Visualização de leitura
FBI Links Cybercriminals to Sharp Surge in Cargo Theft Attacks
What happened The FBI issued a public service announcement on April 30, 2026, warning the US transportation and logistics industry of a sharp rise in cyber-enabled cargo theft, with estimated losses in the United States and Canada reaching nearly $725 million in 2025. That represents a 60% increase over the prior year. Confirmed cargo theft […]
The post FBI Links Cybercriminals to Sharp Surge in Cargo Theft Attacks appeared first on CISO Whisperer.
The post FBI Links Cybercriminals to Sharp Surge in Cargo Theft Attacks appeared first on Security Boulevard.

Digital attacks drive a new wave of cargo theft, FBI says
The FBI warns of rising cyber cargo theft, with hackers targeting brokers and carriers. Experts say digital attacks are replacing traditional cargo theft.
The FBI has issued a Public Service Announcement (PSA) about a surge in cyber-enabled cargo theft, with hackers increasingly targeting brokers and carriers. This trend confirms earlier findings from Proofpoint and alerts from the NMFTA, which noted that traditional cargo theft is being replaced by more sophisticated, digital attacks across the logistics sector.
“The Federal Bureau of Investigation is publishing this Public Service Announcement (PSA) to warn the public of cyber threat actors increasingly using sophisticated, cyber-enabled tactics to impersonate legitimate businesses to hijack freight, steal high-value shipments, and reroute deliveries, resulting in a surge of strategic cargo theft.” reads the FBI’s PSA.
Crooks are increasingly targeting the U.S. transportation and logistics sector, including brokers and carriers. Since 2024, attackers have used phishing emails, fake websites, and compromised accounts to gain access to systems. They impersonate legitimate companies and post fake load listings to trick victims into handing over goods, which are then diverted and resold.
“Since at least 2024, cyber threat actors have gained unauthorized access to the computer systems of brokers and carriers — typically via spoofed emails, fake URLs, and compromised carrier accounts.” continues the announcement. “The cyber actors pose as victim companies and post fraudulent listings on load boards to deceive shippers, brokers, and carriers into handing over goods, which are redirected from their intended destination and stolen for resale. “
In 2025, cargo theft losses in the U.S. and Canada reached nearly $725 million, up 60% from 2024. Incidents rose 18%, while the average loss per theft increased 36% to $273,990, reflecting a shift toward fewer but higher-value targets.
Cyber-enabled cargo theft follows a structured, multi-step scheme. Attackers first compromise broker or carrier accounts using phishing emails and fake links that install remote access tools. With control of these systems, they impersonate companies and post fake loads on trucking platforms, tricking legitimate carriers into engaging and sometimes infecting them too.
Next, criminals pose as trusted carriers to accept real shipments, then “double-broker” them to unsuspecting drivers while altering documents and delivery details. They may even update official records to appear legitimate.
Finally, the cargo gets redirected, transferred to complicit drivers, and stolen for resale. In some cases, attackers demand ransom to reveal shipment details or location.
The PSA includes indicators to spot cyber-enabled cargo theft attacks. These include unexpected contacts about shipments made in their name without authorization, and emails that mimic real domains but use free providers or slight variations. Messages may push users to click shortened or spoofed links, often tied to fake complaints or documents that deliver malware.
Other red flags include new or suspicious mailbox rules, such as auto-forwarding or deletion. Attackers also use altered email addresses with small changes or added titles. Communication often comes via email or short-lived VoIP phone numbers, sometimes linked to overseas activity.
To prevent cargo theft, businesses should verify shipments using independent and multiple channels before releasing goods. Do not trust names or emails alone—confirm requests with additional authentication. Keep detailed records of drivers, vehicles, and transactions to support investigations and reduce fraud risks.
Companies can spot cyber-enabled cargo theft through several warning signs. These include unexpected contacts about shipments made in their name without authorization, and emails that mimic real domains but use free providers or slight variations. Messages may push users to click shortened or spoofed links, often tied to fake complaints or documents that deliver malware.
