The post Omani Government Targeted in Blatant Iranian-Nexus Cyberespionage appeared first on Daily CyberSecurity.
Visualização de leitura
Ransom & Dark Web Issues Week 1, May 2026
Canvas Breach May Put 275M Users, 9,000 Schools at Risk
Instructure confirms a Canvas breach involving user information and messages as hackers claim 275M users and nearly 9,000 schools were affected.
The post Canvas Breach May Put 275M Users, 9,000 Schools at Risk appeared first on TechRepublic.
Carding service Jerry’s Store leak exposes 345,000 stolen payment cards
Jerry’s Store, a card-checking service used by cybercriminals, exposed 345,000 stolen payment cards after leaving its server open, revealing sensitive data.
A cybercriminal operation known as Jerry’s Store has reportedly exposed a large cache of stolen payment card data after leaving its own infrastructure accessible online. The service appears to have been used to test whether stolen credit and debit card details were still valid, effectively acting as a verification tool for fraudsters before the data was resold or abused.
“Jerry’s Store marketplace leaked 345,000 stolen credit card details through an exposed, insecurely configured server created using AI assistance.” reads the report published by CyberNews.
“The leak occurred after Cursor AI generated flawed code without authentication, exposing credit card numbers, names, addresses, and security codes.”
Researchers found that the exposed server contained information linked to roughly 345,000 payment cards. Of those, nearly 200,000 cards had been marked as invalid by the service, while more than 145,000 records were identified as valid. The leaked records reportedly included highly sensitive cardholder data such as card numbers, expiration dates, security codes, names, and billing addresses. Cybernews
The incident is notable not only because of the volume of exposed data, but also because it shows how organized and automated parts of the carding economy have become. Instead of manually checking stolen cards one by one, criminal marketplaces and fraud services increasingly rely on infrastructure that can validate payment data at scale. Once a card is confirmed as active, it becomes more valuable for resale, fraud attempts, or account takeover activity.
Cybernews estimated that valid stolen card records typically sell for around $7 to $18 on dark web markets. Using that range, the valid card data exposed through Jerry’s Store could be worth between $1 million and $2.6 million. The true value of the broader operation may be higher, since the platform reportedly handled more than just the leaked payment-card records.
CyberNews researchers found that Jerry’s Store operators used Cursor, an AI coding tool by Anysphere, to build their server and admin dashboards. However, flawed guidance from the AI likely led to misconfigurations, leaving the system exposed and causing the data leak.
“We were able to confirm that the leak originated from the user asking to create a statistics dashboard, and Cursor created an unauthenticated open web directory to serve the webpage, ignoring the need to set up authentication or ensure that only the intended dashboard would be accessible,” CyberNews team explained.


The case is ironic: a cybercriminal service built to profit from stolen card data exposed itself due to poor security. This failure creates added risk for victims, as data already circulating in underground markets can spread further, reaching new attackers who did not originally steal it.
The story also highlights a wider trend in cybercrime: illicit services are becoming more productized. Carding shops, validation tools, automated fraud services, and dark web marketplaces increasingly resemble commercial platforms, with pricing models, customer interfaces, and backend infrastructure. Rapid7 has described this broader ecosystem as “carding-as-a-service,” where stolen cards and fraud tooling are packaged for easier use by criminals with varying levels of technical skill.
A similar pattern has been seen in other carding-related incidents. BidenCash, a carding-focused marketplace, became known for releasing large batches of stolen payment-card data as a promotional tactic to attract users and vendors.
Law enforcement has also targeted related ecosystems. In a case involving B1ack’s Stash, authorities seized domains tied to underground vendors trafficking stolen financial data, including payment-card records. That case underlines how carding markets remain a priority for investigators because they support a chain of downstream crimes, from unauthorized purchases to identity theft and money laundering.
Consumers should closely monitor accounts, enable alerts, use virtual cards, and replace compromised ones. Banks must strengthen fraud detection, quickly block stolen cards, and monitor underground markets.
