A week in security (March 30 – April 5)
A list of topics we covered in the week of March 30 to April 5 of 2026
The post A week in security (March 30 – April 5) appeared first on Security Boulevard.
A list of topics we covered in the week of March 30 to April 5 of 2026
The post A week in security (March 30 – April 5) appeared first on Security Boulevard.
Last week on Malwarebytes Labs:
Stay safe!
We don’t just report on data privacy—we help you remove your personal information
Cybersecurity risks should never spread beyond a headline. With Malwarebytes Personal Data Remover, you can scan to find out which sites are exposing your personal information, and then delete that sensitive data from the internet.
Apple widened its latest iOS 18 security update to cover far more iPhones and iPads, specifically to stop real‑world DarkSword attacks that can compromise a device from a single website visit.
After researchers published their findings about the DarkSword attacks and an exploit kit abusing the vulnerabilities appeared on GitHub, Apple quietly updated its March 24 security bulletin.
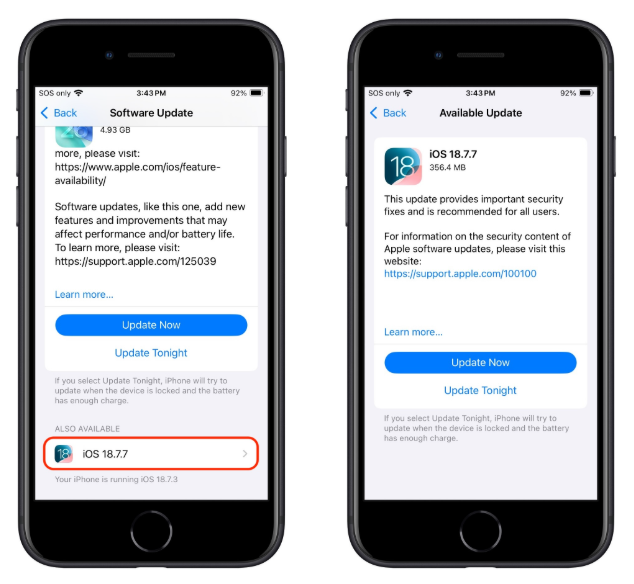
Apple first released iOS/iPadOS 18.7.7 on March 24 to a small set of older devices (iPhone XS/XS Max/XR and 7th‑gen iPad), fixing several vulnerabilities that are part of the DarkSword exploit chain. Newer devices that had the option to upgrade to iOS/iPadOS 26 had stopped receiving iOS 18 point updates, leaving a large group of users effectively stranded on vulnerable 18.x builds.
DarkSword is a full‑chain iOS exploit kit that strings together six vulnerabilities in WebKit, Safari, the dynamic loader, and the kernel to go from a browser visiting a malicious website to full device compromise. The chain has been observed in the wild since at least November 2025 in campaigns set up by commercial spyware vendors and state‑sponsored actors.
There is no need to tap a link in Messages or approve an install prompt. Just loading a compromised site or even a malicious advertisement inside Safari is enough to trigger the exploit chain if your device is still missing the relevant patches.
In this case, attackers combined six vulnerabilities, some already fixed, some still zero‑day at the time, into a cyber-weapon that could turn a routine website visit into a full device compromise and mass data theft. By the time the exploit chain’s details leaked and proof‑of‑concept code hit GitHub, hundreds of millions of devices were potentially exposed, and even “ordinary” users with no reason to fear state surveillance suddenly had to worry about their photos, chats, and crypto wallets.
For years, many iPhone users have treated updates as a trade‑off between “features I don’t care about” and “battery life I do care about.” DarkSword, and Apple’s decision to reopen iOS 18 updates to more devices, is a reminder that there’s a third factor: silently accumulating risk.
For iOS and iPadOS users, here’s how to check if you’re using the latest software version:
If you prefer, and many people do, you can stay on iOS 18 by using the Also Available option in Software Update and explicitly choosing iOS 18.7.7 instead of 26.4.
If you have reason to believe you’re a potential target for attacks of this nature (journalists, activists, or people that have access to sensitive data) it is advisable to enable Lockdown Mode:
Do inform yourself about the consequences of turning on Lockdown Mode. It makes your device a lot less user-friendly, but it has proven effective against highly targeted attacks.