Other red flags include new or suspicious mailbox rules, such as auto-forwarding or deletion. Attackers also use altered email addresses with small changes or added titles. Communication often comes via email or short-lived VoIP phone numbers, sometimes linked to overseas activity.
FBI recommends businesses should verify shipments using independent and multiple channels before releasing goods. Do not trust names or emails alone, confirm requests with additional authentication. Keep detailed records of drivers, vehicles, and transactions to support investigations and reduce fraud risks.
Recently Proofpoint researchers observed crooks targeting trucking and logistics companies, running coordinated remote access campaigns to steal cargo and divert payments. These attacks appear to be linked to organized crime.
The findings highlight a growing trend of cyber-enabled cargo theft, where digital intrusions directly support real-world crime. This threat is expanding rapidly, with losses in North America reaching $6.6 billion in 2025, showing how cyberattacks are increasingly used to disrupt supply chains and generate profit.
In November 2025, Proofpoint first reported cybercriminals were targeting trucking and logistics firms with RMM tools (remote monitoring and management software) to steal freight. Active since June 2025, the group works with organized crime to loot goods, mainly food and beverages.
Crooks infiltrate logistics firms, hijack cargo bids, and steal goods, fueling the rise of cyber-enabled freight theft.
Follow me on Twitter: @securityaffairs and Facebook and Mastodon
(SecurityAffairs – hacking, cargo theft)
US-Estonian Suspect Arrested Over Alleged Scattered Spider Cyberattacks
Cyber attacks fuel surge in cargo theft across logistics industry
Hackers infiltrate logistics firms to steal cargo and divert payments, cyberattacks are linked to organized crime and rising losses.
Proofpoint researchers observed crooks targeting trucking and logistics companies, running coordinated remote access campaigns to steal cargo and divert payments. These attacks appear to be linked to organized crime.
The findings highlight a growing trend of cyber-enabled cargo theft, where digital intrusions directly support real-world crime. This threat is expanding rapidly, with losses in North America reaching $6.6 billion in 2025, showing how cyberattacks are increasingly used to disrupt supply chains and generate profit.
“In late February 2026, Proofpoint researchers executed a malicious payload from a threat actor targeting transportation organizations inside a controlled decoy environment operated by our partners at Deception.pro.” reads the report published by Proofpoint. “While the environment did not represent a transportation carrier, it remained compromised for more than a month—offering rare, extended visibility into post‑compromise operations, tooling, and decision‑making.”
In November 2025, Proofpoint first reported cybercriminals were targeting trucking and logistics firms with RMM tools (remote monitoring and management software) to steal freight. Active since June 2025, the group works with organized crime to loot goods, mainly food and beverages.
Crooks infiltrate logistics firms, hijack cargo bids, and steal goods, fueling the rise of cyber-enabled freight theft.
On February 27, 2026, attackers breached a load board platform and sent emails to carriers about fake shipping jobs.
The message delivered a malicious VBS file that launched a PowerShell script, installed ScreenConnect for remote access, and showed a fake agreement to hide the attack.
After gaining access, they focused on persistence by installing multiple remote management tools. Over a month, they deployed several ScreenConnect instances along with Pulseway and SimpleHelp, ensuring continued access even if one tool was detected or removed.
The researchers reported the attackers used a new “signing-as-a-service” method to deploy a stealthy ScreenConnect instance. A PowerShell chain bypassed controls, downloaded the installer, had it re-signed with a fraudulent but valid certificate, then installed it silently. It also replaced original components with signed versions to avoid detection, bypass revoked certificates, and maintain persistent, trusted remote access.
After gaining stable access, the attacker moved to hands-on activity. They manually checked accounts like PayPal and ran a custom tool to find and steal cryptocurrency wallet data, sending results to Telegram.
They used over a dozen PowerShell scripts to profile victims, collecting user data, browser history, and signs of access to banking, payments, logistics, and accounting platforms. The scripts copied locked files, searched for valuable services, stored data in hidden folders, and ran with SYSTEM privileges.
