Visualização de leitura
Statistics Report on Malware Targeting Windows Database Servers in Q1 2026
Statistical Report on Malware Targeting Windows Web Servers in Q1 2026
Latvia Warns of Disinformation Campaign Targeting Baltic States

Russian Information Operation Targets Baltic Societies
According to Latvian authorities, the campaign involves coordinated disinformation efforts, including the use of social media bots and targeted messaging. The operation is said to focus on Russian-speaking communities and younger audiences. Officials stated that such narratives are being amplified to create confusion and division within Baltic societies. The warning comes amid heightened concerns over hybrid threats in the region, including cyberattacks and influence operations linked to Russia. [caption id="attachment_110822" align="aligncenter" width="737"]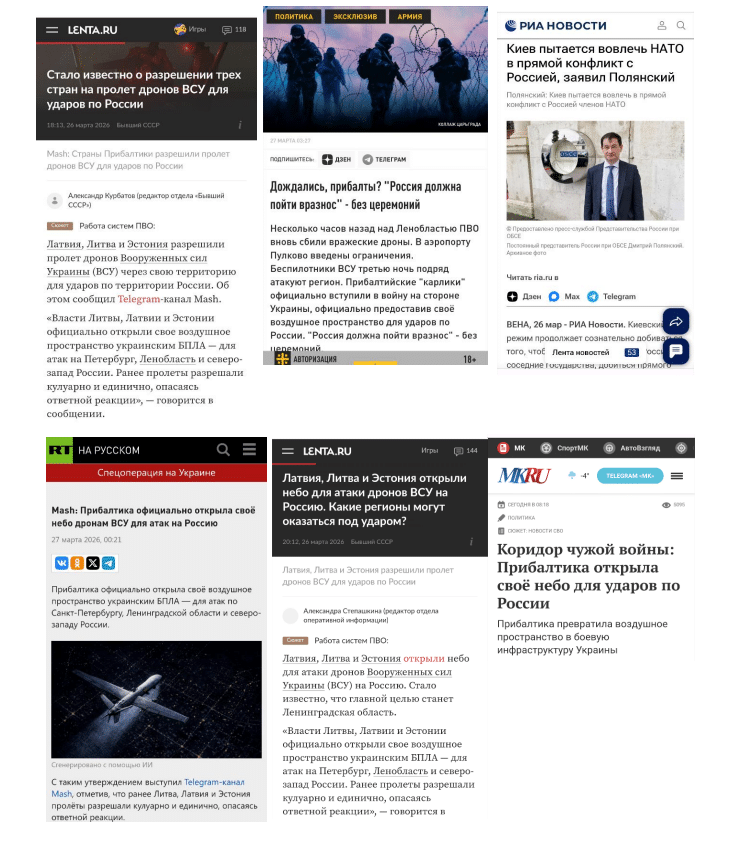 Image Source: Ministry of Defence of Latvia[/caption]
Image Source: Ministry of Defence of Latvia[/caption]
Ukrainian Drone Incidents Used to Amplify Claims
The Russian information operation follows recent reports of Ukrainian drones entering Baltic airspace during large-scale attacks on Russian infrastructure. Authorities in Latvia and Estonia confirmed that two drones entered their airspace earlier this week via Russia. One drone reportedly struck a chimney at a power station near the Estonian border, while another crash-landed. Lithuania also reported a separate incident where a drone fell into a frozen lake. Officials said there were no casualties or significant damage from these incidents. The drones are believed to have been part of a broader Ukrainian operation targeting Russian oil facilities, including ports along the Baltic Sea.No Direct Involvement by Baltic States
Latvian authorities stressed that the Russian information operation is attempting to link these drone incidents to alleged Baltic involvement, which they deny. The Ministry noted that Ukraine has the right to defend itself against Russia’s invasion and that Baltic support does not extend to operational involvement in military actions. Officials also suggested that such claims are intended to divert attention from Russia’s own challenges in countering Ukrainian strikes. [caption id="attachment_110823" align="aligncenter" width="751"]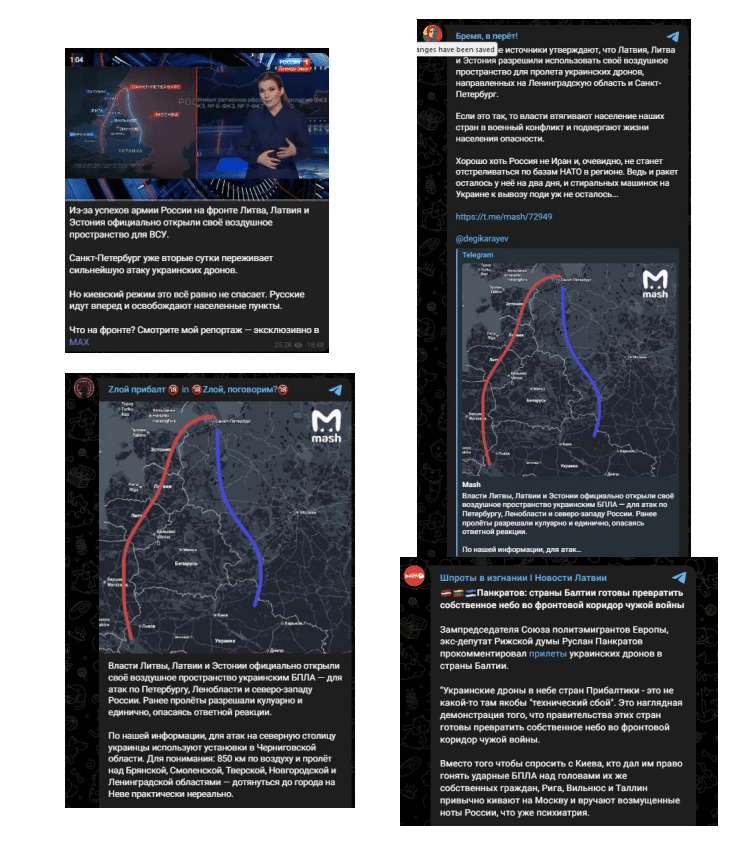 Image Source: Ministry of Defence of Latvia[/caption]