We don’t just report on phone security—we provide it
Cybersecurity risks should never spread beyond a headline. Keep threats off your mobile devices by downloading Malwarebytes for iOS, and Malwarebytes for Android today.
A newer DarkSword exploit leak makes hacking outdated iPhones easier, exposing hundreds of millions of devices to risk.
The post New ‘DarkSword’ Leak Puts Millions of iPhones at Risk After Initial Attack appeared first on TechRepublic.
Apple has warned that iPhones running outdated iOS versions are at risk from exploit kits like Coruna and DarkSword. These attacks use malicious web content to trigger infection chains that can steal sensitive data. Users are strongly advised to update their devices to stay protected.
“Security researchers recently identified web-based attacks that target out-of-date versions of iOS through malicious web content. For example, if you’re using an older version of iOS and were to click a malicious link or visit a compromised website, the data on your iPhone might be at risk of being stolen.” reads Apple’s advisory. “We thoroughly investigated these issues as they were found and released software updates as quickly as possible for the most recent operating system versions to address vulnerabilities and disrupt such attacks.”
Keeping the iPhone updated is the most effective way to stay protected from threats like Coruna and DarkSword. Devices running the latest iOS versions are not vulnerable, and Lockdown Mode also blocks these attacks, even on older systems, though updates are still strongly recommended.
If your iPhone runs an older iOS version, take action:
Updating ensures user data remains secure.
In February, Google’s Threat Intelligence Group identified a powerful new iOS exploit kit called Coruna (also known as CryptoWaters) that targets Apple iPhones running iOS versions 13.0 through 17.2.1. The kit includes five full exploit chains and a total of 23 exploits.
| Codename | CVE | Type |
|---|---|---|
| buffout | CVE-2021-30952 | WebContent R/W |
| jacurutu | CVE-2022-48503 | WebContent R/W |
| bluebird | No CVE | WebContent R/W |
| terrorbird | CVE-2023-43000 | WebContent R/W |
| cassowary | CVE-2024-23222 | WebContent R/W |
| breezy | No CVE | WebContent PAC bypass |
| breezy15 | No CVE | WebContent PAC bypass |
| seedbell | No CVE | WebContent PAC bypass |
| seedbell_16_6 | No CVE | WebContent PAC bypass |
| seedbell_17 | No CVE | WebContent PAC bypass |
| IronLoader | CVE-2023-32409 | WebContent sandbox escape |
| NeuronLoader | No CVE | WebContent sandbox escape |
| Neutron | CVE-2020-27932 | PE |
| Dynamo | CVE-2020-27950 | PE (infoleak) |
| Pendulum | No CVE | PE |
| Photon | CVE-2023-32434 | PE |
| Parallax | CVE-2023-41974 | PE |
| Gruber | No CVE | PE |
| Quark | No CVE | PPL Bypass |
| Gallium | CVE-2023-38606 | PPL Bypass |
| Carbone | No CVE | PPL Bypass |
| Sparrow | CVE-2024-23225 | PPL Bypass |
| Rocket | CVE-2024-23296 | PPL Bypass |
While highly capable against iPhones running iOS 13.0 through 17.2.1versions, Coruna is ineffective against the latest iOS release, according to Google.
GTIG tracked the use of the exploit in highly targeted attacks by a surveillance vendor’s customer, in Ukrainian watering hole campaigns by UNC6353, and later in broad-scale attacks by Chinese financial threat actor UNC6691, showing an active market for “second-hand” zero-day exploits. Multiple threat actors now reuse and adapt these advanced techniques for new vulnerabilities.
GTIG shared the findings to raise awareness and protect users, adding identified domains to Safe Browsing.
Initial discovery occurred in February 2025 when GTIG captured a previously unseen JavaScript framework delivering an iOS exploit chain from a surveillance vendor’s customer.
“In February 2025, we captured parts of an iOS exploit chain used by a customer of a surveillance company.” reads the report published by GTIG. “The exploits were integrated into a previously unseen JavaScript framework that used simple but unique JavaScript obfuscation techniques.”