The Jerry’s Store leak shows that even cybercriminal platforms can have weak security. When they fail, the impact still hits ordinary users, whose stolen card data may spread further and be reused, traded, and exploited across the fraud ecosystem.
Follow me on Twitter: @securityaffairs and Facebook and Mastodon
(SecurityAffairs – hacking, Jerry’s Store)
Vimeo Data Exposed in Anodot Supply Chain Attack
The post Vimeo Data Exposed in Anodot Supply Chain Attack appeared first on Daily CyberSecurity.
Ransom & Dark Web Issues Week 5, April 2026
French Police Arrest HexDex Hacker Over Mass Data Theft and Leaks
RAMP Uncovered: Anatomy of Russia’s Ransomware Marketplace
Leaked data from RAMP reveals Russia’s ransomware ecosystem, analyzing 1,732 threads, 7,707 users, and 340,000 IP records from the forum.
RAMP was not just another dark web forum. It was one of the clearest examples of how ransomware has become an organized marketplace, with sellers, buyers, brokers, and recruiters all playing different roles in the same criminal ecosystem.
A leaked database from RAMP gives us a rare look behind the curtain. It shows how cybercrime works when it becomes structured, commercial, and repeatable. Instead of random hackers acting alone, RAMP functioned like a business platform where criminals could sell access, recruit affiliates, advertise ransomware, and negotiate deals in private.
What the leak exposed
The leaked data covers activity from November 2021 to January 2024 and includes user records, forum threads, private messages, IP logs, and admin activity. That matters because it shows both the public side of the forum and the hidden conversations that helped turn forum posts into real attacks.
“Comparitech gained exclusive access to a leaked database from RAMP. The full MySQL dump contains user records, forum threads, private messages, IP logs, and admin activity spanning November 2021 through January 2024.” reads the analysis published by Comparitech.
The scale is significant. Comparitech’s analysis found 7,707 registered users, 1,732 forum threads, 340,333 IP log records, 1,899 private conversations, and 3,875 private messages. In other words, this was not a small corner of the internet. It was a large criminal marketplace with a lot of movement and a lot of participants.
RAMP in numbers
| Metric | Figure |
|---|---|
| Registered users | 7,707 |
| Forum threads | 1,732 |
| IP log records | 340,333 |
| Private conversations | 1,899 |
| Private messages | 3,875 |
| RaaS programs advertised | 14 |
| Leak sites referenced | 250+ |
These numbers show a mature underground community, not a loose collection of opportunists.
Why RAMP mattered
RAMP became popular because it supported the full ransomware chain. That means it was not only a place to talk about attacks. It was a place to buy access, find partners, exchange tools, and recruit affiliates.
The forum’s access market was especially important. The database shows 333 threads offering access to compromised corporate networks. That is a big deal, because initial access is often the hardest part of a ransomware operation. Once criminals get inside a network, the rest of the attack becomes much easier.
The forum also hosted 60 threads in its ransomware-as-a-service section. That section revealed a growing trend toward generous profit splits, with affiliates getting up to 90% of ransom payments in some cases. That kind of arrangement helps explain why ransomware keeps attracting new actors. It is a criminal business model designed to scale.
What was being sold
| Category | What it tells us |
|---|---|
| Access listings | Criminals were selling entry into real corporate networks |
| RaaS recruitment | Operators were hiring affiliates to spread attacks |
| Private messages | Deals were negotiated behind the scenes |
| IP logs | Activity was tracked and monitored at scale |
This mix of public listings and private negotiations shows how ransomware markets move from advertisement to execution.
Targets and sectors
The leak also shows what kinds of organizations were being targeted. RAMP listings included defense contractors, banks, hospitals, energy companies, technology firms, and government agencies across more than 20 countries.
The United States was the top target. It appeared in 40% of listings where a country could be identified. Government agencies were the most targeted sector, with 21 listings, followed by finance and banking, and technology and telecom, each with 11 listings.