Image Source: Ministry of Defence of Latvia[/caption]
Growing Focus on Hybrid Threats
The latest warning adds to ongoing concerns about hybrid activities in the Baltic region. Earlier this year, Latvian security services reported that cyberattacks and sabotage operations linked to Russia remain a significant threat. Officials have also indicated that Russia’s perception of Latvia is becoming more confrontational, drawing comparisons to its stance toward Ukraine prior to the 2022 invasion. While no immediate military threat has been identified, authorities say information operations remain a key tool being used to influence public opinion and destabilize the region.Monitoring and Response Ongoing
Latvia’s Ministry of Defence said it continues to monitor the Russian information operation and assess its impact across the Baltic States. The government has urged vigilance against disinformation and reiterated its commitment to supporting Ukraine within the framework of international law. The situation remains under observation as authorities track both the spread of false narratives and related security developments in the region.Criminals are renting virtual phones to bypass bank security
Researchers at Group-IB warn about criminals using virtual Android devices to bypass modern security solutions.
Cloud phones are virtual Android devices that can fully mimic real device fingerprints (model, hardware, IP, timezone, sensor data, behavior). This allows them to undermine banks’ device‑based fraud detection.
Originally, phone farms were made up of physical devices and were set up for testing. They grew in number when companies found out they could rent virtual phones and artificially raise engagement stats like follower counts, likes, shares, and so on. Further growth was driven by moving the infrastructure from physical phone farms to cloud phones.
At some point, cybercriminals figured out how to use these “rent-a-phones” to trick people into sharing access to banking accounts and crypto wallets, which were then emptied.
Banks caught on to these tactics and started building mobile apps that rely on device fingerprinting. This helped them detect and block fake devices taking over people’s accounts.