“The core technical value of this exploit kit lies in its comprehensive collection of iOS exploits, with the most advanced ones using non-public exploitation techniques and mitigation bypasses.”

The framework uses fingerprinting to detect device type and iOS version, then loads the appropriate WebKit RCE exploit and pointer authentication bypass. One recovered exploit, CVE-2024-23222, was later patched in iOS 17.3.
Government-backed attackers used the same framework in Ukrainian watering hole attacks, delivering multiple RCE exploits to select iPhone users. Later, Chinese scam websites deployed the full Coruna kit, dropping the same exploits via hidden iFrames on fake financial and crypto sites. GTIG collected hundreds of samples covering all five exploit chains and observed debug versions exposing internal exploit names, confirming the kit’s internal name as Coruna.
The Coruna exploit kit relies on a highly engineered framework that links all components through shared utilities and custom loaders. It avoids devices in Lockdown Mode or private browsing, derives resource URLs from a hard-coded cookie, and delivers WebKit RCE and PAC bypasses in clear form. After exploitation, a binary loader deploys encrypted, compressed payloads disguised as .min.js files, tailored to specific chips and iOS versions. In total, the kit includes 23 exploits covering iOS 13 through 17.2.1, with advanced mitigation bypasses and reusable modules for defeating memory and kernel protections.
At the end of the chain, a stager called PlasmaLoader injects into a root daemon and deploys a financially focused payload.
The malware scans for crypto wallets, backup phrases, and banking data, exfiltrating sensitive information and loading additional modules from command-and-control servers. It targets numerous cryptocurrency apps, uses encrypted communications, and falls back on a custom domain generation algorithm seeded with “lazarus” to maintain persistence.
Google published Indicators of Compromise (IOCs) and Yara rules for this exploit.
Recently, Lookout Threat Labs discovered a new iOS exploit kit called DarkSword that has been used since late 2025 by multiple threat actors, including surveillance vendors and likely nation-state actors. The toolkit enables full-chain attacks to steal sensitive data from Apple devices and has been observed in campaigns targeting countries such as Saudi Arabia, Turkey, Malaysia, and Ukraine.
The exploit chain relies on six vulnerabilities, three used as zero-days, to achieve full device compromise:
Together, these flaws enable full-chain exploitation and complete control of targeted iOS devices.
DarkSword targets iPhones running iOS 18.4–18.7 and has been used by the suspected Russian-linked group UNC6353 against Ukrainian targets. It allows attackers to steal sensitive data, including credentials and crypto wallet information, then quickly exfiltrates it in a “hit-and-run” approach before cleaning traces.
The exploits appear to be linked to Coruna exploits, DarkSword enables near full device access with minimal user interaction, showing how advanced exploits are now available on a secondary market to a wider range of threat actors.
“DarkSword aims to extract an extensive set of personal information including credentials from the device and specifically targets a plethora of crypto wallet apps, hinting at a financially motivated threat actor.” reads the report published by Lookout. “Notably, DarkSword appears to take a “hit-and-run” approach by collecting and exfiltrating the targeted data from the device within seconds or at most minutes followed by cleanup.”
Researchers investigating Coruna uncovered related infrastructure linked to Russian actor UNC6353, including a similar domain used in attacks on compromised Ukrainian sites, even government ones. Malicious iframes loaded scripts to fingerprint devices and target specific iOS versions. Further analysis revealed a new exploit chain, later named DarkSword, discovered in late 2025 through joint research by Lookout, iVerify, and Google, confirming a distinct and evolving threat.
While it initially appeared that this may be another site distributing Coruna, upon closer inspection of the our researchers found that the iframe loads a javascript file called rce_loader.js, which is largely responsible for fingerprinting devices visiting the compromised site in order to determine whether to route the devices to the iOS exploit chain. However, the script was looking for iOS devices with OS versions 18.4 or 18.6.2, which are iOS versions that are not susceptible to the exploit chains used in Coruna.

Recognizing that this was a new threat, our researchers analyzed the code and began capturing all of the stages of the exploits.
