Kaspersky found Coruna iOS exploits reuse updated code from the 2023 Operation Triangulation attacks, suggesting a possible link.
Kaspersky researchers discovered that the Coruna iOS exploit kit uses an updated version of the same kernel exploit seen in the 2023 Operation Triangulation campaign. While early evidence didn’t clearly link the two, the code similarities now suggest a possible connection between them, though shared vulnerabilities alone don’t definitively prove the same actors are behind both attacks.
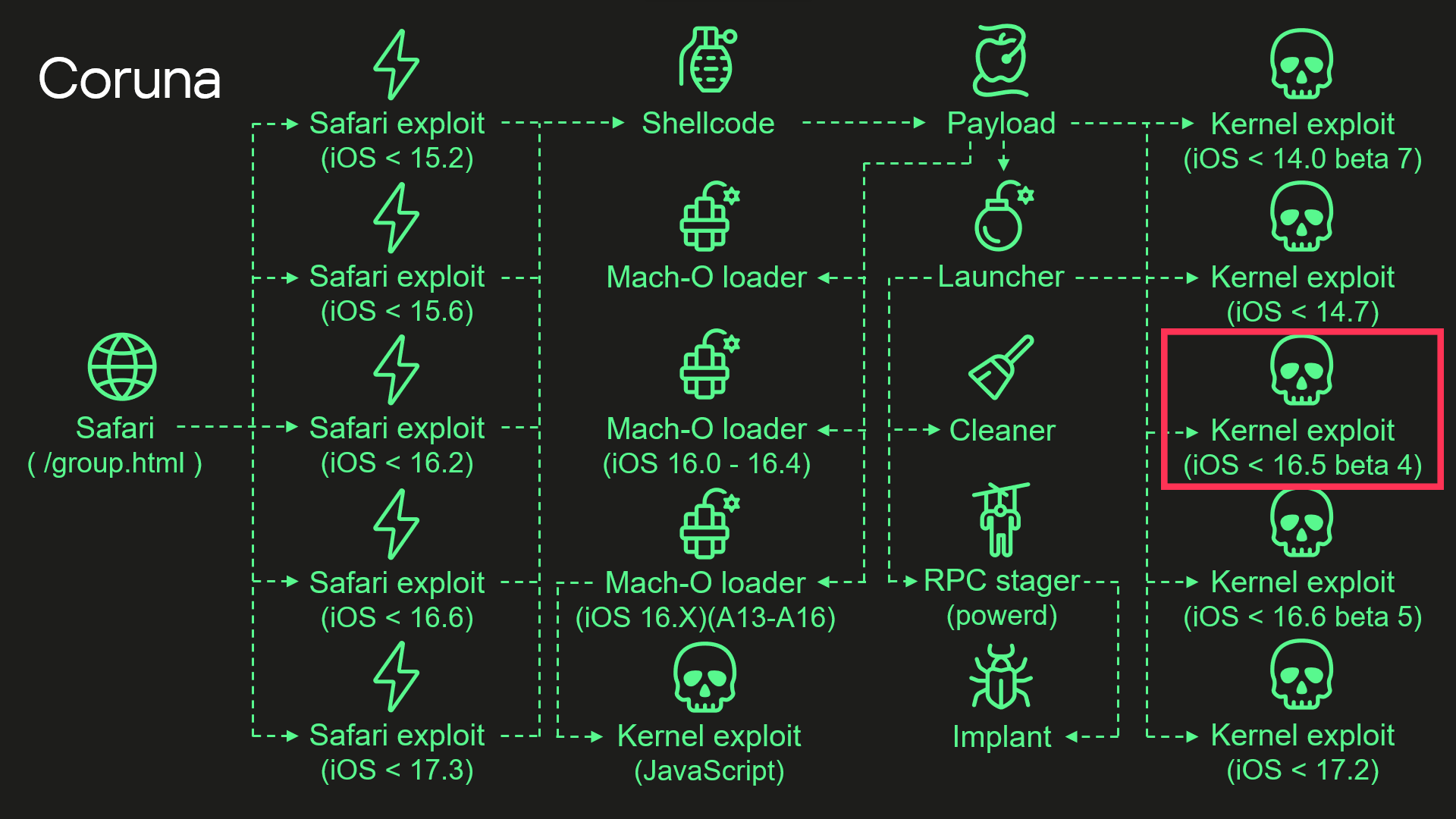
In early March, Google’s Threat Intelligence Group identified a powerful new iOS exploit kit called Coruna (also known as CryptoWaters) that targets Apple iPhones running iOS versions 13.0 through 17.2.1. The kit includes five full exploit chains and a total of 23 exploits.
While highly capable against iPhones running iOS 13.0 through 17.2.1versions, Coruna is ineffective against the latest iOS release, according to Google.
GTIG tracked the use of the exploit in highly targeted attacks by a surveillance vendor’s customer, in Ukrainian watering hole campaigns by UNC6353, and later in broad-scale attacks by Chinese financial threat actor UNC6691, showing an active market for “second-hand” zero-day exploits. Multiple threat actors now reuse and adapt these advanced techniques for new vulnerabilities.
Initial discovery occurred in February 2025 when GTIG captured a previously unseen JavaScript framework delivering an iOS exploit chain from a surveillance vendor’s customer.
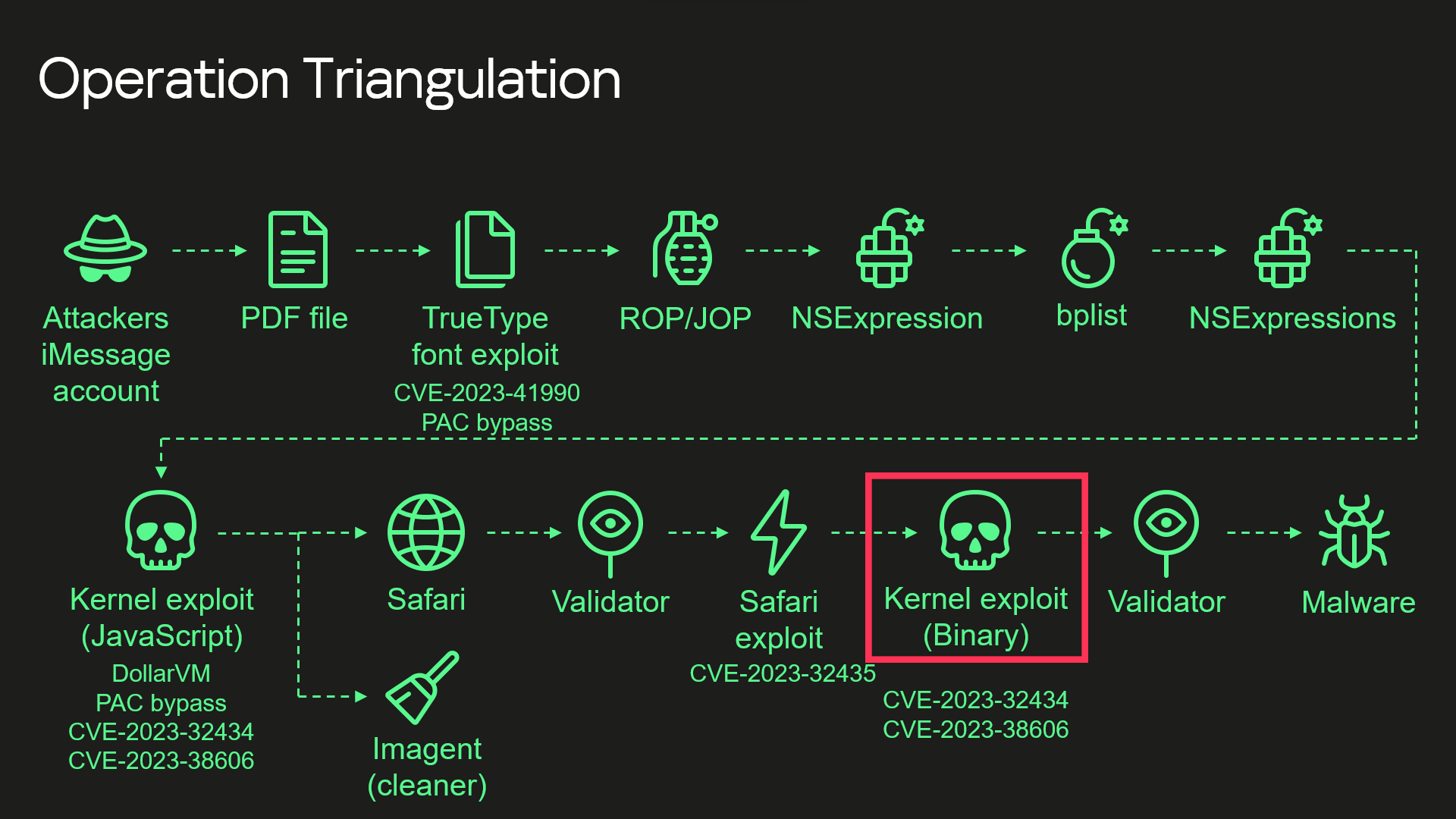
Analysis shows the Coruna exploit kit uses several patched vulnerabilities, including CVE-2023-32434 and CVE-2023-38606, two flaws first seen as zero-days in the Operation Triangulation iOS campaign. While details of these bugs are now public, Kaspersky found Coruna’s kernel exploit is an updated version of the one used in that earlier attack.