The attacker consistently scanned browser databases, matched patterns, and reported findings via Telegram, sometimes using delayed tasks to evade controls. Targets included banks, money transfer services, fleet payment systems, and freight platforms—showing a clear focus on financial fraud and cargo theft.
In a final step, another script quietly gathered system details, checked security tools and financial apps, and sent results back through the existing remote session without raising alerts.
The intrusion shows that financially motivated attackers go far beyond initial access. They focus on staying hidden, gathering intelligence, and stealing credentials to exploit payment systems and logistics platforms—behavior that also aligns with freight theft and cargo diversion preparation.
“Notably, the use of a signing‑as‑a‑service capability underscores a growing trend toward attacker use of legitimate trust mechanisms to evade detection.” concludes the report. “For transportation, logistics, and freight organizations, these findings reinforce the importance of monitoring for unauthorized remote management tools, suspicious PowerShell activity, and abnormal browser telemetry associated with financial platform access. “
Follow me on Twitter: @securityaffairs and Facebook and Mastodon
(SecurityAffairs – hacking, cargo)
GraphAlgo Scam: Lazarus Hackers Register Real US LLCs to Spread Malware
Port of Vigo Hit by Ransomware Attack, Cargo Systems Disrupted

Port of Vigo Cyberattack Slows Port Operations
The cyberattack on Port of Vigo has not impacted the port’s physical functioning, but it has significantly disrupted daily operations. Much of the cargo handling process depends on digital platforms for scheduling, coordination, and documentation. With systems offline, port users have been asked to switch to manual methods. Some operations, including those at the Border Inspection Post (BIP), are now being managed using paper records to keep workflows moving. This fallback has helped avoid a complete shutdown, but it is slowing processes and adding pressure on staff. The situation reflects how dependent modern port operations have become on digital infrastructure.Ransomware Behind the Attack
Authorities have confirmed that the Port of Vigo cyberattack involved ransomware, a type of malware that blocks access to systems or data until a ransom is paid. In many cases, attackers also extract sensitive data, increasing the risk of further exposure. In this case, the focus remains on containment and recovery. A forensic investigation is currently underway to determine how the attackers gained access and whether any data has been compromised.No Immediate Recovery Timeline
Despite progress in controlling the attack, the Port Authority has made it clear that restoring systems will take time. The IT team has not provided an estimated timeline for resuming server activity, citing the need for complete security validation before reconnecting systems. “The port's operational services and physical functioning have not been affected, but the programs will not be reopened to the public until all security checks have been completed,” Botana stated. This cautious approach is increasingly common in ransomware cases, where premature restoration can lead to reinfection or further compromise.A Reminder of Growing Cyber Risks
The Port of Vigo cyberattack highlights the growing risk ransomware poses to critical infrastructure. Ports, in particular, rely on a mix of physical operations and digital systems, making them vulnerable to disruptions that can affect both logistics and trade flow. While operations at Vigo have not stopped entirely, the shift to manual processes shows how quickly efficiency can drop when systems go offline. The Port of Vigo cyberattack incident also points to a broader trend, cyberattacks are no longer limited to data theft. They are increasingly designed to disrupt operations, creating immediate and visible impact. As the investigation into cyberattack on Port of Vigo continues, the focus remains on restoring systems safely and understanding the scope of the breach. For now, the Port of Vigo continues to operate under constrained conditions, managing cargo traffic without the digital tools it typically depends on.Firefox is giving users the AI off switch
Some software providers have decided to lead by example and offer users a choice about the Artificial Intelligence (AI) features built into their products.
The latest example is Mozilla, which now offers users a one-click option to disable generative AI features in the Firefox browser.
Audiences are divided about the use of AI, or as Mozilla put it on their blog:
“AI is changing the web, and people want very different things from it. We’ve heard from many who want nothing to do with AI. We’ve also heard from others who want AI tools that are genuinely useful. Listening to our community, alongside our ongoing commitment to offer choice, led us to build AI controls.”
Mozilla is adding an AI Controls area to Firefox settings that centralizes the management of all generative AI features. This consists mainly of a master switch, “Block AI enhancements,” which lets users effectively run Firefox “without AI.” It blocks existing and future generative AI features and hides pop‑ups or prompts advertising them.
Once you set your AI preferences in Firefox, they stay in place across updates. You can also change them whenever you want.
Starting with Firefox 148, which rolls out on February 24, you’ll find a new AI controls section within the desktop browser settings.
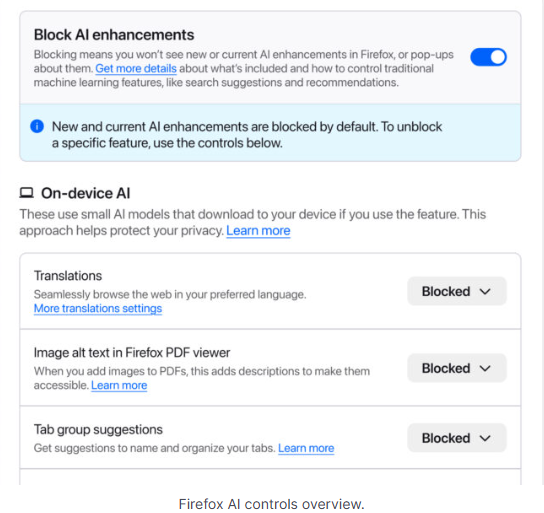
You can turn everything off with one click or take a more granular approach. At launch, these features can be controlled individually:
- Translations, which help you browse the web in your preferred language.
- Alt text in PDFs, which add accessibility descriptions to images in PDF pages.
- AI-enhanced tab grouping, which suggests related tabs and group names.
- Link previews, which show key points before you open a link.
- An AI chatbot in the sidebar, which lets you use your chosen chatbot as you browse, including options like Anthropic Claude, ChatGPT, Microsoft Copilot, Google Gemini and Le Chat Mistral.
We applaud this move to give more control to the users. Other companies have done the same, including Mozilla’s competitor DuckDuckGo, which made AI optional after putting the decision to a user vote. Earlier, browser developer Vivaldi took a stand against incorporating AI altogether.
Open-source email service Tuta also decided not to integrate AI features. After only 3% of Tuta users requested them, Tuta removed an AI copilot from its development roadmap.
Even Microsoft seems to have recoiled from pushing AI to everyone, although so far it has focused on walking back defaults and tightening per‑feature controls rather than offering a single, global off switch.
Choices
Many people are happy to use AI features, and as long as you’re aware of the risks and the pitfalls, that’s fine. But pushing these features on users who don’t want them is likely to backfire on software publishers.
Which is only right. After all, you’re paying the bill, so you should have a choice. Before installing a new browser, inform yourself not only about its privacy policy, but also about what control you’ll have over AI features.
Looking at recent voting results, I think it’s safe to say that in the AI gold rush, the real premium feature isn’t a chatbot button—it’s the off switch.
We don’t just report on privacy—we offer you the option to use it.
Privacy risks should never spread beyond a headline. Keep your online privacy yours by using Malwarebytes Privacy VPN.
One privacy change I made for 2026 (Lock and Code S07E02)
This week on the Lock and Code podcast…
When you hear the words “data privacy,” what do you first imagine?
Maybe you picture going into your social media apps and setting your profile and posts to private. Maybe you think about who you’ve shared your location with and deciding to revoke some of that access. Maybe you want to remove a few apps entirely from your smartphone, maybe you want to try a new web browser, maybe you even want to skirt the type of street-level surveillance provided by Automated License Plate Readers, which can record your car model, license plate number, and location on your morning drive to work.
Importantly, all of these are “data privacy,” but trying to do all of these things at once can feel impossible.