According to Lookout, the actor behind the exploit, UNC6353, remains a largely unknown group but has used advanced iOS exploit chains in watering hole attacks on Ukrainian websites. Likely well-funded, it appears to rely on third-party or brokered exploits, possibly linked to Russian ecosystems. The group targets both intelligence and financial data, including crypto assets, suggesting dual motives.
Its infrastructure is limited but shows deep access to compromised sites. Poor obfuscation and signs of AI-assisted code suggest limited in-house expertise. Overall, UNC6353 is assessed as a capable yet not highly sophisticated actor, potentially a Russia-aligned proxy blending espionage with cybercrime.
Google GTIG experts found multiple actors using DarkSword since November 2025, and believes other surveillance vendors or threat groups are likely using the exploit chain as well.

“The use of both DarkSword and Coruna by a variety of actors demonstrates the ongoing risk of exploit proliferation across actors of varying geography and motivation.” concludes GTIG.
Follow me on Twitter: @securityaffairs and Facebook and Mastodon
(SecurityAffairs – hacking, exploit kits)
Lookout Threat Labs discovered a new iOS exploit kit called DarkSword that has been used since late 2025 by multiple threat actors, including surveillance vendors and likely nation-state actors. The toolkit enables full-chain attacks to steal sensitive data from Apple devices and has been observed in campaigns targeting countries such as Saudi Arabia, Turkey, Malaysia, and Ukraine.
The exploit chain relies on six vulnerabilities, three used as zero-days, to achieve full device compromise:
Together, these flaws enable full-chain exploitation and complete control of targeted iOS devices.
DarkSword targets iPhones running iOS 18.4–18.7 and has been used by the suspected Russian-linked group UNC6353 against Ukrainian targets. It allows attackers to steal sensitive data, including credentials and crypto wallet information, then quickly exfiltrates it in a “hit-and-run” approach before cleaning traces.
The exploits appear to be linked to Coruna exploits, DarkSword enables near full device access with minimal user interaction, showing how advanced exploits are now available on a secondary market to a wider range of threat actors.
“DarkSword aims to extract an extensive set of personal information including credentials from the device and specifically targets a plethora of crypto wallet apps, hinting at a financially motivated threat actor.” reads the report published by Lookout. “Notably, DarkSword appears to take a “hit-and-run” approach by collecting and exfiltrating the targeted data from the device within seconds or at most minutes followed by cleanup.”
Researchers investigating Coruna uncovered related infrastructure linked to Russian actor UNC6353, including a similar domain used in attacks on compromised Ukrainian sites, even government ones. Malicious iframes loaded scripts to fingerprint devices and target specific iOS versions. Further analysis revealed a new exploit chain, later named DarkSword, discovered in late 2025 through joint research by Lookout, iVerify, and Google, confirming a distinct and evolving threat.
While it initially appeared that this may be another site distributing Coruna, upon closer inspection of the our researchers found that the iframe loads a javascript file called rce_loader.js, which is largely responsible for fingerprinting devices visiting the compromised site in order to determine whether to route the devices to the iOS exploit chain. However, the script was looking for iOS devices with OS versions 18.4 or 18.6.2, which are iOS versions that are not susceptible to the exploit chains used in Coruna.

Recognizing that this was a new threat, our researchers analyzed the code and began capturing all of the stages of the exploits.
“As opposed to many other previously reported cases of sophisticated attacks on mobile devices, DarkSword is not designed for ongoing surveillance.” states the report. “Once it finishes collecting and exfiltrating the targeted data, it deletes the files it created on the filesystem of the device and exits. Its dwell time on the device is likely in the range of minutes, depending on the amount of data it discovers and exfiltrates.”
According to Lookout, the actor behind the exploit, UNC6353, remains a largely unknown group but has used advanced iOS exploit chains in watering hole attacks on Ukrainian websites. Likely well-funded, it appears to rely on third-party or brokered exploits, possibly linked to Russian ecosystems. The group targets both intelligence and financial data, including crypto assets, suggesting dual motives.
Its infrastructure is limited but shows deep access to compromised sites. Poor obfuscation and signs of AI-assisted code suggest limited in-house expertise. Overall, UNC6353 is assessed as a capable yet not highly sophisticated actor, potentially a Russia-aligned proxy blending espionage with cybercrime.
