Operation PowerOFF: 53 DDoS domains seized and 3 Million criminal accounts uncovered
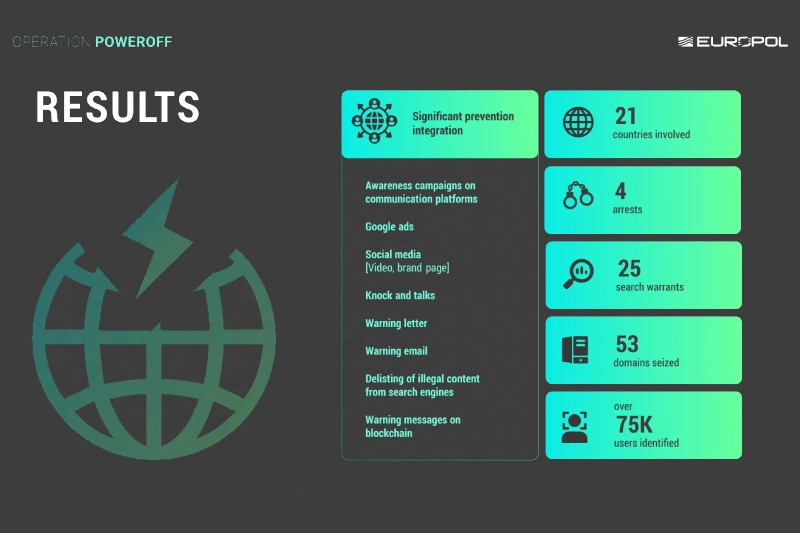
Operation PowerOFF shut down 53 DDoS-for-hire domains, arrested four suspects, and exposed data on over 3 million criminal user accounts.
Operation PowerOFF is an international law enforcement action that dismantled 53 domains linked to DDoS-for-hire services used by over 75,000 cybercriminals. Authorities arrested four suspects, seized infrastructure, and gained access to databases containing more than 3 million user accounts. They are now warning identified users, while continuing investigations with multiple search warrants.
DDoS-for-hire services, or “booters,” are illegal platforms that let users pay to launch DDoS attacks that flood websites or servers with traffic, causing outages. They are used for harassment, extortion, or disruption and can lead to serious legal consequences for users.
“On 13 April 2026, 21 countries joined forces in a coordinated action week that focused on enforcement and prevention measures against over 75 000 criminal users engaging in distributed denial-of-service (DDoS)-for-hire services.” reads the press release published by EUROPOL. “With over 75 000 warning emails and letters being sent to identified criminal users and 4 arrests, the action week also led to the takedown of 53 domains and the issuing of 25 search warrants.”

Authorities disrupted booter services by seizing servers and infrastructure used to launch attacks, limiting further harm. Access to seized databases with over 3 million user accounts enabled coordinated global actions against cybercriminals and raised awareness about the illegality of these services.
Operation PowerOFF continues with a strong prevention phase to stop future DDoS attacks. Authorities launched campaigns targeting users, including ads warning young people searching for attack tools, removal of over 100 malicious URLs, and warning messages sent via blockchains used for payments. They also updated the official website to highlight ongoing actions and raise awareness about the risks and illegality of DDoS-for-hire services.

Authorities continue dismantling global DDoS-for-hire networks under Operation PowerOFF. In August 2025, the U.S. also took down the RapperBot botnet, used for large-scale attacks across more than 80 countries since 2021.
In December 2024, law enforcement agencies operating under Operation PowerOFF disrupted 27 of the most popular platforms (including zdstresser.net, orbitalstress.net, and starkstresser.net) to launch Distributed Denial-of-Service (DDoS) attacks. The authorities also arrested three administrators of these platforms in France and Germany, and identified over 300 users.
Follow me on Twitter: @securityaffairs and Facebook and Mastodon
(SecurityAffairs – hacking, Operation PowerOFF)