That’s why, this year, for Data Privacy Day, Malwarebytes Senior Privacy Advocate (and Lock and Code host) David Ruiz is sharing the one thing he’s doing different to improve his privacy. And it’s this: He’s given up Google Search entirely.
When Ruiz requested the data that Google had collected about him last year, he saw that the company had recorded an eye-popping 8,000 searches in just the span of 18 months. And those 8,000 searches didn’t just reveal what he was thinking about on any given day—including his shopping interests, his home improvement projects, and his late-night medical concerns—they also revealed when he clicked on an ad based on the words he searched. This type of data, which connects a person’s searches to the likelihood of engaging with an online ad, is vital to Google’s revenue, and it’s the type of thing that Ruiz is seeking to finally cut off.
So, for 2026, he has switched to a new search engine, Brave Search.
Today, on the Lock and Code podcast, Ruiz explains why he made the switch, what he values about Brave Search, and why he also refused to switch to any of the major AI platforms in replacing Google.
Tune in today to listen to the full episode.
Show notes and credits:
Intro Music: “Spellbound” by Kevin MacLeod (incompetech.com)
Licensed under Creative Commons: By Attribution 4.0 License
http://creativecommons.org/licenses/by/4.0/
Outro Music: “Good God” by Wowa (unminus.com)
Listen up—Malwarebytes doesn’t just talk cybersecurity, we provide it.
Protect yourself from online attacks that threaten your identity, your files, your system, and your financial well-being with our exclusive offer for Malwarebytes Premium Security for Lock and Code listeners.
A week in security (January 5 – January 11)
Last week on Malwarebytes Labs:
- pcTattletale founder pleads guilty as US cracks down on stalkerware
- Are we ready for ChatGPT Health?
- CISA warns of active attacks on HPE OneView and legacy PowerPoint
- Lego’s Smart Bricks explained: what they do, and what they don’t
- Fake WinRAR downloads hide malware behind a real installer
- One million customers on alert as extortion group claims massive Brightspeed data haul
- Phishing campaign abuses Google Cloud services to steal Microsoft 365 logins
- Disney fined $10m for mislabeling kids’ YouTube videos and violating privacy law
- ALPRs are recording your daily drive (Lock and Code S06E26)
- Grok apologizes for creating image of young girls in “sexualized attire”
Stay safe!
We don’t just report on privacy—we offer you the option to use it.
Privacy risks should never spread beyond a headline. Keep your online privacy yours by using Malwarebytes Privacy VPN.
Hackers commit highway robbery, stealing cargo and goods
There’s a modern-day train heist happening across America, and this time, some of the bandana-masked robbers are sitting behind screens.
According to new research, a group of cybercriminals has been attacking trucking, freight, and logistics companies for months, impersonating brands and even diverting real cargo shipments to unapproved locations so that the stolen goods can be sold or shipped elsewhere.
The impact, the researchers said, extends far beyond the logistics industry:
“Such crimes can create massive disruptions to supply chains and cost companies millions, with criminals stealing everything from energy drinks to electronics. The most targeted commodities are food and beverage products.”
Although the cyberattacks were mostly seen in North America, cargo theft is a problem across the world, impacting consumers and businesses that rely on the often-overlooked network of trucks, trains, ships, planes, and people.
In these attacks, cybercriminals compromise the accounts of carrier companies that transport goods from one location to the next. By posing as legitimate carriers, they can place real bids on shipments and then redirect them to unauthorized destinations, where they or their partners will receive and steal the cargo.
Researchers found that attackers take control of these accounts in at least one of three ways.
1. Fake load boards
Attackers may post a fake order on what’s called a “load board,” a digital marketplace that connects shippers with carriers so that cargo can be assigned and accepted. But when legitimate carriers inquire about the fake load board posting, the criminals reply with an email that includes a malicious link that, when clicked, installs Remote Monitoring and Management (RMM) software. (To make the scam more convincing, the cybercriminals also compromise a “broker” account so their load board posting looks legitimate.)
