Visualização de leitura
Decoding Q1 2026’s $152.9 Billion Crypto Custody Concentration
Stablecoins: Always-On Money Needs Always-On Controls
The Role of Aggregated Liquidity in Modern Crypto Markets
North Korea’s Lazarus APT stole $290M from Kelp DAO
North Korea-linked Lazarus Group stole $290M from Kelp DAO by abusing LayerZero. A second $95M attempt was stopped.
Hackers tied to the North-Korea linked group Lazarus APT carried out a $290M crypto theft targeting Kelp DAO.
Earlier today we identified suspicious cross-chain activity involving rsETH. We have paused rsETH contracts across mainnet and several L2s while we investigate.
— Kelp (@KelpDAO) April 18, 2026
We are working with @LayerZero_Core, @unichain, our auditors and top security experts on RCA.
We will keep you…
Kelp DAO is a decentralized finance (DeFi) protocol built on the Ethereum ecosystem that focuses on a concept called liquid restaking.
Attackers manipulated LayerZero infrastructure, forcing systems to rely on compromised nodes, then issued a malicious command to drain funds.
This is one of the biggest DeFi hacks of 2026
— StarPlatinum (@StarPlatinum_) April 18, 2026
Here’s what just happened:
Kelp DAO’s rsETH bridge got exploited through LayerZero.
Around 116,500 rsETH was drained.
That’s $293M gone in minutes.
Main drain transaction:… pic.twitter.com/9ZfHqUUsWN
After the breach, the platform froze activity and blocked wallets, stopping a second attempted theft worth about $95M.
“Kelp detected the anomaly, paused all relevant contracts on Ethereum mainnet and L2s, blacklisted all wallets associated with the exploiter, and engaged SEAL-911.” wrote Kelp. “A subsequent attempt by the exploiter, leveraging a falsely verified phantom packet to target an additional 40,000 rsETH (~$95M), was fully mitigated by these interventions.”
Kelp DAO lets users deposit ETH, restake it via EigenLayer, and receive rsETH to earn extra rewards. It relies on LayerZero to verify transactions across chains. The attack didn’t exploit the core protocol but targeted the verification layer.
LayerZero checks transactions using multiple servers (RPCs). Attackers hacked two of them and used them to send fake but valid-looking messages.
“On April 18, 2026, LayerZero Labs’ DVN became the target of a highly sophisticated attack, likely attributable to the Lazarus Group, more specifically TraderTraitor. The attack was specifically engineered to manipulate or poison downstream RPC infrastructure by compromising a quorum of the RPCs the LayerZero Labs DVN relied upon to verify transactions. It was not done through an exploit to the protocol, DVN, key management or other means.” reports LayerZero. “Rather, the attacker was able to gain access to the list of RPCs our DVN uses, compromise two of them – which were independent nodes running on separate clusters without direct connection to each other – and swap out binaries running the op-geth nodes. Because of our least-privilege principles, they were unable to compromise the actual DVN instances. However, they used this pivot point to execute an RPC-spoofing attack.”
Then they launched a DDoS attack on the remaining servers, forcing the system to rely on the compromised ones. This allowed malicious transactions to pass. The root cause was Kelp DAO’s insecure “1-of-1” verifier setup, meaning only one DVN checked transactions. This created a single point of failure. Best practice requires multiple independent verifiers, which would have blocked the attack even if one node was compromised.
LayerZero reported that the breach only affected its rsETH setup and did not spread to other apps, thanks to LayerZero’s modular design.
LayerZero confirmed its infrastructure and protocol worked as designed, isolating the damage. The incident highlights a new type of state-level attack targeting off-chain components like RPCs, rather than core blockchain systems. After the breach, compromised nodes were replaced, and stronger multi-verifier configurations are now being enforced to prevent similar attacks.
LayerZero says the hack could have been avoided if Kelp DAO had used multiple verifiers (multi-DVN), the industry standard.
“Industry best practice — and LayerZero’s express recommendation to all integrators — is to configure a multi-DVN setup with diversity and redundancy. This means no single DVN should represent a unilateral point of trust or failure.” continues the LayerZero’s statement. “Operating a single-point-of-failure configuration meant there was no independent verifier to catch and reject a forged message. LayerZero and other external parties previously communicated best practices around DVN diversification to KelpDAO. Despite these recommendations, KelpDAO chose to utilize a 1/1 DVN configuration.”
Kelp DAO refused accusation, saying it followed its default setup and didn’t manage the compromised infrastructure. It’s now focused on limiting damage, with partners like Arbitrum Security Council freezing funds. The impact spread across DeFi, with Aave losing nearly $8B in value.
“Kelp’s priority is our users and preventing contagion across DeFi. We are working with all ecosystem partners to analyse the impact, rally support, and explore all avenues of mitigation.” concludes Kelp. “We are concurrently assessing the potential next steps regarding protocol unpausing, impact assessment, and the way forward, and working with Aave, LZ, and all other key stakeholders.”
