A new GoGra Linux malware uses Microsoft Graph API and an Outlook inbox to deliver payloads, making it stealthy and hard to detect.
A new Linux version of the GoGra backdoor uses Microsoft’s Graph API and an Outlook inbox to deliver malicious payloads stealthily. The malware is linked to the Harvester cyberespionage group, which is believed to be a nation-state actor. The malicious code blends in with legitimate traffic, making detection more difficult and increasing its effectiveness in targeted cyber espionage operations.
“The Harvester APT group has developed a new, highly-evasive, Linux version of its GoGra backdoor. The malware uses the legitimate Microsoft Graph API and Outlook mailboxes as a covert command-and-control (C2) channel, allowing it to bypass traditional perimeter network defenses.” reads the report published by Broadcom Symantec. “The Symantec and Carbon Black Threat Hunter Team linked this new Linux malware to a previously known Windows espionage campaign by Harvester due to similarities in code, demonstrating that the threat actor is actively expanding its cross-platform capabilities.”
Initial evidence suggests the campaign targeted South Asia, with early samples submitted from India and Afghanistan and the use of localized decoy documents indicating a tailored approach. The Harvester group, active since at least 2021 uses both custom malware and public tools, including Graphon, a backdoor similar to GoGra that relies on Microsoft infrastructure for command-and-control.
The GoGra backdoor abuses Microsoft cloud services by using hardcoded Azure AD credentials to obtain OAuth2 tokens. It polls a specific Outlook mailbox folder via Microsoft Graph API, looking for emails with commands. These are decrypted and executed on the system, while results are encrypted and sent back.