That pattern is important. It shows that ransomware actors are not just chasing easy victims. They are targeting organizations that are likely to be pressured into paying because they cannot afford downtime, data loss, or public exposure.
The hidden layer
The most revealing part of the leak may be the private conversations. The database included 1,899 conversations and 3,875 messages. These messages covered topics like VPN access, stealer logs, and private RaaS partnership requests.
That hidden layer matters because public forum posts do not tell the whole story. A public listing can advertise access, but a private conversation is where the real business happens. This is where criminals confirm details, negotiate price, and decide whether a listing is worth moving forward.
The leaked data also suggests that a single access broker posted 41 separate listings. That suggests some actors were operating like wholesalers, moving multiple entry points into corporate networks rather than focusing on just one victim.
Why this matters today
RAMP helps explain why ransomware remains such a serious threat. The forum made it easier for criminals to specialize. One person could steal access, another could sell malware, and another could launch the final attack. That division of labor makes ransomware faster, cheaper, and harder to stop.
It also shows why law enforcement pressure does not automatically end the problem. Even when a major forum is disrupted, the ecosystem can fragment and move elsewhere. Criminal markets often adapt rather than disappear.
In practice, this means defenders need to think beyond malware alone. They need to monitor stolen credentials, exposed remote access, suspicious logins, and signs of initial access being sold or traded. The earliest stage of the attack chain is often the most important one to catch.
What organizations should learn
The RAMP leak reinforces a simple lesson: ransomware is an ecosystem, not just a piece of malware. If attackers can buy access, recruit help, and sell stolen access in one place, then defenders need to protect every stage of the environment, from identity to endpoint to remote access.
Organizations should focus on a few practical controls:
- reduce exposed services and external access paths,
- enforce MFA everywhere possible,
- detect unusual login behavior,
- monitor dark web exposure for corporate credentials,
- and improve incident response before an attack happens.
The leaked database is valuable because it shows the real machinery behind ransomware. It is not just about encryption at the end of an attack. It is about the marketplace that makes the attack possible in the first place.
“This analysis is based on a MySQL database dump of the RAMP forum’s XenForo installation. We parsed raw SQL to extract structured data from the xf_user (7,707 records), xf_thread (1,732 records), xf_post, xf_ip (340,333 records), xf_admin_log, xf_conversation_master (1,899 records), and xf_conversation_message (3,875 records) tables.” concludes the analysis. “IP addresses were decoded from binary format and geolocated against known ISP allocations. All findings are based on data as it existed in the database dump and have not been independently verified against live sources.”
Follow me on Twitter: @securityaffairs and Facebook and Mastodon
(SecurityAffairs – hacking, data leak)
Ransom & Dark Web Issues Week 4, April 2026
Threat Landscape March 2026: Ransomware Dominance, Access Brokers, Data Leaks, and Critical Exploitation Trends

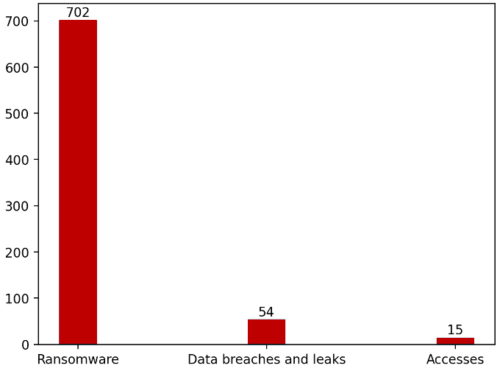
Cyble Research & Intelligence Labs (CRIL) in its monthly threat landscape analysis observed a highly active threat environment throughout March 2026, shaped by large-scale ransomware campaigns, persistent data breach activity, growing initial access brokerage markets, and exploitation of critical vulnerabilities affecting widely deployed enterprise systems.
Threat actors continued to prioritize financial extortion, credential access, and operational disruption, while increasingly targeting sectors rich in sensitive data or dependent on business continuity.
Quick Summary
Key threat trends identified during March 2026 include:
- 702 ransomware attacks recorded globally.
