Europe Moves to Tighten AI Rules While Easing Compliance Burden



The Italian Data Protection Authority fine against Poste Italiane and Postepay has reached over €12.5 million, after regulators found unlawful processing of personal data affecting millions of users.
Italy’s Italian Data Protection Authority imposed a €6.6 million penalty on Poste Italiane and €5.8 million on Postepay. The action follows an investigation launched in April 2024 after multiple complaints from users regarding how their data was being handled through mobile applications.
The Italian Data Protection Authority fine centers on how BancoPosta and Postepay apps collected user data. Customers were required to allow monitoring of information stored on their devices, including details about installed and active applications.
According to the companies, this access was necessary to detect malware and prevent fraud in line with payment security requirements. However, the regulator found that the scope of monitoring went too far.
Authorities stated that the data collection methods were not proportionate and resulted in excessive intrusion into users’ private lives. The ruling emphasized that fraud prevention cannot justify blanket access to personal device data.
The investigation behind the Italian Data Protection Authority fine also revealed broader compliance failures. Regulators flagged insufficient transparency in how users were informed about data collection practices.
The companies were also found to have not conducted an adequate Data Protection Impact Assessment. Such assessments are required when processing activities pose high risks to individual privacy.
Further issues included weak security measures, unclear policies on how long data was stored, and irregularities in defining data controller responsibilities. These gaps raised concerns about how user data was governed internally.
As part of the enforcement action, both companies have been ordered to stop the disputed data processing practices if still ongoing. They must also align their data retention policies with regulatory requirements and report compliance to the Authority.
WhatsApp is testing usernames that could let users chat without sharing phone numbers, adding a new privacy layer now rolling out to some beta users.
The post WhatsApp New Update Lets You Chat Without Sharing Your Phone Number appeared first on TechRepublic.
A widespread outage disrupted banking apps and payment systems across Russia, leaving customers unable to pay by card, withdraw cash, or access mobile banking for hours. According to The Record Media, the incident affected major banks, including Sberbank, VTB, Alfa-Bank, T-Bank, and Gazprombank, and impacted multiple regions, including Moscow.
“The combined client base of VTB , Sberbank, T-Bank , and Alfa-Bank amounts to tens of millions of people across the country. Apparently, the scale of the outage is colossal and affects most regions of Russia. Complaints number in the thousands.” reported the Russian website CNews. “For example, in just one hour, more than 3,300 complaints were filed about a Sberbank outage. Over the past 12 hours, 35% of complaints came from Moscow, 8% each from St. Petersburg and the Sverdlovsk region , and 7% and 5% from the Novosibirsk and Chelyabinsk regions .”

Media say the outage comes as Russia tightens internet control, restricting apps and cracking down on VPN use.
“Russia’s major banks faced large-scale disruptions to their electronic services on April 3, according to online tracking data and customer reports.” reports Kyiv Independent. “The outage comes as the Russian government has increasingly tightened control over internet access in the country, imposing restrictions on popular apps and seeking to clamp down on the use of virtual private networks (VPNs).“
A temporary outage on April 3 affected Sberbank and spread to other major banks, including VTB Bank and T-Bank. Starting around 10 a.m. Moscow time, customers faced issues with mobile apps, transfers, and ATM withdrawals, forcing many businesses to accept only cash and causing long lines across cities.
Russia’s National Payment Card System said the disruption was due to a technical failure at one bank and did not affect funds. Reports from Kommersant linked it to a Sberbank glitch, possibly worsened by VPN use, shortly after plans to curb VPNs.
“The mass outage comes less than a week after Russia’s Digital Development Minister Maksut Shadayev said on March 30 that the government will work to “reduce the use of VPNs” — one of the few remaining ways for Russian citizens to bypass online censorship.” continues the Kyiv Independent. “Shadayev reportedly asked telecom operators and digital platforms to introduce fees and block users for using VPN services following an order by Russian President Vladimir Putin.”
Local security experts speculate that blocking VPNs likely contributed to the April 3 banking outage, describing it as possible “friendly fire” in comments to Kommersant. Russian authorities have steadily tightened online censorship since the war in Ukraine began, with restrictions accelerating in recent months. In early March, the Kremlin introduced a whitelist system allowing access only to selected, mostly pro-government sites during mobile internet outages. Internet shutdowns have become more frequent, officially justified as security measures against Ukrainian drone attacks.
The Record Media also reported that the outage also impacted public transport, with Moscow metro and suburban train turnstiles unable to accept cards, forcing staff to let passengers pass for free to avoid crowding.
By Monday, reports had largely vanished from many sites. Independent media said the Russian Internet watchdog Roskomnadzor ordered outlets to remove content linking the banking outage to its VPN-blocking efforts.
Follow me on Twitter: @securityaffairs and Facebook and Mastodon
(SecurityAffairs – hacking, Russian banking apps)
The FBI is warning Americans about data security risks tied to foreign-developed mobile apps, especially those linked to China.
The post New FBI Warning: Chinese Apps Could Expose User Data appeared first on TechRepublic.
Samsung will discontinue its Messages app in July 2026, pushing users to Google Messages with RCS, AI, and security upgrades.
The post Samsung to Shut Down Its Messaging App, Switch to Google Messages in July appeared first on TechRepublic.
NoVoice malware was found in 50 Android apps on Google Play, with 2.3 million downloads, by bypassing detection and targeting outdated devices.
The post Android Alert: 50 Google Play Apps Linked to ‘NoVoice’ Malware Reached 2.3M Downloads appeared first on TechRepublic.


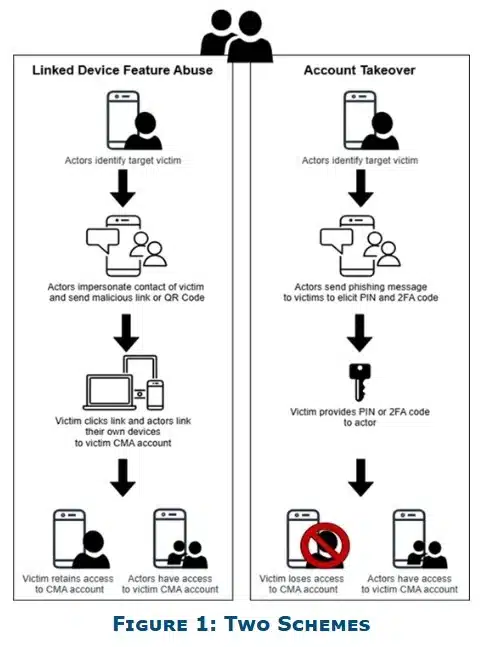 Image Source: FBI[/caption]
If a user complies, attackers can link their own device to the account or take full control.
In some cases, attackers may escalate their tactics by deploying malware, making the campaign more persistent and difficult to contain.
Notably, reporting suggests that platforms like Signal have been specifically targeted, though similar methods can be applied across other messaging apps.
[caption id="attachment_110553" align="aligncenter" width="948"]
Image Source: FBI[/caption]
If a user complies, attackers can link their own device to the account or take full control.
In some cases, attackers may escalate their tactics by deploying malware, making the campaign more persistent and difficult to contain.
Notably, reporting suggests that platforms like Signal have been specifically targeted, though similar methods can be applied across other messaging apps.
[caption id="attachment_110553" align="aligncenter" width="948"]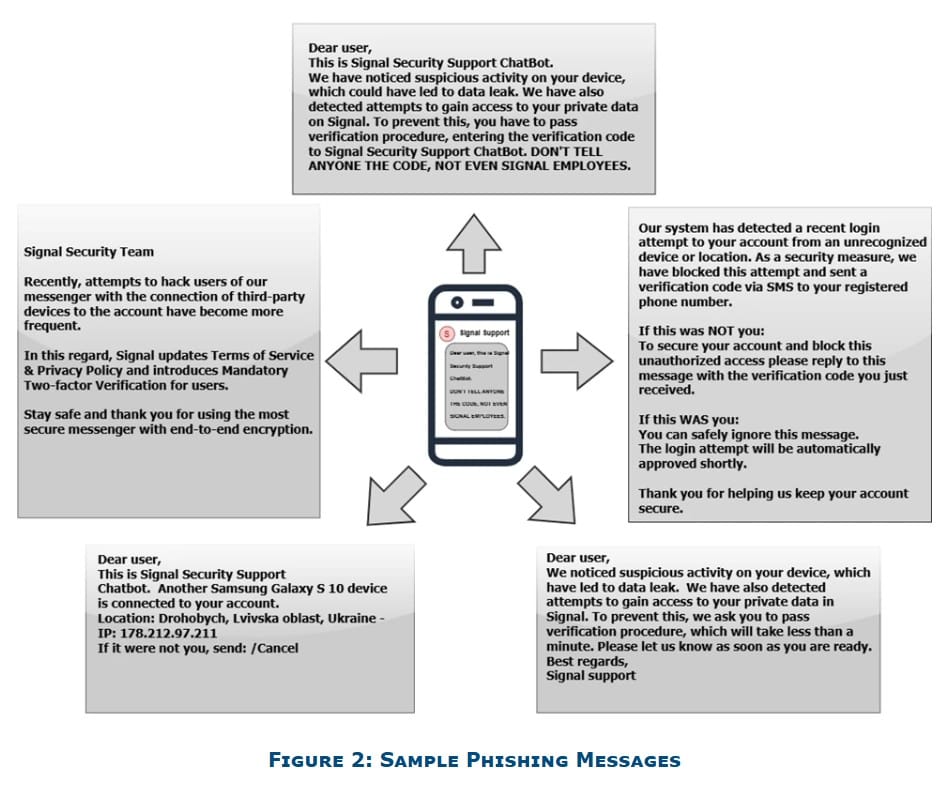 Image Source: FBI[/caption]
Image Source: FBI[/caption]
In a move that bucks the entire industry trend, TikTok has confirmed it will not implement end-to-end encryption (E2EE) for direct messages on its platform — arguing that E2EE would make users less safe. We break down what’s really going on: the child safety argument, the privacy counterargument, the geopolitical questions surrounding ByteDance, and what […]
The post TikTok Says No to End-to-End Encryption: Here’s Why That’s a Big Deal appeared first on Shared Security Podcast.
The post TikTok Says No to End-to-End Encryption: Here’s Why That’s a Big Deal appeared first on Security Boulevard.
Oversecured flagged 1,575 flaws in 10 Android health apps with 14.7M installs, putting chats, CBT notes, and mood logs at risk, per BleepingComputer.
The post Millions at Risk as Android Mental Health Apps Expose Sensitive Data appeared first on TechRepublic.
This article was originally published in EdTech Magazine on 02/11/26 by Didi Gluck. As ransomware and phishing attacks grow more sophisticated, districts can’t rely on perimeter defenses alone. Cybersecurity has become a top priority for K–12 districts, not just to keep students safe online but to ensure continuity across devices, systems and end user accounts. ...
The post EdTech Magazine | What Minimum Viable Cybersecurity Looks Like for K–12 Districts appeared first on ManagedMethods Cybersecurity, Safety & Compliance for K-12.
The post EdTech Magazine | What Minimum Viable Cybersecurity Looks Like for K–12 Districts appeared first on Security Boulevard.
We’re seeing a surge in phishing calendar invites that users can’t delete, or that keep coming back because they sync across devices. The good news is you can remove them and block future spam by changing a few settings.
Most of these unwanted calendar entries are there for phishing purposes. Most of them warn you about a “impending payment” but the difference is in the subject and the action they want the target to take.
Sometimes they want you to call a number:
And sometimes they invite you to an actual meeting:

We haven’t followed up on these scams, but when attackers want you to call them or join a meeting, the end goal is almost always financial. They might use a tech support scam approach and ask you to install a Remote Monitoring and Management tool, sell you an overpriced product, or simply ask for your banking details.
The sources are usually distributed as email attachments or as download links in messaging apps.
This blog focuses on how to remove these unwanted entries. One of the obstacles is that calendars often sync across devices.
If you use Outlook:
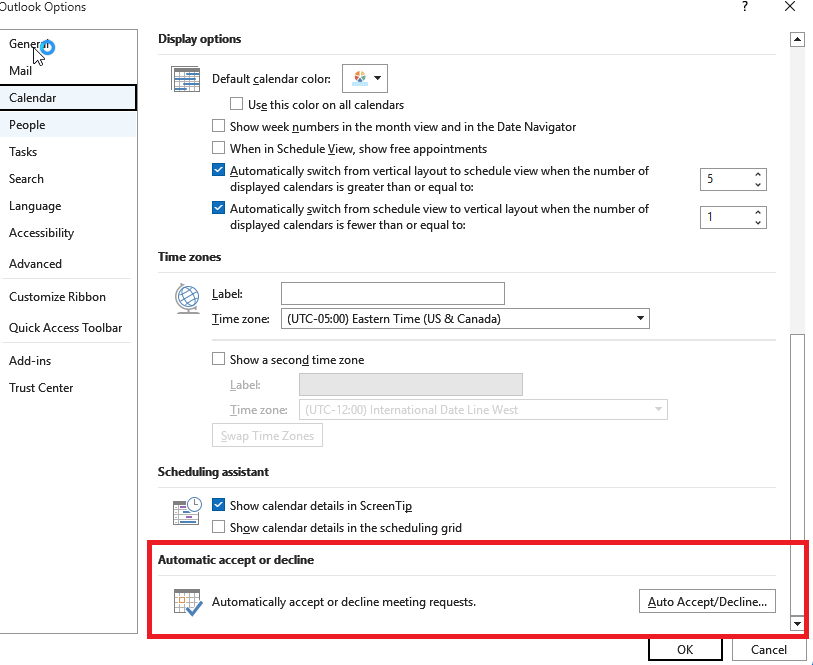
To disable automatic calendar additions:
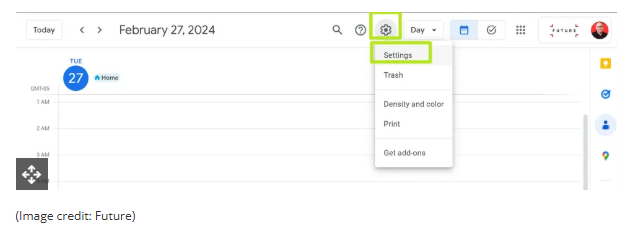
To prevent unknown senders from adding invites:
For help reviewing which apps have access to your Android Calendar, refer to the support page.
To control how events get added to your Calendar on a Mac:
The controls are similar to macOS, but you may also want to remove additional calendars:
Which brings me to my next point. Check both the Outlook Calendar and the mobile Calendar app for Additional Calendars or subscribed URLs and Delete/Unsubscribe. This will stop the attacker from being able to add even more events to your Calendar. And looking in both places will be helpful in case of synchronization issues.
Several victims reported that after removing an event, they just came back. This is almost always due to synchronization. Make sure you remove the unwanted calendar or event everywhere it exists.
Tracking down the source can be tricky, but it may help prevent the next wave of calendar spam.
We’ve covered some of this already, but the main precautions are:
Pro tip: If you’re not sure whether an event is a scam, you can feed the message to Malwarebytes Scam Guard. It’ll help you decide what to do next.

We don’t just report on threats—we remove them
Cybersecurity risks should never spread beyond a headline. Keep threats off your devices by downloading Malwarebytes today.
As we careen toward a future in which Google has final say over what apps you can run, the company has sought to assuage the community's fears with a blog post and a casual "backstage" video. Google has said again and again since announcing the change that sideloading isn't going anywhere, but it's definitely not going to be as easy. The new information confirms app installs will be more reliant on the cloud, and devs can expect new fees, but there will be an escape hatch for hobbyists.
Confirming app verification status will be the job of a new system component called the Android Developer Verifier, which will be rolled out to devices in the next major release of Android 16. Google explains that phones must ensure each app has a package name and signing keys that have been registered with Google at the time of installation. This process may break the popular FOSS storefront F-Droid.
It would be impossible for your phone to carry a database of all verified apps, so this process may require Internet access. Google plans to have a local cache of the most common sideloaded apps on devices, but for anything else, an Internet connection is required. Google suggests alternative app stores will be able to use a pre-auth token to bypass network calls, but it's still deciding how that will work.


© Ryan Whitwam
Join a loyalty scheme and you often get a reward or discount on your special day – but it may have strings attached
Celebrating your birthday isn’t just about getting presents and cards from family and friends. Signing up to loyalty schemes and newsletters can give you access to a host of freebies, deals and discounts from retailers to mark the big day.
With my birthday on the horizon I decided to look at what was on offer, and see which gifts came with some small print.
Continue reading...
© Photograph: Oleksandr Latkun/Getty

© Photograph: Oleksandr Latkun/Getty
Gathering data used to be a fringe pursuit of Silicon Valley nerds. Now we’re all at it, recording everything from menstrual cycles and mobility to toothbrushing and time spent in daylight. Is this just narcissism redesigned for the big tech age?
I first heard about my friend Adam’s curious new habit in a busy pub. He said he’d been doing it for over a year, but had never spoken to anyone about it before. He had a furtive look around, then took out his phone and showed me the product of his burning obsession: a spreadsheet.
This was not a record of his annual tax return or numbers he was crunching for work (Adam is a data scientist). Instead, it was a spreadsheet recording the minutiae of his life, with dozens of columns tracking every element of his daily routine. It all started, he told me, because of a recurring argument with his boyfriend. His partner didn’t think they spent enough time together, but Adam thought that they did. There was only one way to settle this, he decided: cold, hard data. So he began keeping a note of the days they saw each other and the days they didn’t.
Continue reading...
© Illustration: Carl Godfrey/The Guardian

© Illustration: Carl Godfrey/The Guardian