DarkSword shows a troubling trend: advanced iOS exploit chains are being sold on a secondary market, letting even less skilled actors launch powerful attacks. These near zero-click watering hole campaigns are stealthy and bypass user awareness. Once infected, devices face full compromise, with risks to both personal and corporate data, highlighting the urgent need for faster patching and stronger mobile defenses.
“The discovery of DarkSword as the second iOS exploit chain found in the hands of this at least partially financially motivated threat actor reveals a worrying trend.” concludes the report. “There appears to be a secondary market for technically sophisticated exploit chains in which unscrupulous sellers are willing to serve buyers with little or no concerns for how they are going to be used. These groups can then easily customize these kits into malware for their specific purposes, possibly with the help of AI.”
Google GTIG experts found multiple actors using DarkSword since November 2025, and believes other surveillance vendors or threat groups are likely using the exploit chain as well.

“The use of both DarkSword and Coruna by a variety of actors demonstrates the ongoing risk of exploit proliferation across actors of varying geography and motivation.” concludes GTIG.
Follow me on Twitter: @securityaffairs and Facebook and Mastodon
(SecurityAffairs – hacking, DarkSword)
iPhone hacking techniques have sometimes been described almost like rare and elusive animals: Hackers have used them so stealthily and carefully against such a small number of hand-picked targets that they're only rarely seen in the wild. Now a recent spate of espionage and cybercriminal campaigns has instead deployed those same phone-takeover tools, embedded in infected websites, to indiscriminately hack phones by the thousands. And one new technique in particular—capable of taking over any of hundreds of millions of iOS devices—has appeared on the web in an easily reusable form, putting a significant fraction of the world's iPhone users at risk.
Researchers at Google and cybersecurity firms iVerify and Lookout on Wednesday jointly revealed the discovery of a sophisticated iPhone hacking technique known as DarkSword that they've seen in use on infected websites, capable of instantly and silently hacking iOS devices that visit those sites. While the technique doesn't affect the latest updated versions of iOS, it does work against iOS devices running versions of Apple's previous operating system release, iOS 18, which as of last month still accounted for close to a quarter of iPhones, according to Apple's own count.
“A vast number of iOS users could have all of their personal data stolen simply for visiting a popular website,” says Rocky Cole, iVerify's cofounder and CEO. “Hundreds of millions of people who are still using older Apple devices or older operating system versions remain vulnerable.”


© Getty Images Europe

It takes a single page load on a compromised Ukrainian government site, no tap, no download, no warning — and an iPhone running iOS 18.4 through 18.6.2 hands over its messages, photos, passwords, Telegram history, iCloud files, and cryptocurrency wallet keys to an attacker halfway across the world, then erases every trace of the intrusion within minutes.
That is DarkSword. And it has already spread to at least four countries.
On Wednesday, Google Threat Intelligence Group (GTIG), mobile security firm Lookout and device integrity company iVerify published coordinated research disclosing a new iOS full-chain exploit kit they named DarkSword — a name taken directly from a variable buried inside the malware's own code: const TAG = "DarkSword-WIFI-DUMP". The three organizations collaborated across separate discovery threads, with each contributing distinct pieces of a deeply alarming picture.
GTIG tracked DarkSword deployments since at least November 2025, identifying multiple distinct threat actors — including commercial surveillance vendors and suspected state-sponsored groups — deploying the same exploit chain against targets in Saudi Arabia, Turkey, Malaysia, and Ukraine. The chain leverages six vulnerabilities across iOS 18.4 through 18.7, and all six have now been patched in iOS 26.3, though most arrived in earlier updates. Apple was notified by GTIG in late 2025.
The exploit chain's entry point for Ukrainian targets sits inside two compromised websites, novosti[.]dn[.]ua, a news portal, and 7aac[.]gov[.]ua, a Ukrainian government domain. Both sites contained an invisible malicious iframe injected by attackers, which silently loaded exploit code hosted on a server in Estonia. That server only delivered the payload to devices having Ukrainian IP addresses — a deliberate geofencing technique that reduces exposure, frustrates researchers, and increases the operational window before detection.