- 54 major data breach and leak incidents observed.
- 20 compromised access sale listings tracked across cybercrime forums.
- High concentration of attacks against Professional Services, Manufacturing, Retail, and Government sectors.
- Continued exploitation of vulnerabilities listed in CISA’s Known Exploited Vulnerabilities (KEV) catalog.
These trends indicate a mature cybercriminal ecosystem where access brokers, ransomware operators, and data leak actors increasingly operate in parallel.
Ransomware Activity Remained the Dominant Threat
CRIL recorded 702 ransomware attacks worldwide in March 2026, reflecting sustained aggression from both established groups and emerging operators.
Top Ransomware Groups
Qilin, Akira, The Gentlemen, Dragonforce, and INC Ransom were the top five most active ransomware actors in March 2026.
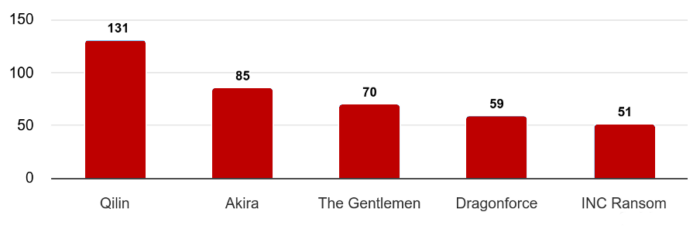
Together, the top five groups accounted for more than 56% of observed ransomware activity, highlighting strong operational scale and affiliate ecosystems.
Most Targeted Industries
Construction, Professional Services, Manufacturing, Healthcare, and Energy & Utilities were the most targeted sectors by ransomware actors in March 2026.
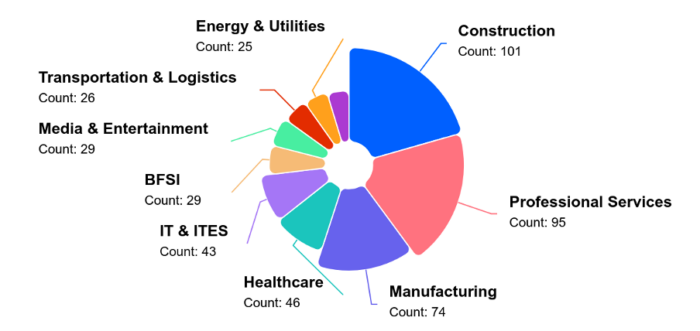
Threat actors continued using data theft + operational disruption as dual-extortion pressure tactics.
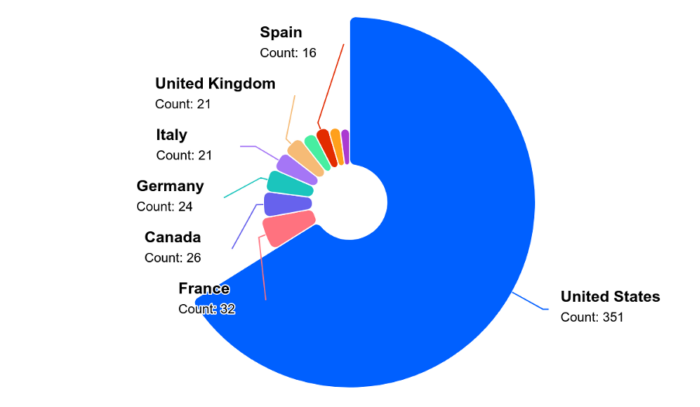
And when it came to country-wise split-up, the United States remained the focal point amid the ongoing geopolitical issues with Iran.
Compromised Access Market Expanded
CRIL tracked 20 distinct incidents involving the sale of unauthorized network access on underground forums.
