Acronis celebrates honorees recognized on the 2026 CRN Women of the Channel list


Unit 42 highlights the need for a comprehensive security strategy that spans every IT zone. Explore the full details here.
The post Essential Data Sources for Detection Beyond the Endpoint appeared first on Unit 42.


The conversation around ANZ ransomware threats has shifted noticeably over the past year. What once looked like sporadic, high-profile incidents has evolved into a sustained and structured campaign against organizations across Australia and New Zealand. Signals emerging from underground forums and marketplaces reveal a sobering reality: ransomware is no longer just a technical problem; it is an economic strategy driven by efficiency, specialization, and scale.
At the center of this shift is ransomware dark web intelligence, which paints a clear picture of attacker intent. Threat actors are not simply increasing volume; they are refining their focus. The ANZ region, with its high-value economy and deeply digitized infrastructure, has become a preferred hunting ground.
Australia’s economic profile plays directly into the hands of ransomware operators. A strong GDP, combined with a relatively small population, creates a high-return environment. Attackers don’t need to cast a wide net; each successful breach can yield significant payouts.
By mid-2025, 71 ransomware incidents had been publicly claimed in Australia, compared to nine in New Zealand. On the surface, those figures may seem moderate. However, when adjusted for population, the rate of ransomware attacks in Australia and New Zealand stands out globally. Even larger economies have not experienced the same intensity relative to their size.
This imbalance reflects a fundamental principle driving ANZ organizations cybersecurity risks: attackers prioritize value over volume. In practical terms, fewer victims can still mean higher profits.
Unlike regions where one ransomware group dominates headlines, the dark web ANZ cyber threats ecosystem is notably fragmented. Multiple groups, including Qilin, Akira, INC, Lynx, and Dragonforce, operate concurrently, each claiming a similar share of attacks.
This decentralization complicates defense strategies. Organizations are not facing a predictable adversary with a consistent playbook. Instead, they must prepare for a rotating cast of threat actors, each bringing different techniques, timelines, and negotiation tactics.
From a ransomware dark web intelligence perspective, this fragmentation signals a competitive market. Threat actors are actively testing sectors, probing defenses, and adapting quickly based on what works.
The distribution of ANZ ransomware threats is far from uniform. Certain sectors continue to absorb the majority of attacks due to the nature of their operations.
Healthcare and professional services sit at the top of the list. In healthcare, the urgency of patient care creates a near-zero tolerance for downtime, increasing the likelihood of ransom payments. Professional services firms, on the other hand, hold large volumes of sensitive client data, making them lucrative targets.
However, the scope is broader than these two sectors alone. Aviation software providers, pharmaceutical companies, engineering firms, and even steel manufacturers have all been affected. This pattern reinforces a key insight: ransomware attacks in Australia and New Zealand are opportunistic but calculated, targeting environments where disruption carries tangible consequences.
Several incidents in 2025 highlight how attackers are evolving their methods.
The Akira group compromised an Australian industrial technology provider, exfiltrating approximately 10GB of sensitive data, including financial records and employee identification documents. This case highlights the growing overlap between ransomware and critical infrastructure risk.
In another breach, a political organization suffered exposure to communications, identity records, and financial data, highlighting that ANZ organizations' cybersecurity risks extend beyond the private sector.
Meanwhile, Dragonforce leaked over 100GB of data from an engineering firm, including technical drawings and internal reports. The long-term implications of such intellectual property theft often exceed immediate financial damage.
These cases share a common thread: encryption is no longer the sole objective. Data exfiltration and double extortion have become standard practices.
One of the most important developments in shaping dark web ANZ cyber threats is the growth of the initial access market. In 2025 alone, 92 instances of compromised access sales were observed across Australia and New Zealand.
Retail organizations accounted for roughly 34% of these cases, followed by BFSI and professional services. The implications are significant. Attackers no longer need to breach networks themselves; they can simply purchase access.
This shift has redefined how ANZ ransomware threats materialize. The most complex phase of an attack—initial intrusion—is now outsourced, accelerating timelines and increasing overall attack volume.
It also introduces indirect risk. Organizations may be compromised through vendors, partners, or shared platforms, expanding the attack surface beyond traditional boundaries.
The emergence of affiliate-driven models, particularly groups like INC Ransom, has further amplified ransomware attacks in Australia and New Zealand. Operating under a Ransomware-as-a-Service structure, these groups separate responsibilities: affiliates handle intrusions, while core operators manage ransom negotiations.
This model enables rapid scaling. Multiple attacks can be executed simultaneously, each leveraging shared infrastructure and tooling.
INC Ransom’s activity across healthcare and professional services highlights how effective this approach has become. Their operations often involve credential compromise, privilege escalation, lateral movement, and eventual deployment of ransomware—frequently paired with data exfiltration.
From a ransomware dark web intelligence standpoint, this reflects a mature ecosystem where roles are specialized, and efficiency is maximized.
Although Australia is the primary target, the broader region is not immune. A ransomware attack on Tonga’s Ministry of Health disrupted national healthcare services, while a major breach in New Zealand’s healthcare sector involved both data theft and system encryption.
These incidents reinforce the interconnected nature of ANZ organizations' cybersecurity risks. Threat actors operate without regard for national boundaries, shifting focus wherever defenses appear weakest.
Despite the evolving ecosystem, many attack methods remain consistent. Spear-phishing campaigns, exploitation of unpatched systems, and the use of stolen credentials continue to dominate.
Once inside, attackers often rely on legitimate tools—file compression utilities, remote management software, and standard data transfer mechanisms—to blend into normal operations. This “living off the land” approach makes detection significantly more difficult.
The steady rise of ANZ ransomware threats signals a need for strategic change. Perimeter-based defenses are no longer sufficient in an environment where access can be purchased, and attacks can be outsourced.
As access is bought and attacks are outsourced, organizations must shift toward stronger identity controls, continuous monitoring, rapid patching, and tighter third-party risk management.
Cybersecurity is no longer just about prevention—it’s about resilience. Attacks are inevitable, but their impact doesn’t have to be. Cyble helps organizations stay ahead with AI-powered threat intelligence, dark web monitoring, and predictive defense through its AI-native platform, Cyble Blaze.
Stay ahead of ransomware threats—book a free demo and build a more resilient security posture.
The post ANZ Organizations Are in the Ransomware Crosshairs— What the Dark Web Is Telling Us appeared first on Cyble.
Unit 42 research reports that TGR-STA-1030 remains an active threat, particularly in Central and South America.
The post TGR-STA-1030: New Activity in Central and South America appeared first on Unit 42.