Follow me on Twitter: @securityaffairs and Facebook and Mastodon
(SecurityAffairs – hacking, Lazarus APT)
Grinex crypto exchange shuts down, blames Western agencies for $13.7M breach
British Hacker Tyler Buchanan Pleads Guilty to $8M Hacking Scheme in US
Kyrgyzstan-based crypto exchange Grinex shuts down after $13.7M cyber heist, blames Western Intelligence
Grinex halted operations after a $13.7M hack, blaming Western intelligence. Stolen funds came from wallets of Russian users on the platform.
Kyrgyz crypto exchange Grinex halted operations after a threat actor stole $13.7 million in a cyber attack that the company attributes to Western intelligence agencies. The stolen funds belonged to Russian users, as the platform supported crypto-ruble transactions for businesses and individuals, raising geopolitical tensions around the incident.
Grinex is a crypto-ruble exchange serving Russian-speaking users and operating under CIS law.
The crypto exchange revealed that hackers stole over 1 billion rubles ($13.1 million) from Russian users’ crypto wallets. Grinex reported the incident to law enforcement and filed a criminal complaint where its infrastructure is located.
“Grinex, a leading crypto-ruble exchange that facilitates digital asset transactions between Russian businesses and individuals, was subjected to a large-scale cyberattack with indications of involvement by foreign intelligence agencies.” reads the press release published by the exchange. “The digital footprint and nature of the attack indicate an unprecedented level of resources and technology, accessible only to entities of hostile states.”
Early findings suggest the attack aimed to damage Russia’s financial sovereignty.
In 2025, Grinex acquired clients and infrastructure from Garantex after an international law enforcement operation led by U.S. Secret Service seized the website (“garantex[.]org”) of the sanctioned Russian crypto exchange Garantex.
In February 2025, the EU announced sanctions on Garantex for ties to sanctioned Russian banks (Sberbank, T-Bank, and Alfa-Bank), leading Tether to block its wallets.
The Kyrgyz crypto exchange helped return over 2.5 billion rubles in crypto previously frozen by Tether. The press release includes the list of wallets from which funds were stolen.
Blockchain security firm Elliptic reported that hackers moved about $15 million in USDT to other wallets, then quickly converted it into TRX or ETH to avoid the risk of Tether freezing the funds.
“These accounts have outgoing transactions totaling approximately $15 million in USDT, at around 12:00 UTC on Wednesday. These funds are then sent to further accounts on the TRON or Ethereum blockchains.” read the report published by blockchain security firm Elliptic. “This USDT was then converted to another asset, either TRX or ETH. By doing so, the thief avoided the risk of the stolen USDT being frozen by Tether.”
Follow me on Twitter: @securityaffairs and Facebook and Mastodon
(SecurityAffairs – hacking, Crypto)
Fake Ledger Live App on Apple Store Linked to $9.5M Crypto Theft
Kraken Exchange Faces Extortion After Insider Recorded System Footage
Bitcoin Depot hack leads to $3.6M Bitcoin theft via stolen credentials
Hackers breached Bitcoin Depot, stole credentials, and took about 50 BTC worth $3.6M from its wallets after a March 23 intrusion.
Hackers breached the largest US Bitcoin ATM operator, Bitcoin Depot, on March 23, stole login credentials, and drained about 50.9 BTC worth $3.6M from company wallets.
Bitcoin Depot told the SEC that a hacker accessed its systems and stole credentials linked to its digital asset settlement accounts, gaining control and enabling unauthorized activity.
“On March 23, 2026, Bitcoin Depot Inc. (the “Company”) discovered that an unauthorized party gained access to certain of its information technology systems. Upon detection, the Company promptly activated its incident response protocols, engaged external cybersecurity experts, and notified law enforcement. Based on the Company’s investigation to date, the unauthorized actor gained access to certain systems and obtained control of credentials associated with the Company’s digital asset settlement accounts.” reads the FORM 8-K filed with the SEC. “As a result, the unauthorized actor transferred approximately 50.903 Bitcoin from Company-controlled wallets, valued at approximately $3.665 million as of the date of this report, without authorization. The Company further believes that the incident was contained to the Company’s corporate environment and did not affect the Company’s customer platforms, divisions, systems, data or environments.”
The company continues to investigate the security breach with the help of external cybersecurity experts and works to strengthen its systems to prevent future attacks. It has not found evidence of stolen customer personal data, but the investigation is still ongoing.
The incident has not disrupted operations, but the company now considers it material due to possible legal, reputational, and response costs. It estimates a $3.665 million loss from unauthorized Bitcoin transfers, though the final impact may change. Insurance may cover part of the damage, but recovery is not guaranteed.
“The Company has recorded a preliminary estimate of loss of approximately $3.665 million, representing the fair value of the Bitcoin transferred without authorization as of the date of the incident. The ultimate impact may differ from this estimate as the investigation continues.” continues the FORM 8-K. “The Company maintains insurance coverage that may cover certain losses associated with cybersecurity incidents, but there can be no assurance that such coverage will be sufficient to recover any or all losses incurred as a result of this incident.”
This isn’t the first incident suffered by the company. In July 2025, Bitcoin Depot notified over 26,000 people about a data breach that happened in 2024. Attackers accessed company systems and stole files containing personal data.