Most Targeted Sectors
- Professional Services – 25%
- Retail – 20%
- IT & ITES
- Manufacturing
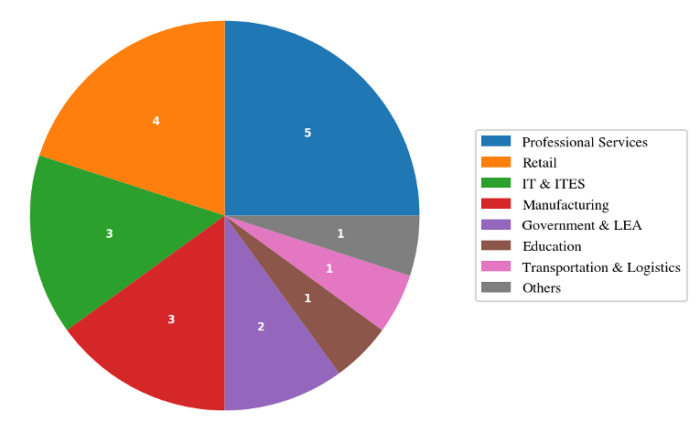
Leading Access Sellers
A small group of actors dominated this market:
- vexin
- holyduxy
- algoyim
These three actors were responsible for over 55% of observed access listings.
This reinforces the role of access brokers as upstream enablers for ransomware, espionage, and fraud operations.
Data Breaches and Leak Markets Remained Active
CRIL observed 54 significant breach and leak incidents during the month.
Most Targeted Sectors
- Government & Law Enforcement
- Retail
- Technology
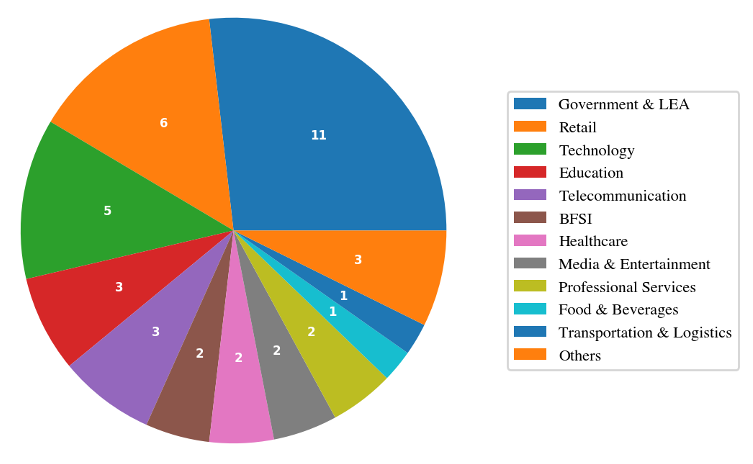
Notable Incidents
Hospitality Holdings – TA Claimed 5TB Leak
Threat actor “nightly” claimed theft of over 5TB of data, including biometric records, CCTV footage, and financial documents.
South African Government Dataset for Sale
Threat actor XP95 advertised 3.8TB of allegedly stolen provincial government data.
Travel Data Leak
Over 95,000 travel-related records were reportedly exposed, including passports and payment data.
Exploited Vulnerabilities Accelerated Risk
March also saw active exploitation of critical vulnerabilities affecting enterprise technologies.
Notable KEV-listed vulnerabilities included:
- CVE-2026-20131 – Cisco Secure Firewall Management Center
- CVE-2025-53521 – F5 BIG-IP APM
- CVE-2026-20963 – Microsoft SharePoint Server
- CVE-2026-33017 – Langflow AI
- CVE-2021-22681 – Rockwell Automation ICS
Key Trend
Attackers exploited both:
- Newly disclosed zero-days
- Legacy vulnerabilities from prior years
This showcases widespread failures in patch management and exposure reduction.
Emerging Strategic Threat Developments
AI-Augmented Offensive Operations
Threat actors reportedly used CyberStrikeAI, an open-source AI-native security testing framework, in attacks against Fortinet FortiGate devices across 55 countries, compromising more than 600 appliances.
Supply Chain Malware via npm
North Korean actors were linked to 26 malicious npm packages distributing RAT malware through Pastebin/Vercel-based infrastructure.
Geopolitical Cyber Risk
Iran-linked cyber operations were assessed as likely to increase following regional tensions, with potential ransomware and hacktivist targeting across the Middle East.