What are the next steps for security leaders in this new age of frontier AI? We answer the top 10 questions customers are asking.
The post Frontier AI and the Future of Defense: Your Top Questions Answered appeared first on Unit 42.

2 min readThere’s a conversation happening inside almost every enterprise right now. Leadership has decided that AI agents are going to change how the organization works. Claude for Work licenses are being purchased. Rollouts are being planned. Employees are being told that their personal AI assistant is here and that it will change everything about how they […]
The post Every Employee is Getting an AI Assistant, But Is Security Infrastructure Ready? appeared first on Aembit.
The post Every Employee is Getting an AI Assistant, But Is Security Infrastructure Ready? appeared first on Security Boulevard.
Key Takeaways We identified an exposed server that provided unusual visibility into a large-scale, multi-victim exploitation and collection operation. Artifacts on the host showed that Claude Code and OpenClaw were embedded in the operator’s day-to-day workflow, supporting troubleshooting, orchestration, and refinement of the collection pipeline. This AI-assisted workflow resulted in the modular platform Bissa scanner […]
The post Bissa Scanner Exposed: AI-Assisted Mass Exploitation and Credential Harvesting appeared first on The DFIR Report.
Unit 42 finds frontier AI models enhance vulnerability discovery, acting as full-spectrum security researchers. They enable autonomous zero-day discovery and faster N-day patching.
The post Fracturing Software Security With Frontier AI Models appeared first on Unit 42.

The problem with how we monitor identity risk today For years, dark web monitoring has been positioned as the frontline defense against compromised credentials and identity exposure. If your data showed up on the dark web, you got an alert. If it didn’t, you assumed you were safe. That model no longer reflects reality. The […]
The post Why Dark Web Monitoring Is No Longer Enough (And What Comes Next) appeared first on Security Boulevard.
Booking.com's breach exposed names, phone numbers, and booking details now being used in targeted WhatsApp phishing. Constella explains how the PII-to-smishing pipeline works and what to do about it.
The post Booking.com Breach Shows Exactly How Smishing Attacks Get Made appeared first on Security Boulevard.