Follow me on Twitter: @securityaffairs and Facebook and Mastodon
(SecurityAffairs – hacking, Bitcoin Depot)
New macOS Malware notnullOSX Targets Crypto Wallets Over $10K
New ClickFix Attack Uses Node.js Malware via Tor to Steal Crypto
Hackers Pose as Non-Profit Developers to Deploy Monero Mining Malware
North Korean Hackers Pose as Trading Firm to Steal $285M from Drift
24/7 Payments for 24/7 Agents: The Case for Crypto in the Machine Economy
SEC Rules – Crypto IS A Security – Sometimes

Cryptocurrency is a speculative asset, a payment system, and critical infrastructure all at once. Explore why this "Shimmer" problem creates an unstable security model where users bear 100% of the risk.
The post SEC Rules – Crypto IS A Security – Sometimes appeared first on Security Boulevard.
Fake OpenClaw Token Giveaway Targets GitHub Devs with Wallet-Draining Scam
Fake Pudgy World site steals your crypto passwords
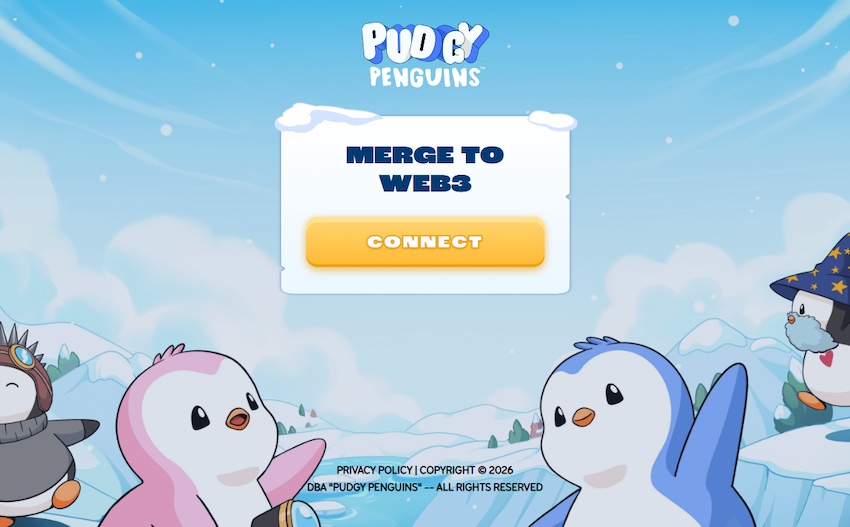
A phishing site impersonating the newly-launched Pudgy World browser game is targeting crypto users with a technique that goes well beyond a convincing logo and matching color scheme.
Pudgy World is a free-to-play browser game built around the Pudgy Penguins NFT brand. Players explore a virtual world, customize penguin avatars, and complete quests. But some features are tied to digital collectibles and in-game items stored in cryptocurrency wallets.
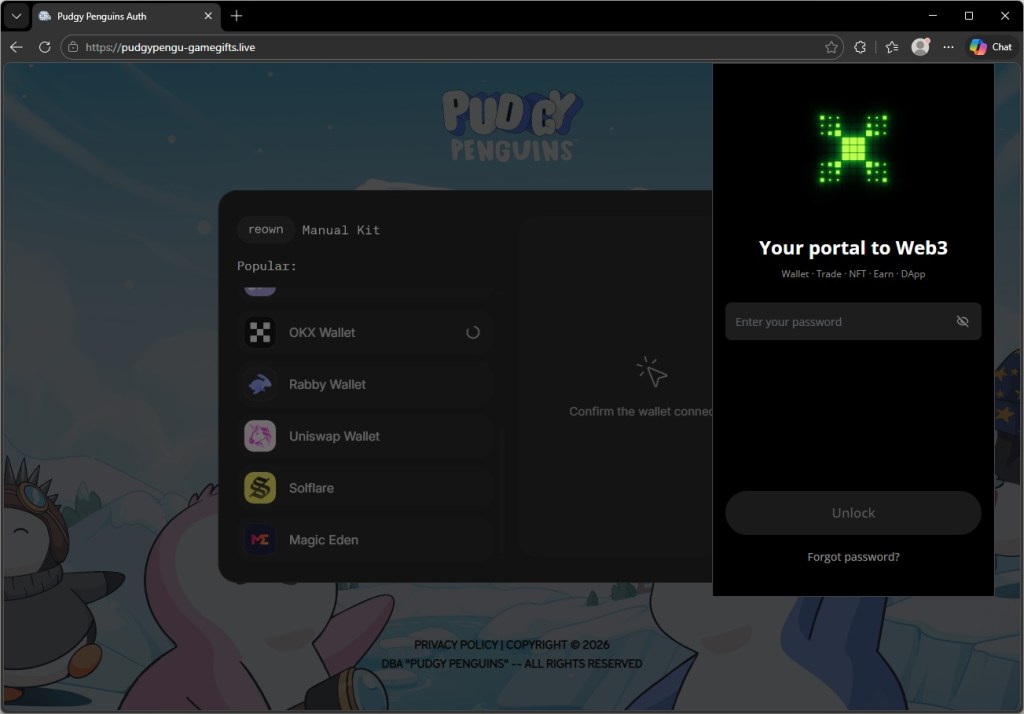
That means the official game sometimes asks players to connect a crypto wallet to verify ownership of items or unlock additional features. The phishing site abuses that step: When a visitor selects their wallet on this fake site, it shows what appears to be that wallet’s own unlock screen. To the user, it looks for all the world like the real crypto wallet software they already trust.