But as with any arms race, criminals found a way around that too. They now “pre‑warm” devices by adding banking apps, registering credentials, and running small transactions so accounts and device telemetry look low‑risk.
The researchers note that:
“They moved to cloud phones—remote-access Android devices running in data centers. For all intents and purposes, these are real phones, running genuine firmware, exhibiting natural sensor behavior, and presenting valid hardware attestation.”
And it’s not a big investment for the criminals. Major cloud phone platforms offer device rentals for as little as $0.10-0.50 per hour, making fraud infrastructure accessible to almost anyone.
One place these devices are used is in mobile games with real-money economies. These games have long struggled with a specific problem: bot farming of in-game currency and resources. In many cases, automated accounts can generate in-game items that have real-world value.
Banks face a different problem: account take-over (ATO) attacks. As banking shifted from web browsers to mobile apps, they needed more reliable and comprehensive ways to identify trusted devices. Many banks now bind accounts to specific devices and flag transfers that don’t come from that device.
The start of an attack is still social engineering. Criminals try to trick users into sharing one-time passwords (OTPs), approve a login, or make a transfer “to a safe account.”
Behind the scenes, the criminal logs into a cloud phone instance that already looks like the victim’s device to their bank, thanks to matching or plausible fingerprints and pre‑warmed behavior.
Once the criminals are in, they carry out authorized push payment (APP) transfers (often to money‑mule accounts), that the bank’s systems may treat as low‑risk because nothing about the device seems obviously wrong.
At that point the criminals can start emptying your account or sell the virtual phones to other criminals. According to the researchers:
“Darknet markets actively trade pre-verified dropper accounts created on cloud phones, with Revolut and Wise accounts priced at $50-200 each, often including continued access to the cloud phone instance.”
How to stay safe
The Group-IB researchers advise end users to:
- Never complete account verification processes under third-party instruction. Keep in mind that banks and government institutions will not ask customers to authenticate accounts through unfamiliar apps or remote environments.
- Enable device-based security features. Use official mobile banking apps, biometric authentication, and strong device-level security settings.
- Be cautious of “easy income” schemes involving bank accounts. Fake job offers requiring you to “verify” bank accounts, government officials requesting account verification, bank representatives asking you to move money to “safe” accounts.
- If you suspect that you have been targeted, contact your bank immediately. Update passwords and enable multi-factor authentication on all accounts.
We’d like to add:
- Turn on banking alerts for logins, payee changes and transactions where possible so you see unusual activity immediately.
- Use an up-to-date, real-time anti-malware solution for your Android device to detect and stop information stealers.
- When in doubt about a message, consult Malwarebytes Scam Guard. It will help you figure out if it’s a scam and guide you through what to do.
We don’t just report on phone security—we provide it
Cybersecurity risks should never spread beyond a headline. Keep threats off your mobile devices by downloading Malwarebytes for iOS, and Malwarebytes for Android today.
Russia establishes Vienna as key western spy hub targeting NATO
Russia uses Vienna as its largest Western spy hub, monitoring NATO and other sensitive communications via diplomatic sites and satellite dishes.
Western intelligence reports that Russia has transformed Vienna into its largest Western spy hub, steadily expanding surveillance over the past two years. Using diplomatic compounds and rooftop satellite clusters, Russia monitors sensitive communications across NATO, the Middle East, and Africa, reviving a major Cold War-era signals intelligence operation, according to the Financial Times.
“This is one of our main concerns,” a senior European diplomat in Vienna told the Financial Times. “They are targeting NATO government and military communications… Vienna is their hub in Europe.”
Western intelligence reports Russia steadily expanding surveillance in Vienna, with moving antennas and rooftop dishes actively tracking satellites, even adjusting them around major events like the Munich Security Conference.
At Vienna’s “Russencity,” a nine-acre Russian compound, satellite dishes track Europe-Africa communications via geostationary satellites, with movable lenses enhancing signal capture. The complex includes residences, a school, and Russia’s UN mission, revealing advanced espionage capabilities.