Industries Facing Highest Risk
Based on March activity, organizations in the following sectors faced elevated risk:
- Professional Services
- Government
- Manufacturing
- Retail
- Healthcare
- Critical Infrastructure
- Transportation & Logistics
These sectors combine valuable data, high uptime requirements, or complex supply chains.
Conclusion
The March 2026 threat landscape was defined by scale, specialization, and speed.
Threat actors increasingly leveraged:
- Access brokerage markets
- High-volume ransomware operations
- Large-scale data theft
- Rapid weaponization of critical vulnerabilities
- AI-enhanced offensive tooling
The combination of concentrated criminal ecosystems and widespread enterprise exposure creates a sustained high-risk environment for organizations globally.
Key Recommendations
- Prioritize remediation of KEV-listed vulnerabilities
- Strengthen identity security and MFA across remote access platforms
- Monitor for exposed credentials and access sale activity
- Segment critical networks to reduce lateral movement
- Conduct tabletop exercises for ransomware response
- Improve backup resilience and recovery testing
- Monitor software supply chain ecosystems
- Expand threat intelligence coverage across dark web and leak forums
Cyble’s threat intelligence, ransomware monitoring, vulnerability intelligence, and attack surface management solutions help organizations proactively identify risks, prioritize remediation, and defend against evolving global threats.
Book your demo now to see it in action!!!
The post Threat Landscape March 2026: Ransomware Dominance, Access Brokers, Data Leaks, and Critical Exploitation Trends appeared first on Cyble.
Public Notion Pages Leaks Profile Photos and Email address of Editors
Notion, a popular productivity and collaboration platform, is under significant scrutiny from the cybersecurity community.
Security researchers have revealed that public Notion pages silently expose the personally identifiable information (PII) of anyone who has ever edited them.
This data leak includes full names, email addresses, and profile photos, raising significant privacy concerns for organizations that rely on the platform for public documentation.
Notion Pages Exposes User Data
The underlying vulnerability stems from how Notion processes user data within public workspaces.
When a document is published to the web, the platform embeds editor UUIDs (Universally Unique Identifiers) directly into the page’s block permissions.
Threat actors and open-source intelligence (OSINT) researchers discovered that these internal identifiers are readily accessible in the page data without requiring any authentication, active session cookies, or security tokens.
Once these UUIDs are harvested, an attacker can feed them into a single unauthenticated POST request to Notion’s internal API endpoint: /api/v3/syncRecordValuesMain.
Because this endpoint does not enforce access controls for public page data, it returns the complete user profiles associated with those UUIDs.
every public Notion page is leaking the email addresses of everyone who edited it.
— impulsive (@weezerOSINT) April 19, 2026
zero authentication. no cookies. no tokens. one POST request returns full names, emails, and profile photos for every editor on the page.
your company wiki is public? every employee's email is… pic.twitter.com/jqWSCVBoyH
Consequently, a public company wiki or open-source project board can inadvertently expose the exact contact details of every employee or contributor who interacts with the document.
The most controversial aspect of this exposure is its long, unresolved timeline. According to security researchers, this exact API behavior was responsibly disclosed to Notion through the HackerOne bug bounty program in July 2022.
At the time, Notion’s security team triaged the submission as merely “informative”. It closed the report as out of scope without implementing a structural patch.
The issue recently resurfaced on X, sparking outrage among developers and cybersecurity professionals. Many paying subscribers expressed extreme frustration with the platform’s perceived negligence, noting that an issue ignored for nearly 4 years leaves thousands of indexable pages vulnerable to scraping.
Security experts emphasized that this exposed data creates a massive attack surface for targeted phishing campaigns and social engineering attacks against corporate targets.
Official Response and Proposed Mitigations
Following the intense public backlash, Notion has formally acknowledged the problem. Notion representative Max Schoening addressed the community’s concerns, noting that the platform provides user warnings about data visibility when a page is published to the web.
