On November 29th, 2024, Black Friday, shoppers flooded online stores to grab the best deals of the year. But while consumers were busy filling their carts, cyber criminals were also seizing the opportunity to exploit the shopping frenzy. Our system detected a significant surge in Gozi malware activity, targeting financial institutions across North America.
The Black Friday connection
Black Friday creates an ideal environment for cyber criminals to thrive. The combination of skyrocketing transaction volumes, a surge in online activity and often lax security awareness among users provides fertile ground for launching attacks. Gozi malware, a well-known banking Trojan, exploits this seasonal chaos to target unsuspecting users and financial institutions alike.
This year’s Black Friday activity was particularly concerning, with a notable increase in web-inject attacks. These sophisticated techniques compromised online banking sessions, enabling the theft of credentials, financial information and other sensitive data.
The campaign is not expected to stop there. With the subsequent year-end shopping rush, Gozi malware is poised to continue its onslaught. Cyber criminals are likely to capitalize on the desperation of last-minute shoppers seeking the best holiday deals, amplifying the malware’s reach and impact.
These ongoing attacks emphasize the need for vigilance and proactive security measures. Whether you’re a consumer enjoying the convenience of online shopping or a business managing increased transaction volumes, understanding the evolving tactics of cyber criminals is critical to staying ahead of the threat.
What is Gozi malware?
Gozi, also known as Ursnif and ISFB, is a modular banking Trojan that has been active since the mid-2000s. It is infamous for its ability to steal banking credentials, monitor user activity and execute advanced web-injects during online banking sessions. Over the years, it has evolved to include features like anti-debugging mechanisms and encrypted communication and is also used for targeted attacks on specific regions and financial institutions.
Observations from our system
During Black Friday, our telemetry revealed the following trends:
- Targeted campaigns: Gozi operators appeared to focus on North American banks, aligning their campaigns with the peak shopping hours.
- Increase in attack volume: The malware’s web-inject functionality was heavily used, indicating a rise in compromised banking sessions.
Why the surge?
The Black Friday spike in Gozi activity can be attributed to:
- Volume of transactions: The sheer number of financial transactions increases the probability of successful attacks.
- Weakened defenses: Many businesses prioritize frictionless user experience, uptime and sales during Black Friday, potentially delaying or weakening their security measures.
- Human behavior: Consumers are more likely to overlook suspicious activity when rushing to grab deals.
What we found
The provided script demonstrates a sophisticated web injection attack used to compromise online banking sessions. It dynamically injects malicious code into the legitimate banking page, allowing attackers to manipulate the session without the victim’s knowledge. The malicious script operates in the background to steal sensitive data, such as credentials, and is designed to evade detection by immediately removing itself from the page after execution. By blending with the legitimate page and erasing evidence, the attack becomes nearly invisible to both users and traditional security measures. This highlights the growing sophistication of web-inject attacks and underscores the need for advanced monitoring systems and robust security measures to detect and prevent such threats.
Figure 1: Sample of Gozi injection
From the screenshot below, it appears that the attacker left minimal evidence, likely attempting to test the mechanism and ensure everything is functioning correctly:
Figure 2: Attacker preparation
We believe the web-inject is still a work in progress, with potential future updates and enhancements to the code likely.
If you’d like to learn more about Gozi malware, you can find additional information here.
Final thoughts
As cyber criminals continue to exploit global events like Black Friday, staying vigilant is more crucial than ever. The resurgence of Gozi malware activity highlights the importance of proactive security measures for both businesses and individuals. While the current attacks are predominantly targeting North America, we suspect this campaign will soon expand to Europe, leveraging the holiday shopping season to further its impact.
While we enjoy the convenience of online shopping, it’s vital to stay aware of the ever-present cyber threats lurking in the digital landscape. By adopting robust security practices and remaining cautious, we can reduce the risks and protect ourselves against these sophisticated attacks. Cybersecurity is not just a technical challenge—it’s a shared responsibility.
How to avoid Gozi malware
Here are some recommendations to avoid Gozi malware and protect yourself from similar threats:
- Be wary of email links. Exercise caution when opening email attachments or clicking on links, especially if they come from unknown or suspicious sources. Be particularly vigilant for phishing emails that may attempt to trick you into downloading malware.