Despite the sneaky install method, RMM software itself is entirely legitimate. It’s used by IT support teams to remotely fix issues for employees. But that legitimacy makes RMM software perfect for any cybercriminal campaign because it may raise fewer red flags from older antivirus tools.
Once the attackers gain access to a carrier’s account, they can also deploy malware to steal account credentials, giving them greater access to a company’s network.
2. Compromised email accounts
A second observed attack method involved hijacking an active email address and then impersonating the owner when responding to emails about cargo orders and shipments. Here, too, cybercriminals inserted malicious links into emails that eventually install RMM tools.
3. Social engineering
Finally, researchers also observed the attackers sending direct phishing emails to carriers, using classic social engineering tricks—like sending a bogus bill to lure victims into clicking malicious links.
While many of the well-tested security best practices still apply—like not clicking on links inside emails—one of the strongest defenses is to use a security product that notifies users about RMM tools (also sometimes referred to as Remote Desktop Programs) installed on their device. RMM tools are legitimate, but because of their abuses in cybercriminal campaigns, it is important that every installation is verified and tracked.
We don’t just report on threats—we remove them
Cybersecurity risks should never spread beyond a headline. Keep threats off your devices by downloading Malwarebytes today.
Tracking Adversaries: Ghostwriter APT Infrastructure
Introduction to Infrastructure Pivoting
Pivoting on infrastructure is a handy skill for cyber threat
intelligence (CTI) analysts to learn. It can help to reveal the bigger picture
when it comes to malware, phishing, or network exploitation campaigns. Infrastructure
pivoting essentially is the act of looking for more systems an adversary has
created. The main benefit of this pursuit is the identification of additional
targets or victims, more tools or malware samples, and ultimately new insights
about the adversary’s capabilities.
If done correctly, being able to pivot on adversary
infrastructure will be very useful during incident response (IR) engagements. For
example, it may lead to being able to attribute the intrusion to a known
adversary. This will help others during an IR engagement understand the level
of threat posed to the victim organisation.
Receiving Threat Data
To be able to pivot on adversary infrastructure, threat data
is needed such as the intelligence shared by threat reports put out
by various researchers from public and private sector organisations. This
scenario, however, involves relying on the analysis skills of other researchers to explain
what the infrastructure is and when they observed it in use.
This blog will examine threat data provided by public sector
organisations such as the Computer Emergency Response Team of Ukraine (CERT-UA)
as well as cybersecurity vendors such as Deep Instinct, Cyble, and Fortinet.
These organisations have shared indicators of compromise (IOCs) uncovered
following analysis of adversary intrusion activities or upload to online
malware sandboxes, such as VirusTotal, among others.
Introduction to the Ghostwriter Campaign
On 3 June 2024, Fortinet shared a report
on malicious XLS macro documents leading to Cobalt Strike Beacons. Analysis of
the XLS documents showed that they appeared to be targeting the Ukrainian
military and linked to a known Belarusian state-sponsored APT group tracked as Ghostwriter
(aka UNC1151, UAC-0057, TA445). On 4 June 2024, Cyble also shared a report
on a similar campaign.
In both reports, if the XLS was opened and the macros were executed
by the target, a malicious DLL file was downloaded from an adversary-created domain.
In Fortinet’s report, two similar “.shop” domains were mentioned. In Cyble’s
report another “.shop” domain was also called out.
Overlapping IOCs
The first pivot on Ghostwriter APT infrastructure that will be
demonstrated involves finding indicators of compromise (IOCs) such as domains
and IP addresses that appear in multiple threat reports.
The fastest way to realize these overlaps is through
continuous collection of reported IOCs into a Threat Intelligence Platform
(TIP). This will reveal IOCs that appear in multiple threat reports through
tagging and sources of where IOCs come from. Eventually, one domain or IP
address will get reported by multiple entities and the connection will make
itself apparent.
In Figure 1 (see below) the domain “goudieelectric[.]shop”
appeared in both Cyble’s blog and Fortinet’s blog. Analysis of all three
domains found that they use the same generic top-level domain (gTLD),
registrar, and name servers, as well as have a robots.txt directory configured.
These common infrastructure characteristics indicate that all three domains
were created by the same adversary.
Domain Registration & Hosting Overlaps
When more IOCs are reported in other threat reports it is
possible to link them to other known domains, this is due to adversaries
reusing the same registrars, name servers, and gTLDs.
In Figure 2 (see below), Deep Instinct reported
two more domains that could also be linked to the previous three domains through
the mutual use of the PublicDomainsRegistry registrar, Cloudflare name servers,
and the robots.txt file.
Further, CERT-UA reported three more domains (see
Figure 3 below) that could be linked to the infrastructure cluster through this
same method as well. This pattern of behaviour is a strong indicator that these
domains were created by the same adversary.
Finding Unreported Domains
Since the domains from the above threat reports were
collected and linked together through overlapping attributes, it is now
possible to use these attributes to find more domains that had gone unreported.
Using a VirusTotal domain attribute query, additional domains
can be found by using the following registration pattern:
- Name Servers: CLOUDFLARE
- Registrar: PublicDomainRegistry
- TLD: *.shop
This revealed up to 24 domains that matched this pattern
that were likely created by Ghostwriter, a state-sponsored APT group:
- backstagemerch[.]shop
- bryndonovan[.]shop
- chaptercheats[.]shop
- clairedeco[.]shop
- connecticutchildrens[.]shop
- disneyfoodblog[.]shop
- eartheclipse[.]shop
- empoweringparents[.]shop
- foampartyhats[.]shop
- goudieelectric[.]shop
- ikitas[.]shop
- jackbenimblekids[.]shop
- kingarthurbaking[.]shop
- lansdownecentre[.]shop
- lauramcinerney[.]shop
- medicalnewstoday[.]shop
- moonlightmixes[.]shop
- penandthepad[.]shop
- physio-pedia[.]shop
- semanticscholar[.]shop
- simonandschuster[.]shop
- thevegan8[.]shop
- twisterplussize[.]shop
- utahsadventurefamily[.]shop
Note: VirusTotal domain searches are only available
to VirusTotal Enterprise users. There are other providers which allow you to search
for domain registration patterns such as DomainTools, Validin, and Zetalytics. There
also some free OSINT sites such as nslookup.io
and viewdns.info that can be useful in
certain scenarios.
Finding Related Malware Samples
Using the list of similar domains that were uncovered
through the registration pattern search, it is then possible to find additional
malware samples communicating with them.
This can be achieved by looking at domains in VirusTotal and checking the Relations tab can show communicating files as shown in Figure 4 below.
Using a VirusTotal graph can help to reveal every
communicating file with every domain discovered through the registration pattern
search, as shown in Figure 5 below.
URL to the VirusTotal Graph: https://www.virustotal.com/graph/embed/gd2c04407d9ba4b75b2ce73d6155d166d3ef75eaf29894ff5ac287c90400072bc?theme=dark
URL to the VirusTotal Collection: https://www.virustotal.com/gui/collection/2aa6b36a717be8bc49f7925434ca40f3ecb9f628414b491da3e985677508ca08/iocs
Lessons Learned
In conclusion, it is important for CTI analysts to closer
inspect the attributes of the IOCs they come across. It is not uncommon for
state-sponsored APT groups to make such mistakes when creating their
infrastructure to launch attacks from. By exploiting this fact, CTI analysts
can learn much more about the adversary’s targets, capabilities, and the behaviours
of the humans themselves behind such campaigns.
The importance of this type of work was demonstrated in
December 2023 when the US Treasury
sanctioned members of the Russian APT group known as Callisto
(aka Star Blizzard, BlueCharlie, COLDRIVER, GOSSAMER BEAR). The real world
identity of Andrey Korinets was revealed after he was sanctioned for fraudulently
creating and registering malicious domain infrastructure for Russian federal
security service (FSB) spear phishing campaigns.