The most expensive piece of the Cold War that never ended is a building in central Vienna, and it's still on the clock. Russia's "Russencity" compound in Vienna, a nine-acre complex on the Danube, has SIGINT satellite dishes on its rooftops that face West. They reposition… pic.twitter.com/EITk29aaHm
— Lukasz Olejnik (@lukOlejnik) March 17, 2026
“Russencity” houses residences, a school, and the UN mission, topped with satellite dishes mainly pointing west to 18 geostationary satellites. Researchers identified four in use (Eutelsat 3B, 10B, SES-5, and Rascom QAF1) for Europe-Africa communications, with movable lenses allowing wider satellite coverage. Russencity is just one site; others include the embassy, cultural center, a former sanatorium, and upgraded apartments with rooftop equipment. Dating to 1983 under KGB chief Yuri Andropov, the complex was likely built for intelligence work, and Vienna has become a hub for Russian espionage in Europe.
Russia has around 500 diplomats in Vienna, with up to a third likely covert spies; Austria warns that Russian SIGINT stations present a serious security risk.
Austria’s intelligence warns Russian surveillance poses a major risk, but the law limits action to espionage targeting Austria, so authorities avoid expulsions to prevent Moscow retaliation.
“Austria’s intelligence agency (DSN) has warned that Russia’s surveillance capabilities in Vienna pose a “significant security risk.”” concludes Kyiv Post. “But Austrian law limits action – espionage is only prosecutable if it targets Austria directly. Authorities have identified individuals running the operations but have avoided expulsions, fearing retaliation from Moscow.”
Follow me on Twitter: @securityaffairs and Facebook and Mastodon
(SecurityAffairs – hacking, NATO)
iPhone and iPad are the first consumer devices cleared for NATO ‘RESTRICTED’ classification
Apple’s iPhone and iPad are now NATO-approved for classified use, listed in the alliance’s Information Assurance Product Catalogue.
Apple announced that its iPhone and iPad have received NATO approval to handle classified information. The devices are now officially listed in the NATO Information Assurance Product Catalogue (NIAPC), allowing military personnel to use them securely for sensitive communications and operations.
Devices listed in the NATO Information Assurance Product Catalogue (NIAPC) are commercial security products built in NATO member states, designed to protect NATO or national classified information. They meet strict information security standards, undergo NATO or national vetting, hold recognized certifications like Common Criteria or INFOSEC approvals, and receive explicit approval for handling classified data, often up to levels such as NATO Restricted or NATO Secret.
iPhone and iPad are the first consumer devices cleared for NATO’s ‘RESTRICTED’ classification.
“iPhone and iPad with indigo configuration provide secure access to Mail, Calendar, and Contacts data using apps built for iPhone and iPad.” reads the announcement. “iOS 26 and iPadOS 26 with indigo configuration is approved for iPhone and iPad up to NATO RESTRICTED. Indigo doesn’t require any special additional software or settings beyond managing and supervising devices using a device management service.”
Apple iNDIGO (iOS Native Devices in Government Operation) is a hardened, government-specific configuration for iOS and iPadOS devices, approved by Germany’s BSI for classified info like VS-NfD (German Secret).
Apple confirmed that the NIAPC “indigo configuration” is just a naming by the German BSI and that standard iPhone and iPad setups received NATO approval.
Apple devices use Touch ID and Face ID for fast, secure access, offer Memory Integrity Enforcement on A19/M5 chips, and support VPNs..
Follow me on Twitter: @securityaffairs and Facebook and Mastodon
(SecurityAffairs – hacking, iPhone)
Apple Devices Become First Consumer Products Cleared for NATO Classified Data—But Questions Remain

iPhone and iPad running iOS 26 can now handle restricted NATO information without special software, though security experts warn consumer devices create new attack surfaces.
Apple announced Thursday that iPhone and iPad became the first consumer mobile devices approved to handle classified NATO information up to the restricted level, following extensive security testing by Germany's Federal Office for Information Security.