As the cybersecurity community prepares for Black Hat Asia 2026 Singapore, the conversation is shifting from isolated incidents to systemic risk. The Black Hat Asia 2026 conference arrives at a moment when cyber threats are no longer sporadic disruptions. Instead, they are persistent, industrialized, and intertwined with global infrastructure.
The discussions expected in the Black Hat Asia 2026 schedule and among Black Hat Asia 2026 speakers will likely reflect a reality that defenders are already grappling with: scale has become the defining feature of modern cybercrime.
Ransomware activity since late 2025 has moved beyond periodic spikes into a sustained, high-frequency operating model. Over the last four months, threat actors have claimed roughly 700 victims per month on average. This marks a notable jump from the approximately 512 monthly victims observed in the first three quarters of 2025, an increase of more than 30 percent.
This is not just growth; it highlights maturation. Ransomware groups are no longer operating like loosely organized gangs. They resemble production systems, automated, repeatable, and optimized for throughput. Attack pipelines now rely heavily on credential theft, automated exploitation of known vulnerabilities, and scalable infrastructure that allows campaigns to run continuously.
Supply chain compromises have amplified this efficiency. Rather than targeting organizations individually, attackers breach IT providers or managed service vendors to access multiple downstream victims. One compromised vendor can cascade into dozens of affected organizations, dramatically increasing operational impact.
Among active groups, Qilin has demonstrated particularly aggressive activity, with over 100 claimed victims in a single month.
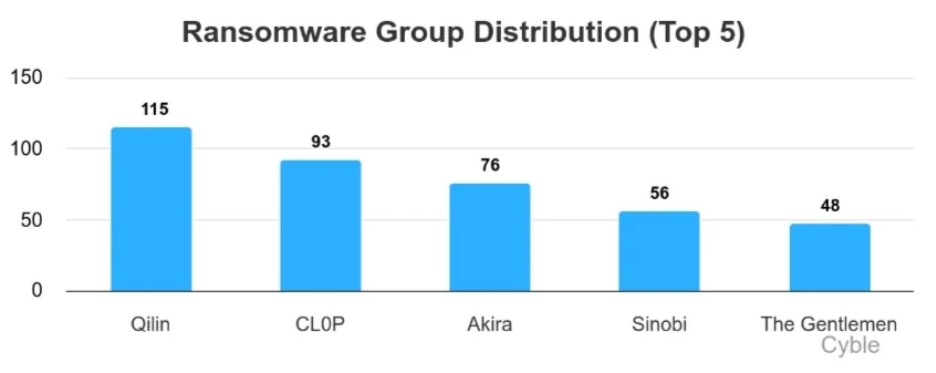
Meanwhile, CL0P has re-emerged with campaigns targeting enterprise software ecosystems, an approach that historically yields high-volume results when successful.
Other groups, such as Akira continue to operate at a steady pace, while newer entrants like Sinobi and The Gentlemen are quickly establishing themselves. This constant churn reflects a competitive underground economy where innovation is driven by survival.
Notably, the tactics themselves are evolving. Traditional ransomware encryption is no longer the centerpiece. Instead, attackers prioritize data exfiltration, public exposure threats, and rapid monetization. Negotiation cycles are shrinking, and pressure tactics are intensifying.
Geographically, ransomware activity continues to concentrate in highly digitized economies. The United States remains the primary target, accounting for nearly half of observed incidents in early 2026. However, the United Kingdom and Australia have also seen increased activity, partly linked to large-scale exploitation campaigns.
The logic is straightforward: attackers follow digital density. Regions with mature enterprise ecosystems, extensive outsourcing, and interconnected infrastructure offer higher payouts and more opportunities for lateral movement.
From a sector perspective, construction, manufacturing, and professional services remain frequent targets. These industries often operate with fragmented security controls and rely heavily on interconnected supplier networks, conditions that attackers exploit.
The IT services sector is also attractive. Compromising a service provider can unlock access to multiple client environments, effectively multiplying the impact of a single intrusion.
Recent incidents highlight the diversity and scale of ransomware impact. CL0P-linked campaigns have affected organizations across the finance, healthcare, and hospitality sectors in multiple regions. Meanwhile, the Everest group has reportedly targeted a U.S.-based telecommunications manufacturer, exfiltrating sensitive engineering data such as circuit schematics and design files, assets that carry long-term intellectual property risks.
Critical infrastructure-adjacent organizations are also under pressure. A breach attributed to Qilin reportedly exposed sensitive data from a U.S. airport authority, including financial records and operational documents.
In Asia, attacks against IT service providers underscore the ongoing vulnerability of managed environments. When attackers access centralized infrastructure, they gain leverage over multiple organizations simultaneously.