“Connect your wallet to get started”
The Pudgy Penguins brand has had an extraordinary few months. The penguin NFT project, revived by CEO Luca Netz after he acquired it in 2022, has steadily built one of the most convincing crossover stories in Web3: physical plush toys on Walmart and Target shelves, a mobile game called Pudgy Party that crossed a million downloads, and a browser-based game called Pudgy World that went live on 10 March 2026 to immediate viral attention.
The official game asks players to connect a crypto wallet to get started. That text: “Connect your wallet to get started” is now appearing, verbatim, on a site that has nothing to do with Pudgy Penguins.
The domain in question is pudgypengu-gamegifts[.]live. It is not affiliated with Igloo Inc., the company behind Pudgy Penguins, in any way. The site reproduces the official game’s icy background artwork, the Pudgy Penguins logo, and the brand’s characteristic blue-and-white color palette with enough fidelity that a user arriving during the excitement of a new game launch would have no obvious reason for suspicion.
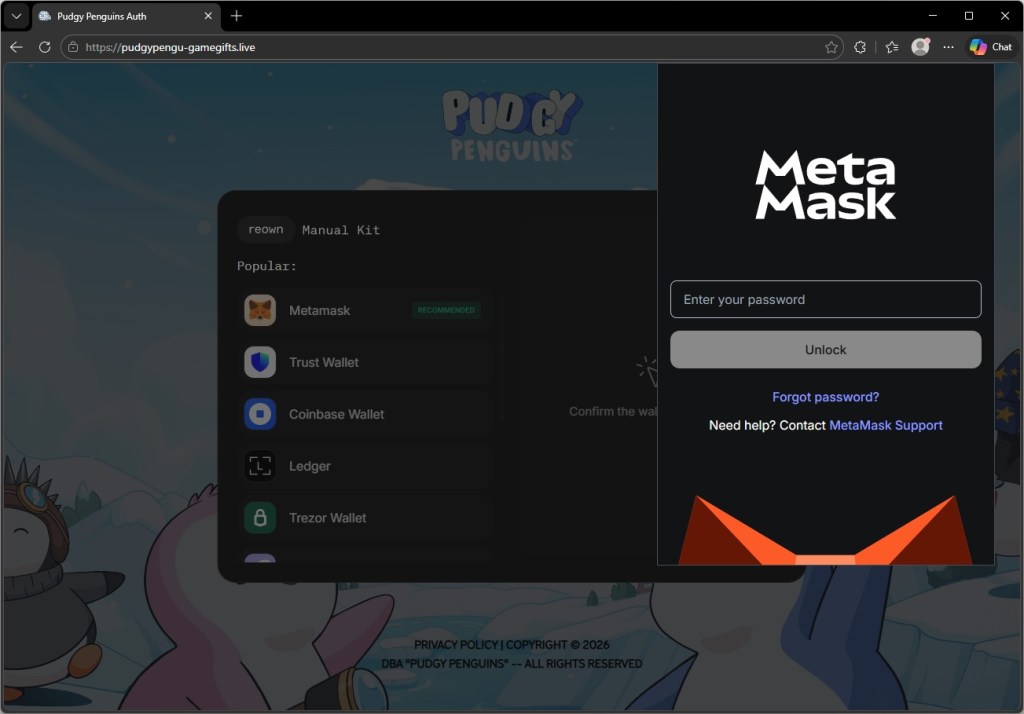
Eleven wallets, eleven convincing forgeries
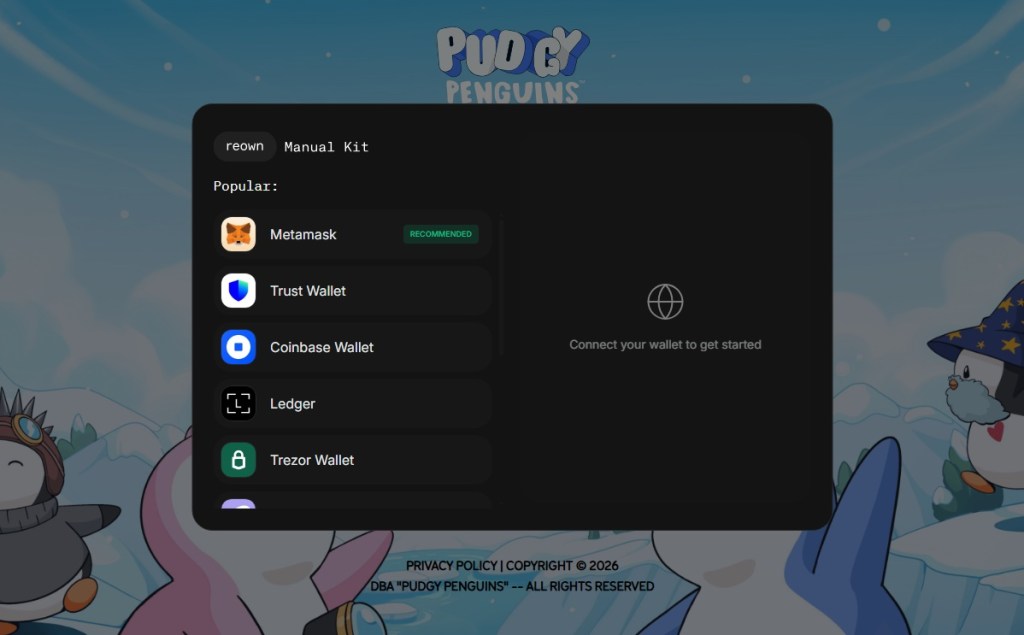
Clicking the CONNECT button opens a dark-themed pop-up window built to resemble the Reown WalletConnect connection kit—the open-source library that the real Pudgy World site uses to handle wallet connections. The modal even displays the “reown” and “Manual Kit” tab labels at the top, matching the genuine component.