Once Safari loaded the iframe, DarkSword executed a disciplined, multi-stage attack entirely in JavaScript — a design choice that is itself significant. There is no binary implant, no Mach-O library injected into processes, no traditional malware artifact that endpoint detection logic would expect to find.
The chain breaks out of WebKit's WebContent sandbox, uses WebGPU to inject into a background media process called mediaplaybackd, builds arbitrary kernel read-write access from there, and then uses that access to lift sandbox restrictions across the device's most privileged processes — including configd, wifid, securityd, and UserEventAgent.
The final payload orchestrator, pe_main.js, then injects targeted data-theft modules into each of these processes before staging everything in accessible filesystem locations and exfiltrating the complete collection to a command-and-control server. The staged files are then deleted and the process exits cleanly.
The entire dwell time on a victim device measures in minutes. GTIG has identified three distinct malware families delivered following successful DarkSword compromise: GHOSTBLADE, GHOSTKNIFE, and GHOSTSABER.
What DarkSword steals covers almost every surface of a modern iPhone. SMS and iMessage content, call history, address book, WiFi passwords, Safari browsing history and cookies, location history, health data, photos, iCloud Drive, emails, saved passwords, WhatsApp and Telegram message histories, and the complete list of installed applications.
Most unusually for a state-adjacent espionage tool, DarkSword specifically targets cryptocurrency wallets like Coinbase, Binance, Kraken, Kucoin, Ledger, Trezor, MetaMask, and Exodus, among others. Lookout assesses this as evidence of a financially motivated dimension to the threat actor's operations, distinct from conventional cyber espionage.
The Six Vulnerabilities Underneath DarkSword
DarkSword's power derives from chaining six distinct flaws across different layers of iOS, each one unlocking the next stage of access.
[caption id="attachment_110322" align="aligncenter" width="486"] The six vulnerabilities exploited at various levels of the exploit chain. (Image source: GTIG)[/caption]
The six vulnerabilities exploited at various levels of the exploit chain. (Image source: GTIG)[/caption]
The remote code execution stage exploited two memory corruption vulnerabilities in JavaScriptCore — the JavaScript engine that powers WebKit and Safari. The first, CVE-2025-31277, formed the foundation of the earliest observed DarkSword deployments targeting iOS 18.4 and 18.5.
A second JavaScriptCore memory corruption bug, CVE-2025-43529, was added in a later iteration of the kit targeting iOS 18.6, giving operators redundant entry points across a wider version range. Both bugs enable an attacker to corrupt memory through a malicious webpage alone, requiring no interaction from the victim beyond the page load itself.
Alongside either RCE exploit, DarkSword chains CVE-2026-20700, a Pointer Authentication Code (PAC) bypass in dyld — the dynamic linker responsible for loading code into Apple processes. PAC is a hardware-level security feature Apple introduced specifically to prevent attackers from hijacking code execution; bypassing it is a prerequisite for the deeper access DarkSword achieves. The remaining three vulnerabilities handle the sandbox escape and privilege escalation stages, progressively dismantling iOS security boundaries until the attacker holds unrestricted kernel read-write access across the entire device.
Apple addressed the vulnerabilities on a rolling basis rather than in a single emergency patch, reflecting the staggered pace at which researchers discovered each flaw. CVE-2025-31277 and CVE-2025-43529 received fixes in iOS 26.1 and iOS 26.2 respectively, while CVE-2026-20700 and the remaining privilege escalation vulnerabilities were closed with iOS 26.3.
The final complete remediation, covering all six DarkSword vulnerabilities, landed in iOS 18.7.3 for devices on the iOS 18 branch. The gap between the earliest known DarkSword deployment in November 2025 and the final patch in iOS 26.3 represents a window of roughly four months during which the full chain operated against unpatched devices.
The infrastructure analysis by Lookout revealed an important link to a prior campaign. The delivery domain cdncounter[.]net shares nameservers, registrar, registration date, and IP resolution overlap with uacounter[.]com, a domain GTIG previously tied to UNC6353 — a suspected Russian espionage group that also used the earlier Coruna iOS exploit kit against Ukrainian targets. The same Ukrainian government domain that hosted DarkSword delivery code had previously distributed Coruna. GTIG has now observed UNC6353 incorporating DarkSword into its watering hole campaign repertoire alongside its previous toolkit.
