime — sourcing the raw ingredient that ransomware operators cannot easily produce at volume themselves.
Volkov was arrested on January 18, 2024, in Italy after a Bitcoin transaction originating in Indianapolis tied him to the cybercrime group. He was subsequently extradited to the United States and pleaded guilty to charges including aggravated identity theft and access device fraud.
As part of his plea agreement, Volkov agreed to pay $9,167,198.19 in restitution to known victims. In addition to the 81-month prison term, he received two years of supervised probation. He had been indicted in both the Southern District of Indiana and the Eastern District of Pennsylvania.
The Yanluowang ransomware group, one of the criminal organizations Volkov supplied, previously claimed responsibility for high-profile breaches including a 2022 intrusion into Cisco's corporate network. The group's willingness to target major enterprise organizations shows the downstream risk that a single access broker enabling their operations can create across the entire victim landscape.
Prosecuting access brokers — rather than only the ransomware operators who deploy the final payload — directly attacks the supply chain that makes large-scale ransomware campaigns economically viable. Targeting that upstream layer forces criminal networks to either develop intrusion capabilities in-house — a significant barrier — or risk greater exposure by broadening their supplier relationships.

In this week’s cybersecurity roundup, The Cyber Express covers key global security developments, including a major supply chain disruption affecting a global manufacturer, rising concerns over security and legal risks linked to rapid AI adoption, and the continued escalation of cyber activity driven by geopolitical tensions.
Across industries, organizations are facing a mix of disruptive attacks and long-term espionage campaigns targeting both operational systems and critical infrastructure. Intelligence reports also continue to highlight sustained nation-state activity shaping the global threat landscape.
These developments reflect a cybersecurity environment where operational resilience, secure technology adoption, and coordinated defense strategies are increasingly essential to managing interconnected and fast-evolving risks.