Inside is a list of supported wallets:
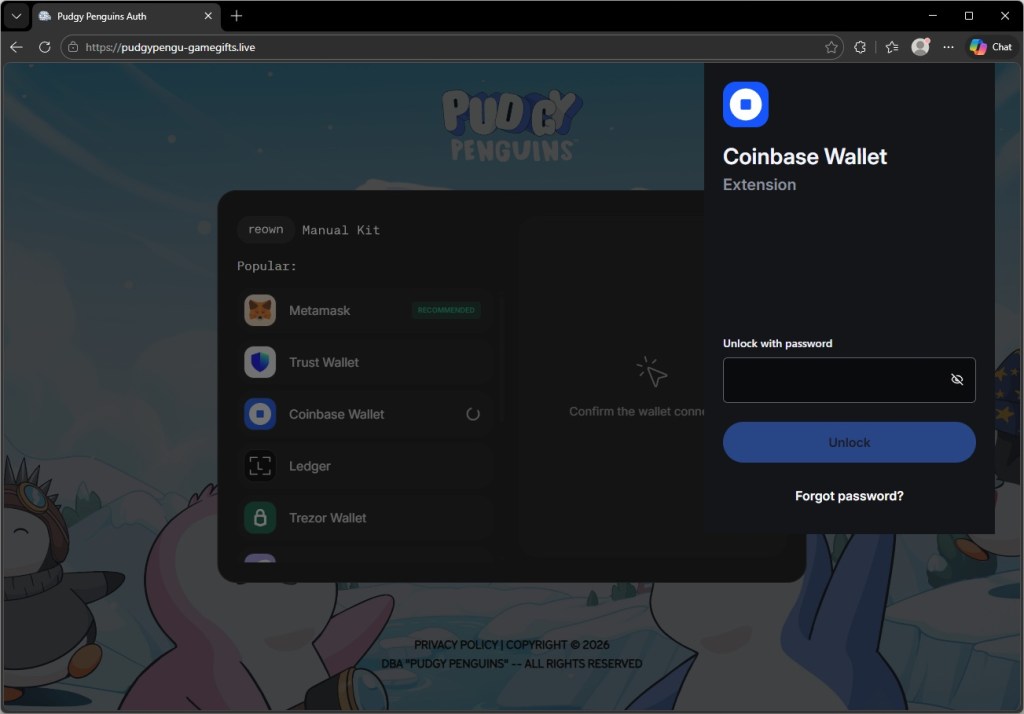
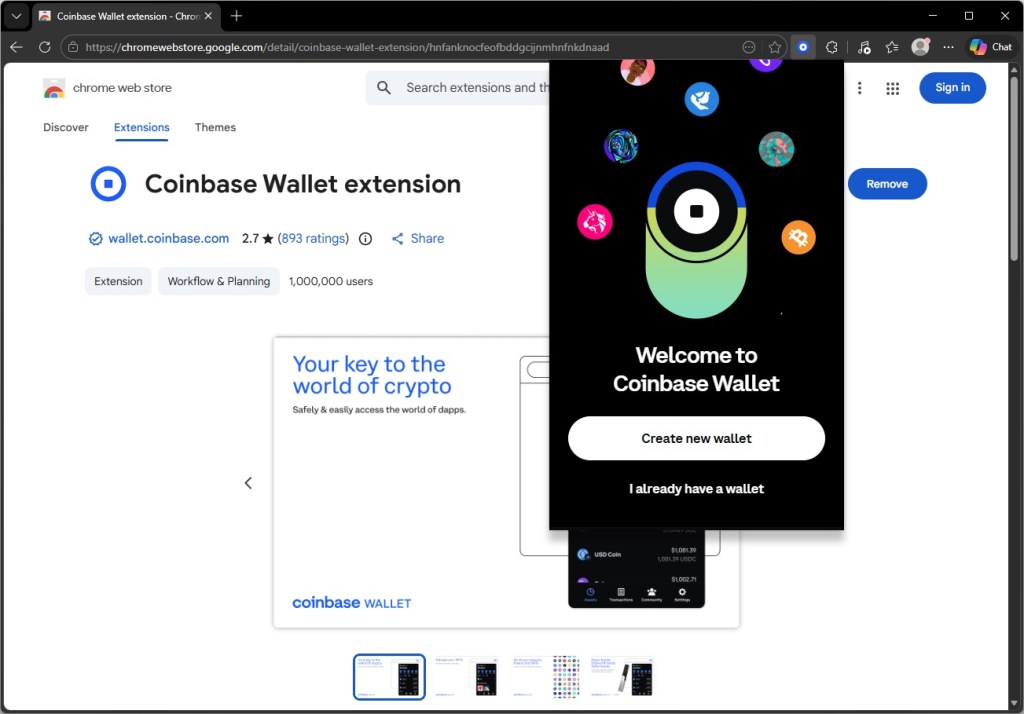
MetaMask (marked “RECOMMENDED”), Trust Wallet, Coinbase Wallet, Ledger, Trezor Wallet, Phantom Wallet, Rabby Wallet, OKX Wallet, Magic Eden, Solflare, and Uniswap Wallet.