However, recognizing that this design choice poses unacceptable security risks, Notion is now working on a permanent architectural fix.
The engineering team plans to either strip PII completely from public-facing endpoints or implement an email proxy system to mask user addresses.
In the meantime, organizations using Notion for public-facing resources should remain vigilant, as their employee contact information may already be indexed and accessible to automated scraping tools.
Follow us on Google News, LinkedIn, and X for daily cybersecurity updates. Contact us to feature your stories.
The post Public Notion Pages Leaks Profile Photos and Email address of Editors appeared first on Cyber Security News.

Smashing Security podcast #463: This AI company leaked its own code. It’s also built something terrifying
Capsule Security Emerges From Stealth to Secure AI Agents at Runtime

Capsule Security emerges from stealth with a $7M seed round to launch a runtime security platform for AI agents. Featuring the open-source ClawGuard, the platform enforces governance and mitigates prompt injection risks like ShareLeak and PipeLeak without requiring SDKs or proxies.
The post Capsule Security Emerges From Stealth to Secure AI Agents at Runtime appeared first on Security Boulevard.
March 2026 Dark Web Issue Trends Report
Massive Data Breach Exposes 337K LAPD-Linked Records
A massive breach exposed 337K LAPD-linked files, raising concerns over third-party risk, sensitive data exposure, and law enforcement cybersecurity gaps.
The post Massive Data Breach Exposes 337K LAPD-Linked Records appeared first on TechRepublic.
A Compromised Tool Opened the Door to a 91GB European Commission Data Leak
European Commission Cloud Breach Traced to Compromised Trivy Tool
Investigators from CERT-EU say, with high confidence, that the European Commission cloud breach began with a supply-chain compromise involving Trivy, a widely used security scanning tool. The malicious version, attributed to a threat actor known as TeamPCP, was unknowingly used within the Commission’s environment after being delivered through standard update channels. On March 19, the attacker obtained an AWS secret, an API key—with management-level permissions. That single key became the gateway into the Commission’s cloud infrastructure. From there, the activity was deliberate. The attacker attempted to uncover more credentials using TruffleHog, a tool designed to scan for secrets and validate access through AWS Security Token Service (STS). They also created a new access key tied to an existing user, an attempt to maintain access while avoiding detection. The European Commission cloud breach did not rely on breaking in. It relied on blending in.Data Theft and Dark Web Leak
The impact became clearer days later. A large volume of data, around 91.7 GB compressed, or roughly 340 GB uncompressed—was exfiltrated from the compromised AWS account. On March 28, the data extortion group ShinyHunters published the dataset on its dark web leak site. The group claimed it included “data dumps of mail servers, datavases [sic], confidential documents, contracts, and much more sensitive material”. Early analysis confirms that the European Commission cloud breach exposed personal data, including names, usernames, and email addresses. The dataset also contains more than 51,000 files linked to outbound email communications. While most of these emails are automated notifications, some “bounce-back” messages may include original user-submitted content. That detail matters, as it raises the risk of unintended personal data exposure across systems that rely on user interaction.Wider Impact Across EU Entities
The European Commission cloud breach goes beyond a single institution. The compromised AWS account is part of the infrastructure behind the “europa.eu” web hosting platform, which supports dozens of websites. Data linked to up to 71 clients may be affected, 42 internal European Commission services and at least 29 other Union entities. This shared infrastructure model is efficient, but it also means that one compromised component can have a broader footprint. Despite this, officials have confirmed that no websites were defaced, taken offline, or altered during the incident. There were no service disruptions. But the absence of visible damage should not be mistaken for limited impact.Timeline Shows Speed of Supply-Chain Attacks
The timeline of the European Commission cloud breach highlights how quickly such incidents can unfold:- March 19: AWS credential obtained via compromised Trivy tool
- March 24: Alerts triggered over unusual API activity and traffic spikes
- March 25: CERT-EU notified; access secured and keys revoked
- March 27: Public disclosure by the European Commission
- March 28: Data published by ShinyHunters