Perhaps the most significant finding across all three research publications is not the sophistication of any single vulnerability, but what the proliferation of DarkSword across multiple unrelated threat actors reveals about the commercial exploit market. Code comments written in Russian appear in the early infrastructure stages; code in subsequent exploit stages switches to English — consistent with a tool built by one developer and sold or transferred to multiple buyers. References to iOS 17.4.1 and 17.5.1 in portions of the code indicate this kit evolved from an earlier version, suggesting an ongoing commercial development and distribution pipeline rather than a one-time build.
Lookout states the threat actor likely gained access to an exploit and post-exploitation toolkit built by a third party. The nation-state grade iOS zero-day chains, which were once assumed exclusive to Tier 1 commercial surveillance vendors supplying governments, now circulate in a secondary market accessible to actors with narrower resources and mixed motives, including financial crime.
Devices running iOS 18.7.3 or iOS 26.3 and later are not vulnerable. Google has added DarkSword delivery domains to Safe Browsing. For devices that cannot be updated immediately, Apple's Lockdown Mode reduces the available attack surface.
Researchers at Google have identified an iOS exploit chain, named DarkSword, that has been used since late last year by multiple actors to infect iPhones with malware in targeted attacks.
DarkSword combines six vulnerabilities in iOS and Safari to deploy malware on the device. It demonstrates, once again, how important it is to keep up with updates.
The exploit works against iPhones running iOS versions 18.4 through 18.7, and simply visiting a malicious or compromised website with a vulnerable device can be enough to get infected (a drive‑by attack).
The researchers found that several groups are using the tool to attack their preferred targets. DarkSword has been used both by commercial spyware vendors and by state‑backed actors, with campaigns observed in Saudi Arabia, Turkey, Malaysia, and Ukraine.
In Saudi Arabia, attackers used a fake Snapchat lookalike. In Ukraine, attackers compromised at least two Ukrainian websites, including a government site.
Upon successful exploitation, malware is executed on the device. The type of malware depends on the attacker. In the Ukrainian campaign, that malware is known as Ghostblade, one example of a payload delivered via the DarkSword exploit chain.
Ghostblade is a JavaScript‑based data‑stealer that exfiltrates unique device identifiers, SMS and iMessage messages, call history, contacts, Wi‑Fi configuration and passwords, Safari cookies and browsing history, location data, notes, calendar entries, health data, photos, iCloud Drive files, SIM information, emails, a list of installed apps, saved passwords, and the message history from Telegram and WhatsApp.
Beyond this, Ghostblade stands out because it also targets cryptocurrency‑related data, actively seeking apps for major exchanges (Coinbase, Binance, Kraken, Kucoin, OKX, Mexc) and wallet apps (Ledger, Trezor, Metamask, Exodus, Uniswap, Phantom, Gnosis Safe). Researchers note that Ghostblade is not built for long‑term surveillance: once it has collected the data, it deletes its temporary files and terminates itself.
Vulnerable devices can be infected just by visiting that one malicious or compromised website. And the consequences can be severe. DarkSword turns a single website visit into full device compromise, followed by Ghostblade exfiltrating as much data as it can in one go.
Since the same exploit kit is being reused across commercial surveillance firms and state‑aligned actors, the number of campaigns and victims will increase over time.
Update to the latest iOS available for your device. DarkSword can affect iOS versions 18.4 through 18.7, and Apple’s recent releases include fixes for CVE‑2026‑20700 and related vulnerabilities.
If you have reason to believe you’re a potential target for attacks of this nature (journalists, activists, or people that have access to sensitive data) it is advisable to enable Lockdown Mode:
Do inform yourself about the consequences of turning on Lockdown Mode. It makes your device a lot less user-friendly, but it has proven effective against highly targeted attacks.
Here are some more general tips:
We don’t just report on phone security—we provide it
Cybersecurity risks should never spread beyond a headline. Keep threats off your mobile devices by downloading Malwarebytes for iOS, and Malwarebytes for Android today.