The attack becomes technically interesting at the next step.
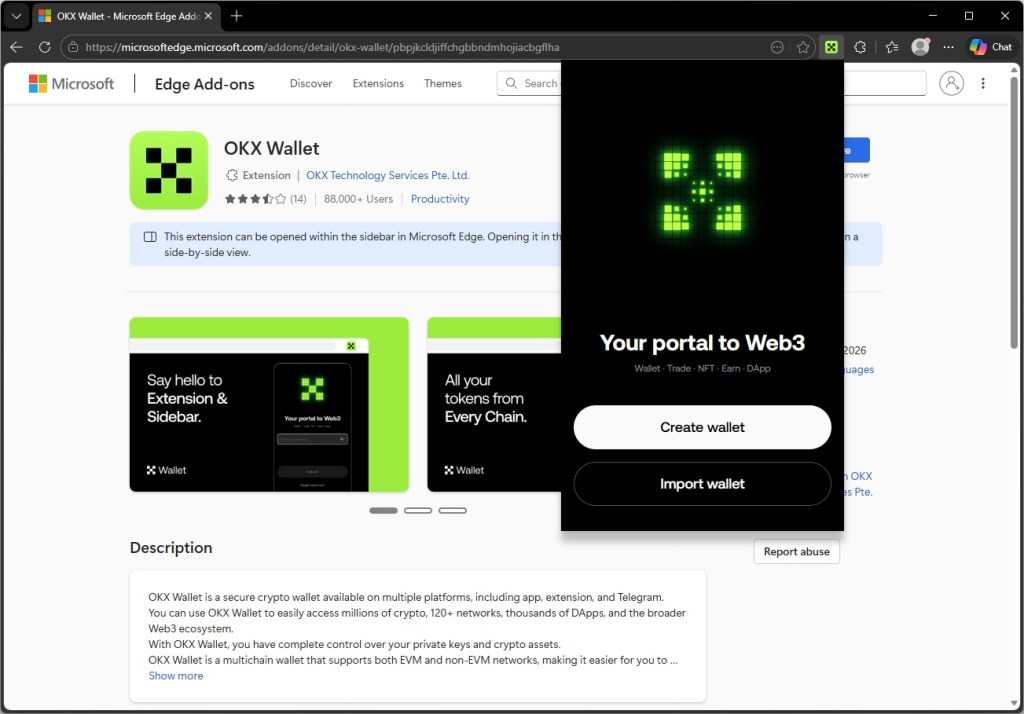
Selecting a software wallet does not redirect the user to another page or open an external site. Instead, the page renders an overlay designed to look like the wallet’s actual browser extension unlock screen. The overlay appears at the edge of the browser viewport right where a real extension popup would appear.
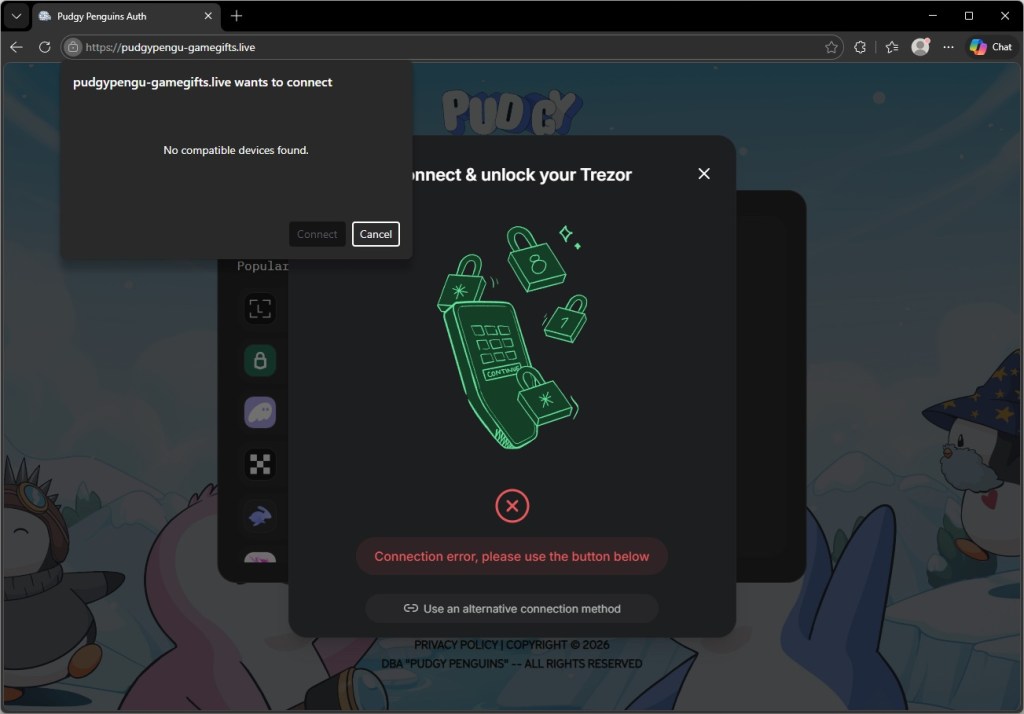
Hardware wallet flows behave differently. Selecting Trezor Wallet opens a center-screen dialog mimicking the Trezor Connect interface, rather than a corner overlay. In both cases, the result is that the user believes they are looking at their own installed software, when they are in fact looking at a webpage element controlled by the attacker.
The forgery sits exactly where your real extension would
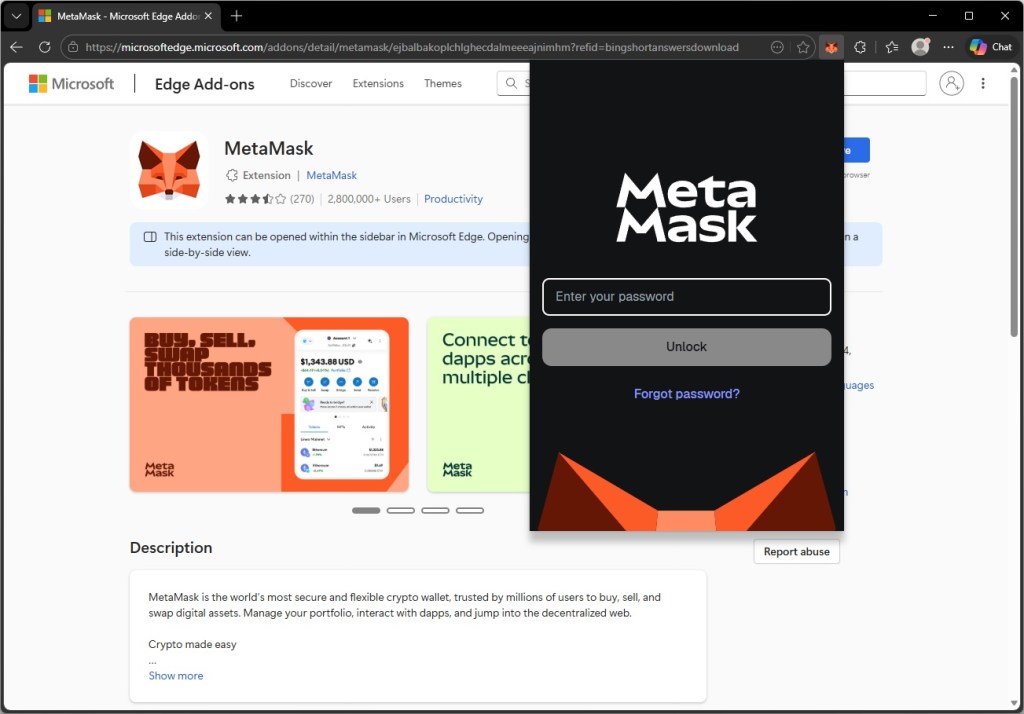
For every browser extension wallet on the list, the phishing site renders an unlock screen built to match the real extension’s own visual identity, with the correct logo, color scheme, button layout, and wording.
The screenshots below show the forgeries alongside the genuine extensions. The differences are not visible to someone who is not looking for them.
Hardware wallet users are not exempt, and the targeting of Trezor is particularly telling.
Trezor devices are typically owned by people who have been in crypto long enough to invest in dedicated security hardware. In other words, users likely holding higher-value accounts.
Selecting Trezor Wallet on the phishing site triggers a dialog that closely mimics the Trezor Connect bridge interface. At the same time, the browser displays a native USB device permission prompt—the operating system’s own dialog, triggered by a WebUSB API call—reading “pudgypengu-gamegifts.live wants to connect.”
The prompt says “No compatible devices found” if no Trezor is plugged in, but the sequence is designed to look like a genuine hardware handshake.
A user who plugs in their Trezor at this point and approves the USB permission has granted the phishing site access to the device bridge.
For those without a device to hand, the dialog offers another option: “Use an alternative connection method.” That path is likely where the most damage is done. A user who cannot get the hardware flow to work and falls back to a manual option is one step away from being asked to type in their seed phrase, the master key to everything in their wallet, directly into a field the attacker controls.
The page that plays dead for researchers
The phishing page is more cautious than it first appears.
Embedded in the site is an obfuscated JavaScript loader, its real contents compressed and hidden behind multiple layers of encoding, that performs a series of checks before doing anything visible.
First, it tests whether the browser is being driven by an automated tool of the kind security researchers and sandboxes use to analyse suspicious pages in bulk. If it detects one, it quietly stops and the page appears clean.