“It uses OData queries to poll a specific mailbox folder, named “Zomato Pizza”, at two-second intervals. OData (Open Data Protocol) query is the syntax used to filter, sort, and shape data when interacting with the Microsoft Graph API. Interestingly, the Windows version of the malware used a mailbox named “Dragan Dash”. Dragan Dash Kitchen is a food delivery restaurant located in in the Indian city of Hyderabad.” continues the report. “The backdoor filters for incoming email messages with a subject line starting with the word ‘Input’. Upon receiving an email, it decrypts the base64-wrapped message body using AES-CBC encryption, and executes the payload on the host via /bin/bash -c.”
Afterward, the malware deletes the messages to erase traces and remain stealthy.
The researchers noted that Linux and Windows versions of GoGra share a nearly identical codebase, indicating a cross-platform development effort by the Harvester group. Despite different OS targets, both variants keep the same command-and-control logic and even share identical coding mistakes, suggesting a single developer.
Both versions use the same AES key and similar modules, but differ in architecture, beacon timing, and mailbox names used for command delivery.
“The use of a new Linux backdoor shows that Harvester is continuing to expand its toolset and actively develop new tooling in order to go after a wider range of victims and machines.” concludes the report. “While we did not see victims in this activity, it seems clear that the group continues to retain an interest in the South Asia region for espionage purposes. “
Follow me on Twitter: @securityaffairs and Facebook and Mastodon
Pierluigi Paganini
(SecurityAffairs – hacking, malware)



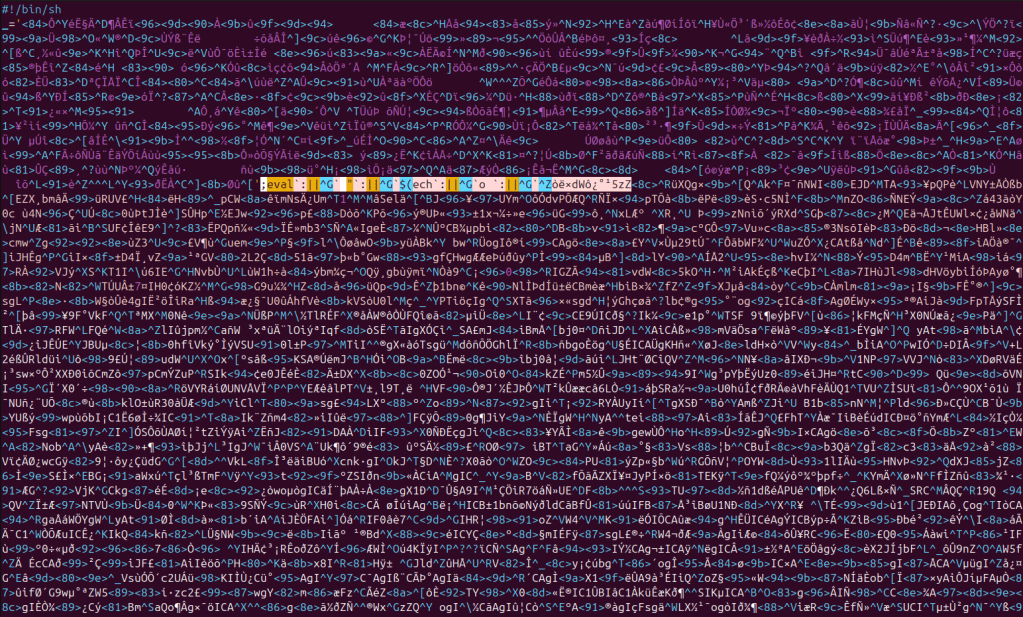 Bincrypt Obfuscated Loader (Source: CRIL)[/caption]
Bincrypt Obfuscated Loader (Source: CRIL)[/caption]
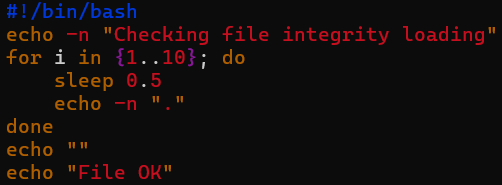 Dropper Cosmetics (Source: CRIL)[/caption]
Dropper Cosmetics (Source: CRIL)[/caption]
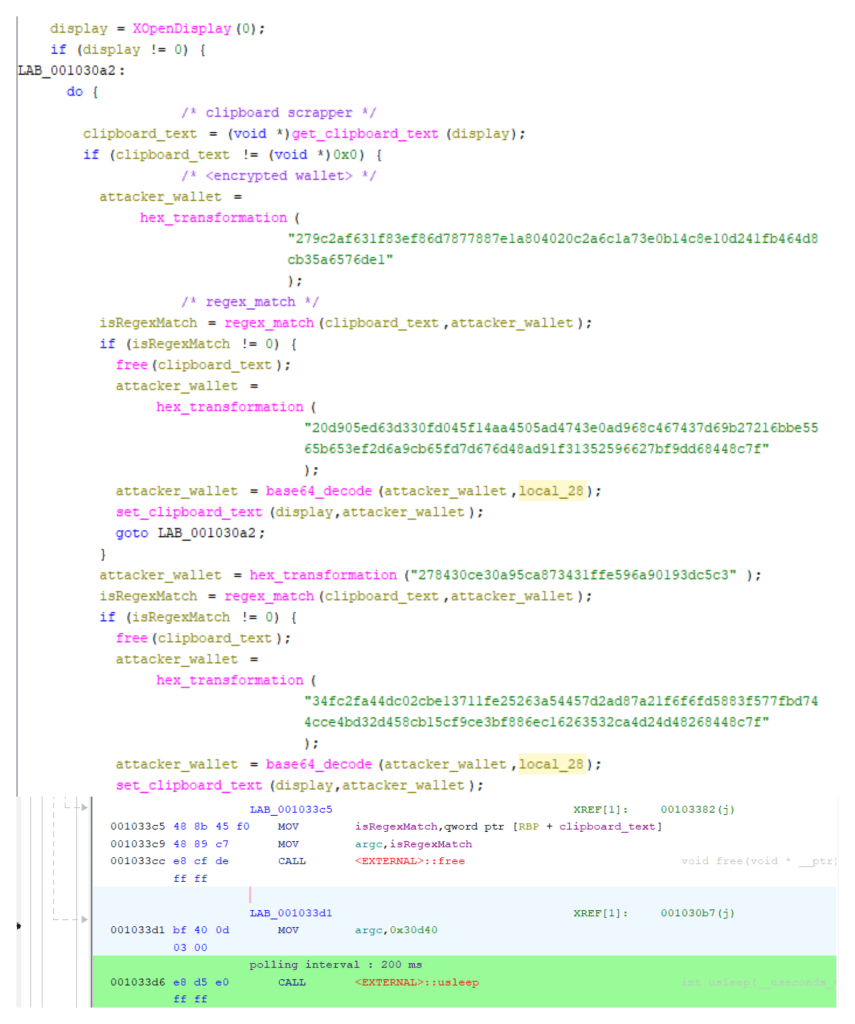 Clipboard Monitoring Loop with 200ms Polling (Source: CRIL)[/caption]
Clipboard Monitoring Loop with 200ms Polling (Source: CRIL)[/caption]