
The FBI Internet Crime Report 2025 shows just how expensive cybercrime has become. In 2025, the
FBI’s Internet Crime Complaint Center (IC3) received over one million complaints, with reported losses touching $20.8 billion, the highest ever recorded.
That figure is not just a statistic. It reflects everyday incidents, individuals losing life savings to investment scams, businesses wiring money to fraudulent accounts, and organizations dealing with disruptions from
ransomware attacks. What used to be isolated cases are now happening at scale.
The FBI Internet Crime Report 2025 also shows how the nature of
cybercrime is changing.
Fraud is no longer limited to suspicious emails or obvious scams. Criminals are using social platforms, messaging apps, and now even
artificial intelligence to make their operations look legitimate. In many cases, victims don’t realize they are being targeted until the money is already gone.
At the same time, the report highlights that law enforcement is trying to keep pace. Operations targeting
crypto scams and international fraud networks are making an impact, but the overall trend shows that cybercrime is expanding faster than it is being contained.
Cyber-Enabled Fraud Remains the Biggest Driver
A large share of these losses comes from cyber-enabled fraud, which alone accounts for nearly
85% of the total financial damage, or about $17.7 billion.
Investment fraud continues to cause the most damage. In 2025, it led to $8.6 billion in losses, followed by business email compromise (BEC) and
tech support scams.
Within this,
cryptocurrency investment fraud stands out. Losses linked to crypto scams reached $7.2 billion, making it the biggest single category.
[caption id="attachment_111088" align="aligncenter" width="577"]
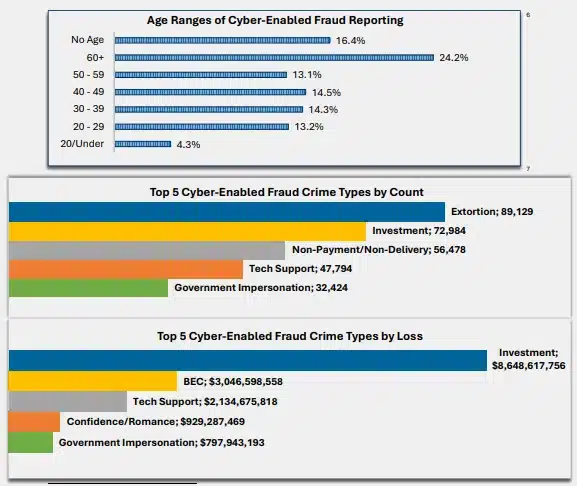
Image Source: FBI Report[/caption]
These scams are no longer basic
phishing attempts. Attackers spend time building trust, approaching victims through social media, messaging apps, or even dating platforms. Once trust is established, victims are guided toward fake investment platforms that show fabricated profits. By the time withdrawals are attempted, the money is gone.
AI-Enabled Scams Are Growing Fast
The FBI Internet Crime Report 2025 includes a separate section on
AI-enabled scams for the first time, and the early numbers are already concerning.
- More than 22,000 complaints linked to AI
- Around $893 million in losses
AI is making scams more convincing. Fake profiles, cloned voices, and realistic conversations can now be created quickly and at scale. This allows attackers to run highly targeted campaigns without much effort.
The challenge is that these scams often look legitimate, making it harder for individuals and even businesses to identify red flags in time.
Ransomware Continues to Target Critical Sectors
Ransomware remains a steady threat, especially for critical infrastructure.
- Over 3,600 complaints reported in 2025
- Losses crossed $32 million
The actual impact is likely much higher. Many organizations do not report full losses, especially indirect costs like downtime or recovery expenses.
The report also notes 63 new
ransomware variants identified during the year, showing how quickly these attacks continue to evolve.
Sectors such as healthcare, manufacturing, and government facilities remain frequent targets, where even short disruptions can have serious consequences.
FBI Operations Are Preventing Some Losses
The report also highlights efforts by law enforcement to limit the damage.
One example is Operation Level Up, focused on
cryptocurrency investment scams. Since its launch in 2024, the initiative has helped reduce potential losses by more than $500 million.
In many cases, victims did not realize they were being scammed until they were contacted. This reflects a larger issue, many
cyber fraud cases go unnoticed until significant financial damage has already occurred.
Cybercrime Is Becoming More Structured
The report also points to broader trends.
Cybercriminal groups are operating more like organized businesses. At the same time, state-linked actors are becoming more active, targeting infrastructure and sensitive
data.
One example highlighted is the DPRK IT worker
scam, where individuals posing as remote IT workers gain access to company systems and use that access for data theft or further attacks.
These developments show that
cybercrime is no longer limited to isolated incidents. It is part of a larger, global ecosystem.
A Growing Gap Between Threats and Preparedness
The FBI
Internet Crime Report 2025 shows a clear pattern—cybercrime is scaling faster than awareness and response.
- Fraud tactics are becoming more personal and long-term
- AI is helping attackers improve success rates
- Cryptocurrency is making transactions harder to trace
While recovery efforts and law enforcement actions are improving, most interventions still happen after the damage is done.
Final Take on FBI Internet Crime Report 2025
The FBI Internet Crime Report 2025 highlights a shift in how cybercrime operates today. The scale—over $20 billion in losses—is significant, but the methods behind these numbers are just as important.
From cyber-enabled fraud to AI-enabled scams and cryptocurrency investment fraud, attackers are using a mix of technology and human psychology to succeed.
For individuals and organizations, the
risk is no longer occasional—it is constant, and it is evolving.


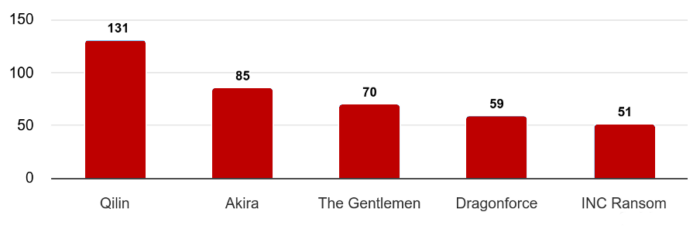

 Image Source: FBI Report[/caption]
These scams are no longer basic
Image Source: FBI Report[/caption]
These scams are no longer basic 