Next, it reads the graphics hardware identifier to determine whether it is running inside a virtual machine, which is another common analysis environment.
Only once it is satisfied that a real user is present does it request a second, larger payload from the attacker’s server. That payload contains the code responsible for credential theft.
Even that request contains a safeguard. If the server response is smaller than 500 KB (the kind of placeholder response a security vendor might serve to a known malicious domain), the loader discards it and does nothing.
The practical consequence of all this is that automated scanning tools are likely to rate the initial page as benign, because on their infrastructure, it behaves like one. The malicious functionality never loads unless the attacker’s server decides the visitor is worth targeting.
Why this campaign targets Pudgy players
The timing seems to be deliberate. Pudgy World launched on March 10, 2026, and the phishing campaign appears to have been active around the same window. New players arriving at the game for the first time are walking through a Web3 onboarding flow they have never experienced before.
The legitimate “connect your wallet” step on the official site teaches users that this behaviour is normal. The phishing site then exploits that expectation before experience can challenge it.
The range of wallets targeted is also significant. The campaign leaves almost no wallet blind spot. Whether the victim holds Ethereum, Solana, or multi-chain assets, there is a convincing forgery waiting for them. Building 11 wallet-specific UI forgeries is not a trivial undertaking. It points either to a well-resourced threat actor or, more likely, to the reuse of a commercial phishing kit built for precisely this class of attack.
What to do if you may have been affected
Crypto phishing campaigns have long relied on fake airdrops and fake MetaMask pages. This campaign stands out for how precisely it imitates a wallet’s unlock screen, placing the prompt exactly where a real extension pop-up would appear and exploiting users’ muscle memory.
The attack also piggybacks on Pudgy World’s launch. As Web3 products reach wider audiences, they attract attackers targeting users unfamiliar with wallet security.
One rule still holds: a website can never display your real browser extension unlock screen.
- If you entered your MetaMask, Coinbase Wallet, or any other software wallet password on this site, change your password immediately by unlocking the extension normally and going to Settings. Consider transferring assets to a new wallet address whose seed phrase has never been used on any website.
- If you approved the USB device permission prompt for Trezor, disconnect your device and review your Trezor Suite connection history. A WebUSB connection alone does not expose your seed phrase, but it can allow a malicious page to communicate with the bridge. Revoke the permission in your browser’s site settings immediately.
- Bookmark the official Pudgy Penguins site (pudgypenguins.com) and the official game URL. Navigate to it directly from that bookmark, never from a link in Discord, Twitter, or a direct message.
- Install a browser extension that flags known phishing domains before you interact with them. Malwarebytes Browser Guard will block this domain.
- Remind yourself of this rule: your wallet’s unlock screen always appears in the bar at the very top of the window, not inside the page itself. Any page that appears to show you your wallet’s password prompt inside the page content is a phishing site.
Indicators of Compromise (IOCs)
Domains
pudgypengu-gamegifts[.]live
LABScon25 Replay | Your Apps May Be Gone, But the Hackers Made $9 Billion and They’re Still Here
In this LABScon 25 talk, Andrew MacPherson dives deep into the high-stakes world of crypto crime, which has amassed approximately $9 billion in illicit funds. Andrew demystifies the technical landscape and exposes the sophisticated attack vectors plaguing the decentralized finance (DeFi) space.
The talk begins with an explanation of the core concepts necessary to understand crypto-related security threats, including definitions of blockchains, wallets, and smart contracts. Andrew explains that a key point in the architectural difference of many crypto applications is that they typically rely solely on frontends, with all interactions happening in the browser via the wallet extension.
The talk then moves on to focus on attack patterns. Crypto thieves target every weak point, from applications and code to the developers and executives themselves. The speaker details the largest crypto heist to date, the $1.5 billion loss from Bybit. This attack involved infecting a developer’s machine, gaining access to production JavaScript code, and modifying it to authorize a full wallet drain during a multi-signature transaction. The talk also covers supply chain risks like typo-squatting, exploitation of personal servers like Plex to compromise GitHub accounts, and the rise of “drainers as a service” that simplify crypto theft.
Andrew also covers the challenges attackers face in laundering stolen funds, and how they leverage techniques such as cross-chain swaps, using mixers like Tornado Cash, and non-KYC platforms for conversion to cash. Despite the fact that all blockchain logs are public and permanent, the presentation also discusses the challenges threat intel analysts face in tracking these rapidly moving funds.
Andrew’s presentation is essential viewing for anyone interested in cryptocurrency and cybersecurity, especially those looking to understand the technical realities of financial crime in the decentralized era.
About the Author
Starting at Paterva, Andrew Macpherson spent more than 10 years creating Maltego before moving to the US for security roles at BitMEX (IR), Robinhood (IR/D&R), Uniswap (Head of Security), and now Privy (Principal Security Engineer). He’s spoken at Black Hat, DEF CON, DSS, EthCC and countless others, teaching courses and drinking malibu on the way.
About LABScon
This presentation was featured live at LABScon 2025, an immersive 3-day conference bringing together the world’s top cybersecurity minds, hosted by SentinelOne’s research arm, SentinelLABS.
Keep up with all the latest on LABScon here.