Even as established groups dominate headlines, new ransomware operations continue to emerge. Groups like Green Blood, DataKeeper, and MonoLock highlight how accessible the ransomware ecosystem has become. Many operate under ransomware-as-a-service models, lowering the barrier to entry for affiliates.
These newer groups often emphasize technical features such as in-memory execution, multithreaded encryption, and hybrid cryptographic techniques. But more importantly, they reflect a broader trend: ransomware is becoming a business model, complete with revenue-sharing schemes and affiliate programs.
While ransomware dominates, it is only part of the threat landscape leading into Black Hat Asia 2026. Hacktivist activity has expanded, with loosely aligned groups forming coordinated networks across geopolitical lines. These operations are often low in sophistication, focused on DDoS attacks and defacements, but high in volume and visibility.
At the same time, mobile-based threats and social engineering campaigns are accelerating. Attackers are leveraging real-world events to craft convincing phishing messages, malicious apps, and even voice-based scams. The use of AI tools has made these attacks more scalable and believable, reducing the skill required to execute them.
The rapid adoption of artificial intelligence, particularly in countries like India, is introducing both opportunity and risk. AI systems are no longer passive tools; they are active decision-makers embedded in critical workflows.
This shift expands the attack surface. Threats now include data poisoning, model manipulation, prompt injection, and unintended data leakage through AI outputs. At the same time, AI is enabling attackers to automate reconnaissance, personalize phishing, and accelerate vulnerability discovery.
The result is a more balanced battlefield; both attackers and defenders have access to powerful tools, but the speed of offense is increasing faster than defensive adaptation.
The Black Hat Asia 2026 schedule is likely to reflect these converging trends: industrialized ransomware, supply chain fragility, AI-driven threats, and the growing complexity of global cyber operations. The Black Hat Asia 2026 speakers will not just be discussing vulnerabilities; they will be addressing systemic risk across interconnected ecosystems.
The current threat landscape suggests a fundamental shift in how organizations must approach security. Prevention alone is no longer sufficient. Resilience, through segmentation, strong identity controls, continuous monitoring, and robust backup strategies, has become essential.
Equally important is understanding external risk. Third-party exposure, supply chain dependencies, and shared infrastructure are now central to organizational security posture.
As Black Hat Asia 2026 Singapore approaches, one thing is cannot be overlooked: cybersecurity is no longer a technical function operating in the background. It is a discipline that must evolve continuously to keep pace with an organized, adaptive, and relentless adversary ecosystem.
The post Black Hat Asia 2026 Is Coming to Singapore — Here’s What the Threat Landscape Looks Like Ahead of It appeared first on Cyble.

A new category is emerging in cybersecurity For years, organizations have relied on monitoring tools to detect compromised credentials and exposed data. But as identity has become the primary attack surface, those tools are no longer enough. A new category is emerging in response: Identity Risk Intelligence This isn’t just a new label. It represents […]
The post What Is Identity Risk Intelligence? (And Why It’s Replacing Monitoring) appeared first on Security Boulevard.

Security has shifted—but many strategies haven’t For decades, cybersecurity strategies have focused on protecting infrastructure: Firewalls Endpoints Networks But attackers have evolved. Today, they don’t need to break in. They log in. And that shift has made identity the most critical—and most overlooked—attack surface. Why identity has become the primary target Several factors have contributed […]
The post Identity Is the New Attack Surface (And Most Teams Aren’t Prepared) appeared first on Security Boulevard.

The misconception: more data intelligence equals better security In cybersecurity, there’s a common assumption: More data = more visibility = better protection But in reality, more data often creates more problems. Security teams today are overwhelmed with: Alerts Feeds Data sources Yet many still struggle to understand what actually matters. The problem with too many […]
The post From Data to Intelligence: Why More Signals Don’t Equal Better Security appeared first on Security Boulevard.