Researchers were able to collect and analyze Coruna components, confirming strong code similarities. The kit also includes four additional kernel exploits, some developed after Triangulation, all built on the same framework.
These findings suggest Coruna is not a mix of reused parts but a more advanced evolution of the same exploitation framework behind Operation Triangulation.
“These findings led us to conclude that this exploit kit was not patchworked but rather designed with a unified approach.” reads the report published by Kaspersky. “We assume that it’s an updated version of the same exploitation framework that was used — at least to some extent — in Operation Triangulation.”
The Coruna exploit chain starts with a Safari-based stager that identifies the target device and selects suitable exploits based on browser version. It includes a link and key to download encrypted components.
The payload then decrypts and processes multiple layers of data using ChaCha20 and LZMA compression, revealing structured containers that store files and instructions. These define which exploits, loaders, and malware components to fetch, depending on device type, CPU, and iOS version.
Coruna supports multiple package types, including kernel exploits, loaders, and implants, tailored for different architectures and firmware versions. Once all components are retrieved, the payload executes kernel exploits, loads malware, and launches the attack, adapting dynamically to the target environment for maximum effectiveness.
Researchers analyzed five kernel exploits in Coruna and found one is an updated version of the exploit used in Operation Triangulation. The newer code improves compatibility by checking more XNU version details, supporting newer iOS versions (up to 17.2), and recognizing recent Apple chips like A17 and M3. Although the original vulnerabilities were patched earlier, these checks were added to support newer exploits built on the same shared framework.
“Why does the exploit need to check for iOS 17.2 and newer CPUs if the targeted vulnerabilities were fixed in iOS 16.5 beta 4? The answer can be found by examining other exploits: they are all based on the same source code.” continues the report. “The only difference is in the vulnerabilities they exploit, so these checks were added to support the newer exploits and appeared in the older version after recompilation.”
The launcher handles post-exploitation tasks. Instead of re-running the exploit, it reuses existing kernel access created earlier to read and write memory. It removes traces of the attack, selects a target process, injects a stager, and executes it to deploy the final malware. This streamlined approach makes the attack more efficient and stealthy once initial access is gained.
“Originally developed for cyber-espionage purposes, this framework is now being used by cybercriminals of a broader kind, placing millions of users with unpatched devices at risk.” concludes the report. “Given its modular design and ease of reuse, we expect that other threat actors will begin incorporating it into their attacks. We strongly recommend that users install the latest security updates as soon as possible, if they have not already done so.”
In mid-March, Lookout Threat Labs discovered a new iOS exploit kit called DarkSword that has been used since late 2025 by multiple threat actors, including surveillance vendors and likely nation-state actors. The toolkit enables full-chain attacks to steal sensitive data from Apple devices and has been observed in campaigns targeting countries such as Saudi Arabia, Turkey, Malaysia, and Ukraine.
DarkSword targets iPhones running iOS 18.4–18.7 and has been used by the suspected Russian-linked group UNC6353 against Ukrainian targets. It allows attackers to steal sensitive data, including credentials and crypto wallet information, then quickly exfiltrates it in a “hit-and-run” approach before cleaning traces.
The exploits appear to be linked to Coruna exploits, DarkSword enables near full device access with minimal user interaction, showing how advanced exploits are now available on a secondary market to a wider range of threat actors.
Follow me on Twitter: @securityaffairs and Facebook and Mastodon
(SecurityAffairs – hacking, Coruna)