The certification enables NATO personnel across all member nations to use standard iOS 26 and iPadOS 26 devices for restricted data without requiring specialized software, containerization or additional security layers—a milestone no other consumer device manufacturer has achieved.
Germany's BSI conducted exhaustive technical assessments, comprehensive testing and deep security analysis to verify Apple's built-in platform security capabilities met NATO nations' operational and assurance requirements. The devices now appear on NATO's Information Assurance Product Catalogue, formally recognizing that Apple's hardware-software integration provides adequate protections for restricted classified information.
Also read: NATO Faces Escalating Cyberthreats: From Espionage to Disinformation
"Secure digital transformation is only successful if information security is considered from the beginning in the development of mobile products," said Claudia Plattner, BSI's president. The certification builds on Apple's previous approval to handle classified German government data using native iOS and iPadOS security measures without third-party modifications.
Apple stressed that its security architecture differs fundamentally from traditional approaches requiring bespoke solutions. "Prior to iPhone, secure devices were only available to sophisticated government and enterprise organizations after a massive investment in bespoke security solutions," said Ivan Krstić, Apple's vice president of Security Engineering and Architecture. "Instead, Apple has built the most secure devices in the world for all its users, and those same protections are now uniquely certified under assurance requirements for NATO nations."
The certification relies on Apple's integrated security features including hardware-based encryption through the Secure Enclave processor, biometric authentication via Face ID, Memory Integrity Enforcement preventing code injection attacks, and comprehensive device encryption that protects data at rest and in transit. These capabilities operate across Apple's custom silicon, operating system and applications without requiring users to enable special modes or install government-specific software.
NATO's "restricted" classification represents the alliance's lowest tier for classified information, covering data requiring protection but not meeting thresholds for confidential, secret or top secret designations. Restricted information typically includes operational planning details, logistics coordination and administrative documents that could aid adversaries if disclosed but would not directly compromise critical security operations.
The approval marks a pragmatic shift in how governments balance security requirements against operational flexibility. NATO personnel can now use familiar consumer devices rather than specialized hardened phones that typically cost thousands of dollars per unit, offer limited functionality and create friction in daily workflows. The consumer device approval potentially saves member nations substantial procurement costs while improving user adoption.
However, security experts note that consumer devices certified for government use introduce considerations absent from purpose-built secure communications platforms. Unlike specialized government phones designed exclusively for classified communications, iPhones and iPads run consumer applications, connect to public networks and integrate with cloud services creating expanded attack surfaces.
A cryptography professor at a known U.S. University, told The Cyber Express that he would still want to be cautious on this since in the past few years, Apple's security architecture has been proven to have consumer threats, including nation-state adversaries targeting NATO countries. "The question isn't whether Apple has good security—they do. It's whether consumer devices designed for billions of users can adequately protect against targeted attacks by adversaries specifically hunting for NATO intelligence," he said.
Also read: Apple Patches Actively Exploited iOS Zero-Day CVE-2025-24200 in Emergency Update
The certification also raises questions about long-term support and update requirements. Consumer devices receive operating system updates for limited periods before Apple designates them obsolete. Government security requirements typically demand decades-long support commitments that conflict with consumer product lifecycles where devices become outdated within five years.
Apple has not disclosed whether NATO members negotiated extended support agreements, how the company will handle security vulnerabilities discovered in iOS 26 after consumer support ends, or whether classified data handling requires organizations to prevent users from installing consumer applications that could introduce risks.
The announcement follows Apple's decade-long effort to gain U.S. government security clearances. The U.S. Department of War (formerly know as Department of Defense) approved iPhones for handling certain classified information in 2013-14, though those implementations required mobile device management software and container applications separating classified data from personal use—requirements NATO's certification explicitly eliminates.
Despite concerns, the NATO approval represents validation that Apple's security-by-design approach can meet rigorous government standards for protecting sensitive information, potentially encouraging other consumer technology manufacturers to prioritize security architecture capable of government certification rather than relying on post-hoc security layers.