- Increase your password security. Create strong and unique passwords for all your online accounts, including cryptocurrency exchanges and wallets. Avoid using easily guessable information and consider using a reliable password manager to securely store and manage your passwords.
- Remain vigilant online. Pay attention to any unusual behavior or unexpected requests when accessing websites, especially financial or cryptocurrency-related platforms. If you encounter unexpected pop-ups, requests for additional personal information or changes in website appearance, it could be a sign of a web-inject attempting to deceive you.
- Stay informed about the latest cybersecurity threats and best practices. Familiarize yourself with common techniques used by cyber criminals, such as phishing scams and social engineering, to avoid falling victim to their tactics.
One of the best tools to detect Gozi malware and protect your organization is IBM Security Trusteer Pinpoint Detect. The tool uses artificial intelligence and machine learning to protect digital channels against account takeover and fraudulent transactions and detect user devices infected with high-risk malware. Learn more here.
/usbank/inj[.]php
/in/sella/sella[.]php
/in/paypal/p[.]php
/in/ebay/ebay[.]php
/in/poste/po[.]php
/in/ubibanca/ub[.]php
/in/amazon/a[.]php
/in/clienti.chebanca/ch[.]php
/in/credem/cr[.]php
frcorporateonline/inj[.]php
hsbcnet/inj[.]php
/lancher/in
The post Black Friday chaos: The return of Gozi malware appeared first on Security Intelligence.

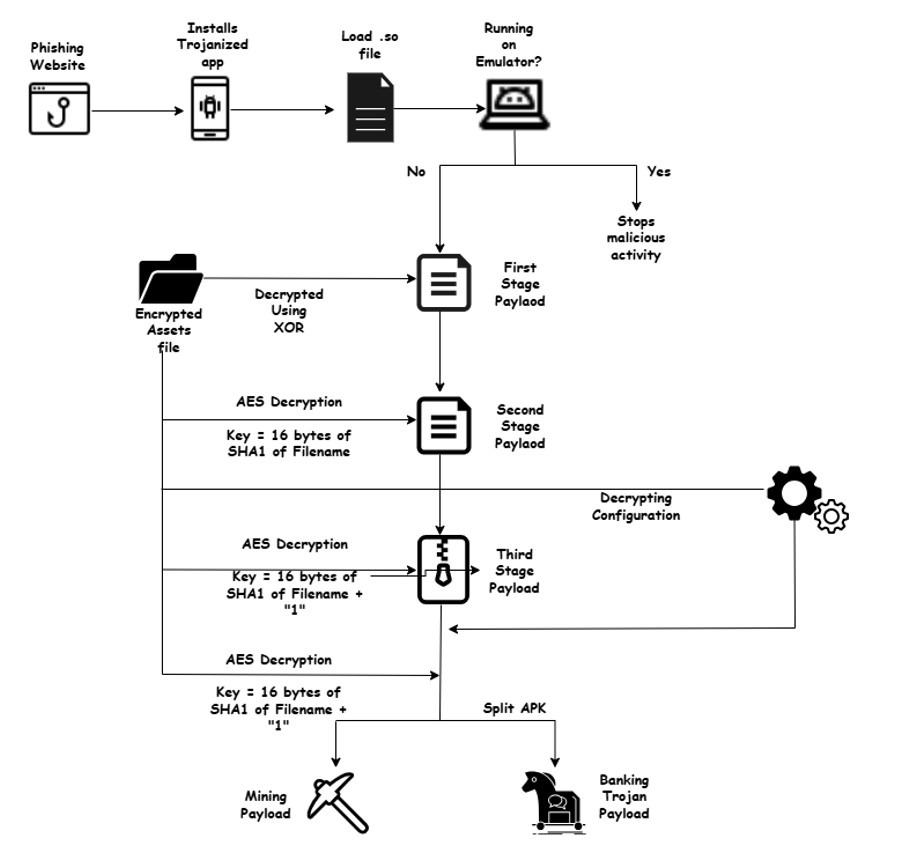 MiningDropper attack chain (Source: Cyble)[/caption]
MiningDropper’s infection chain unfolds across multiple stages:
MiningDropper attack chain (Source: Cyble)[/caption]
MiningDropper’s infection chain unfolds across multiple stages: