Meta Pauses Work With Mercor After Data Breach Puts AI Industry Secrets at Risk



Unit 42 uncovers multiple clusters of cyberespionage targeting a Southeast Asian government organization with USBFect, RATs and loaders.
The post Converging Interests: Analysis of Threat Clusters Targeting a Southeast Asian Government appeared first on Unit 42.

Discover the best VoIP routers for businesses in 2025. Easily compare range, transfer rates, connectivity types, price, and more.
The post The 5 Best VoIP Routers (Wired, Wireless, and Mesh) in 2026 appeared first on TechRepublic.

Akamai researchers saw a 245% spike in cyberattacks in the first two weeks after the start of the U.S. and Israeli war against Iran as Iranian nation-state groups and independent hacktivists launch increasingly decentralized and destructive cyberattacks, which are expected to increase as long as the kinetic battle continues.
The post Cyberattacks Spike 245% in the Two Weeks After the Start of War With Iran appeared first on Security Boulevard.
Iranian threat group Boggy Serpens' cyberespionage evolves with AI-enhanced malware and refined social engineering. Unit 42 details their persistent targeting.
The post Boggy Serpens Threat Assessment appeared first on Unit 42.

Hackers are impersonating IT staff in Microsoft Teams to trick employees into installing malware, giving attackers stealthy access to corporate networks.
The post Hackers Pose as IT Staff in Microsoft Teams to Install Malware appeared first on TechRepublic.
Explore the tools Unit 42 found on a Muddled Libra rogue host. Learn how they target domain controllers and use search engines to aid their attacks.
The post A Peek Into Muddled Libra’s Operational Playbook appeared first on Unit 42.

In 2025 a threat group compromised government and critical infrastructure in 37 countries, with reconnaissance in 155.
The post The Shadow Campaigns: Uncovering Global Espionage appeared first on Unit 42.

Operators behind RansomHouse, a ransomware-as-a-service (RaaS) group, have upgraded their encryption methods from single-phase to complex and layered.
The post From Linear to Complex: An Upgrade in RansomHouse Encryption appeared first on Unit 42.

Hamas-affiliated threat actor Ashen Lepus (aka WIRTE) is conducting espionage with its new AshTag malware suite against Middle Eastern government entities.
The post Hamas-Affiliated Ashen Lepus Targets Middle Eastern Diplomatic Entities With New AshTag Malware Suite appeared first on Unit 42.

A prolific cybercriminal group that calls itself “Scattered LAPSUS$ Hunters” has dominated headlines this year by regularly stealing data from and publicly mass extorting dozens of major corporations. But the tables seem to have turned somewhat for “Rey,” the moniker chosen by the technical operator and public face of the hacker group: Earlier this week, Rey confirmed his real life identity and agreed to an interview after KrebsOnSecurity tracked him down and contacted his father.
Scattered LAPSUS$ Hunters (SLSH) is thought to be an amalgamation of three hacking groups — Scattered Spider, LAPSUS$ and ShinyHunters. Members of these gangs hail from many of the same chat channels on the Com, a mostly English-language cybercriminal community that operates across an ocean of Telegram and Discord servers.
In May 2025, SLSH members launched a social engineering campaign that used voice phishing to trick targets into connecting a malicious app to their organization’s Salesforce portal. The group later launched a data leak portal that threatened to publish the internal data of three dozen companies that allegedly had Salesforce data stolen, including Toyota, FedEx, Disney/Hulu, and UPS.
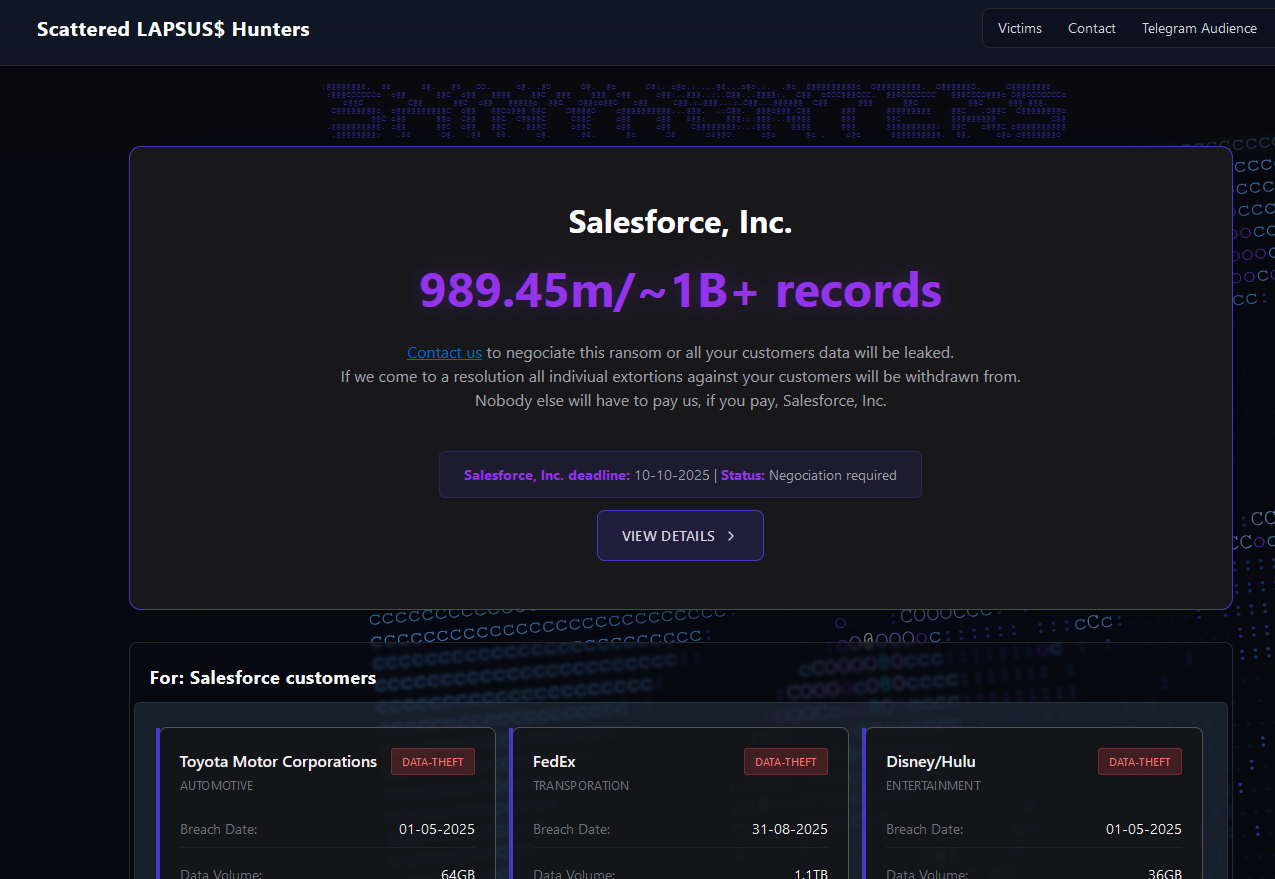
The new extortion website tied to ShinyHunters, which threatens to publish stolen data unless Salesforce or individual victim companies agree to pay a ransom.
Last week, the SLSH Telegram channel featured an offer to recruit and reward “insiders,” employees at large companies who agree to share internal access to their employer’s network for a share of whatever ransom payment is ultimately paid by the victim company.
SLSH has solicited insider access previously, but their latest call for disgruntled employees started making the rounds on social media at the same time news broke that the cybersecurity firm Crowdstrike had fired an employee for allegedly sharing screenshots of internal systems with the hacker group (Crowdstrike said their systems were never compromised and that it has turned the matter over to law enforcement agencies).
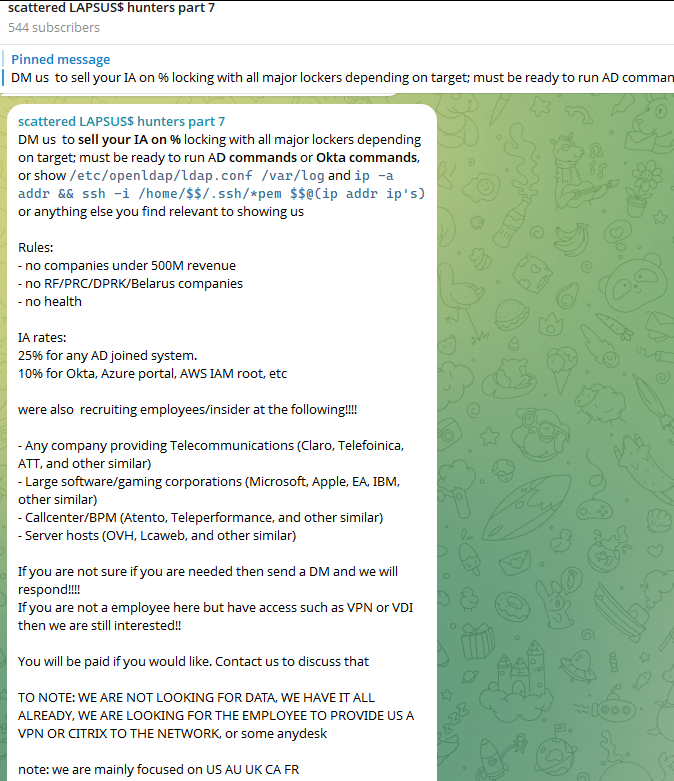
The Telegram server for the Scattered LAPSUS$ Hunters has been attempting to recruit insiders at large companies.
Members of SLSH have traditionally used other ransomware gangs’ encryptors in attacks, including malware from ransomware affiliate programs like ALPHV/BlackCat, Qilin, RansomHub, and DragonForce. But last week, SLSH announced on its Telegram channel the release of their own ransomware-as-a-service operation called ShinySp1d3r.
The individual responsible for releasing the ShinySp1d3r ransomware offering is a core SLSH member who goes by the handle “Rey” and who is currently one of just three administrators of the SLSH Telegram channel. Previously, Rey was an administrator of the data leak website for Hellcat, a ransomware group that surfaced in late 2024 and was involved in attacks on companies including Schneider Electric, Telefonica, and Orange Romania.
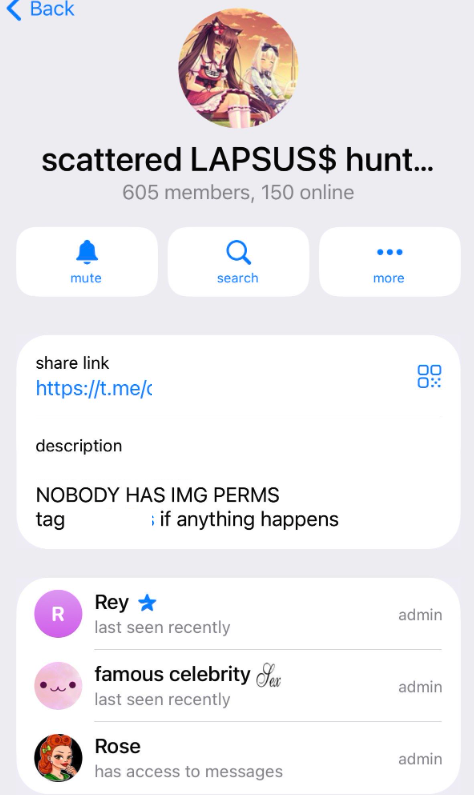
A recent, slightly redacted screenshot of the Scattered LAPSUS$ Hunters Telegram channel description, showing Rey as one of three administrators.
Also in 2024, Rey would take over as administrator of the most recent incarnation of BreachForums, an English-language cybercrime forum whose domain names have been seized on multiple occasions by the FBI and/or by international authorities. In April 2025, Rey posted on Twitter/X about another FBI seizure of BreachForums.
On October 5, 2025, the FBI announced it had once again seized the domains associated with BreachForums, which it described as a major criminal marketplace used by ShinyHunters and others to traffic in stolen data and facilitate extortion.
“This takedown removes access to a key hub used by these actors to monetize intrusions, recruit collaborators, and target victims across multiple sectors,” the FBI said.
Incredibly, Rey would make a series of critical operational security mistakes last year that provided multiple avenues to ascertain and confirm his real-life identity and location. Read on to learn how it all unraveled for Rey.
According to the cyber intelligence firm Intel 471, Rey was an active user on various BreachForums reincarnations over the past two years, authoring more than 200 posts between February 2024 and July 2025. Intel 471 says Rey previously used the handle “Hikki-Chan” on BreachForums, where their first post shared data allegedly stolen from the U.S. Centers for Disease Control and Prevention (CDC).
In that February 2024 post about the CDC, Hikki-Chan says they could be reached at the Telegram username @wristmug. In May 2024, @wristmug posted in a Telegram group chat called “Pantifan” a copy of an extortion email they said they received that included their email address and password.
The message that @wristmug cut and pasted appears to have been part of an automated email scam that claims it was sent by a hacker who has compromised your computer and used your webcam to record a video of you while you were watching porn. These missives threaten to release the video to all your contacts unless you pay a Bitcoin ransom, and they typically reference a real password the recipient has used previously.
“Noooooo,” the @wristmug account wrote in mock horror after posting a screenshot of the scam message. “I must be done guys.”
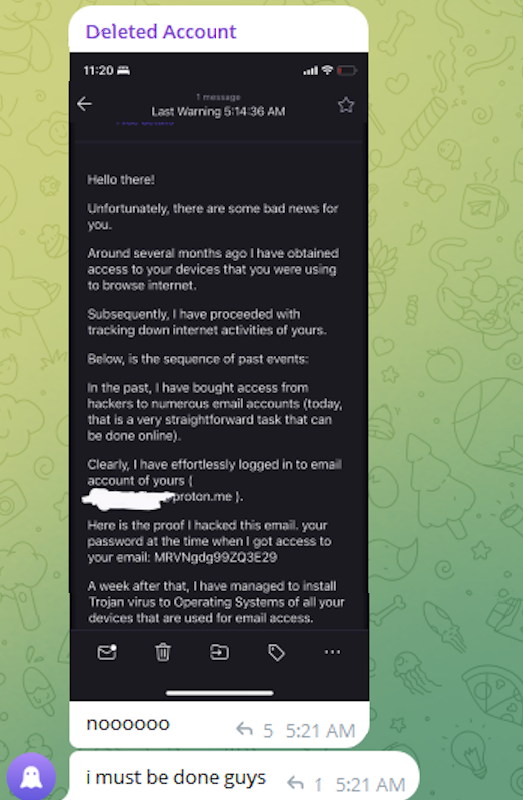
A message posted to Telegram by Rey/@wristmug.
In posting their screenshot, @wristmug redacted the username portion of the email address referenced in the body of the scam message. However, they did not redact their previously-used password, and they left the domain portion of their email address (@proton.me) visible in the screenshot.
Searching on @wristmug’s rather unique 15-character password in the breach tracking service Spycloud finds it is known to have been used by just one email address: cybero5tdev@proton.me. According to Spycloud, those credentials were exposed at least twice in early 2024 when this user’s device was infected with an infostealer trojan that siphoned all of its stored usernames, passwords and authentication cookies (a finding that was initially revealed in March 2025 by the cyber intelligence firm KELA).
Intel 471 shows the email address cybero5tdev@proton.me belonged to a BreachForums member who went by the username o5tdev. Searching on this nickname in Google brings up at least two website defacement archives showing that a user named o5tdev was previously involved in defacing sites with pro-Palestinian messages. The screenshot below, for example, shows that 05tdev was part of a group called Cyb3r Drag0nz Team.

Rey/o5tdev’s defacement pages. Image: archive.org.
A 2023 report from SentinelOne described Cyb3r Drag0nz Team as a hacktivist group with a history of launching DDoS attacks and cyber defacements as well as engaging in data leak activity.
“Cyb3r Drag0nz Team claims to have leaked data on over a million of Israeli citizens spread across multiple leaks,” SentinelOne reported. “To date, the group has released multiple .RAR archives of purported personal information on citizens across Israel.”
The cyber intelligence firm Flashpoint finds the Telegram user @05tdev was active in 2023 and early 2024, posting in Arabic on anti-Israel channels like “Ghost of Palestine” [full disclosure: Flashpoint is currently an advertiser on this blog].
Flashpoint shows that Rey’s Telegram account (ID7047194296) was particularly active in a cybercrime-focused channel called Jacuzzi, where this user shared several personal details, including that their father was an airline pilot. Rey claimed in 2024 to be 15 years old, and to have family connections to Ireland.
Specifically, Rey mentioned in several Telegram chats that he had Irish heritage, even posting a graphic that shows the prevalence of the surname “Ginty.”
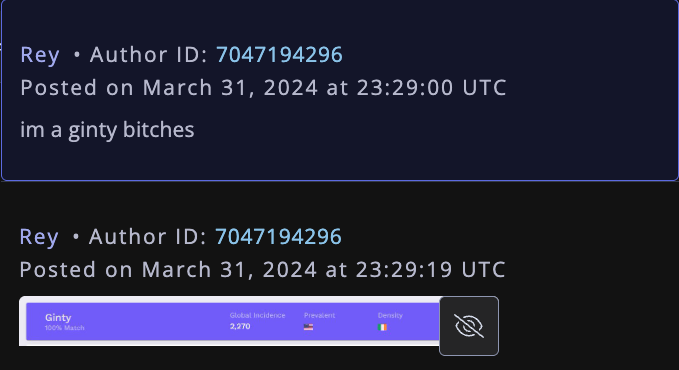
Rey, on Telegram claiming to have association to the surname “Ginty.” Image: Flashpoint.
Spycloud indexed hundreds of credentials stolen from cybero5dev@proton.me, and those details indicate that Rey’s computer is a shared Microsoft Windows device located in Amman, Jordan. The credential data stolen from Rey in early 2024 show there are multiple users of the infected PC, but that all shared the same last name of Khader and an address in Amman, Jordan.
The “autofill” data lifted from Rey’s family PC contains an entry for a 46-year-old Zaid Khader that says his mother’s maiden name was Ginty. The infostealer data also shows Zaid Khader frequently accessed internal websites for employees of Royal Jordanian Airlines.
The infostealer data makes clear that Rey’s full name is Saif Al-Din Khader. Having no luck contacting Saif directly, KrebsOnSecurity sent an email to his father Zaid. The message invited the father to respond via email, phone or Signal, explaining that his son appeared to be deeply enmeshed in a serious cybercrime conspiracy.
Less than two hours later, I received a Signal message from Saif, who said his dad suspected the email was a scam and had forwarded it to him.
“I saw your email, unfortunately I don’t think my dad would respond to this because they think its some ‘scam email,'” said Saif, who told me he turns 16 years old next month. “So I decided to talk to you directly.”
Saif explained that he’d already heard from European law enforcement officials, and had been trying to extricate himself from SLSH. When asked why then he was involved in releasing SLSH’s new ShinySp1d3r ransomware-as-a-service offering, Saif said he couldn’t just suddenly quit the group.
“Well I cant just dip like that, I’m trying to clean up everything I’m associated with and move on,” he said.

The former Hellcat ransomware site. Image: Kelacyber.com
He also shared that ShinySp1d3r is just a rehash of Hellcat ransomware, except modified with AI tools. “I gave the source code of Hellcat ransomware out basically.”
Saif claims he reached out on his own recently to the Telegram account for Operation Endgame, the codename for an ongoing law enforcement operation targeting cybercrime services, vendors and their customers.
“I’m already cooperating with law enforcement,” Saif said. “In fact, I have been talking to them since at least June. I have told them nearly everything. I haven’t really done anything like breaching into a corp or extortion related since September.”
Saif suggested that a story about him right now could endanger any further cooperation he may be able to provide. He also said he wasn’t sure if the U.S. or European authorities had been in contact with the Jordanian government about his involvement with the hacking group.
“A story would bring so much unwanted heat and would make things very difficult if I’m going to cooperate,” Saif said. “I’m unsure whats going to happen they said they’re in contact with multiple countries regarding my request but its been like an entire week and I got no updates from them.”
Saif shared a screenshot that indicated he’d contacted Europol authorities late last month. But he couldn’t name any law enforcement officials he said were responding to his inquiries, and KrebsOnSecurity was unable to verify his claims.
“I don’t really care I just want to move on from all this stuff even if its going to be prison time or whatever they gonna say,” Saif said.
Cloudflare launched fifteen years ago with a mission to help build a better Internet. Over that time the Internet has changed and so has what it needs from teams like ours. In this year’s Founder’s Letter, Matthew and Michelle discussed the role we have played in the evolution of the Internet, from helping encryption grow from 10% to 95% of Internet traffic to more recent challenges like how people consume content.
We spend Birthday Week every year releasing the products and capabilities we believe the Internet needs at this moment and around the corner. Previous Birthday Weeks saw the launch of IPv6 gateway in 2011, Universal SSL in 2014, Cloudflare Workers and unmetered DDoS protection in 2017, Cloudflare Radar in 2020, R2 Object Storage with zero egress fees in 2021, post-quantum upgrades for Cloudflare Tunnel in 2022, Workers AI and Encrypted Client Hello in 2023. And those are just a sample of the launches.
This year’s themes focused on helping prepare the Internet for a new model of monetization that encourages great content to be published, fostering more opportunities to build community both inside and outside of Cloudflare, and evergreen missions like making more features available to everyone and constantly improving the speed and security of what we offer.
We shipped a lot of new things this year. In case you missed the dozens of blog posts, here is a breakdown of everything we announced during Birthday Week 2025.
Monday, September 22
| What | In a sentence … |
|---|---|
| Help build the future: announcing Cloudflare’s goal to hire 1,111 interns in 2026 | To invest in the next generation of builders, we announced our most ambitious intern program yet with a goal to hire 1,111 interns in 2026. |
| Supporting the future of the open web: Cloudflare is sponsoring Ladybird and Omarchy | To support a diverse and open Internet, we are now sponsoring Ladybird (an independent browser) and Omarchy (an open-source Linux distribution and developer environment). |
| Come build with us: Cloudflare’s new hubs for startups | We are opening our office doors in four major cities (San Francisco, Austin, London, and Lisbon) as free hubs for startups to collaborate and connect with the builder community. |
| Free access to Cloudflare developer services for non-profit and civil society organizations | We extended our Cloudflare for Startups program to non-profits and public-interest organizations, offering free credits for our developer tools. |
| Introducing free access to Cloudflare developer features for students | We are removing cost as a barrier for the next generation by giving students with .edu emails 12 months of free access to our paid developer platform features. |
| Cap’n Web: a new RPC system for browsers and web servers | We open-sourced Cap'n Web, a new JavaScript-native RPC protocol that simplifies powerful, schema-free communication for web applications. |
| A lookback at Workers Launchpad and a warm welcome to Cohort #6 | We announced Cohort #6 of the Workers Launchpad, our accelerator program for startups building on Cloudflare. |
Tuesday, September 23
| What | In a sentence … |
|---|---|
| Building unique, per-customer defenses against advanced bot threats in the AI era | New anomaly detection system that uses machine learning trained on each zone to build defenses against AI-driven bot attacks. |
| Why Cloudflare, Netlify, and Webflow are collaborating to support Open Source tools | To support the open web, we joined forces with Webflow to sponsor Astro, and with Netlify to sponsor TanStack. |
| Launching the x402 Foundation with Coinbase, and support for x402 transactions | We are partnering with Coinbase to create the x402 Foundation, encouraging the adoption of the x402 protocol to allow clients and services to exchange value on the web using a common language |
| Helping protect journalists and local news from AI crawlers with Project Galileo | We are extending our free Bot Management and AI Crawl Control services to journalists and news organizations through Project Galileo. |
| Cloudflare Confidence Scorecards - making AI safer for the Internet | Automated evaluation of AI and SaaS tools, helping organizations to embrace AI without compromising security. |
Wednesday, September 24
| What | In a sentence … |
|---|---|
| Automatically Secure: how we upgraded 6,000,000 domains by default | Our Automatic SSL/TLS system has upgraded over 6 million domains to more secure encryption modes by default and will soon automatically enable post-quantum connections. |
| Giving users choice with Cloudflare’s new Content Signals Policy | The Content Signals Policy is a new standard for robots.txt that lets creators express clear preferences for how AI can use their content. |
| To build a better Internet in the age of AI, we need responsible AI bot principles | A proposed set of responsible AI bot principles to start a conversation around transparency and respect for content creators' preferences. |
| Securing data in SaaS to SaaS applications | New security tools to give companies visibility and control over data flowing between SaaS applications. |
| Securing today for the quantum future: WARP client now supports post-quantum cryptography (PQC) | Cloudflare’s WARP client now supports post-quantum cryptography, providing quantum-resistant encryption for traffic. |
| A simpler path to a safer Internet: an update to our CSAM scanning tool | We made our CSAM Scanning Tool easier to adopt by removing the need to create and provide unique credentials, helping more site owners protect their platforms. |
Thursday, September 25
| What | In a sentence … |
|---|---|
| Every Cloudflare feature, available to everyone | We are making every Cloudflare feature, starting with Single Sign On (SSO), available for anyone to purchase on any plan. |
| Cloudflare's developer platform keeps getting better, faster, and more powerful | Updates across Workers and beyond for a more powerful developer platform – such as support for larger and more concurrent Container images, support for external models from OpenAI and Anthropic in AI Search (previously AutoRAG), and more. |
| Partnering to make full-stack fast: deploy PlanetScale databases directly from Workers | You can now connect Cloudflare Workers to PlanetScale databases directly, with connections automatically optimized by Hyperdrive. |
| Announcing the Cloudflare Data Platform | A complete solution for ingesting, storing, and querying analytical data tables using open standards like Apache Iceberg. |
| R2 SQL: a deep dive into our new distributed query engine | A technical deep dive on R2 SQL, a serverless query engine for petabyte-scale datasets in R2. |
| Safe in the sandbox: security hardening for Cloudflare Workers | A deep-dive into how we’ve hardened the Workers runtime with new defense-in-depth security measures, including V8 sandboxes and hardware-assisted memory protection keys. |
| Choice: the path to AI sovereignty | To champion AI sovereignty, we've added locally-developed open-source models from India, Japan, and Southeast Asia to our Workers AI platform. |
| Announcing Cloudflare Email Service’s private beta | We announced the Cloudflare Email Service private beta, allowing developers to reliably send and receive transactional emails directly from Cloudflare Workers. |
| A year of improving Node.js compatibility in Cloudflare Workers | There are hundreds of new Node.js APIs now available that make it easier to run existing Node.js code on our platform. |
Friday, September 26
| What | In a sentence … |
|---|---|
| Cloudflare just got faster and more secure, powered by Rust | We have re-engineered our core proxy with a new modular, Rust-based architecture, cutting median response time by 10ms for millions. |
| Introducing Observatory and Smart Shield | New monitoring tools in the Cloudflare dashboard that provide actionable recommendations and one-click fixes for performance issues. |
| Monitoring AS-SETs and why they matter | Cloudflare Radar now includes Internet Routing Registry (IRR) data, allowing network operators to monitor AS-SETs to help prevent route leaks. |
| An AI Index for all our customers | We announced the private beta of AI Index, a new service that creates an AI-optimized search index for your domain that you control and can monetize. |
| Introducing new regional Internet traffic and Certificate Transparency insights on Cloudflare Radar | Sub-national traffic insights and Certificate Transparency dashboards for TLS monitoring. |
| Eliminating Cold Starts 2: shard and conquer | We have reduced Workers cold starts by 10x by implementing a new "worker sharding" system that routes requests to already-loaded Workers. |
| Network performance update: Birthday Week 2025 | The TCP Connection Time (Trimean) graph shows that we are the fastest TCP connection time in 40% of measured ISPs – and the fastest across the top networks. |
| How Cloudflare uses performance data to make the world’s fastest global network even faster | We are using our network's vast performance data to tune congestion control algorithms, improving speeds by an average of 10% for QUIC traffic. |
| Code Mode: the better way to use MCP | It turns out we've all been using MCP wrong. Most agents today use MCP by exposing the "tools" directly to the LLM. We tried something different: Convert the MCP tools into a TypeScript API, and then ask an LLM to write code that calls that API. The results are striking. |
Helping build a better Internet has always been about more than just technology. Like the announcements about interns or working together in our offices, the community of people behind helping build a better Internet matters to its future. This week, we rolled out our most ambitious set of initiatives ever to support the builders, founders, and students who are creating the future.
For founders and startups, we are thrilled to welcome Cohort #6 to the Workers Launchpad, our accelerator program that gives early-stage companies the resources they need to scale. But we’re not stopping there. We’re opening our doors, literally, by launching new physical hubs for startups in our San Francisco, Austin, London, and Lisbon offices. These spaces will provide access to mentorship, resources, and a community of fellow builders.
We’re also investing in the next generation of talent. We announced free access to the Cloudflare developer platform for all students, giving them the tools to learn and experiment without limits. To provide a path from the classroom to the industry, we also announced our goal to hire 1,111 interns in 2026 — our biggest commitment yet to fostering future tech leaders.
And because a better Internet is for everyone, we’re extending our support to non-profits and public-interest organizations, offering them free access to our production-grade developer tools, so they can focus on their missions.
Whether you're a founder with a big idea, a student just getting started, or a team working for a cause you believe in, we want to help you succeed.
Thank you to our customers, our community, and the millions of developers who trust us to help them build, secure, and accelerate the Internet. Your curiosity and feedback drive our innovation.
It’s been an incredible 15 years. And as always, we’re just getting started!
(Watch the full conversation on our show ThisWeekinNET.com about what we launched during Birthday Week 2025 here.)
Lots of startups use Google’s productivity suite, known as Workspace, to handle email, documents, and other back-office matters. Relatedly, lots of business-minded webapps use Google’s OAuth, i.e. “Sign in with Google.” It’s a low-friction feedback loop—up until the startup fails, the domain goes up for sale, and somebody forgot to close down all the Google stuff.
Dylan Ayrey, of Truffle Security Co., suggests in a report that this problem is more serious than anyone, especially Google, is acknowledging. Many startups make the critical mistake of not properly closing their accounts—on both Google and other web-based apps—before letting their domains expire.
Given the number of people working for tech startups (6 million), the failure rate of said startups (90 percent), their usage of Google Workspaces (50 percent, all by Ayrey’s numbers), and the speed at which startups tend to fall apart, there are a lot of Google-auth-connected domains up for sale at any time. That would not be an inherent problem, except that, as Ayrey shows, buying a domain with a still-active Google account can let you re-activate the Google accounts for former employees.


© Aurich Lawson | Getty Images